Future-Proof Your Privacy with Next-Generation VPN Encryption [2026]
Last month, I had a revelation while sipping my morning coffee. I realized that the world of online security is on the brink of a seismic shift. With World Quantum Day 2026 just around the corner, there's a palpable buzz surrounding the future of privacy and VPN encryption. It's not just about safeguarding your data against today's threats but preparing for tomorrow's quantum-powered universe.
TL; DR
- Quantum Computing: A game-changer in both solving complex problems and threatening current encryption standards, as discussed in The Quantum Insider.
- VPN Evolution: The advent of quantum-resistant VPNs to secure privacy in the quantum age.
- Implementation: Practical steps for integrating quantum-resistant protocols into existing systems.
- Challenges: Addressing the common pitfalls and hurdles in adopting new encryption technologies.
- Future Trends: Predictions on the evolution of encryption technologies and best practices.

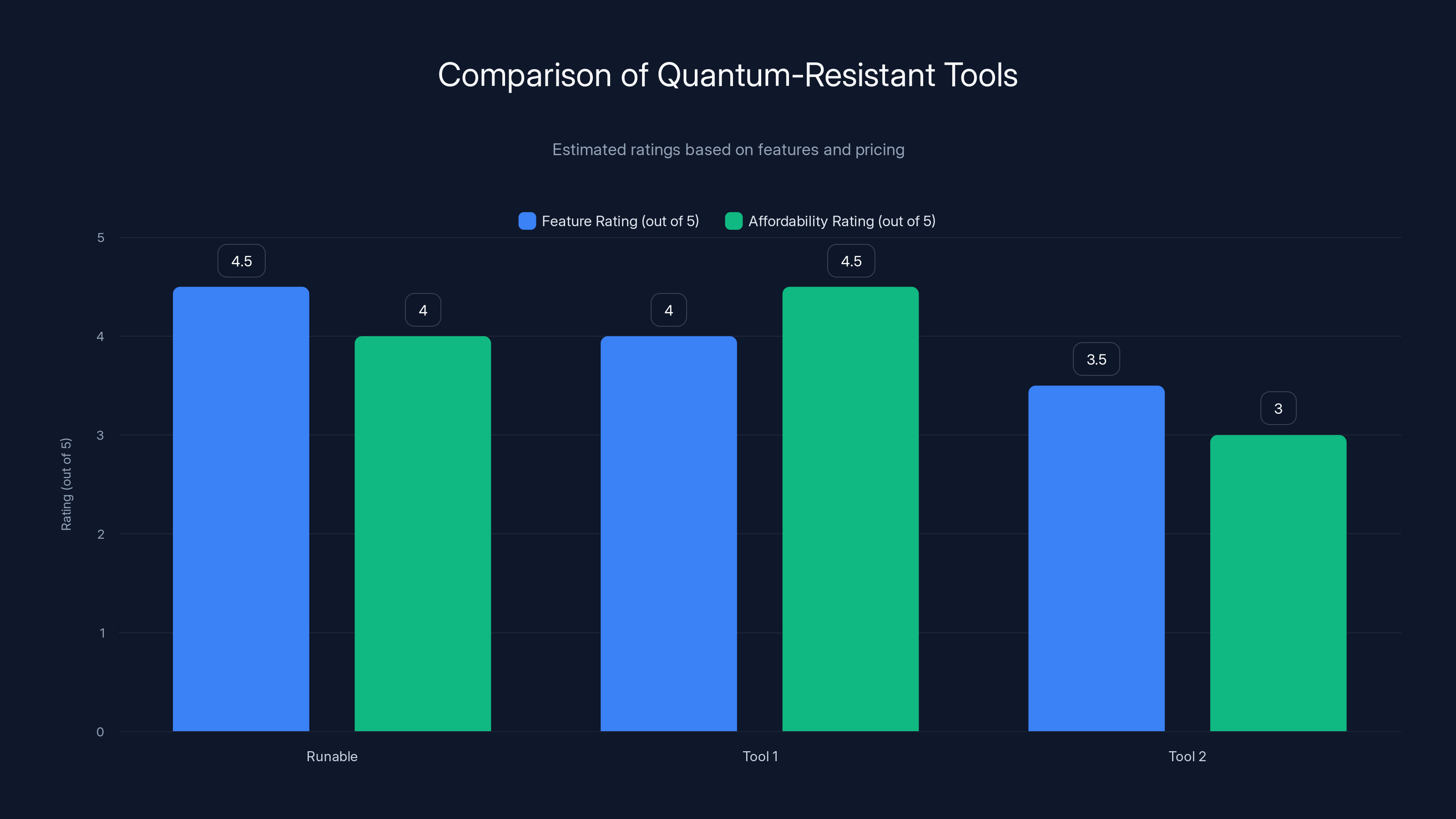
Runable scores high on features with AI automation, while Tool 1 offers great affordability with its free trial. Estimated data.
