North Korean Identity Theft: How One Man's Scheme Infiltrated Dozens of US Tech Companies
In early 2026, a federal court handed down a five-year prison sentence that exposed one of the most brazen and geopolitically consequential schemes to hit American tech companies in recent memory. The defendant wasn't a disgruntled insider or a sophisticated hacker. He was a 29-year-old Ukrainian named Oleksandr Didenko who built a marketplace—literally called Upworksell—that let people buy or rent stolen identities of American citizens. The purpose? To help North Korean workers bypass background checks and secure legitimate employment at US firms, funneling their salaries back to Pyongyang to fund nuclear weapons development as reported by CyberScoop.
This wasn't some fringe operation. The Justice Department says Didenko handled more than 870 stolen identities. He organized "laptop farms"—rooms packed with open computers—across California, Tennessee, and Virginia. North Korean workers logged into these machines remotely, appearing to be physically present in the United States while actually working from overseas. They took jobs as software developers, data analysts, cybersecurity specialists, and other technical roles that paid six figures in some cases according to The Register.
What makes this case so significant is that it represents a collision of three major national security threats: sanctions evasion, employment fraud, and intellectual property theft. The North Korean regime, cut off from the global financial system by international sanctions, has become increasingly creative about generating hard currency. Tech companies, desperate to fill engineering roles, often fail to catch sophisticated fraud schemes. And somewhere in between, there's a massive vulnerability in how we verify who people really are as detailed by The Wall Street Journal.
This article digs into how the scheme actually worked, why it was so effective, what it tells us about North Korean cyber operations, and what companies and regulators are doing to stop it from happening again.
TL; DR
- Oleksandr Didenko, a Ukrainian, ran Upworksell, a website where people could buy or rent 870+ stolen American identities to apply for US jobs as noted by The Record.
- North Korean workers used these fake identities to get hired as software developers and other tech roles, with salaries funneled back to fund the regime's nuclear program according to CyberScoop.
- The scheme involved "laptop farms"—rooms full of computers in California, Tennessee, and Virginia—where North Koreans worked remotely while appearing to be in the US as reported by Defcros News.
- North Korean IT workers are described as a "triple threat" because they violate sanctions, steal company data, and later extort victims as highlighted by CyberScoop.
- Didenko was arrested by Polish authorities, extradited to the US, and sentenced to five years in prison after pleading guilty according to Help Net Security.
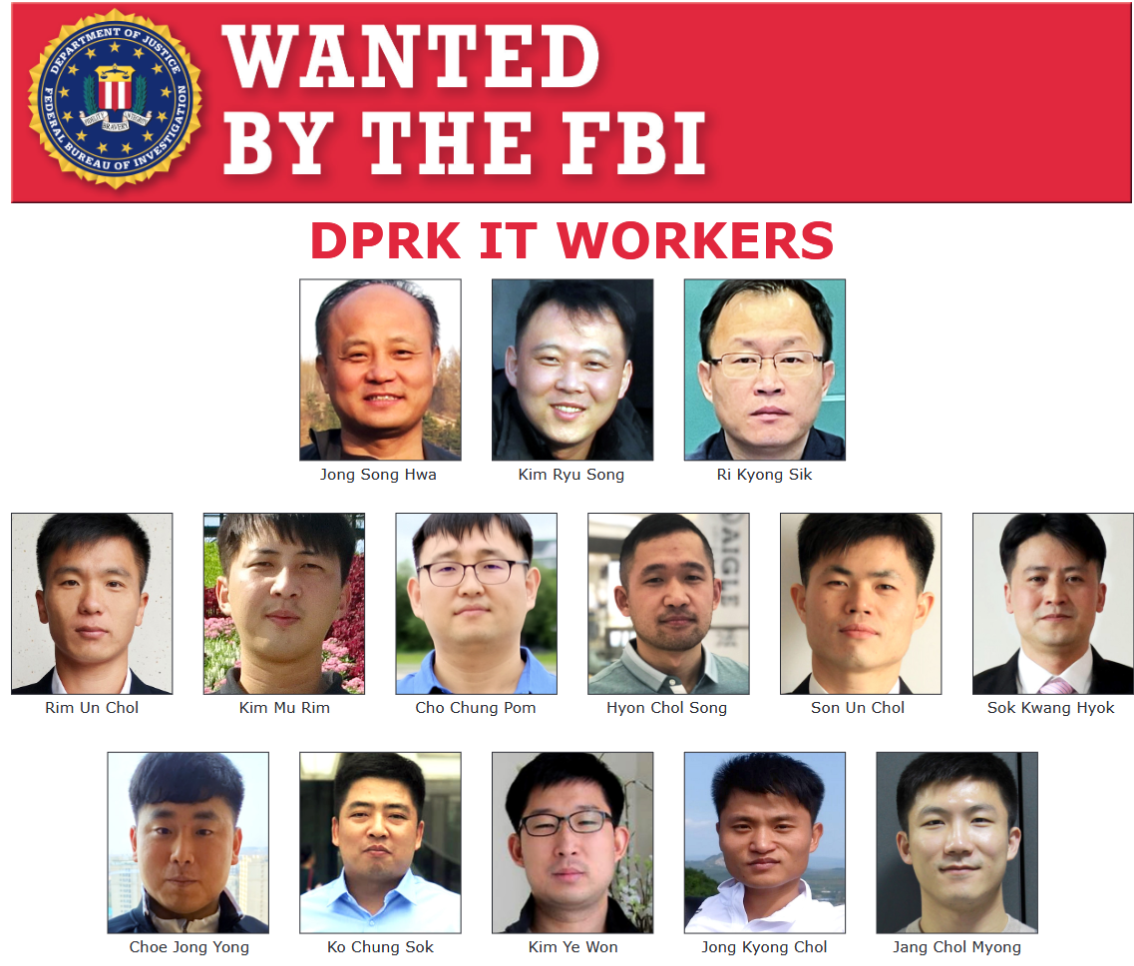
- This is part of a larger pattern: the FBI and Crowd Strike have seen a sharp rise in North Korean workers infiltrating American tech companies as noted by the Institute for the Study of War.

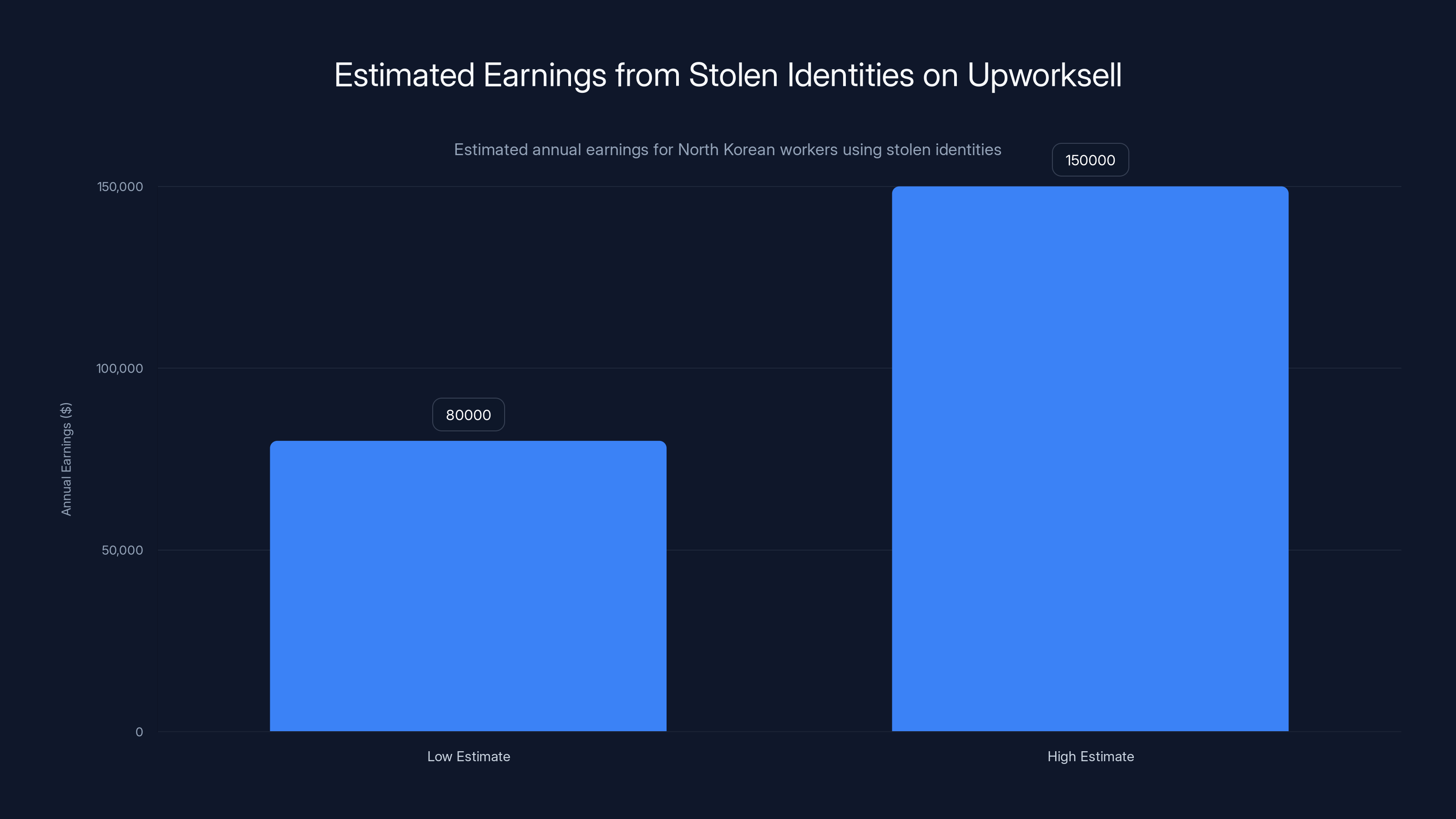
Estimated earnings for North Korean workers using stolen identities range from
The Upworksell Marketplace: A Store for Stolen Identities
Here's the straightforward part first. Oleksandr Didenko set up a website called Upworksell. If you visited it, you could browse a catalog of stolen identities—names, Social Security numbers, birth dates, addresses—all belonging to real American citizens. The site functioned like any other marketplace. You could buy an identity outright, or you could rent one for a specific period. The pricing was presumably tiered based on the quality and credibility of the identity, though exact prices aren't public as reported by CyberScoop.
