Introduction
Last year, a series of cyberattacks linked to Iranian hacker groups, such as the so-called "Charming Kitten," have alarmed global cybersecurity experts. These groups have been employing cunning Cold War-era espionage tactics, combined with fake digital identities, to infiltrate systems and steal sensitive data from users of major tech companies like Apple and Microsoft.
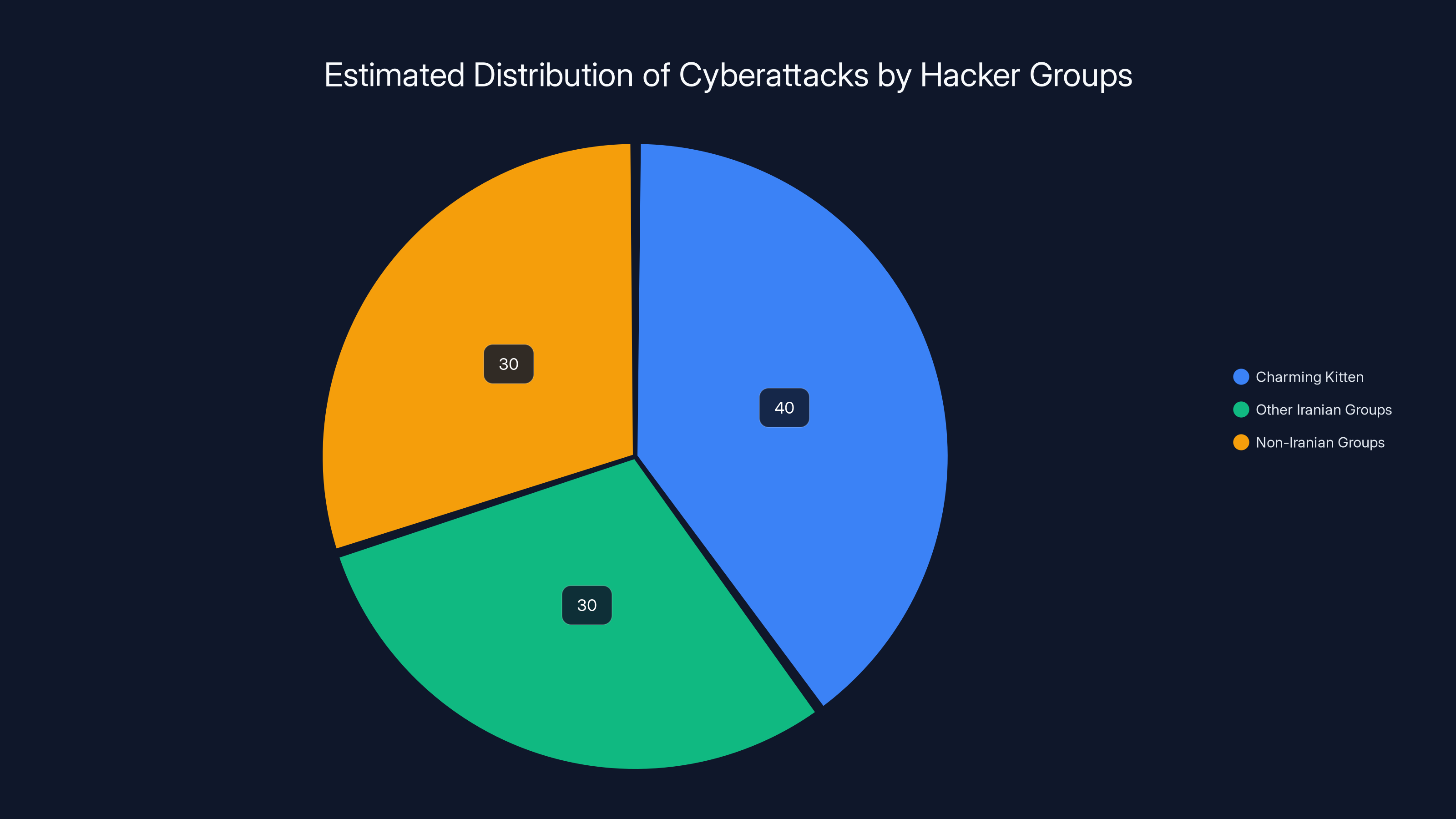
Charming Kitten is estimated to be responsible for 40% of recent cyberattacks linked to Iranian groups, highlighting their significant role in global cybersecurity threats. Estimated data.