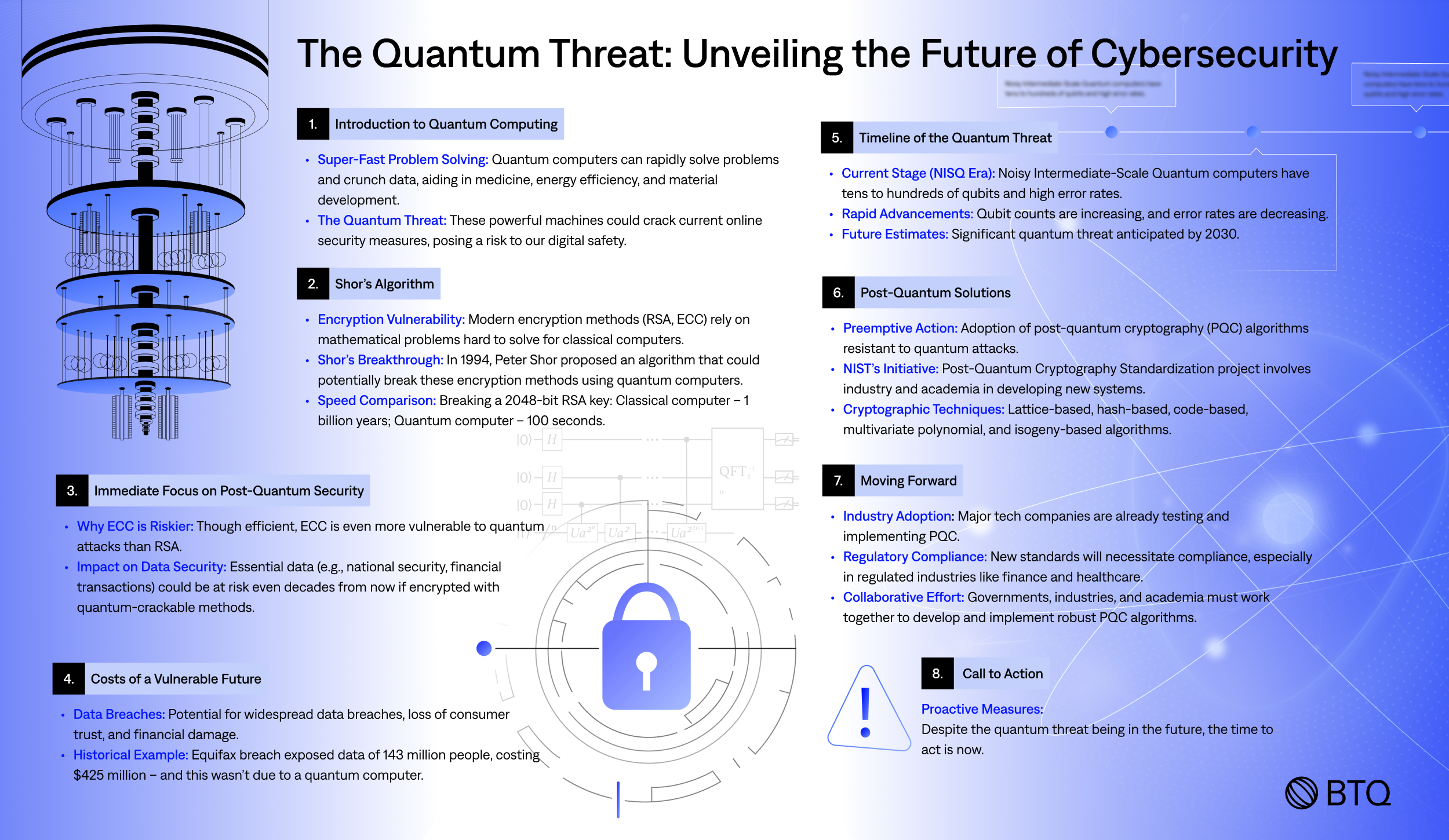
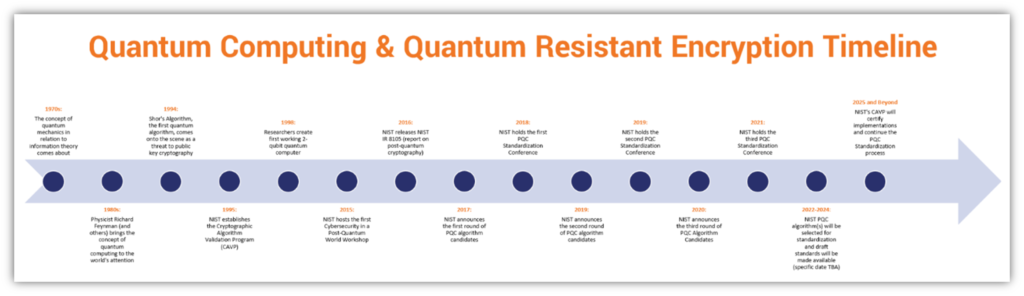
Understanding Quantum Computing
Quantum computing isn't just the stuff of science fiction anymore. It's here, and it's powerful enough to break traditional encryption methods. Unlike classical computers that use bits, quantum computers operate with qubits. This allows them to process a vast amount of data simultaneously, making them exponentially faster at cracking encryption algorithms, as explained in Colby News.
The Quantum Threat to Current Encryption
Today, most VPNs rely on RSA or ECC (Elliptic Curve Cryptography) to secure data. These algorithms are robust against classical attacks but could be easily dismantled by a sufficiently advanced quantum computer. Shor's algorithm, for instance, can factor large integers exponentially faster than the best-known classical algorithm, shaking the foundations of RSA, as noted by Nature.
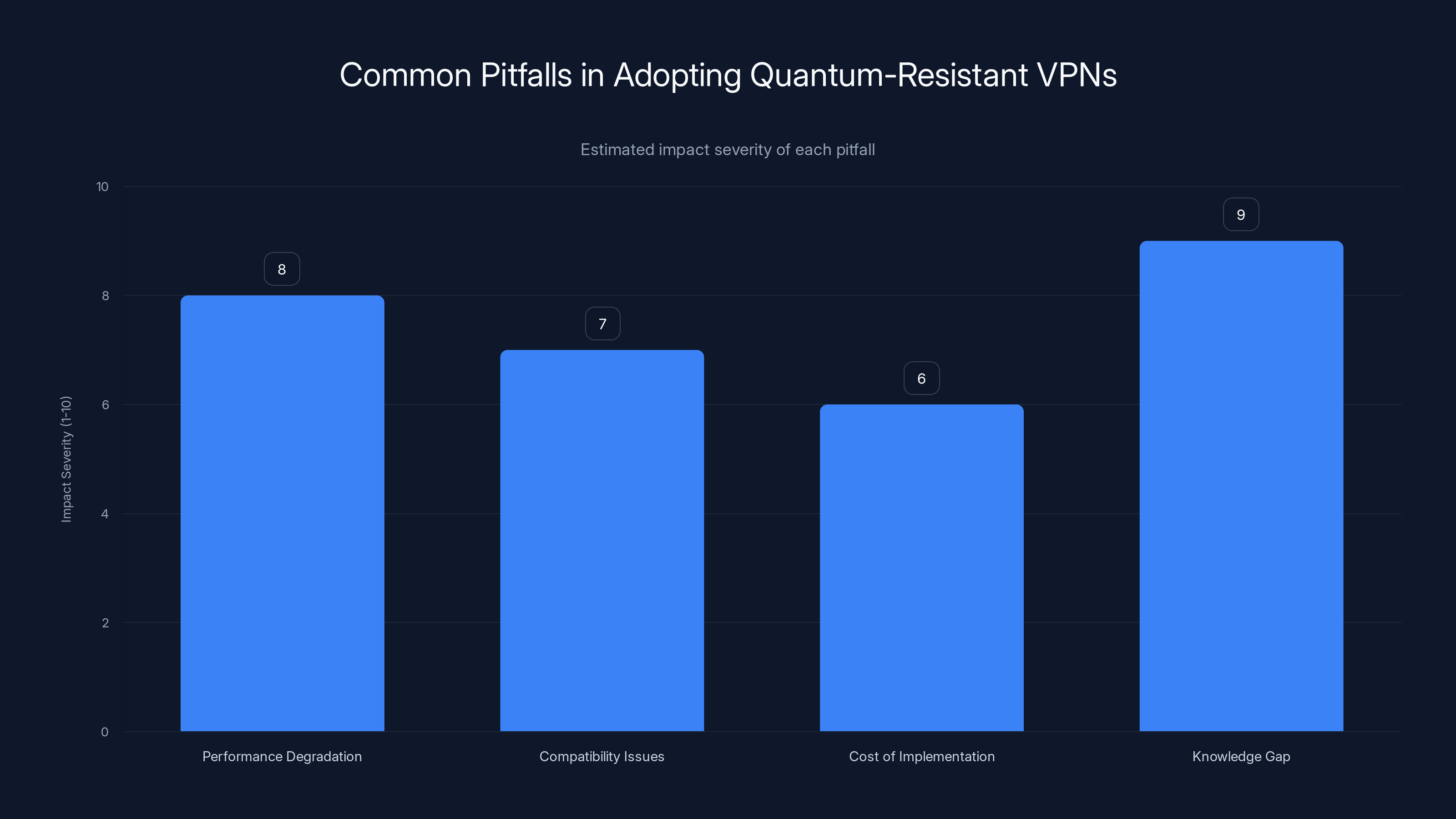