Who were the customers? Primarily overseas workers, especially those from North Korea, who wanted to apply for jobs at US companies. The economics made sense for them. A North Korean worker earning a legitimate US salary could be making
The genius of Upworksell wasn't technological. It was operational. Didenko didn't hack into background check databases or create sophisticated fake documentation. Instead, he exploited a simple fact: most US hiring processes, no matter how thorough, rely on third-party background check companies. Those companies verify information against public records, databases, and previous employment history. If you had a stolen identity that matched all that data perfectly—because it was a real person's identity—the checks would pass as detailed by CyberScoop.
When a North Korean applicant submitted a resume under a stolen American name and provided an address where they had a "laptop farm" set up, emails would be checked at that address, phone calls would go to that location, and everything would appear legitimate. Video interviews could happen on Zoom from anywhere in the world, but the employer thought they were hiring an American worker or at least someone physically located in America as noted by CyberScoop.
The timing was also important. This scheme worked especially well during the pandemic and post-pandemic years when remote work became normalized. Before 2020, asking someone to work from home full-time was unusual. After 2020, it became standard. A software developer working from home in California? Completely normal. The fact that "California" was actually just a room with laptops in somebody's house, and those laptops were being accessed from Pyongyang, went undetected for years as reported by CyberScoop.
How North Korean Workers Infiltrated US Tech Companies
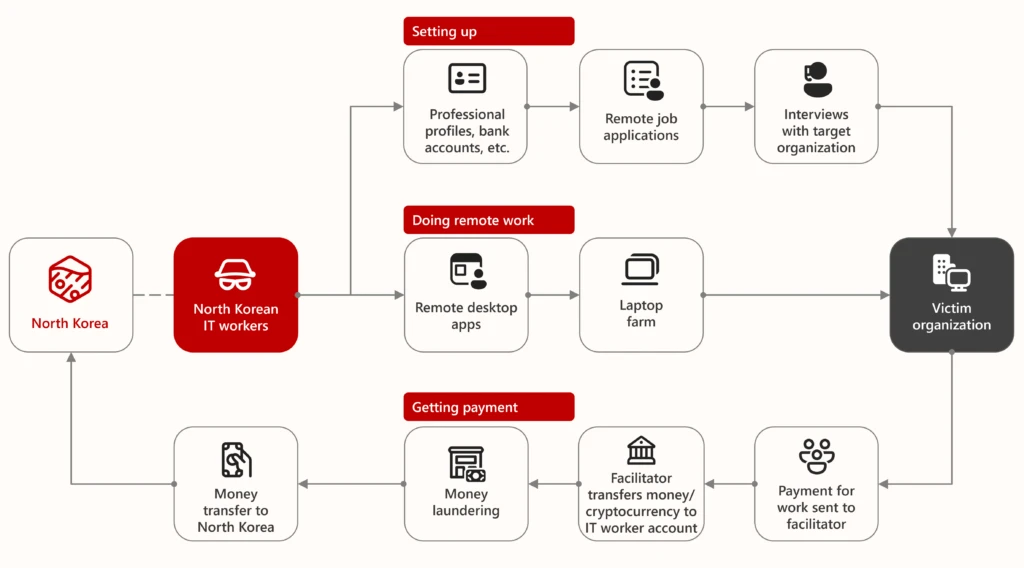
Once Didenko supplied the stolen identity, the practical execution required coordination across multiple parties. First, someone needed to physically receive packages and host the equipment. That's where the "laptop farm" operators came in. Didenko paid US-based individuals—in California, Tennessee, and Virginia—to store computers at their residences and provide internet connectivity as detailed by The Record.
These weren't small setups. A laptop farm might contain 20, 50, or even 100 individual machines, all networked together. Each one could be logged into by a different North Korean worker. The machines were set up with keystroke logging prevention, screen sharing software, and VPN infrastructure to hide the true geographic origin of the connections. When a North Korean worker logged in, they'd see a standard Windows desktop with access to Slack, email, Git Hub, Jira, and whatever other tools the American company used according to CyberScoop.
From the employer's perspective, they were hiring a remote developer in the US. Background checks would show an American name and address. Tax withholding would go to an address they thought was in America. The employee would show up to Zoom meetings at US times (even though they might be bleary-eyed working graveyard shifts from Korea). They'd submit code, attend standups, collaborate with teammates—all the things a legitimate employee does as noted by CyberScoop.
The sophistication here isn't in the technology. It's in the social engineering and process understanding. North Korean IT workers, who are actually quite skilled (they've been trained by the regime for years in cyber operations), understood American tech culture well enough to blend in. They knew technical jargon, asked reasonable questions, and produced working code. Some teams reported that their North Korean developers were actually among their most productive employees as highlighted by CyberScoop.
But there were tells if you looked carefully. Time zone patterns were sometimes odd—someone claiming to be in California but online at unusual hours for that zone. Some had very minimal social media presence (because creating elaborate fake Facebook profiles is additional work). A few had email addresses that had been compromised in previous breaches but were still being used according to CyberScoop.
The real question is: how many North Korean workers got through completely undetected? The Didenko case reveals one specific operation, but the scope suggests this was far larger. When the FBI seized Upworksell in 2024, they didn't just shut down one marketplace. They diverted traffic to their own servers to see who would try to log in or use the service next. That's investigative tradecraft—keeping the honey pot running to catch more players in the ecosystem as reported by CyberScoop.