TL; DR
- Cold War Tactics Revived: Iranian hackers use deception and psychological manipulation instead of advanced technical exploits.
- Targeted Attacks: Focused on Apple and Microsoft users, exploiting trust through fake identities.
- Digital Espionage: Use of phishing, social engineering, and malware to extract secrets.
- User Awareness: Emphasizing the importance of skepticism and vigilance in digital interactions.
- Future Threats: Anticipation of more sophisticated hybrid attacks combining old and new tactics.

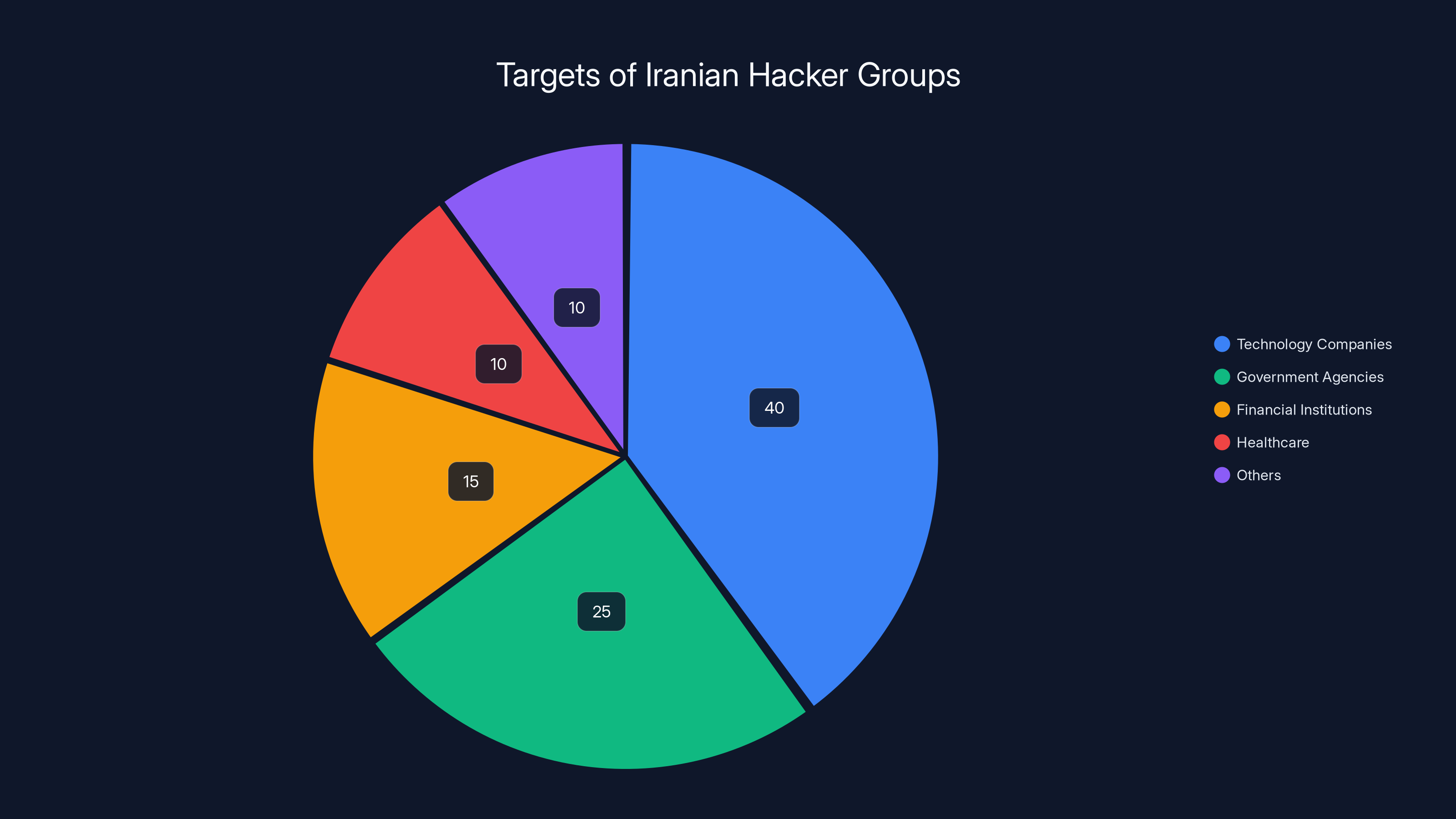
Estimated data shows technology companies like Apple and Microsoft are prime targets, comprising 40% of Iranian hacker attacks.
