Aadhaar's Expansion Into Wallets, Hotels, and Policing: What Privacy Advocates Worry About [2025]
India just made a major move with Aadhaar. The world's largest digital identity system is no longer just background infrastructure for banks and government agencies. It's now moving into your phone as an app, integrating with Google Wallet and Apple Wallet, and showing up at hotel check-ins and police databases.
On the surface, it sounds convenient. No more digging through your wallet for ID. Just pull out your phone. Verify your age without handing over your full birthdate. Share selective information instead of photocopying your entire identity document.
But here's what's keeping digital rights advocates up at night: India's data protection framework isn't ready for this kind of expansion. The foundational laws that should govern how this data gets handled are still being written. And the security infrastructure that protects 1.4 billion Aadhaar numbers? It's been tested before, and the results weren't always reassuring, as noted in a report on cybersecurity risks in India.
This isn't fearmongering. It's the reality of scaling a digital identity system faster than the rules can keep up. India's government and the Unique Identification Authority of India (UIDAI) say they're putting control in citizens' hands through selective data sharing. Critics say we won't know if that's actually true until much later, when the system is already deeply embedded in everyday life.
Let's break down what's actually happening with Aadhaar, why it matters, and what the real risks look like.
TL; DR
- Massive scale meets new use cases: Aadhaar handles 2.5 billion authentication transactions monthly and is now expanding from backend verification into consumer-facing apps, mobile wallets, hotels, and police systems.
- New app downloads exploded: The latest Aadhaar app reached 9 million monthly installs by December 2025, overtaking the older m Aadhaar app in weeks.
- Offline verification reshapes the game: UIDAI launched offline identity verification that doesn't require real-time database queries, moving Aadhaar from government infrastructure into private sector and everyday settings.
- Data protection framework lags behind implementation: India's Data Protection Board isn't established yet, leaving no independent oversight for the system's expansion into hotels, wallets, and policing.
- Historical security issues create credibility gaps: Previous Aadhaar data breaches and database access vulnerabilities raise questions about whether selective sharing actually prevents leaks.

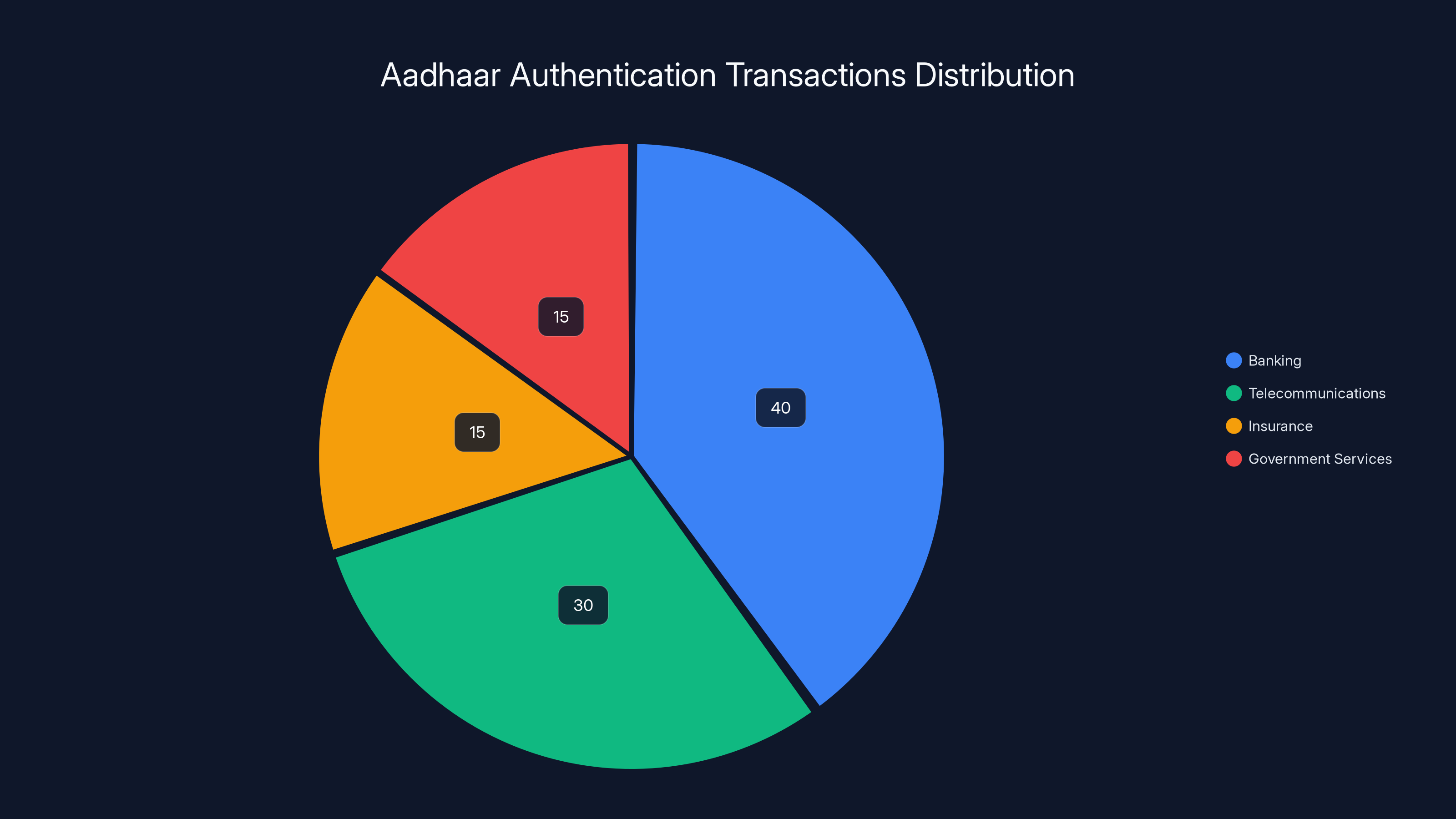
Estimated data shows that banking and telecommunications sectors account for the majority of Aadhaar's 2.5 billion monthly authentication transactions.
Understanding Aadhaar: Why 1.4 Billion People Have It
Aadhaar isn't new. It's been around since 2009, and it's unlike anything else in the world at this scale. We're talking about a biometric-based digital identity system that covers roughly 95% of India's adult population.
Here's what makes it different from national ID systems in other countries: it was built from the ground up as digital-first infrastructure. Not a digitized version of an old paper system, but designed to work in an entirely digital ecosystem from day one.
The original purpose was practical. India needed a way to deliver government benefits more efficiently. Aadhaar became the backbone for that. No more forging documents to claim subsidies. No more duplicate payments. One number, biometric verification, and the system could track who gets what.
It worked at scale in ways nobody quite expected. By 2025, Aadhaar handles roughly 2.5 billion authentication transactions each month. That's not theoretical capacity. That's actual usage. Every month.
Electronic know-your-customer checks through Aadhaar? Tens of billions since launch. Banks use it. Telecom companies use it. Insurance companies use it. Government agencies use it. The system became so fundamental to India's digital infrastructure that pulling it out would break things.
But there's a crucial difference between using something for backend verification and putting it directly in users' hands. That's where the recent changes come in.