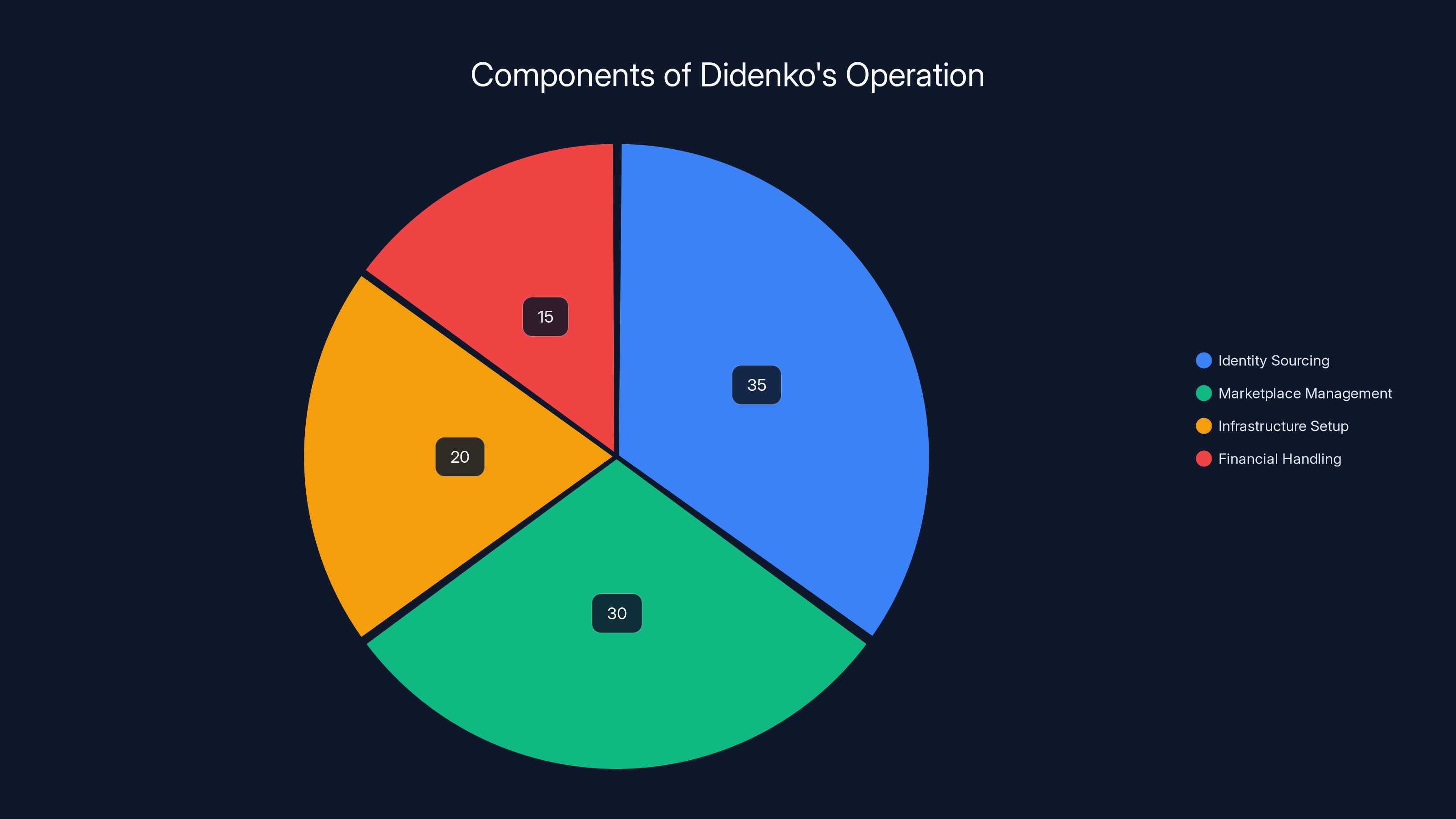
Estimated data showing Didenko's operation focus: identity sourcing (35%), marketplace management (30%), infrastructure setup (20%), and financial handling (15%).
The "Triple Threat": Why North Korean Workers Are Uniquely Dangerous
Security researchers have coined a phrase for this problem: North Korean IT workers represent a "triple threat" to Western businesses. Let's break down each threat.
Threat One: Sanctions Violation. The United States and United Nations have imposed comprehensive sanctions on North Korea specifically designed to cut off the regime's access to hard currency. These sanctions are meant to pressure the government to abandon its nuclear weapons program. When a North Korean worker gets hired under a fake identity and earns a US salary, that directly violates sanctions law. The employer, the employee, the identity broker, and anyone facilitating the scheme could face criminal charges. This isn't a victimless crime. It's funding a nuclear weapons program that threatens millions of people as noted by CyberScoop.
Threat Two: Intellectual Property Theft. North Korea has a dedicated unit within its military intelligence apparatus specifically tasked with stealing intellectual property and conducting espionage. This isn't speculation—it's been documented by cybersecurity firms and governments for years. When a North Korean IT worker gets hired as a software engineer at a biotech company, a defense contractor, or a cloud infrastructure provider, they have access to source code, infrastructure designs, security architecture, and proprietary algorithms. They can clone repositories, download datasets, and exfiltrate information. Some of this is grabbed automatically by malware. Some is manually copied. The regime then either sells this information to other adversarial states, uses it to accelerate their own tech development, or keeps it for future espionage operations as detailed by CyberScoop.
Threat Three: Extortion. Here's where it gets particularly nasty. After the North Korean worker has been discovered (or before, if they're preemptively planning ahead), North Korea leverages the fact that the company has unknowingly hired a sanctioned foreign national. They make contact with the company and essentially say: "Pay us, or we publish your proprietary code. Or we tell the US government you violated sanctions." Companies face an impossible choice. If they publicly report the incident, they potentially expose themselves to civil liability, shareholder lawsuits, and regulatory scrutiny. If they pay, they're funding a nuclear weapons program and potentially committing a crime. The scheme is diabolical because the victim's best move—going to the authorities—comes with massive downside risk as highlighted by CyberScoop.
This is the unique danger of North Korean operations compared to, say, Russian or Chinese IT worker infiltration schemes. Those countries might be interested in IP theft. North Korea adds the extortion layer and makes it part of their funding strategy according to CyberScoop.
How Oleksandr Didenko Built This Operation
Didenko's background isn't well-documented in public sources, but the operational details the Justice Department released paint a picture. He was based in Kyiv, Ukraine, which put him in an interesting geographic position. Ukraine has a large and relatively cheap IT workforce with good English skills and technical knowledge. It's also a country with porous financial systems—you can move money in and out more easily than from North Korea but still below the radar of many automated compliance systems as reported by CyberScoop.
At some point, Didenko either made contact with North Korean agents or was recruited by them. Perhaps he started as a legitimate freelance platform operator and pivoted to the illicit market. Perhaps someone approached him directly. The details haven't been made public. What's clear is that by the time the FBI was investigating, Upworksell had become a sophisticated operation handling hundreds of stolen identities as noted by CyberScoop.
Didenko's role was dual. First, he sourced the stolen identities. This could have come from previous data breaches (there are millions of American identities floating around the dark web), from inside sources at companies or agencies that store this data, or from phishing campaigns specifically designed to harvest personal information. Second, he operated the marketplace infrastructure. He built or contracted out the website, handled payments (probably in cryptocurrency to obscure the money trail), managed customer service (dark web style), and coordinated with the laptop farm operators as detailed by CyberScoop.
He also apparently paid people to set up and maintain the physical infrastructure—the laptop farms themselves. This required finding landlords (perhaps using shell companies or temporary tenancies), purchasing or leasing equipment, setting up internet service, and monitoring the systems to make sure they stayed operational. It's not glamorous work, but it's essential according to CyberScoop.
For his services, Didenko likely took a percentage of each transaction—maybe 20%, 30%, or 40% depending on the deal size. Even taking 20% of hundreds of millions of dollars in fraudulently earned wages would make him very wealthy. The Justice Department's court documents don't mention how much money Didenko personally accumulated, but given the scale (870+ identities), he was likely sitting on significant assets when he was arrested as reported by CyberScoop.
His operational security was apparently not perfect. Polish authorities were able to locate and arrest him, which suggests that his digital footprint was traceable or that he had made an error in operational security (using a personal device, meeting with associates, conducting financial transactions). Polish law enforcement then extradited him to the United States, where he was prosecuted in federal court as noted by CyberScoop.
North Korea's Broader IT Worker Export Program
The Didenko case is one visible piece of something much larger. North Korea has systematized the export of IT workers as a revenue-generating mechanism. Estimates suggest the regime brings in hundreds of millions of dollars annually from tech worker placements, along with other cyber operations like cryptocurrency theft and ransomware attacks as reported by CyberScoop.
Here's how the broader program works. North Korea has training facilities where young men (and some women) with technical aptitude are selected and trained intensively in programming, network administration, cybersecurity, and social engineering. These aren't casual IT bootcamps. They're military-grade technical training programs run by the Reconnaissance General Bureau, North Korea's primary intelligence agency. Graduates are essentially conscripted into serving the regime as noted by CyberScoop.
The regime then uses networks of labor brokers, fixers, and facilitators spread across Southeast Asia, Eastern Europe, and beyond to place these workers. Some placement is done through legitimate-looking recruiting agencies. Some is done through underground networks like Upworksell. Some is done directly by intelligence officers posing as recruiters as detailed by CyberScoop.
The workers themselves are in an impossible position. If they refuse to work, their families back in North Korea might face retaliation. If they steal from employers and don't turn over the proceeds, they face punishment. They're essentially indentured servants working for the regime. Some are actually defectors or have family members outside the country, which gives the regime leverage. It's a coercive system according to CyberScoop.
From the regime's perspective, this is brilliant. They get hard currency (critical because of sanctions). They get access to cutting-edge technology and business practices. They get intelligence on Western companies and government contractors. And they get plausible deniability—if caught, they claim the workers acted independently as highlighted by CyberScoop.