Understanding the Threat Landscape
Iranian hackers are not just another group of cyber criminals. They stand out due to their strategic use of deception and manipulation over brute-force technical attacks. This approach mirrors Cold War-era espionage, where the focus was on misleading and misdirection rather than direct confrontation.
A Brief History of Espionage
During the Cold War, espionage was a game of shadows, where intelligence agencies used spies to gain strategic advantages. Today, hacker groups like Charming Kitten have adapted these techniques for the digital age. They create fake personas, develop elaborate backstories, and infiltrate networks by gaining the trust of unsuspecting targets.
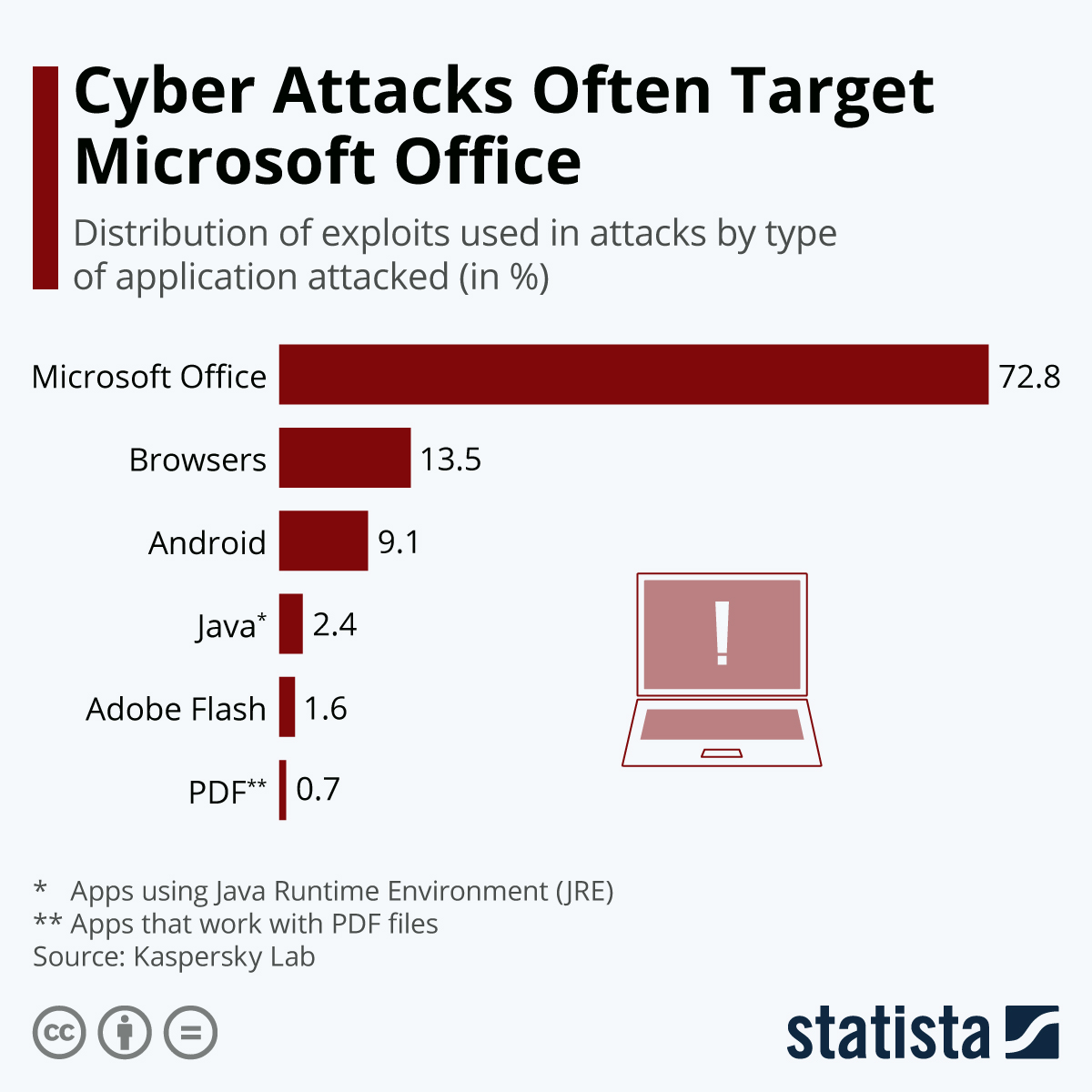
Why Apple and Microsoft?