The New Aadhaar App: What Changed in 2025
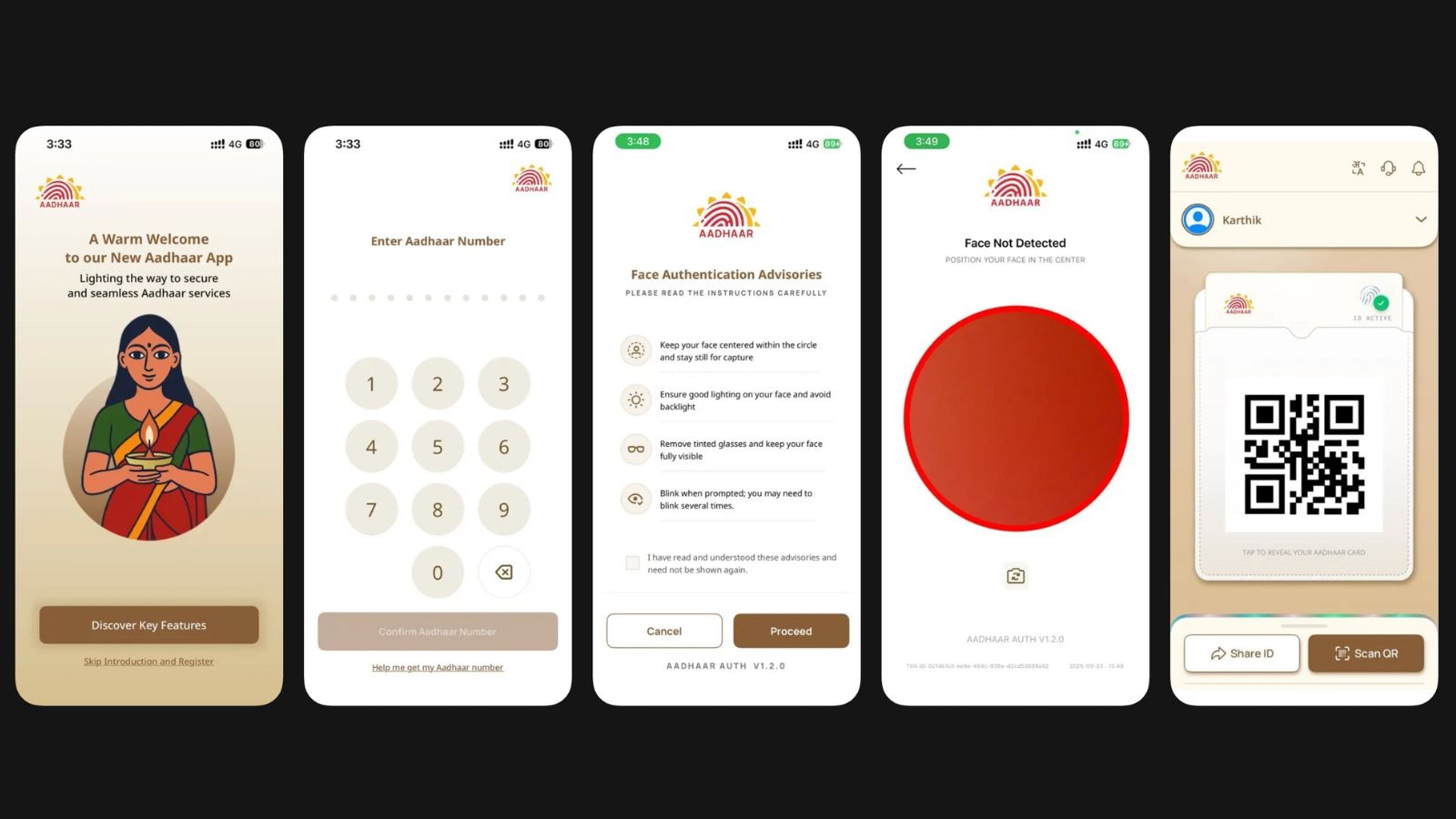
In late January 2025, UIDAI announced something different. Not a minor update to existing systems, but a new app that fundamentally changes how Aadhaar works in daily life.
Let's be specific about what the new app does. It lets you share limited information instead of everything. Your full Aadhaar number? Not shared. Your complete birthdate? Not needed. Instead, you can confirm to a hotel that you're over 18 without revealing you were born in 1987. You can confirm to a housing society that you're a verified resident without handing over biometric data.
This is called selective data sharing, and it sounds smart on paper. The app generates digital credentials that prove specific facts about you without proving everything about you.
Download numbers show adoption is happening fast. When the app appeared in app stores toward the end of 2025, it started accumulating downloads quietly. By October 2025, combined Aadhaar-related app installs were around 2 million monthly. By December, that jumped to nearly 9 million.
The new app is outpacing the older m Aadhaar app. That shift matters because it shows people are moving toward the new interface. They're downloading it. They're using it.
But rapid adoption creates a pressure problem. When something grows faster than the systems meant to govern it, gaps appear.
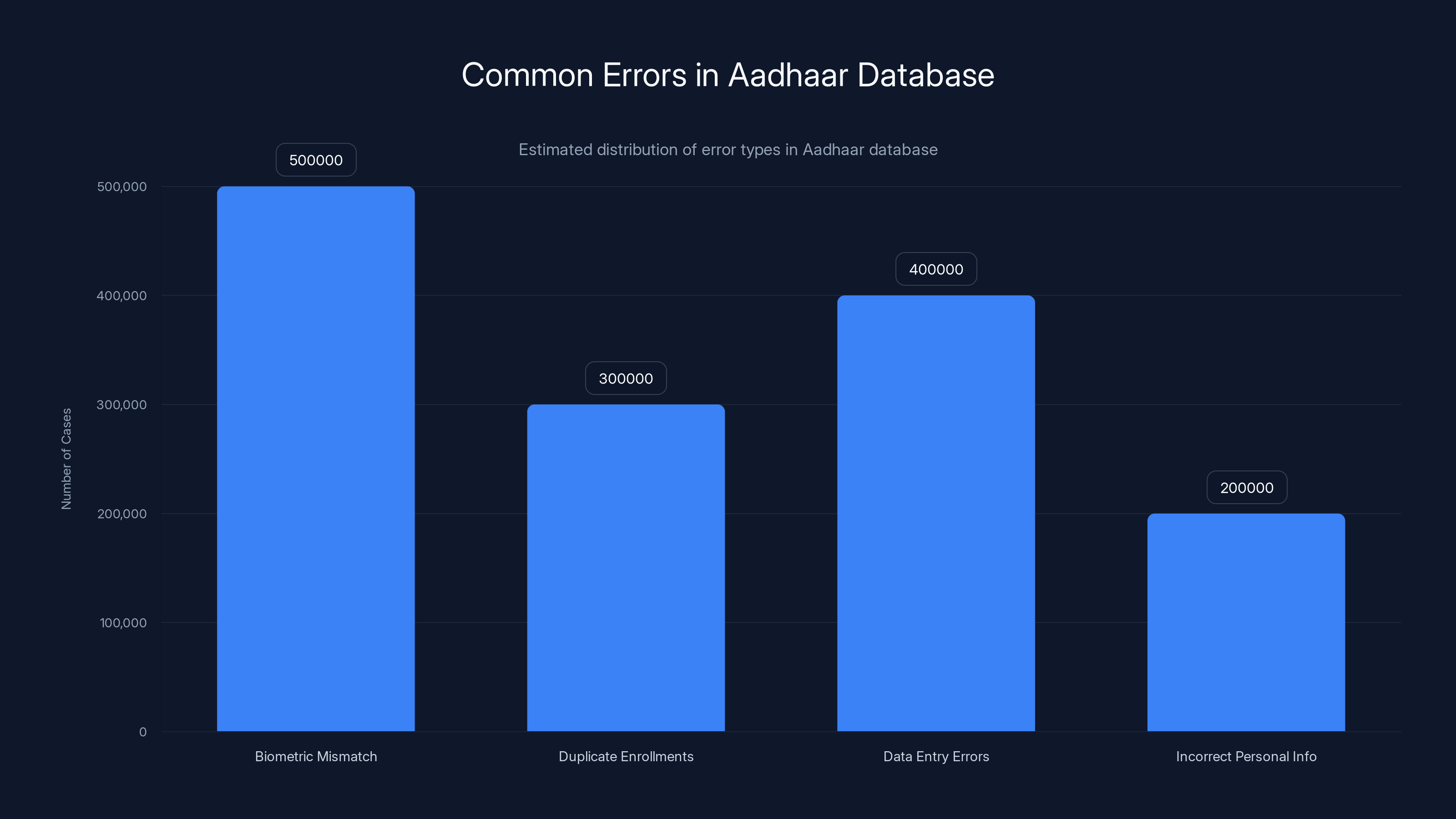
Biometric mismatches and data entry errors are the most common inaccuracies in the Aadhaar database, affecting millions. (Estimated data)
Offline Verification: Convenience or Risk?