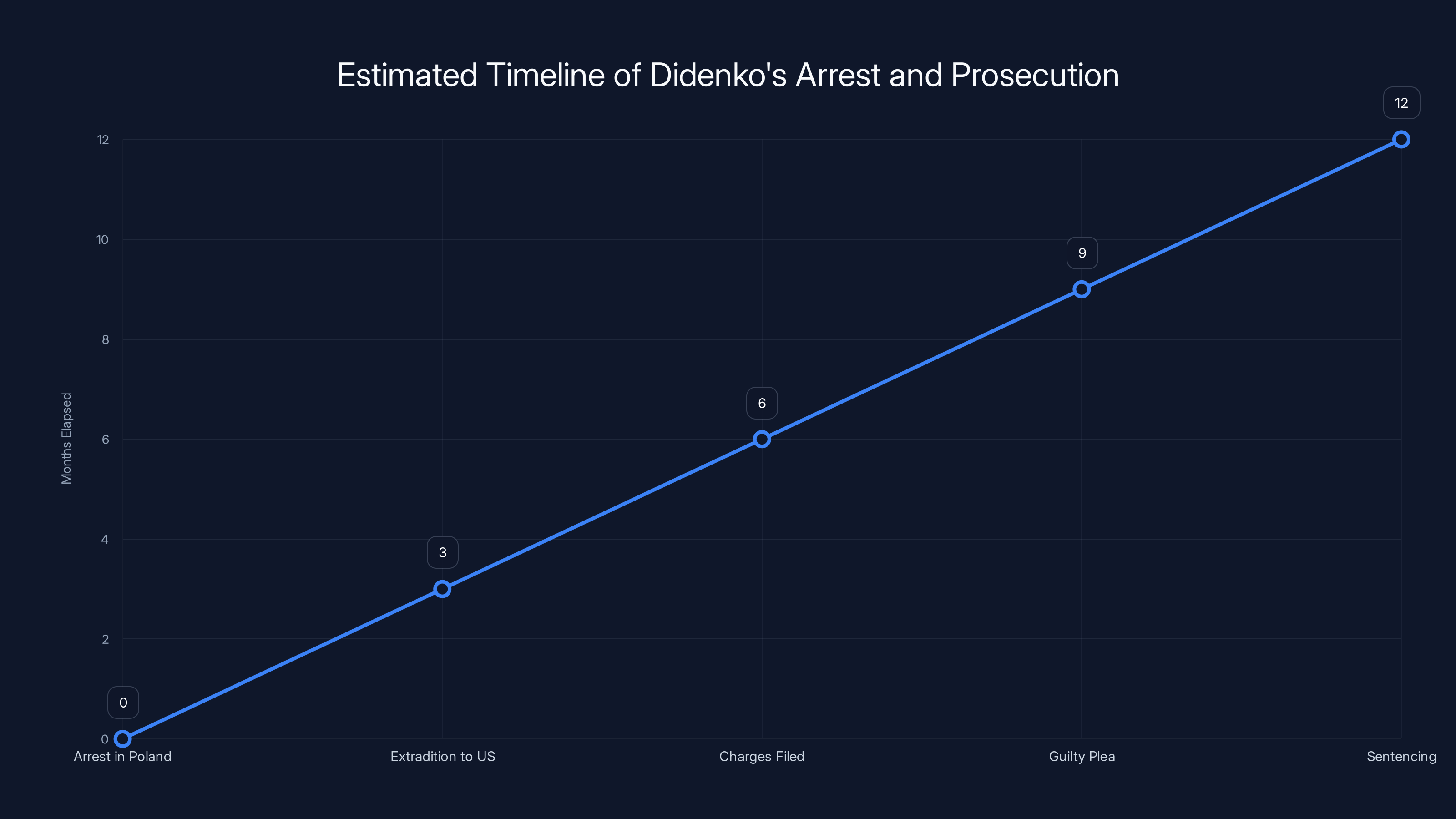
Estimated timeline shows a typical 12-month process from arrest to sentencing, highlighting the complexity of international extradition and federal prosecution. Estimated data.
Why US Companies Failed to Detect This
This is the uncomfortable part. Dozens of US companies hired North Korean workers without knowing it. Some large, well-resourced firms. Some smaller startups. The question is: why didn't existing security and compliance processes catch this?
First, let's acknowledge that background checks in the US, while reasonably thorough by global standards, have real limitations. Most standard background checks verify against public records, employment history, and databases of criminals. If you have a fake identity that was created from a real person's stolen information, and that person has a clean record, the checks will pass. The problem is data quality and source verification. Background check companies rely on third-party data sources, and if those sources contain outdated or incomplete information, the checks fail to catch fraud as noted by CyberScoop.
Second, US companies often outsource background checks to third-party vendors. Those vendors, competing on price and speed, may not do the most thorough verification. They might not call previous employers to confirm employment. They might not do video interviews to verify the applicant's identity. They might rely on automated database checks that are vulnerable to spoofing as detailed by CyberScoop.
Third, the normalization of remote work created a huge blind spot. When everyone could work from home, the expectation that you'd be in an office or even in the right time zone disappeared. A developer working at midnight their local time is now considered normal. That eliminated a major red flag according to CyberScoop.
Fourth, most companies don't have active monitoring for this specific threat. They're looking for insider threats, data exfiltration, unusual access patterns. But a North Korean worker who's actually doing their job, submitting code, attending meetings—they might not trigger any alerts. From a data loss prevention perspective, they're just an employee who happens to be accessing systems from certain IP addresses. If those IP addresses are masked by VPN, they could appear to be coming from the US as highlighted by CyberScoop.
Fifth, there's a cultural bias toward trusting hiring processes and background check vendors. Once someone passes a background check and is hired, there's an assumption that they are who they say they are. Managers don't go around verifying employee identities on an ongoing basis. Why would they? That would be paranoid. Except in this case, the paranoia would have been justified as reported by CyberScoop.
The Crowd Strike Connection: Detecting North Korean Workers in Real-Time
Security firms like Crowd Strike have been among the first to publicly acknowledge and document the rise of North Korean workers in US companies. In statements and public reports, Crowd Strike's researchers noted that they've observed a sharp increase in hiring attempts and successful placements of North Korean IT workers across various sectors as noted by CyberScoop.
What's particularly valuable about Crowd Strike's contribution is that their visibility comes from endpoint data. When companies use Crowd Strike's Falcon agent on their computers, Crowd Strike has visibility into what's happening on those endpoints—what software is running, what network connections are being made, what files are being accessed. This gives them a different vantage point than other security vendors as detailed by CyberScoop.
Crowd Strike and other endpoint security vendors have identified some behavioral patterns associated with North Korean workers. For example, unusual network access patterns—connecting from locations that don't match the employee's claimed residence. Accessing sensitive data that's outside their job scope. Using tools or protocols more commonly associated with offensive operations. Attempting to exfiltrate data outside normal business hours according to CyberScoop.
But here's the honest limitation: if a North Korean worker is actually doing their job competently and not trying to steal data, they might not trigger many alerts. They're not malware. They're a legitimate employee doing legitimate work. The crime is in how they were hired, not necessarily in what they're doing day-to-day as highlighted by CyberScoop.
For Crowd Strike and other vendors to be effective at catching this, they need to correlate endpoint data with identity verification data, hiring system data, and background check data. That's a complex information fusion problem. Most companies don't have that level of integration across systems. Your HR system doesn't talk to your endpoint security team in real-time as reported by CyberScoop.
The Laptop Farm Infrastructure: Hiding in Plain Sight
One of the most ingenious aspects of the scheme was the laptop farm infrastructure. Let's think through the logistics.
Didenko needed people in the US who would host these computers. He found them in California, Tennessee, and Virginia. Maybe he recruited them through dark web forums. Maybe he found people in financial distress who were willing to take cash for letting someone set up computers in their garage. The Justice Department didn't reveal exactly how he found these people, but recruiting domestically was essential as noted by CyberScoop.
For the hosts, the deal was probably simple: "We'll pay you
The computers themselves needed to be set up specifically. They needed to be configured so that North Korean operators could log in from overseas. This probably involved VPN software, remote desktop software, and possibly custom malware or rootkits to hide the true location and maintain access. The computers might have been running legitimate Windows or Linux installations to avoid suspicion, but with backdoors built in according to CyberScoop.
Internet connectivity was critical. A laptop farm needs multiple Mbps of upload and download bandwidth. If you have 50 computers actively being used for work, and each developer is uploading code and accessing large files, you need serious bandwidth. Standard residential internet wouldn't cut it. The farm operators probably had to upgrade to business-class or even dedicated internet. That's another sign of suspicion, but most ISPs don't flag unusual activity to law enforcement automatically as highlighted by CyberScoop.