Apple and Microsoft are prime targets due to their massive user base and the sensitive nature of the data they handle. By compromising these systems, hackers can access valuable information, from personal data to proprietary software.
The Tools of Deception: Cold War Meets Cyber Age
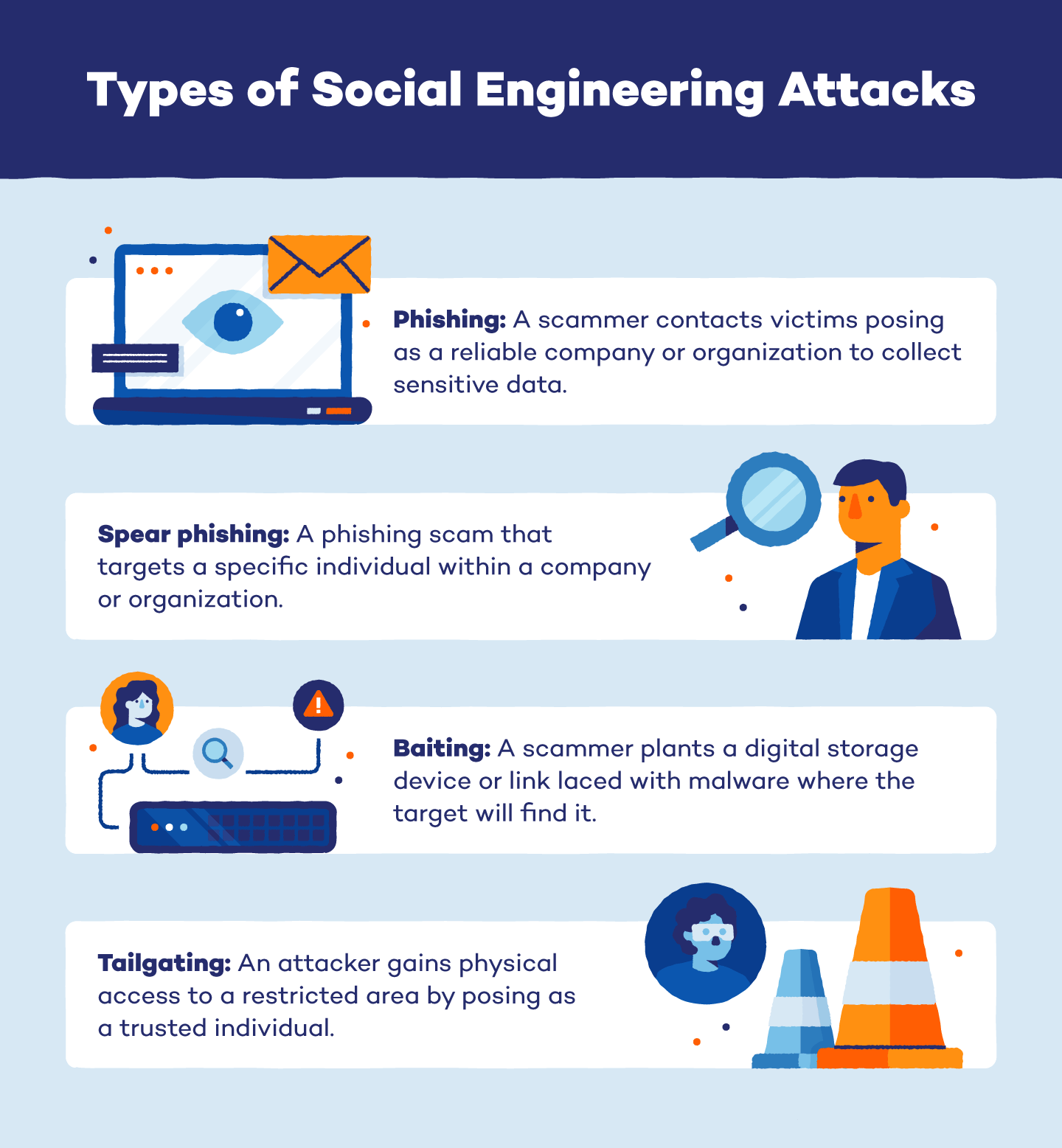
The tools used by these hackers are not technically advanced but are remarkably effective. They include phishing emails, fake social media profiles, and sophisticated social engineering techniques.
Phishing and Social Engineering
Phishing remains the cornerstone of these attacks. Hackers send emails that appear to be from trusted sources, tricking users into revealing passwords or clicking on malicious links. According to Cybersecurity Insiders, phishing attacks account for over 90% of data breaches.