Here's the feature that makes everything different: offline verification.
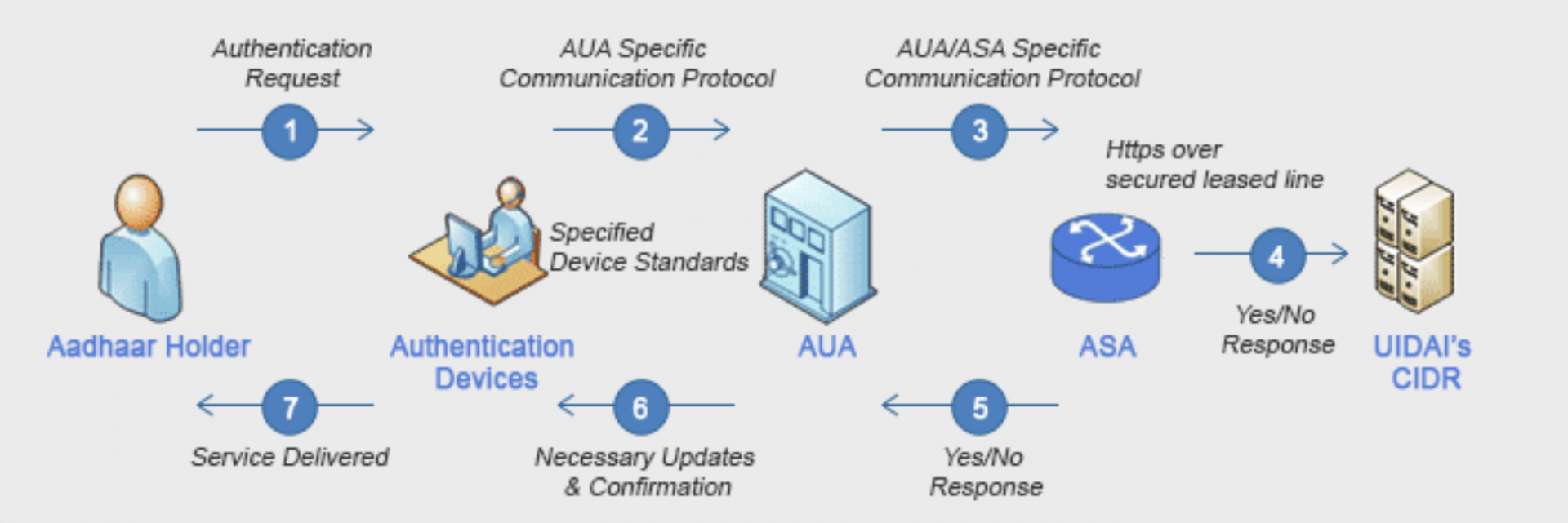
Traditionally, when someone verified your Aadhaar, the system sent a query to UIDAI's central database. Real-time check. Central authority. Instant answer: yes or no, this person is who they claim.
Offline verification removes that requirement. Instead of querying the database every time, you can now generate a digital credential locally on your phone. Show that credential to verify yourself. No central database call required.
On the surface, this solves real problems. Not everyone in India has reliable internet. Why require a database query if you can verify offline? It enables verification at scale without creating bottlenecks. It distributes the verification process instead of funneling everything through a central system.
UIDAI officials said it also addresses how Aadhaar has historically been misused. People photocopy their Aadhaar cards. Those photocopies get circulated. They're stored improperly. They're screenshotted. A lot of sensitive data ends up in places it shouldn't because the physical document is too easy to duplicate and distribute.
Offline verification could theoretically change that. Instead of handing over a physical copy or a full digital file, you share just enough information to verify a specific fact. Age verification shares age. Residence verification shares residence. Nothing else.
The problem is theoretical versus actual. In theory, selective sharing prevents misuse. In practice, it depends entirely on how the system is implemented, who has access to the credentials, and whether the framework preventing data leaks actually works.
The Mobile Wallet Integration: From App to Pocket
Aadhaar is moving beyond an app on your phone. It's integrating into mobile wallets. Google Wallet first. Apple Wallet and Samsung Wallet are in discussions.
If that happens, your digital identity lives in the same place you keep your credit card, your boarding pass, and your transit payment. One platform for financial transactions and identity verification.
The convenience argument is obvious. One app for everything makes sense. But it also means identity data is now stored alongside financial data in systems designed by Google, Apple, and Samsung.
That creates a new question: who controls the data now? UIDAI built Aadhaar. Google built Google Wallet. Those are different companies with different security standards and different regulatory obligations.
When Aadhaar is just on UIDAI's servers, there's one point of attack. When it's synchronized with Google's servers, Apple's servers, and Samsung's servers, the attack surface expands dramatically.
None of this means it will definitely fail. Google's security is solid. Apple's is solid. But it does mean the risk profile changed. It's not just "UIDAI's security" anymore. It's "UIDAI plus Google plus Apple plus whoever else the system connects to."
That's a higher complexity threshold, and complexity is usually where security breaks.
Police, Hotels, and Policing: Normalization Through Integration
Here's where things get genuinely concerning. Aadhaar is now being integrated into police systems.
The Ahmedabad City Crime Branch launched the first integration of Aadhaar-based offline verification with PATHIK, a guest-monitoring platform. Hotels and guest accommodations use PATHIK to record visitor information. Now they can verify visitors through Aadhaar.
From a law enforcement perspective, the logic is clear. You know who stayed at a hotel. You have verified identity data. Less forging of guest registers. Less confusion about who was where.
But look at the implications. Every hotel stay is now linked to verified identity. That creates a permanent record of movement and location. Police can query that. Hotels can query that. Third parties who get access to that data can query that.
That's fundamentally different from the old system where a hotel had a guest register and law enforcement would need to go physically get it.
UIDAI positioned the app as a digital visiting card for business and networking. You share your details via QR code at a meeting. Convenient. Professional. But it also means your professional network and your identity data start converging.