The beauty of the geographic distribution is that it's hard to detect patterns. If all laptop farms were in one location, that location might get flagged by ISPs or someone might notice suspicious activity. Spread across three states, it looks like normal business activity. "My cousin needed help setting up computers for his business," the farm operator might say if questioned. Or "I'm offering colocation services." These are real business practices that exist legitimately as reported by CyberScoop.
From the North Korean side, the logistics were equally clever. Each worker would have a username and password to log into their assigned machine. They'd connect through one or more VPN services (probably paid for with cryptocurrency) to mask their location. They'd then log into the remote desktop connection and see the Windows desktop of a computer that was physically located in Tennessee but was presenting itself as a machine in an American office as noted by CyberScoop.
Once logged in, the North Korean worker would open Slack, Gmail, Git Hub, and start their workday. No one on the engineering team would know that the person typing in that Slack channel was 6,000 miles away as detailed by CyberScoop.

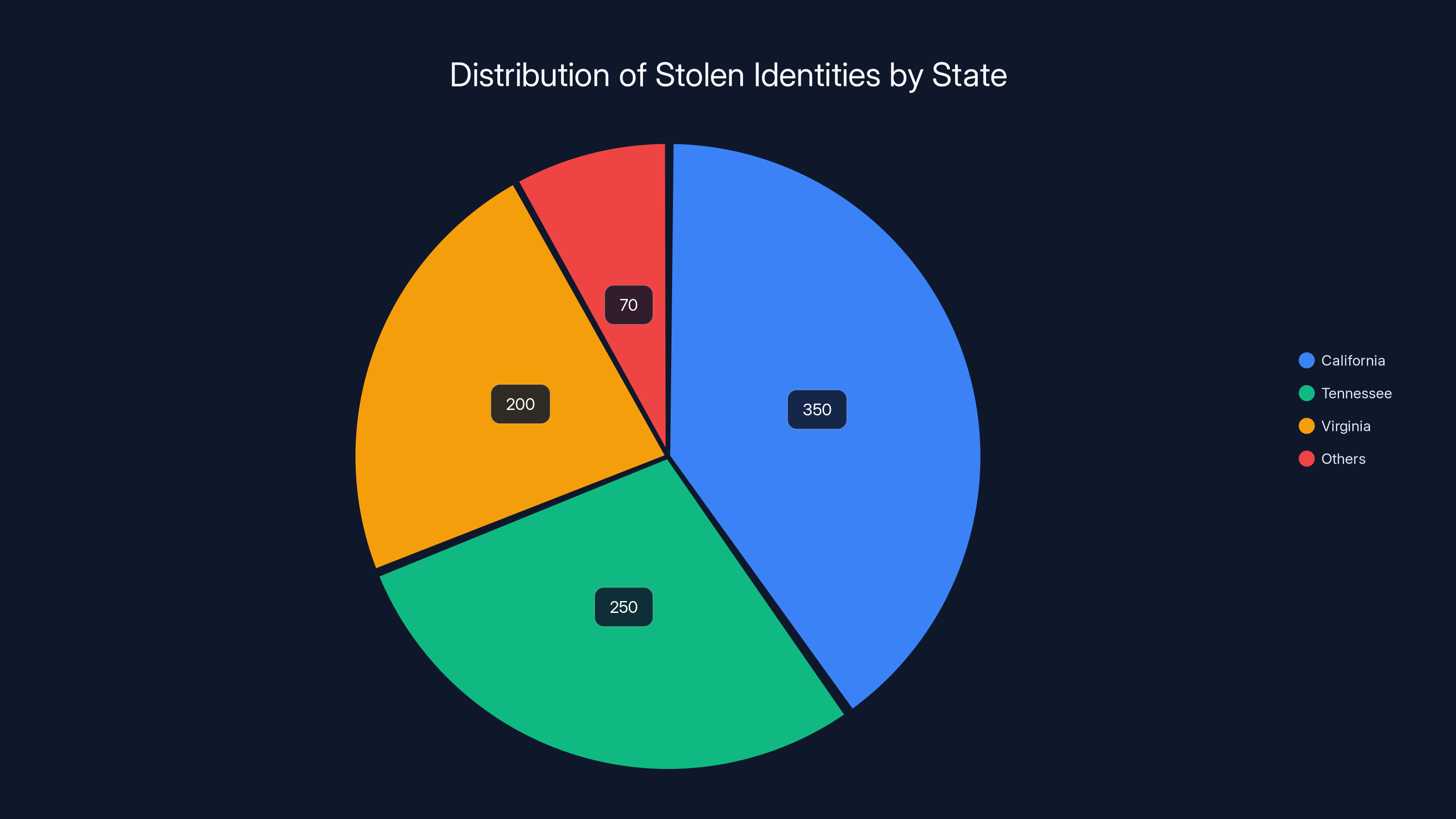
Estimated data shows that California hosted the largest share of stolen identities used in the scheme, followed by Tennessee and Virginia. This highlights regional vulnerabilities in tech company operations.
The Role of Cryptocurrency and Financial Obfuscation
Paying for a stolen identity marketplace and operating laptop farms requires money movement that avoids detection. This is where cryptocurrency enters the picture.
Didenko probably accepted payments in Bitcoin, Monero, or other cryptocurrencies. These have the advantage of being programmable, not needing bank accounts, and being harder (though not impossible) to trace than traditional wire transfers. A North Korean worker earning $120,000 annually could have that converted to cryptocurrency, then moved to wallets controlled by the regime or its proxies as reported by CyberScoop.
The regime then has a choice about what to do with the cryptocurrency. They could sell it on exchanges for fiat currency, though that's risky because exchanges are now requiring KYC (know-your-customer) verification. They could use it to purchase goods that are imported into the country or sold on the black market. They could exchange it with other cryptocurrency users who are sympathetic to the regime or simply seeking to launder money themselves as noted by CyberScoop.
Didenko himself probably took a percentage in cryptocurrency. He might have stored it in offshore wallets, used it to purchase assets (which could later be seized by law enforcement if he's caught), or converted it to fiat in financial systems in countries with weak compliance as detailed by CyberScoop.
The cryptocurrency angle is important because it's one of the few payment mechanisms that could have scaled this operation. Traditional banking would have left a trail. Wire transfers between US companies and Ukrainian bank accounts to North Korean handlers would have triggered compliance checks. But cryptocurrency moves silently, at least until someone traces the blockchain according to CyberScoop.
Didenko's Arrest and the Criminal Justice Process
Parts of Didenko's arrest and prosecution timeline are public, while others remain classified or sealed.
What we know is that Polish authorities arrested him, probably after coordination with the FBI or Interpol. Poland has been increasingly cooperative with US law enforcement on cybercrime and sanctions violations. Didenko was in Poland (probably Kyiv would have been riskier given the Ukraine-Russia conflict and more porous governance), so Polish authorities could move quickly as reported by CyberScoop.
He was then extradited to the United States. This process takes time and requires both countries to agree that the charges are serious enough to warrant extradition. The fact that it happened suggests the evidence was strong and the US made a compelling case as noted by CyberScoop.
Once in US custody, Didenko faced federal charges likely including: wire fraud, identity theft, conspiracy, sanctions violations, and possibly money laundering. The Justice Department prosecuted him, and he eventually pleaded guilty. Pleading guilty has advantages for both sides. The defendant avoids the risk of a worse sentence if convicted at trial. The government avoids the cost and unpredictability of trial as detailed by CyberScoop.
The sentence: five years in prison. That's meaningful but not extraordinary by federal standards. Serious cybercrime cases can result in 10, 15, or even 20-year sentences. Five years suggests the prosecutors and judge felt Didenko was part of a larger operation but not the mastermind, or that he cooperated with investigators (which is sometimes not publicly revealed) according to CyberScoop.
Before sentencing, there was likely a pre-sentence investigation report, victim impact statements, and arguments from both the prosecution and defense about appropriate sentencing. The judge considered all this and determined five years was appropriate as highlighted by CyberScoop.
The Broader Pattern: Previous Convictions and Ongoing Cases
The Didenko case is the latest in what prosecutors describe as a "string of recent convictions" of individuals involved in facilitating North Korean IT worker schemes. This suggests there have been others—perhaps not all publicized or still ongoing as reported by CyberScoop.
Previous cases have involved North Korean workers themselves being caught and prosecuted. Some have been deported after serving time. Some have been flipped to become cooperating witnesses. Cases have involved recruiters, brokers, identity sellers, and laptop farm operators. Each prosecution adds another piece to understanding the ecosystem as noted by CyberScoop.