- Example: A user receives an email from what appears to be Apple Support, urging them to reset their password due to a security threat.
Fake Digital Identities
Creating convincing fake identities is a skill honed by these hackers. They build detailed personas on social media, complete with friends, education history, and professional connections.
- Use Case: A hacker posing as a recruitment agent might reach out to a tech employee on LinkedIn, offering a lucrative job opportunity that requires sharing confidential information.
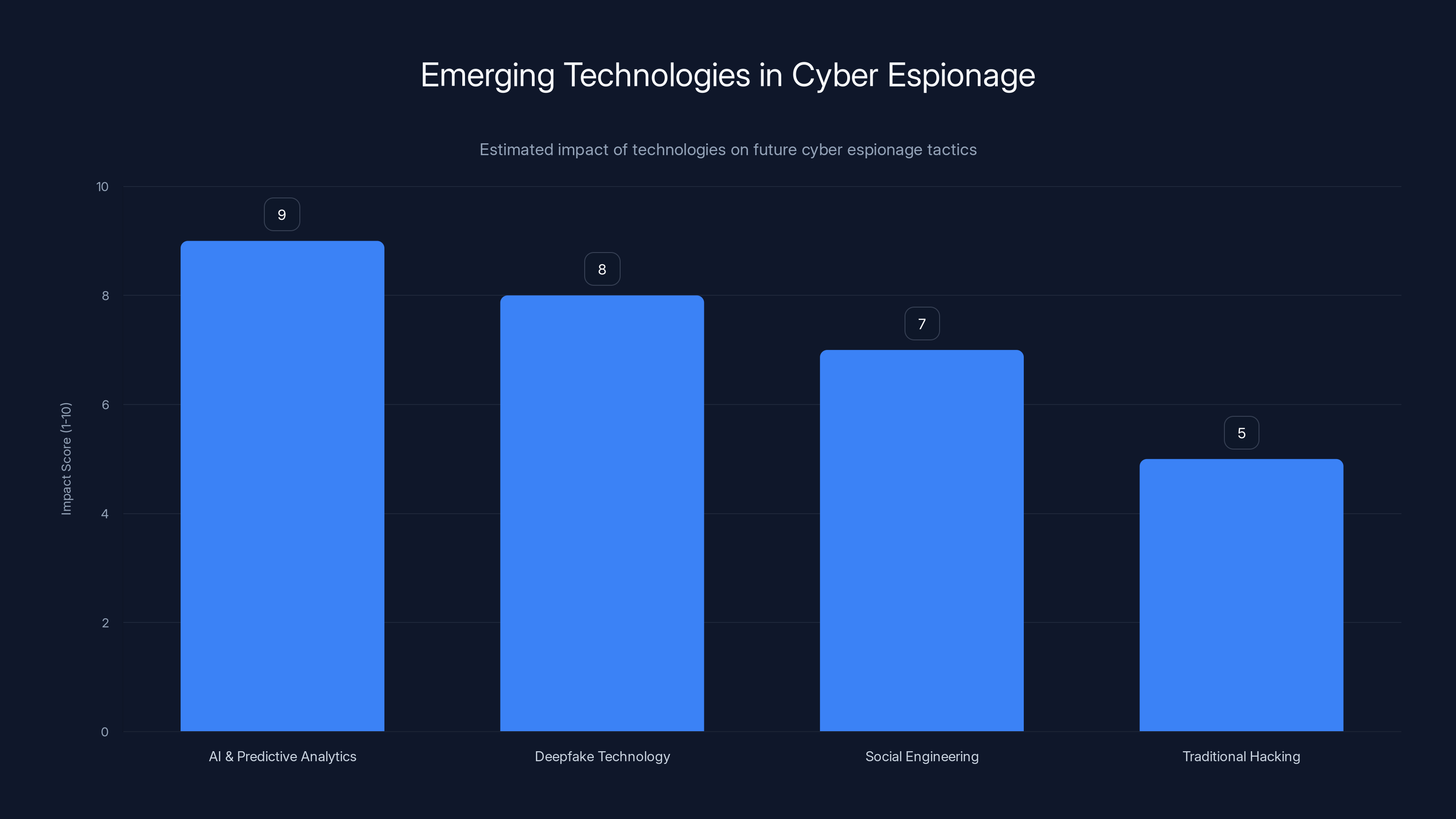
AI and predictive analytics are expected to have the highest impact on future cyber espionage, followed closely by deepfake technology. Estimated data.
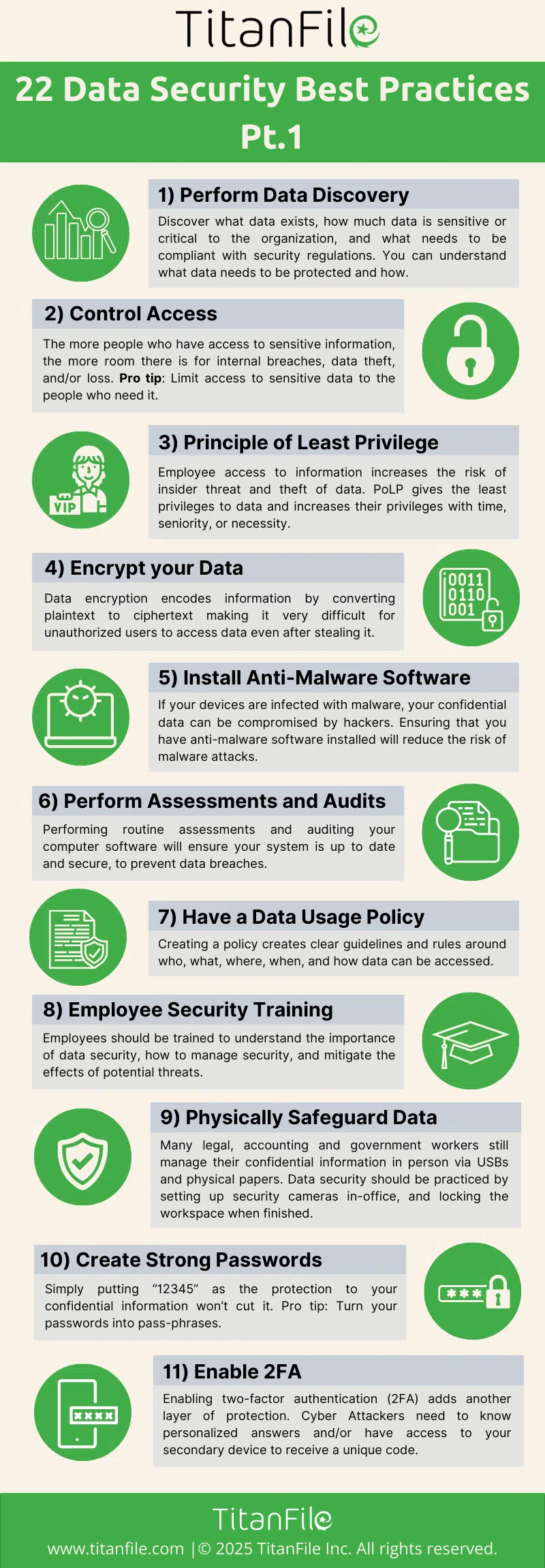
Best Practices for Protecting Against Digital Deception