Performance degradation and knowledge gap are the most severe challenges when adopting quantum-resistant VPNs. (Estimated data)
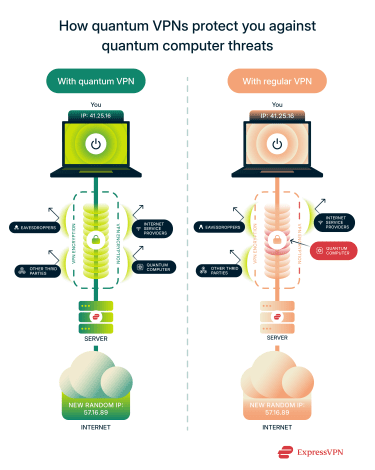
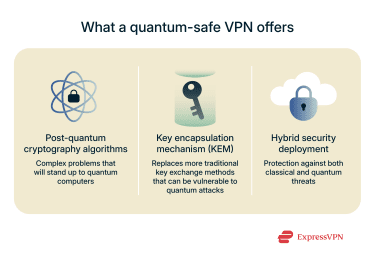
The Next Generation of VPN Encryption
As we brace for the quantum era, next-gen VPNs are stepping up with quantum-resistant encryption. These VPNs use algorithms that are impervious to both classical and quantum attacks, ensuring that your data remains secure, as highlighted by CyberScoop.
Quantum-Resistant Algorithms
Here's a look at some of the front-runners:
- Lattice-Based Cryptography: Uses complex mathematical structures, known for their resilience against quantum attacks.
- Hash-Based Cryptography: Builds on the security of hash functions, providing a robust alternative.
- Multivariate Quadratic Equations: A novel approach leveraging the complexity of solving multivariate polynomial equations.
- Code-Based Cryptography: Uses error-correcting codes, a time-tested method with a quantum twist.
Each of these algorithms offers unique benefits and trade-offs, making them suitable for different applications, as detailed in The Quantum Insider's report on quantum cryptography companies.
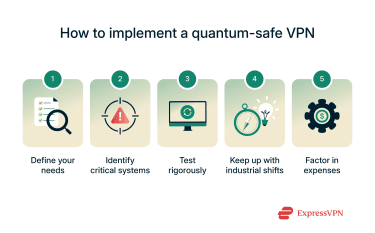
Practical Implementation of Quantum-Resistant VPNs
Transitioning to quantum-resistant VPNs isn't just about flipping a switch. It requires a thoughtful approach to integrate these advanced protocols into existing infrastructure.
Steps for Integration
- Assess Current Infrastructure: Understand your current encryption methods and potential vulnerabilities.
- Research Quantum-Resistant Protocols: Evaluate which algorithms best meet your security needs.
- Pilot Testing: Implement quantum-resistant protocols in a controlled environment to gauge performance and compatibility.
- Gradual Rollout: Transition existing systems to quantum-resistant encryption in phases to minimize disruption.
- Continuous Monitoring: Regularly update and monitor encryption methods to address emerging threats.