Combine the police integration, the hotel integration, and the networking use case, and you start to see the issue. Aadhaar becomes the thread connecting your location, your profession, your travel history, and your verified identity. All in one system.

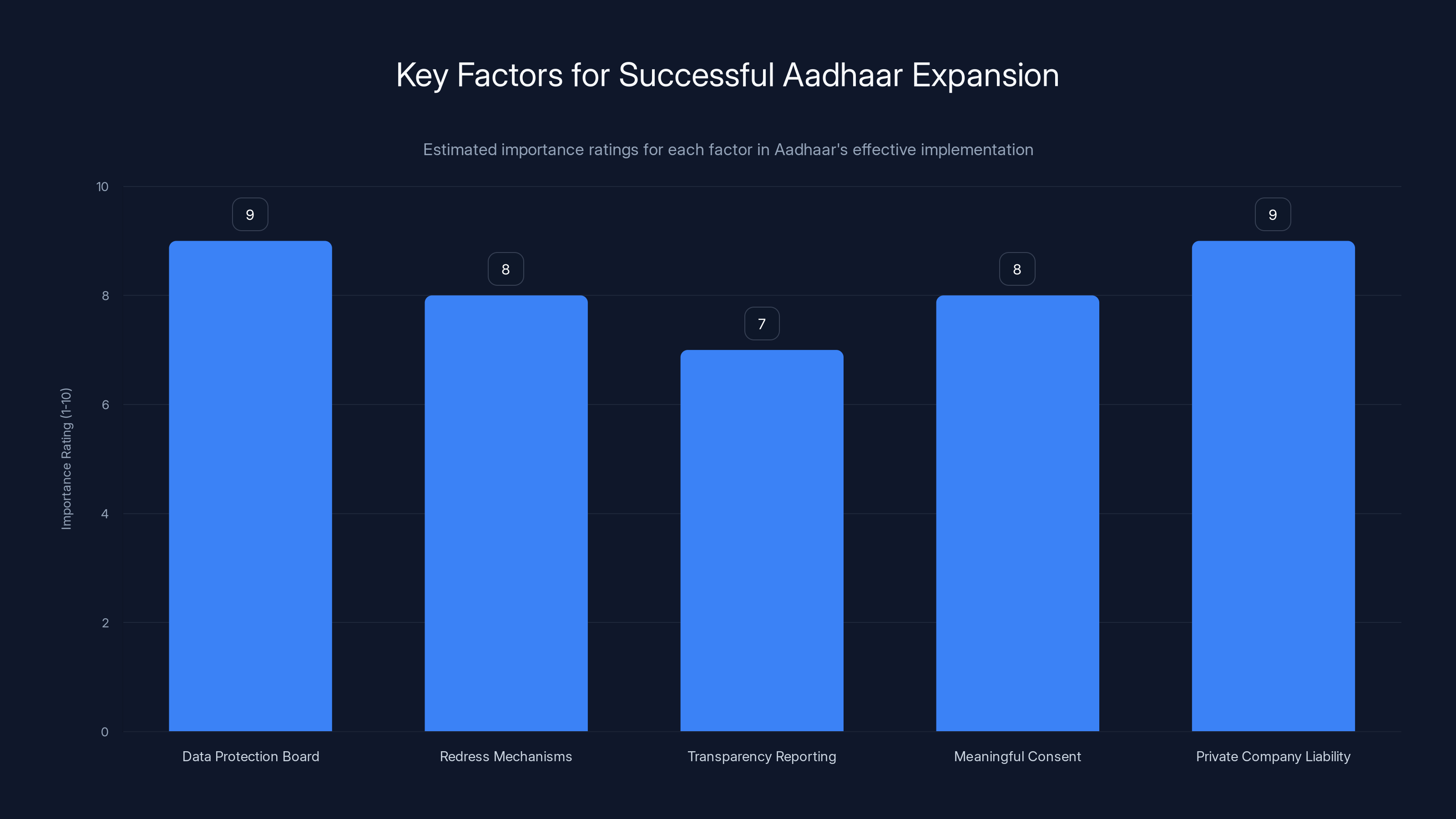
Estimated data shows that establishing a Data Protection Board and enforcing private company liability are crucial for Aadhaar's successful expansion.
The Data Protection Framework Problem: Laws Behind Technology
Here's the real structural issue that keeps experts awake: India's Data Protection Board doesn't exist yet.
Let that sink in. India is expanding a massive digital identity system into wallets, police systems, and everyday verification. The independent oversight body that's supposed to review and approve this expansion? Still being established.
Access Now's Raman Jit Singh Chima pointed out the timing problem directly. The government should have waited. Get the Data Protection Board in place. Let it review the expansion. Allow public consultation. Check with affected communities.
Instead, the expansion is happening now. The oversight comes later. That's backwards.
It's not that the rules don't exist. India has regulations around data handling. But those regulations are generic. They're not specifically designed for a system like Aadhaar, where one identifier connects financial systems, government services, police databases, hotels, and private sector verification.
When the Data Protection Board finally forms, it will inherit a system that's already deeply embedded. Already normalized. Already processing 2.5 billion transactions monthly. Changing the rules at that point becomes vastly more complicated.
There's also a consent problem baked in. UIDAI says the system is consent-based. Users decide what data to share. But consent only works if people understand what they're consenting to. Do most hotel guests understand that their Aadhaar verification creates a permanent government-accessible record of their stay? Do they know police can query that data?
Likely not. Most people consent because it's convenient and seems normal. That's not meaningful consent. That's consent through momentum.

Historical Security Issues: Why Trust Is Hard to Rebuild
Aadhaar's security record isn't pristine. That's important context because it shapes why experts are skeptical about selective data sharing.
In 2017, journalists found that Aadhaar data was available for purchase on the dark web. The data wasn't hacked from UIDAI directly. It was collected from government systems and private companies that had access to Aadhaar information.
Later, investigations revealed that unauthorized people had access to Aadhaar enrollment data through government portals. Not a breach in the technical sense. A failure in access controls. People who shouldn't have access did have access.
There's also the question of data duplication. Even if UIDAI's systems are secure, the data has to exist somewhere when it's used. Banks store it. Telecom companies store it. Insurance companies store it. Each copy is a potential vulnerability.
When you add offline verification to that, the data spreads further. Every credential generated locally on a phone is another copy that could be compromised. Every wallet integration creates another system holding Aadhaar data. Every hotel, every police station, every business that validates those credentials is a new endpoint where the data sits.
Poor security practices exist everywhere. A hotel might store credentials in a badly configured database. A police station might leave data on an unsecured server. A third-party vendor might handle credentials carelessly.
UIDAI can't control all of that. They can set standards. They can audit. But they can't prevent every mistake. And with 1.4 billion people's identities in the system, mistakes get expensive.

Inaccuracies in the Aadhaar Database: A Persistent Problem
Here's something that doesn't get enough attention: Aadhaar database inaccuracies.
The system isn't perfect. Biometric matching sometimes fails. Duplicate enrollments happen. Data entry errors occur. When you're processing 1.4 billion identities, even a 0.1% error rate means 1.4 million people have problems.
These errors create real consequences. Someone can't open a bank account because their biometric doesn't match perfectly. Someone's name is spelled wrong in the database, so they can't receive government benefits. Someone's age is recorded incorrectly, which matters for everything from insurance to voting.