To defend against these threats, organizations and individuals must cultivate a culture of vigilance and skepticism.
Implementing Security Awareness Programs
- Training: Regularly educate employees about the latest phishing tactics and how to recognize suspicious behavior. Resources like SANS Security Awareness offer comprehensive training programs.
- Simulations: Conduct phishing simulations to test employee responses and resilience.
Enhancing Technical Defenses
- Multi-Factor Authentication (MFA): Add an extra layer of security by requiring multiple forms of verification. According to CSO Online, MFA can block over 99.9% of account compromise attacks.
- Email Filtering: Use advanced email filters to detect and block phishing attempts.
Common Pitfalls and Solutions
Despite awareness efforts, common mistakes still leave systems vulnerable.
Pitfall: Overconfidence in Existing Security Measures
Many organizations believe their security systems are infallible, leading to complacency.
- Solution: Regularly update and audit security measures to address new threats and vulnerabilities. Gartner emphasizes the importance of continuous security assessments.
Pitfall: Ignoring Social Media Threats
Employees often overlook the risks posed by social media interactions.
- Solution: Implement guidelines and training on safe social media practices. According to Forbes, social media guidelines are crucial for reducing cyber risks.

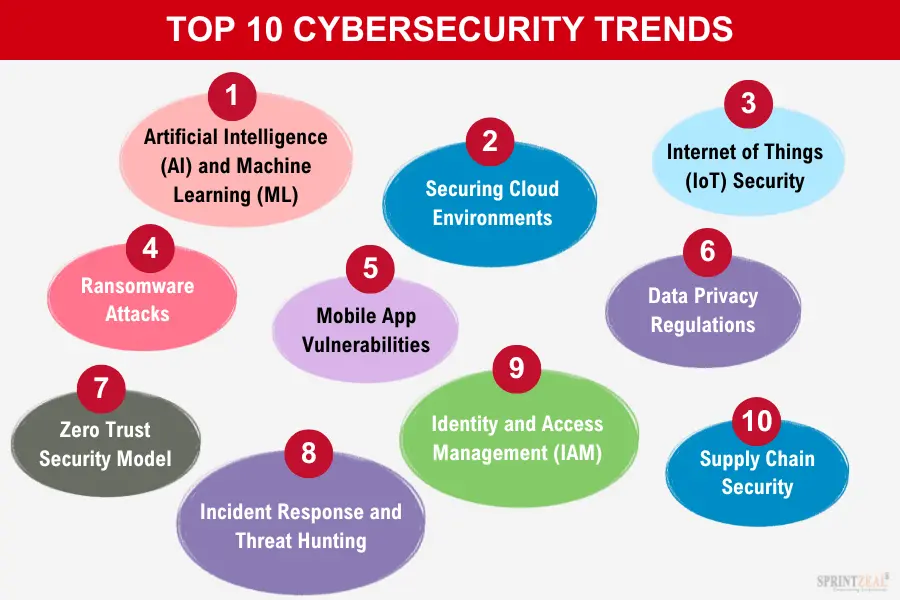
Future Trends in Cyber Espionage
As hackers continue to evolve, we can expect to see more sophisticated attacks that blend traditional espionage tactics with modern technology.