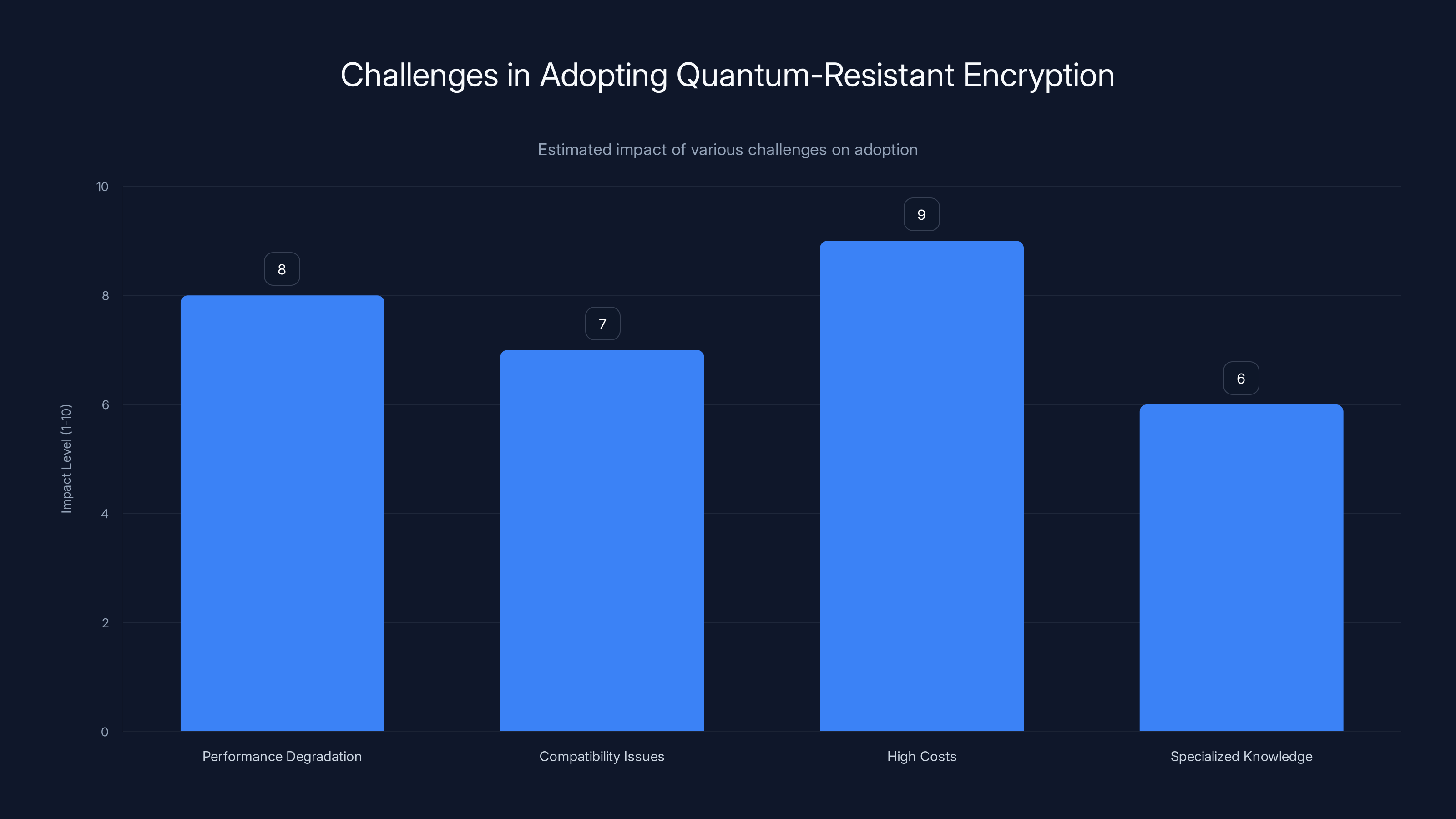
High costs and performance degradation are the most significant challenges in adopting quantum-resistant encryption. (Estimated data)
Common Pitfalls and Solutions
As with any technological shift, adopting quantum-resistant VPNs comes with its own set of challenges.
Pitfall 1: Performance Degradation
Quantum-resistant algorithms can be computationally intensive, potentially slowing down network speeds. To mitigate this, consider optimizing network architecture and leveraging hardware acceleration where possible.
Pitfall 2: Compatibility Issues
Older systems may not be compatible with new encryption standards. Address this by ensuring that all systems are updated and capable of supporting new protocols.
Pitfall 3: Cost of Implementation
While the initial investment might be significant, the long-term benefits of staying ahead of quantum threats far outweigh the costs. Consider phased investments to spread out expenses, as suggested by Tech Times.