When these errors happen, redress mechanisms are supposed to fix them. You file a complaint. UIDAI investigates. They correct the data.
Except that process is slow. It's bureaucratic. And for people who desperately need the correction, slow is the same as broken.
Now add selective data sharing to this. The app generates credentials based on database data. If the database is wrong, the credential is wrong. You're sharing incorrect information about yourself, and you might not even know it.

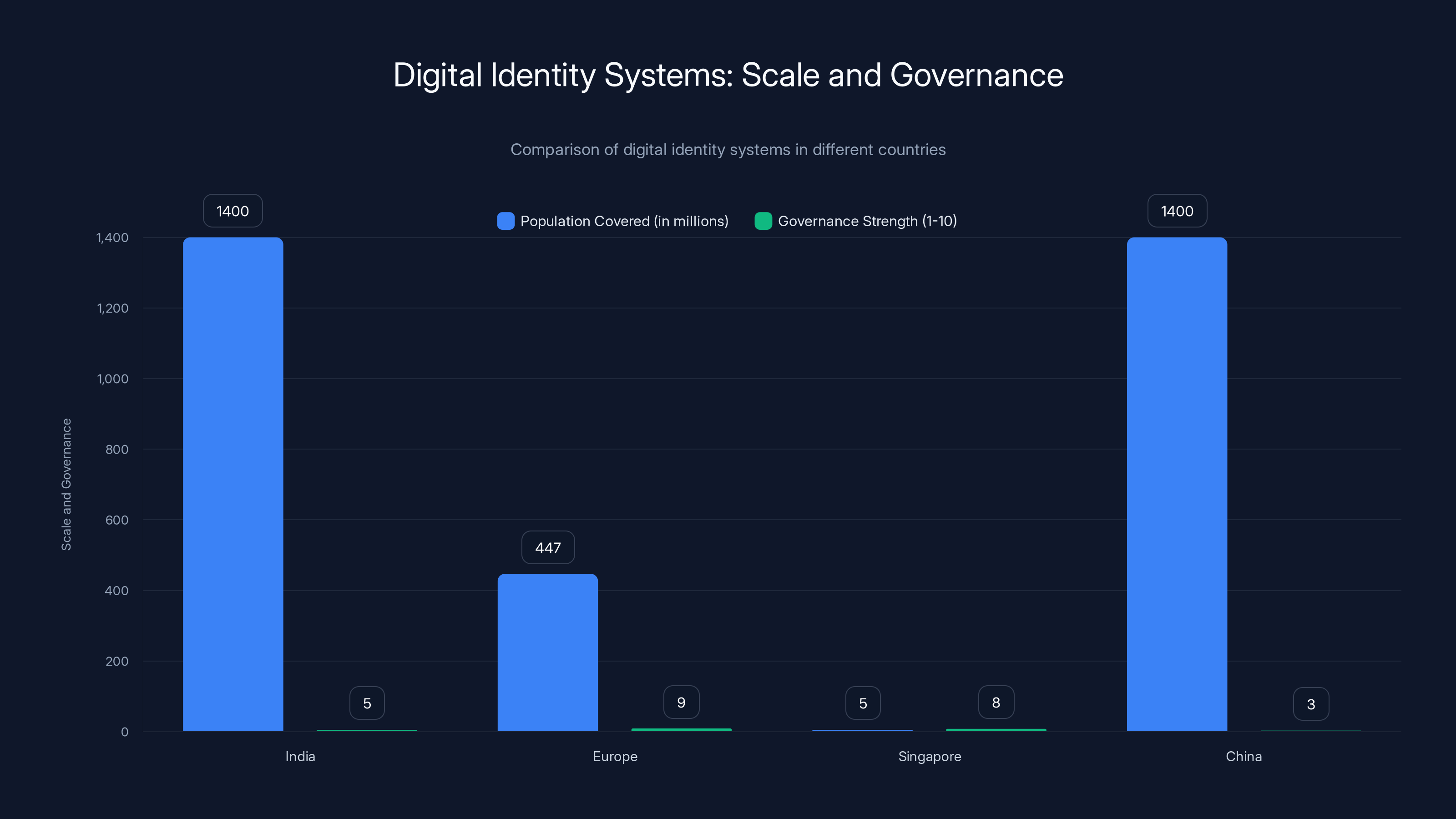
India's digital identity system covers a massive population, similar to China, but aims for governance standards akin to Europe. Estimated data.
The Consent Question: Is Sharing Really Voluntary?
This might be the most important issue, and it's the hardest to measure.
UIDAI says the system is consent-based. You control what information you share. You decide who gets what. It's empowering.
But meaningful consent requires several things: understanding what you're consenting to, genuine alternatives if you refuse, and freedom from coercion.
How many hotel guests understand that checking in with Aadhaar creates a record that police can access? How many employees at companies requiring Aadhaar verification for entry understand they're creating a location history? How many people using Aadhaar in wallets realize they're linking their identity to their payment system?
Most don't. They see convenience. They don't see the downstream implications.
Also, in India's context, Aadhaar has become quasi-mandatory for many services. You need it for a phone plan. You need it for a bank account. You need it for government benefits. When something is effectively required, consent becomes theoretical.
If a hotel says "Please check in with Aadhaar for quick verification," you have a choice. But if most hotels require it and paper-based check-in becomes impossible, your choice disappears.
That's not consent through coercion. But it's consent under conditions that aren't entirely free.
The Integration Cascade: One System Connecting Everything
The real risk isn't any single integration. It's the cascade effect of integrating Aadhaar everywhere.
Aadhaar starts as identity verification for government services. Then it's used for banking. Then telecom. Then insurance. Each integration makes sense individually. But together, they create a system where one identifier connects your government interactions, your financial life, your communications, your insurance, your travel, your hotel stays, and your police records.
That's not just identity infrastructure. That's surveillance infrastructure. Not because anyone maliciously designed it that way, but because the aggregate of many sensible decisions creates something with different properties than any individual decision.
Data analysts call this a knowledge graph. One identifier sits at the center, and lines connect to every other thing you do. Insurance companies love knowledge graphs because they can deduce patterns. Police love them because they can track movements. Marketers love them because they can predict behavior.
For individuals, knowledge graphs are nightmares. Everything becomes correlated. Everything becomes knowable.
The scary part is that this happens gradually. First Aadhaar for government services. Then for banks. Most people don't object. It seems fine. Then hotels. Police systems. Wallets. Networking apps. Each step seems small. But the destination—total digital identity integration—arrived almost without anyone noticing.

Regulatory Gaps: Standards Without Enforcement
UIDAI has set standards for how Aadhaar data should be handled. They've issued guidelines. But guidelines aren't laws. And even laws are only as effective as enforcement.
When a hotel improperly stores Aadhaar credentials, who enforces the rules? UIDAI can audit them. But do they have the power to shut them down? Can they impose meaningful fines? Can individuals sue for damages?
Those are questions without clear answers. The legal framework is still forming.
More importantly, much of Aadhaar's expansion is happening through private companies. Google Wallet isn't a government system. Hotels aren't government systems. Even PATHIK, the police guest-monitoring platform, involves private vendors.
When the system spreads to private actors, regulatory control becomes harder. UIDAI can't audit every company using Aadhaar data. They don't have the resources. So standards get written, but enforcement is spotty.