Predictive Analytics and AI
Hackers are likely to use AI to enhance their social engineering efforts, analyzing data to predict and manipulate target behavior more effectively. McKinsey reports that AI can significantly improve the accuracy and impact of cyberattacks.
- Example: An AI-powered tool could analyze a target's social media activity to craft highly personalized phishing messages.
The Rise of Deepfake Technology
Deepfake technology poses a new threat, allowing hackers to create realistic fake videos and audio to deceive targets. Wired highlights the growing concern over deepfakes in cybersecurity.
- Recommendation: Invest in tools that can detect deepfakes and authenticate communication channels.
Conclusion
The battle against cyber espionage is ongoing and complex. By understanding the tactics used by hacker groups like Charming Kitten, we can better prepare and defend against their attacks. Organizations must remain vigilant, continually updating their defenses and educating their teams to stay ahead in this digital arms race.

FAQ
What is digital deception in hacking?
Digital deception involves using fake identities and social engineering to manipulate targets into revealing sensitive information or granting access to secure systems.
How can organizations protect themselves from phishing attacks?
Implementing multi-factor authentication, conducting regular security training, and using advanced email filtering are effective ways to protect against phishing attacks.
What are the signs of a phishing attempt?
Common signs include emails with urgent language, requests for personal information, and links to unfamiliar websites.
How do hackers create convincing fake identities?
Hackers use publicly available information and social media platforms to build detailed and believable fake personas.
Why are Apple and Microsoft frequent targets for hackers?
Their vast user bases and the sensitive nature of the data they handle make them attractive targets for hackers seeking valuable information.
What is the role of AI in modern cyber espionage?
AI can enhance social engineering efforts by providing insights into target behavior and crafting personalized phishing messages.
How can individuals stay safe from digital espionage?
Stay informed about the latest threats, use strong passwords, enable multi-factor authentication, and be cautious of unsolicited communications.
What future trends should we watch for in cyber espionage?
Expect more sophisticated attacks involving AI, deepfakes, and a blend of traditional and modern espionage techniques.
Key Takeaways
- Iranian hackers revive Cold War tactics, using deception over technical exploits.
- Apple and Microsoft users are prime targets due to their data sensitivity.
- Phishing and fake digital identities are key tools for these hackers.
- Security awareness is crucial to defend against these sophisticated attacks.
- Expect future cyber espionage to integrate AI and deepfake technologies.
Related Articles
- Exposing the Cracks: Syria’s Digital Security Challenges in the Modern Era [2025]
- Hackers Are Posting the Claude Code Leak With Bonus Malware | WIRED
- Anthropic's Potential Expansion in London: Opportunities and Challenges [2025]
- The iPhone 17 Pro Max: Capturing the Cosmos with Artemis II [2025]
- Why AI Agents are Indispensable in Today's Work Environment [2025]
- Rebellions' Rack-Scale AI Systems: A New Era in Data Center Efficiency [2025]
![Iranian Hackers: Cold War Tactics and Digital Deceptions [2025]](https://tryrunable.com/blog/iranian-hackers-cold-war-tactics-and-digital-deceptions-2025/image-1-1775414032312.jpg)