The fact that there have been multiple convictions suggests law enforcement has gotten more effective at identifying and prosecuting these networks. The FBI has probably assigned dedicated resources to this threat. Interpol might have issued red notices for known facilitators. Countries are sharing intelligence about North Korean IT worker operations as detailed by CyberScoop.
But the broader point is that this is an ongoing cat-and-mouse game. For every Didenko who's convicted, there might be others operating with better operational security. The Upworksell marketplace was shut down, but other marketplaces or operations might be running right now. North Korean IT workers might be employed right now at companies you know according to CyberScoop.
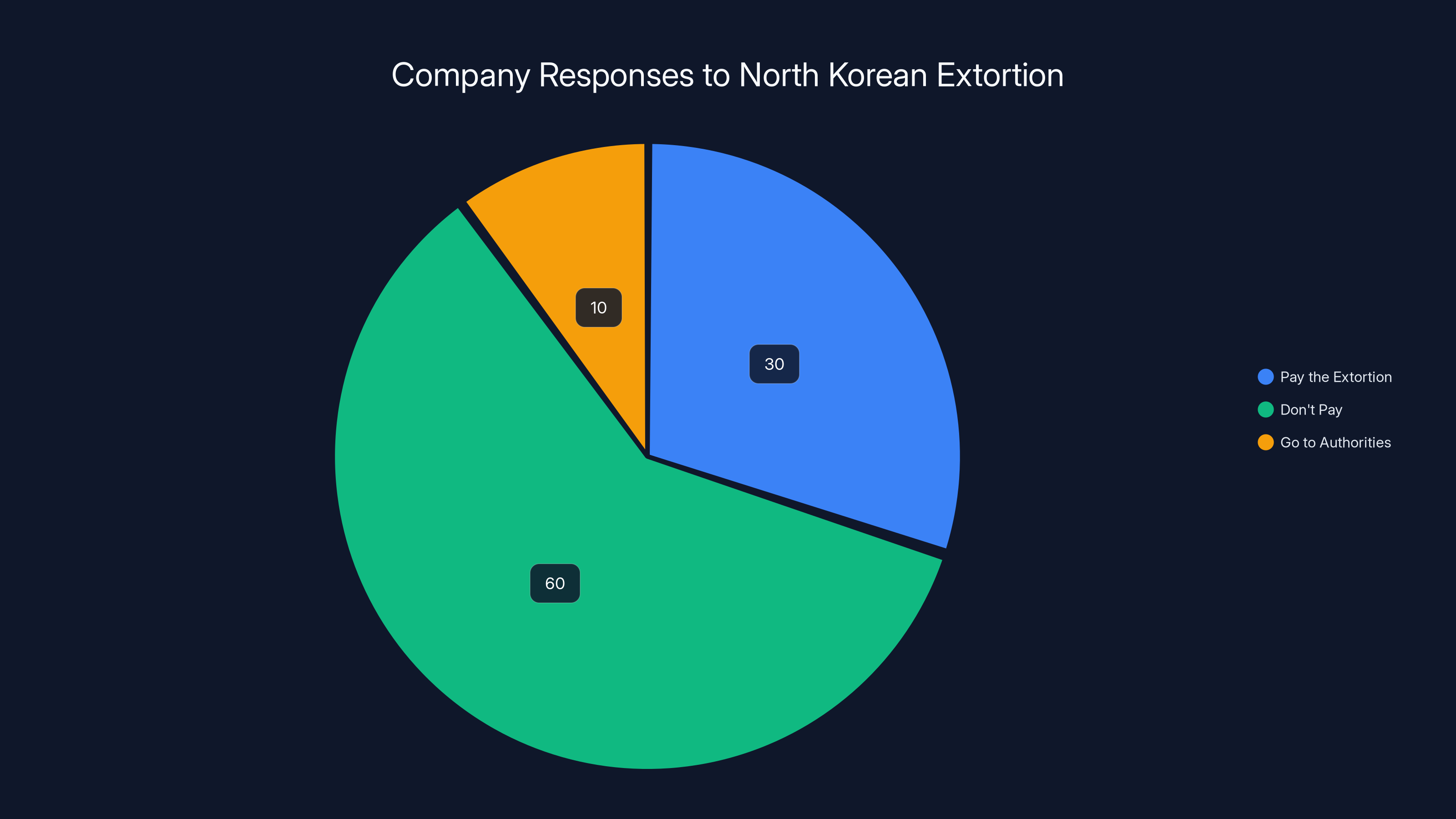
Estimated data suggests that most companies choose not to pay or settle extortion demands silently, with very few going to authorities.
Impact on Targeted Companies: Data Loss and Extortion
When a company discovers they've hired a North Korean worker, the impact extends far beyond the embarrassment of being infiltrated. There's real damage.
First, there's the investigation cost. The company needs to bring in external security firms (often at $10,000+ per day), notify law enforcement, and audit what the employee accessed. For a company with thousands of employees and complex access controls, determining what one person had access to can take weeks or months as reported by CyberScoop.
Second, there's the data loss. If the employee exfiltrated source code, customer data, security architecture, or other sensitive information, the company has been harmed. That IP is now in the hands of the North Korean regime. The company might have lost its competitive advantage. If customer data was stolen, the company might need to notify those customers, potentially triggering regulatory fines as noted by CyberScoop.
Third, there's the extortion threat. As mentioned earlier, North Korea has allegedly threatened companies with publicizing stolen code unless they pay. Some companies might have quietly paid to make the problem go away. Others might have refused and weathered the fallout. None of this is public because companies won't disclose extortion, but it's happening as detailed by CyberScoop.
Fourth, there's reputational damage. If a company is publicly identified as having hired a sanctioned foreign national, investors get nervous, customers question the security of their data, and the company's recruitment becomes harder according to CyberScoop.
Fifth, there's potential regulatory liability. The company knowingly hired someone who's now known to be subject to sanctions (after the fact). They might face OFAC (Office of Foreign Assets Control) fines. They might be investigated by other regulators as highlighted by CyberScoop.
Smaller companies are particularly vulnerable. A startup that can't afford a sophisticated background check process might end up hiring multiple North Korean workers without realizing it. Their damage could be existential as reported by CyberScoop.

How Companies Should Strengthen Hiring Security
Given the demonstrated threat, what should US companies do?
Identity Verification. Use multiple methods beyond a single background check vendor. Consider video verification calls where the person is asked questions only they would know. Verify previous employment by calling actual humans at previous companies (not just email addresses provided by the candidate). Cross-reference information against public records directly, not just vendor databases. Some companies are moving toward using biometric verification or government-issued ID scanning for remote hires as noted by CyberScoop.
Behavioral Monitoring. Track network access patterns. If an employee claiming to be in California is consistently accessing systems from IP addresses in Asia, that's a red flag. Not a certainty—VPNs exist—but a flag. Monitor for unusual access to data outside the employee's job scope. Use user behavior analytics tools that baseline normal activity and alert on anomalies as detailed by CyberScoop.
Ongoing Verification. Don't assume that because someone passed a background check, they're legitimate forever. Conduct periodic re-verification, especially for employees with access to sensitive systems. This might sound paranoid, but it's appropriate given the threat according to CyberScoop.
Supplier Due Diligence. If background check vendors are being used, verify that they're actually conducting checks thoroughly. Ask for details about their process. Don't just assume they're doing the job right as highlighted by CyberScoop.
Referral Programs. Prefer hiring people referred by existing employees who can vouch for them. North Korean operatives can't easily create elaborate fake networks of contacts, so a person who has real connections to your company is lower risk as reported by CyberScoop.
Red Flag Training. Teach hiring managers and team leads what to look for: unusual communication patterns, requests for unusual access, strange financial behavior, signs that someone is exfiltrating data. Most people aren't trained to notice these things as noted by CyberScoop.
Third-Party Checks. For roles with access to sensitive data, consider hiring a private investigator to do physical verification. Have them meet the employee in person or at least verify that they're actually living where they claim to be as detailed by CyberScoop.
None of this is foolproof. But it raises the bar significantly according to CyberScoop.
Regulatory and Law Enforcement Response
The US government has several agencies involved in combating this threat.
The FBI is clearly taking the lead on criminal investigation and prosecution. They have cyber divisions in major cities, and they're actively investigating North Korean IT worker schemes. The seizure of Upworksell and the tracking of Didenko shows active investigative capability as highlighted by CyberScoop.
OFAC (Office of Foreign Assets Control), part of the Treasury Department, is responsible for enforcing sanctions. They've issued guidance specifically about North Korean IT workers and have the authority to fine companies that knowingly hire them or unknowingly hire them without doing due diligence as reported by CyberScoop.