This creates a situation where compliant companies follow the rules, but others cut corners. Users don't know the difference. They just see an Aadhaar verification option and trust it works the same everywhere.

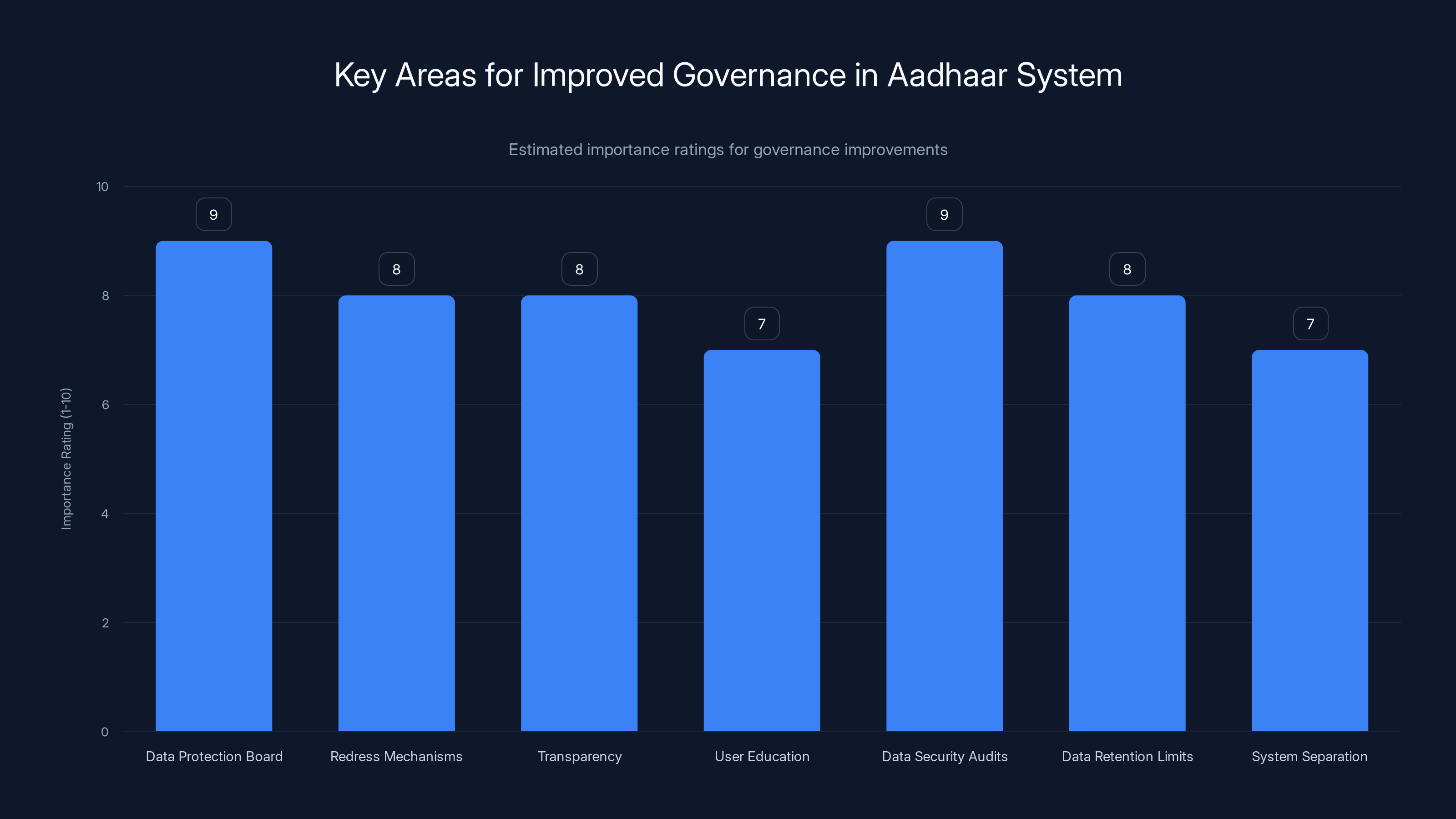
Improving governance in Aadhaar involves focusing on data protection, security audits, and transparency. Estimated data highlights these as key areas.
The Middle Path: How This Could Actually Work
None of this means Aadhaar expansion is necessarily bad. The selective data sharing concept is sound. The offline verification approach is smart. But it requires better execution than what's happening now.
Here's what would need to happen for this to work properly.
First, the Data Protection Board needs to exist. Not as an afterthought, but as an active reviewer of major expansions. Before Aadhaar integrates with police systems, the board should review it. Before mobile wallet integration, review it. Get public input. Flag risks. Require safeguards.
Second, redress mechanisms need teeth. When something goes wrong—data is breached, credentials are leaked, inaccurate information is shared—individuals need a realistic path to remedy. Not a bureaucratic nightmare that takes years. Quick fixes. Fair compensation. Real consequences for organizations that mishandle data.
Third, transparency reporting should be mandatory. UIDAI should publish regular reports on data requests from police. On database access. On breaches. On redress complaints. Individuals should know how their data is being used.
Fourth, meaningful consent requires education. The government should invest in helping people understand what Aadhaar integration means. Not propaganda. Real education. "When you use Aadhaar at a hotel, police can later query where you were." People deserve to know that.
Fifth, private companies integrating Aadhaar should face serious liability. If Google Wallet improperly handles Aadhaar data, Google should face meaningful penalties. Not just UIDAI issuing warnings, but legal liability that actually changes behavior.
Global Context: How Other Countries Handle Digital Identity
India isn't alone in building large-scale digital identity systems. But the speed and scope of Aadhaar's expansion is unusual.
Europe took a different approach. The EU's digital identity framework is federated. Multiple national systems can interoperate, but no single identifier connects everything. There's also the GDPR, which strictly limits how identity data can be used and requires explicit consent for many uses.
Singapore built a unified digital identity system, but it's much smaller (5 million people versus 1.4 billion). They also built sophisticated governance first, then scaled.
China built a facial recognition and ID system at massive scale. But it operates under different governance assumptions—privacy is less central to the framework.
India's situation is unique because it's trying to do what Europe did with governance, at a scale approaching China, with a population that's still developing digital literacy.
That's extraordinarily difficult. Get it right and it's transformative. Get it wrong and the consequences affect 1.4 billion people.

Industry Response: Companies Adopting Aadhaar
From the private sector's perspective, Aadhaar is incredibly valuable. It solves the identity problem. Hotels don't have to worry about fake registrations. Employers can verify workers. Platforms can reduce fraud.
Banks were early adopters. Using Aadhaar for know-your-customer compliance made onboarding much faster. Telecom companies followed. Insurance companies followed.
Now, with the new app and selective data sharing, the business case is even stronger. A hotel can verify a guest is over 18 without storing their full identity data. That reduces liability. That reduces storage costs. That reduces audit burden.
From a business perspective, it's a win-win. Consumers get convenience. Businesses get efficiency.
But here's the issue: business incentives and privacy incentives don't align. A business benefits from collecting and storing data. Privacy advocates worry about that collection and storage.
When the regulatory framework is weak, business incentives win. Companies collect more data than necessary, store it longer than necessary, and share it more broadly than necessary. Because they can. Because it creates business value.
That's not malicious. It's just how incentives work.