Pitfall 4: Knowledge Gap
The complexity of quantum-resistant algorithms can be daunting. Providing training and resources for your team is essential to ensure a smooth transition.
Future Trends in VPN Encryption
As we look towards the future, several trends are emerging in the world of encryption and VPNs.
Trend 1: Increased Adoption of Quantum-Resistant Protocols
As quantum computing becomes more mainstream, industries across the board will adopt quantum-resistant protocols, not just in VPNs but in all areas of cybersecurity, as noted by The Quantum Insider.
Trend 2: Integration with AI and Machine Learning
AI and machine learning will play crucial roles in optimizing encryption algorithms, predicting threats, and automating security measures.
Trend 3: Decentralized VPN Networks
The future might see a rise in decentralized VPN networks, leveraging blockchain technology to enhance security and transparency.
Trend 4: Increased Regulation and Standards
Governments and regulatory bodies will likely introduce new standards for quantum-resistant encryption, driving widespread adoption and compliance.

Recommendations for Future-Proofing Your Privacy
- Stay Informed: Keep up-to-date with the latest developments in quantum computing and encryption technologies, as advised by Stock Titan.
- Invest in Quantum-Resistant Technologies: Don't wait for quantum computers to become mainstream. Start investing in quantum-resistant technologies now.
- Educate Your Team: Ensure your team understands the implications of quantum computing on cybersecurity and the steps needed to mitigate risks.
- Collaborate with Experts: Work with cybersecurity experts and consultants to develop a robust strategy for quantum resistance.
- Adopt a Multi-Layered Security Approach: Combine quantum-resistant VPNs with other security measures for a comprehensive defense.
Conclusion
As we celebrate World Quantum Day 2026, it's clear that the quantum age is upon us. While it brings incredible opportunities, it also poses significant challenges to our current understanding of cybersecurity. By embracing next-generation VPN encryption and staying ahead of the curve, you can ensure your privacy remains intact in this brave new world.
FAQ
What is Quantum Computing?
Quantum computing is a type of computing that leverages the principles of quantum mechanics to process information in fundamentally different ways than classical computers.
How does Quantum Computing Impact VPN Encryption?
Quantum computing can break traditional encryption algorithms, necessitating the development of quantum-resistant protocols to secure data.
What Are Quantum-Resistant Algorithms?
Quantum-resistant algorithms are cryptographic methods designed to withstand attacks from quantum computers. Examples include lattice-based, hash-based, and code-based cryptography.
How Can I Implement Quantum-Resistant VPNs?
Start by assessing your current infrastructure, researching suitable protocols, and gradually integrating them into your systems with continuous monitoring.
What Are the Main Challenges in Adopting Quantum-Resistant Encryption?
Challenges include performance degradation, compatibility issues, high costs, and the need for specialized knowledge.
What Future Trends Should I Watch for in VPN Encryption?
Look for trends such as increased adoption of quantum-resistant protocols, AI integration, decentralized networks, and regulatory changes.
How Can I Future-Proof My Privacy?
Stay informed, invest in quantum-resistant technologies, educate your team, collaborate with experts, and adopt a multi-layered security approach.
Key Takeaways:
- Quantum computing poses a real threat to current encryption standards.
- Next-gen VPNs with quantum-resistant encryption are essential for future-proofing privacy.
- Implementing these technologies requires careful planning and investment.
- Staying informed and proactive is crucial in the fast-evolving landscape of cybersecurity.
The Best Quantum-Resistant Tools at a Glance
| Tool | Best For | Standout Feature | Pricing |
|---|---|---|---|
| Runable | AI automation | AI agents for presentations, docs, reports, images, videos | $9/month |
| Tool 1 | Quantum encryption | Lattice-based cryptography | Free trial available |
| Tool 2 | Data security | Code-based cryptography | By request |
Quick Navigation:
- Runable for AI-powered presentations, documents, reports, images, videos
- Tool 1 for quantum encryption
- Tool 2 for data security
Future-proofing your privacy is not just a necessity, but a responsibility in today's tech-driven world. Embrace the change, and you'll be ready for whatever the quantum future holds.
![Future-Proof Your Privacy with Next-Generation VPN Encryption [2026]](https://tryrunable.com/blog/future-proof-your-privacy-with-next-generation-vpn-encryptio/image-1-1776181084506.jpg)