The NSA and other intelligence agencies are presumably collecting signals intelligence on North Korean IT worker recruitment and operations, though this work is classified as noted by CyberScoop.
DHS (Department of Homeland Security) has components involved in cybersecurity and counterintelligence as detailed by CyberScoop.
International coordination is also happening. The FBI works with Polish law enforcement (in the Didenko case). Interpol might be involved in alerting countries to known facilitators. The Five Eyes alliance (US, UK, Canada, Australia, New Zealand) likely shares intelligence about North Korean cyber operations according to CyberScoop.
The Justice Department can also bring charges against companies that knowingly hire sanctioned individuals, though this has happened rarely, probably because prosecutors recognize that companies are often unwitting victims as highlighted by CyberScoop.

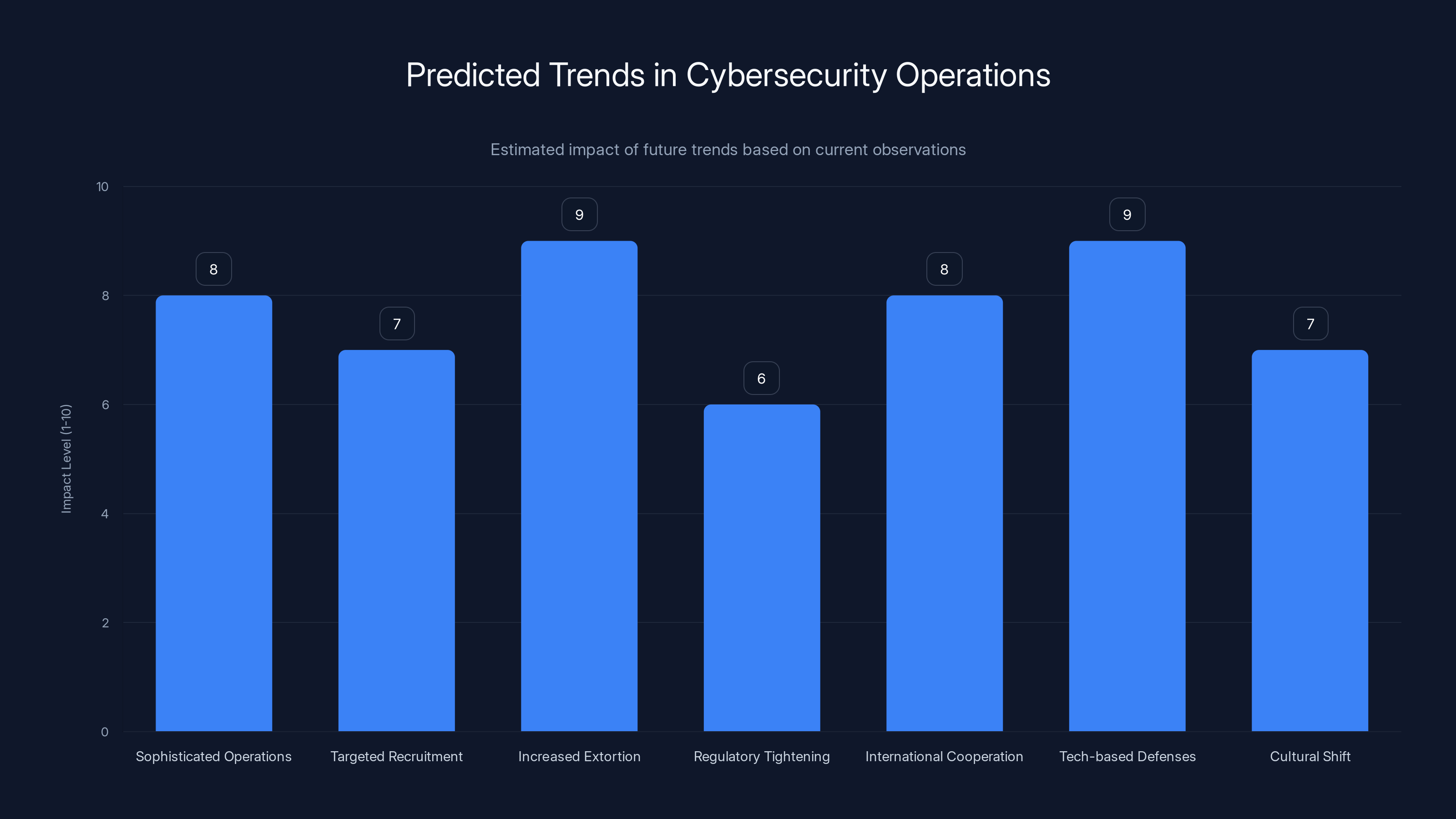
The chart estimates the impact of various predicted trends in cybersecurity operations, with increased extortion and technology-based defenses expected to have the highest impact. Estimated data.
The Geopolitical Dimension
Why does North Korea run these operations? Because the regime is desperately poor and heavily sanctioned.
North Korea's economy is estimated at around $30-40 billion in gross domestic product, and most of that isn't accessible because of international sanctions. The government controls most economic activity, and revenue is desperately needed to fund the military, the security apparatus, and the nuclear weapons program as reported by CyberScoop.
The regime generates hard currency through several methods:
- Cyberattacks and ransomware. North Korean-linked groups have stolen billions in cryptocurrency and ransomed critical infrastructure as noted by CyberScoop.
- Drug trafficking. The regime is involved in producing methamphetamine, which is exported to Southeast Asia as detailed by CyberScoop.
- Counterfeiting. North Korea produces counterfeit US currency (though less so now) according to CyberScoop.
- Mining cryptocurrency. The regime has large-scale cryptomining operations powered by cheap electricity as highlighted by CyberScoop.
- IT worker exports. This is relatively low-risk and high-volume, which makes it attractive as reported by CyberScoop.
The IT worker export program is genius from the regime's perspective because it's hard to detect and has plausible deniability. Individual workers can be claimed to be freelancers acting without regime authorization. It generates ongoing revenue (workers are paid regularly, unlike one-time theft operations). It builds the regime's technical capacity. And it gives access to Western technology and business practices as noted by CyberScoop.
From a broader geopolitical perspective, this is part of how North Korea survives despite crippling sanctions. It's a reminder that sanctions, while important, are imperfect tools. Determined adversaries find ways around them as detailed by CyberScoop.
The Extortion Angle: North Korea's Criminal Underworld Strategy
One dimension of the North Korean IT worker threat that deserves more attention is the extortion angle. It reveals something about how North Korea operates strategically.
The extortion works like this: North Korean IT worker infiltrates a company. While there, they or their handlers exfiltrate sensitive source code, algorithms, or company secrets. After weeks or months, North Korea makes contact with the company and says: "We have your code. Pay us in cryptocurrency, or we'll release it publicly" as reported by CyberScoop.
This is a sophisticated form of extortion because the victim faces a terrible choice:
Option A: Pay the extortion. You lose money, you admit (at least privately) that you've been compromised, and you're funding a nuclear weapons program. This violates sanctions law and could expose you to prosecution or OFAC fines as noted by CyberScoop.
Option B: Don't pay and hope they don't release the code. But they probably will, because their threat has no credibility if they don't follow through. Your code is now public, your competitive advantage is gone, and your IP is worth less as detailed by CyberScoop.
Option C: Go to the authorities. You report the extortion to the FBI, admit you were infiltrated, and face potential regulatory consequences. But at least you're complying with the law according to CyberScoop.
Most companies that face this choose either B (suffer the damage silently) or unofficially settle it somehow. Very few go public. The result is that we don't have great data on how many companies have been extorted this way as highlighted by CyberScoop.
This strategy is brilliant because it achieves multiple objectives for North Korea: it generates money, it damages US tech companies, it gathers intelligence, and it's extremely difficult for law enforcement to investigate (how do you prosecute someone for threatening to release something that's already been stolen?). You'd need to build a case against a North Korean government agent operating from Pyongyang, which is practically impossible as reported by CyberScoop.

Sector-Specific Risks: Which Industries Are Most Vulnerable?
Not all US tech companies are equally at risk. Some sectors are more attractive targets than others.
Defense and Aerospace. Companies working on military contracts, classified projects, or advanced weapons systems are high-value targets. North Korea would love access to design details of military hardware, software, or systems. These companies should have stronger security, but they're also under the most pressure to hire skilled people quickly as noted by CyberScoop.
Finance and Cryptocurrency. North Korea is very interested in cryptocurrency systems and financial infrastructure. Access to source code for trading systems, wallet software, or exchange infrastructure is valuable. Some of the highest-profile cryptocurrency thefts have North Korean fingerprints as detailed by CyberScoop.