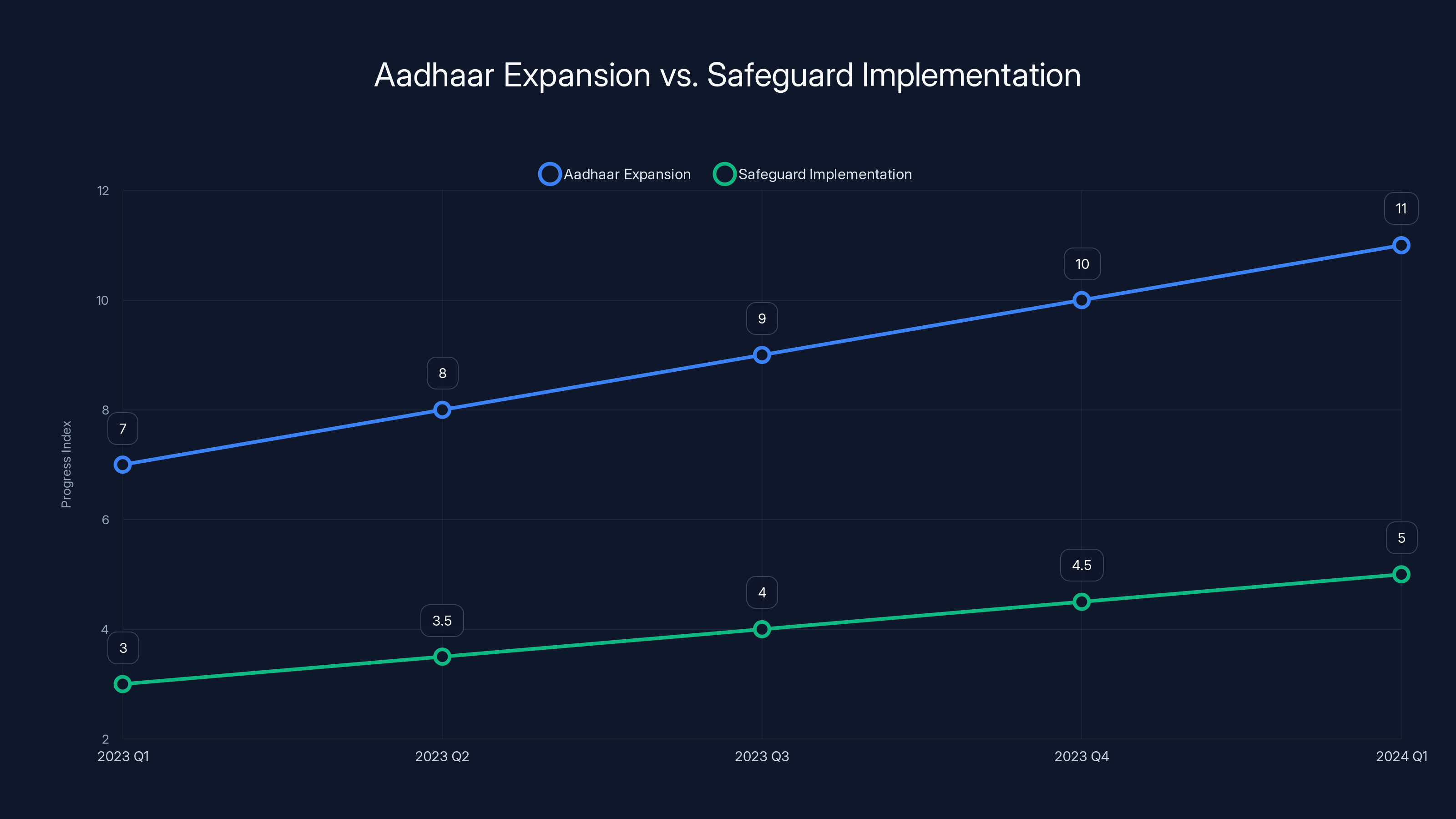
Aadhaar's expansion is estimated to be outpacing the implementation of safeguards, highlighting a potential risk in data protection (Estimated data).
Looking Ahead: What Changes Are Coming
Aadhaar won't stop expanding. The government has made that clear. The question is how it expands and what safeguards accompany that expansion.
We'll probably see more mobile wallet integration. Apple Wallet integration is likely because it's technically feasible and because the business case is strong.
We'll probably see more police and government agency adoption. Tracking. Identification. Verification. These are valuable for government operations.
We'll probably see more private sector adoption. Every company that needs identity verification will eventually use Aadhaar because it's integrated, accessible, and standard.
The Data Protection Board will probably form eventually. When it does, it will inherit a system that's already pervasive. Changing rules at that point will be much harder.
We might see better redress mechanisms. As more people experience issues with inaccurate data or improper sharing, political pressure for fixes will increase.
We might see better transparency. Public interest litigation and investigative journalism have a track record of forcing disclosure in India. Expect that to continue.
But the core pattern—expansion first, regulation later—is likely to continue unless there's political pressure to change it.
Real-World Implications: What This Means for Users
So, what does all of this actually mean for someone in India using Aadhaar?
In the short term, convenience. The app works. Verification is faster. Digital visiting cards are cool. Mobile wallet integration will be seamless.
In the medium term, normalization. Aadhaar verification becomes expected everywhere. Not providing it starts to feel suspicious. Opting out becomes harder.
In the long term, potential risk. If data handling improves and safeguards work, it's fine. If data handling stays sloppy and safeguards fail, you're living in a system where everything about your life is known and connected to a single identifier.
That's not theoretical risk. It's risk based on how large databases typically operate. Historical security failures. Normal human carelessness. Pressure to monetize data.
The upside of Aadhaar is massive. Better government service delivery. Reduced fraud. Faster verification. Real benefits for real people.
The downside risk is also massive. Total digital identity integration without adequate privacy safeguards.
Both are true simultaneously. That's what makes this so tricky.

Expert Perspectives: What Digital Rights Advocates Are Saying
The consensus among digital rights experts is consistent: expansion without protection.
SFLC.in's Prasanth Sugathan pointed out that the core problems remain unresolved. Database inaccuracies. Security lapses. Poor redress mechanisms. Those aren't going away. The new app doesn't fix them. It just creates new ways for those problems to propagate.
Access Now's Raman Jit Singh Chima emphasized the timing issue. The government is expanding a system that operates at a scale without equivalent regulatory maturity. That's not cautious governance. That's governance by momentum.
The pattern experts see is consistent: capability first, responsibility later. Build the system. Get adoption. Then worry about safeguards.
That approach might work if safeguards are quickly put in place. But history suggests they often aren't. The system becomes entrenched. Changing it becomes politically difficult.

The Path Forward: Better Governance, Not Less Technology
The answer isn't to stop Aadhaar expansion. That's probably impossible now and possibly undesirable. Digital identity is useful. Aadhaar works at a scale no other system comes close to.
The answer is better governance alongside technology.
That means the Data Protection Board needs to exist and function well. It means redress mechanisms need to be accessible and effective. It means transparency needs to be real, not cosmetic. It means private companies handling Aadhaar data face real liability.
It also means users need education. Not fear-mongering. Real information about how their data flows. What risks exist. What choices they have.
It means periodic audits of data security. Not once a year. Continuously. With public reporting.
It means limiting data retention. Just because you can store Aadhaar data forever doesn't mean you should. Retention limits reduce risk by reducing the amount of stored data.