Cloud Infrastructure and AI. Companies building cloud platforms or training large AI models have code and data that's valuable. Models themselves can be stolen and repurposed. Infrastructure designs could be exfiltrated according to CyberScoop.
Healthcare and Biotech. Especially companies working on expensive or novel drugs. The regime might be interested in intellectual property or could use access to extort money from health systems as highlighted by CyberScoop.
Telecommunications. Companies operating telecommunications infrastructure are targets for nation-state surveillance and intelligence. Access to systems or information about infrastructure vulnerabilities would be valuable as reported by CyberScoop.
Startups and Scale-ups. These are actually high-risk targets because they often have weaker security and hiring processes, but they're working on cutting-edge technology. A newly developed machine learning algorithm or a novel approach to distributed systems could be valuable to competitors or to intelligence agencies as noted by CyberScoop.
Sector-specific risk assessment should inform hiring security practices. A startup can't implement security measures designed for a defense contractor, but they should be aware of risks appropriate to their sector as detailed by CyberScoop.
Looking Ahead: Predictions and Trends
Based on the Didenko case and broader trends, where is this heading?
More sophisticated operations. Law enforcement is getting better at detecting and prosecuting these schemes, so facilitators like Didenko will adapt. Future operations might involve more distributed networks, better operational security, and more careful vetting of participants. We might see fewer large marketplaces like Upworksell and more decentralized operations according to CyberScoop.
More targeted recruitment. Instead of broadly recruiting North Korean IT workers, future operations might focus on specific high-value targets. A recruiter might approach a developer at a specific company and offer $200,000 per year to "work remotely" for a foreign entity. The sophistication of recruitment will increase as highlighted by CyberScoop.
Increased extortion and threats. As companies get better at detecting infiltration, the window for silent data exfiltration closes. But the extortion angle will probably intensify. Expect to hear about more companies being threatened with release of stolen code as reported by CyberScoop.
Regulatory tightening. OFAC will probably become more aggressive. Companies might be required to certify their hiring practices. Background check vendors will face pressure to improve detection. Some countries might implement national hiring standards for sensitive sectors as noted by CyberScoop.
International cooperation. More countries will work together to disrupt these networks. Extradition of facilitators like Didenko will become more common. Intelligence sharing will improve as detailed by CyberScoop.
Technology-based defenses. Companies will invest more in identity verification technology, behavioral analytics, and continuous monitoring. Biometric verification might become standard. AI-powered tools might detect anomalies that humans miss according to CyberScoop.
Cultural shift. As companies realize how vulnerable they are, hiring security will become a core competency, not an afterthought. CISOs and hiring teams will coordinate more closely. The idea of hiring someone without serious verification will become seen as reckless as highlighted by CyberScoop.
Lessons for Defenders
If there's a lesson in the Didenko case and the broader North Korean IT worker phenomenon, it's that traditional hiring and background check processes are insufficient against a determined adversary.
The threat is real and ongoing. North Korea is running sophisticated operations that have penetrated dozens or potentially hundreds of US companies. These operations are generating hundreds of millions of dollars annually. The extortion angle suggests the regime is not just interested in money but in destabilizing Western tech companies as reported by CyberScoop.
Defense requires a multi-layered approach. It requires investment in better identity verification. It requires monitoring and behavioral analytics. It requires training and awareness. It requires coordination between hiring, security, legal, and compliance teams. It requires international law enforcement cooperation as noted by CyberScoop.
For companies, the calculus is: the cost of improved hiring security is much less than the cost of being infiltrated. For regulators, the calculus is: proactive enforcement is better than reactive prosecution. For law enforcement, the calculus is: international cooperation and disruption of facilitator networks is more effective than prosecuting individual workers as detailed by CyberScoop.
The Didenko case is one data point in a larger struggle. It shows that the problem is being taken seriously and that perpetrators can be caught and prosecuted. But it's unlikely that any single prosecution will solve the problem. The regime has deep pockets, strong motivation, and a long time horizon. This is a competition that will continue for years according to CyberScoop.
FAQs
What is an identity theft marketplace like Upworksell?
Upworksell was a website operated by Oleksandr Didenko where individuals could buy or rent stolen American identities, including names, Social Security numbers, and dates of birth. The platform was designed to facilitate employment fraud by allowing overseas workers, particularly from North Korea, to apply for jobs at US companies using fake identities of legitimate American citizens. This marketplace model made identity theft scalable and accessible to criminal networks as reported by CyberScoop.
How did North Korean workers actually perform their jobs?
North Korean workers used stolen American identities to get hired at US companies and then worked remotely through "laptop farms"—rooms filled with computers located in California, Tennessee, and Virginia. These machines were accessed by the workers from overseas through VPN connections, making it appear they were physically present in the United States. From the employer's perspective, they appeared to be hiring American or US-based remote workers, when in reality the workers were located in North Korea as noted by CyberScoop.
Why is this called a "triple threat" to US companies?
Security researchers describe North Korean IT workers as a triple threat because they: (1) violate international sanctions by earning US salaries that are funneled back to the regime, (2) steal sensitive intellectual property and trade secrets while employed at US companies, and (3) conduct extortion schemes by threatening to publicly release stolen source code unless companies pay ransom. This combination makes them uniquely dangerous compared to other forms of cyber infiltration as detailed by CyberScoop.
How many people were affected by Didenko's operation?
Oleksandr Didenko handled more than 870 stolen American identities according to the US Justice Department. This suggests that potentially hundreds of North Korean workers used the Upworksell marketplace to gain fraudulent employment at US companies, though the exact number of workers placed is not publicly disclosed according to CyberScoop.
What happened to the money earned by North Korean workers?
Salaries earned by North Korean workers using stolen identities were funneled back to the North Korean regime through various mechanisms, often using cryptocurrency to avoid detection. These funds were used by the government to support nuclear weapons development and other military programs that are prohibited under international sanctions as highlighted by CyberScoop.
How did law enforcement shut down Upworksell?
The FBI seized Upworksell in 2024 during its investigation into the identity theft marketplace. Rather than simply shutting down the website immediately, the FBI diverted traffic from the seized domain to their own servers to monitor who would try to access or use the service next, which allowed them to gather additional evidence and identify other participants in the ecosystem as reported by CyberScoop.
What charges and sentence did Oleksandr Didenko face?
Didenko faced federal charges including wire fraud, identity theft, conspiracy, and sanctions violations. He was arrested by Polish authorities, extradited to the United States, pleaded guilty to the charges, and was sentenced to five years in federal prison in 2026 as noted by CyberScoop.
What are laptop farms and why are they effective?
Laptop farms are physical locations containing multiple computers networked together that allow remote operators to log in and use the machines as if they were physically present. In the North Korean scheme, these farms located in US cities provided the infrastructure for workers to appear to be US-based while actually working from overseas. They were effective because they created the technical and logistical foundation for the identity fraud scheme to operate at scale as detailed by CyberScoop.

Conclusion: A Vulnerability Exposed
The Oleksandr Didenko case represents more than just one criminal's prosecution. It's a window into a systematic vulnerability in how US companies hire, verify identities, and monitor for insider threats. It reveals that a determined adversary with sufficient resources can infiltrate dozens or potentially hundreds of companies using relatively simple techniques: stolen identities, fake infrastructure, and social engineering as reported by CyberScoop.
The North Korean regime has weaponized IT employment as part of its broader strategy to circumvent sanctions, fund weapons development, steal intellectual property, and destabilize Western tech companies. The fact that Didenko has been convicted and sentenced is important, but it's also just one visible success in what is likely a much larger operation still ongoing as noted by CyberScoop.
For US companies, the lesson is clear: traditional background check processes are no longer sufficient. Identity verification needs to be multi-layered. Ongoing monitoring and behavioral analytics need to be implemented. Hiring teams and security teams need to coordinate. Red flag training needs to be standard as detailed by CyberScoop.
For regulators and law enforcement, the imperative is to continue disrupting these networks internationally, to prosecute facilitators like Didenko, to share intelligence with allies, and to increase penalties for sanctions violations related to North Korean IT workers. The cost of enforcement is far less than the cost of allowing the regime to continue funding its nuclear weapons program through employment fraud <a href="https://cyberscoop.com/doj-ukrainian-north-korea-remote-worker-scheme-facilitator-sentenced/" target
![North Korean Identity Theft Scheme at US Companies [2025]](https://tryrunable.com/blog/north-korean-identity-theft-scheme-at-us-companies-2025/image-1-1771611149737.jpg)