It means separating systems. Police verification doesn't need to go to the same database as commercial verification. Age confirmation doesn't need the same access level as full identity verification.
None of this is difficult technically. All of it is difficult politically because it creates constraints on data use.
But constraints are what actually protect privacy. Without them, you get maximum data collection, maximum retention, maximum sharing. That's not a privacy-respecting system. It's a surveillance system with consent-based branding.

FAQ
What is Aadhaar exactly?
Aadhaar is India's massive biometric-based digital identity system that assigns a unique 12-digit number to individuals based on their fingerprints, iris scans, and demographic information. Since its launch in 2009, it has issued over 1.4 billion identity numbers and handles roughly 2.5 billion authentication transactions each month across banking, telecommunications, insurance, and government services. It was originally created to efficiently deliver government benefits and reduce fraud in the distribution of subsidies and public services.
How does the new Aadhaar app's selective data sharing work?
The new Aadhaar app allows users to share limited information about themselves without revealing their complete identity data. Instead of sharing your full Aadhaar number or complete birthdate, the app generates digital credentials that can prove specific facts about you—such as confirming you're over 18 or that you're a verified resident—without disclosing unnecessary personal details. This uses offline verification technology that doesn't require real-time queries to UIDAI's central database, enabling verification without constant internet connectivity.
What are the security concerns digital rights experts have raised?
Experts worry about several intersecting issues: Aadhaar has experienced previous security lapses including unauthorized database access and data circulation on the dark web, the database contains inaccuracies that harm users with poor redress mechanisms, and the system is expanding into new areas (police systems, hotels, mobile wallets) before India's Data Protection Board is even established to provide independent oversight. The expansion also multiplies the number of organizations storing Aadhaar data, creating more potential points of vulnerability and reducing UIDAI's ability to control how data is actually handled.
How does Aadhaar's integration with police systems affect privacy?
When hotels use Aadhaar for guest verification through police platforms like PATHIK, it creates a permanent government-accessible record of who stayed where and when. This transforms hotel records from local, manual systems into centralized, searchable databases. The system enables police to query movement patterns and location history in ways that would have been impossible with previous paper-based records, creating a surveillance capability at scale without equivalent legal oversight.
What is the Data Protection Board and why does it matter?
India's Data Protection Board is an independent oversight body meant to review how personal data is collected, used, and protected in systems like Aadhaar. The critical issue is that as of 2025, this board doesn't yet exist, meaning Aadhaar is expanding into police systems, mobile wallets, and everyday use without independent regulatory review. Once the board is established, changing governance rules will be much harder because the system will already be deeply embedded in society.
Can individuals control what data is shared through Aadhaar?
Theoretically yes—the new app is designed around selective sharing and consent. However, meaningful consent requires that people understand what they're consenting to and have genuine alternatives. Since Aadhaar has become quasi-mandatory for many services (phone plans, bank accounts, government benefits), and most users don't fully understand the downstream implications of their data use, "voluntary" consent operates under significant constraints. When something is effectively required for participation in modern Indian life, consent becomes less about choice and more about necessity.
What happens if there's an error in the Aadhaar database?
Errors do occur—biometric mismatches, duplicate enrollments, data entry mistakes—and the impact can be serious, preventing people from opening bank accounts or receiving government benefits. While redress mechanisms exist in theory, they're slow and bureaucratic. When the new app generates credentials based on potentially inaccurate database information, users might share incorrect data about themselves without realizing it, since the app reflects whatever is in the system, accurate or not.
How does mobile wallet integration change the risk profile?
Integrating Aadhaar into Google Wallet, Apple Wallet, and Samsung Wallet means identity data now sits alongside financial data in systems controlled by technology companies rather than UIDAI alone. While these companies have strong security, the expansion increases complexity and creates new attack surfaces. The integration also links identity to payment systems, creating a permanent record of transactions tied to verified identity in a way that didn't exist before.
What would better governance of Aadhaar look like?
Meaningful safeguards would include: establishing the Data Protection Board before expanding into new sectors, creating accessible and effective redress mechanisms for errors and breaches, requiring mandatory transparency reporting on police data requests and breaches, establishing strict data retention limits rather than storing information indefinitely, imposing real liability on private companies that improperly handle Aadhaar data, separating different types of verification (police queries shouldn't have access to commercial verification data), and providing genuine user education about data flows and privacy implications rather than just emphasizing convenience.
Is Aadhaar expansion definitely bad for privacy?
Not necessarily. The selective data sharing concept is sound, and offline verification is technically smart. The real issue is whether the governance structure evolves at the same pace as the technology. If robust safeguards, independent oversight, and meaningful redress mechanisms are put in place, expanded Aadhaar use can work reasonably well. If governance lags behind technology adoption—which is the current trajectory—then the system becomes increasingly risky. The outcome depends entirely on whether India's government prioritizes privacy protection as seriously as they're pursuing digital convenience.

The Bottom Line
Aadhaar's expansion is happening. That's a fact. The new app is downloading at 9 million installs monthly. Mobile wallets are integrating it. Police systems are querying it. Hotels are verifying against it. This isn't theoretical—it's active, operating infrastructure processing billions of transactions monthly.
The debate isn't about whether Aadhaar will expand. It's about whether the expansion happens with adequate safeguards or without them.
Right now, the trajectory suggests expansion is outpacing safeguards. The Data Protection Board doesn't exist. Redress mechanisms are weak. Security standards are guidelines without teeth. Consent is meaningful in theory but constrained in practice.
This doesn't mean things will definitely go wrong. The system might mature. The board might form and actually protect people. Companies might handle data carefully. Breaches might be rare.
But history of large databases suggests otherwise. They tend to sprawl. Data gets stored longer than necessary. More people get access than should. Security lapses happen. And once a system is pervasive, changing it becomes nearly impossible.
The ideal path forward would be: pause major expansions until the Data Protection Board exists and reviews them. Establish strong redress mechanisms. Require transparency reporting. Impose real liability on companies mishandling data. Invest in user education about what their consent actually means.
Will that happen? Probably not. Momentum favors expansion. The system works well enough that people use it. The convenience is real. The political will to slow things down doesn't exist.
So what you're watching is a massive digital identity system expanding faster than the rules keeping it honest can keep up. That's not necessarily a disaster. But it's a gamble. The house edge goes to whichever outcome—safeguards working or safeguards failing—happens to arrive first.
Right now, the system is winning.

Key Takeaways
- Aadhaar handles 2.5 billion monthly authentication transactions and issued 1.4 billion identity numbers, making it the world's largest digital identity system.
- The new Aadhaar app reached 9 million monthly installs by December 2025, rapidly replacing the older mAadhaar app, showing massive user adoption.
- Offline verification removes real-time database queries, enabling local credential generation but multiplying data copies and potential breach points.
- India's Data Protection Board—meant to provide independent oversight—hasn't been established yet despite Aadhaar expanding into police systems, wallets, and hotels.
- Historical security lapses including unauthorized database access and data circulation on the dark web raise credibility questions about selective data sharing's actual protection.
![Aadhaar's Expansion Into Wallets, Hotels, and Policing: What Privacy Advocates Worry About [2025]](https://tryrunable.com/blog/aadhaar-s-expansion-into-wallets-hotels-and-policing-what-pr/image-1-1770692787351.jpg)



