Quantum Computing's Looming Threat to Bitcoin Encryption [2025]
Quantum computing is no longer a distant dream. It's rapidly becoming a reality that could reshape industries, disrupt economies, and challenge the very foundations of cybersecurity. One of the most pressing concerns is the potential impact on Bitcoin encryption, a cornerstone of cryptocurrency security. In this comprehensive guide, we'll explore the latest developments in quantum computing, its implications for Bitcoin, and how stakeholders can prepare for a quantum future.
TL; DR
- Quantum Leap: Quantum computing is advancing faster than anticipated, threatening current encryption standards as noted by The Quantum Insider.
- Bitcoin Vulnerability: Bitcoin's SHA-256 encryption may be compromised sooner due to reduced qubit requirements, according to Google's research.
- Immediate Actions: Transitioning to quantum-resistant algorithms is crucial for future-proofing Bitcoin.
- Long-Term Strategy: Collaboration between tech companies, governments, and cryptographers is essential.
- Stay Informed: Continuous research and development will be key to adapting to quantum advancements.
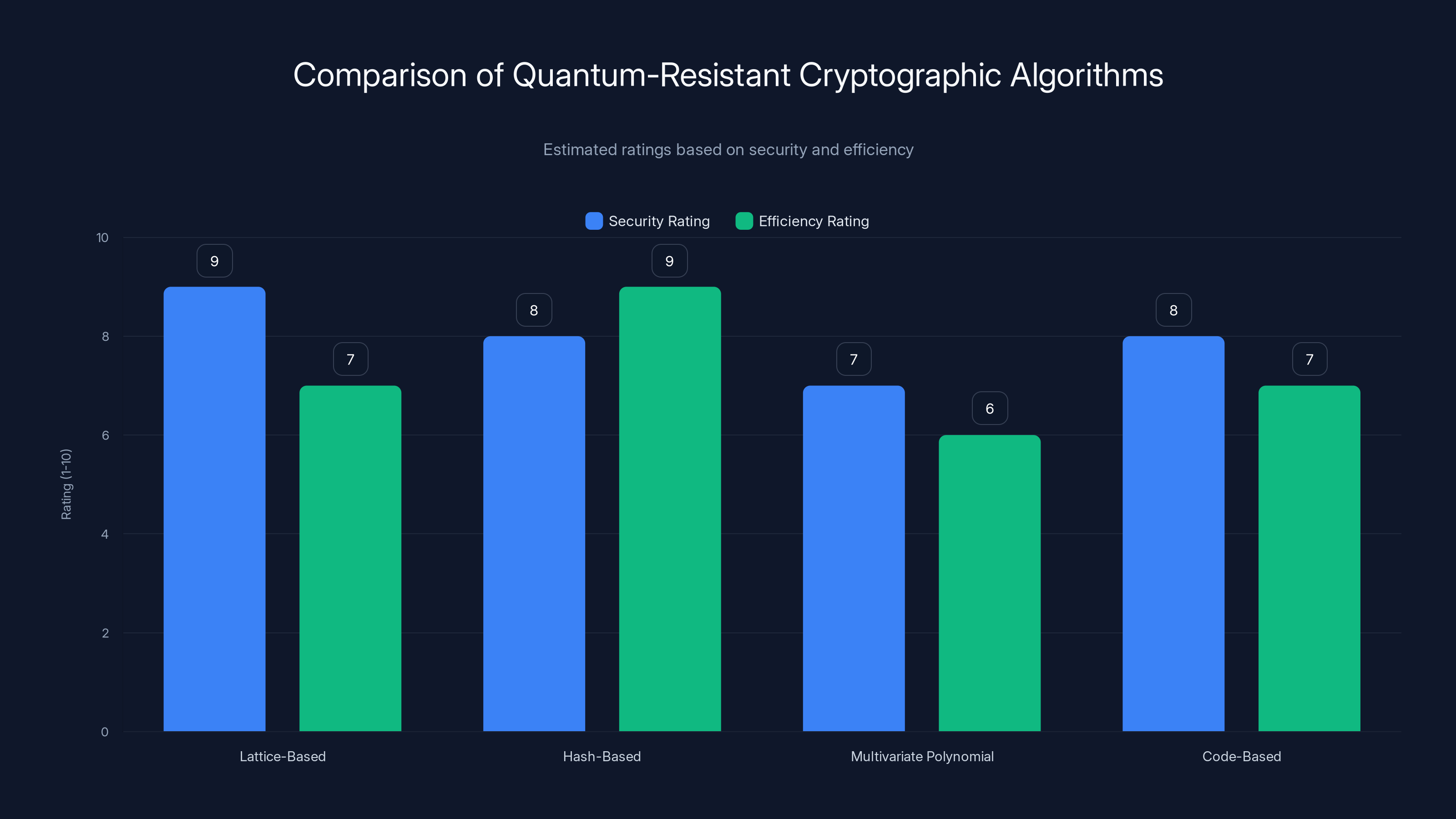
Estimated data shows lattice-based algorithms score high in security, while hash-based methods excel in efficiency. Diversifying cryptographic strategies enhances overall security.
The Quantum Revolution: An Overview
Quantum computing leverages the principles of quantum mechanics to process information in fundamentally different ways than classical computers. While traditional computers use bits as the smallest unit of data, quantum computers use qubits. A qubit can exist in multiple states simultaneously, thanks to the phenomenon of superposition, allowing quantum computers to perform complex calculations at unprecedented speeds.
How Quantum Computers Work
At the heart of quantum computing are two key principles: superposition and entanglement. Superposition allows qubits to exist in multiple states at once, enabling parallel processing on a massive scale. Entanglement, on the other hand, links qubits in such a way that the state of one qubit can instantly influence the state of another, regardless of distance. This entanglement facilitates complex problem-solving capabilities that are unattainable with classical computing.
The Race for Quantum Supremacy
Tech giants like IBM, Google, and Microsoft are investing heavily in quantum research, aiming to achieve quantum supremacy — the point at which a quantum computer can perform tasks beyond the capabilities of the most powerful classical supercomputers. Google's recent warning about Bitcoin encryption vulnerability underscores the urgency of this race, as highlighted in Google's research blog.

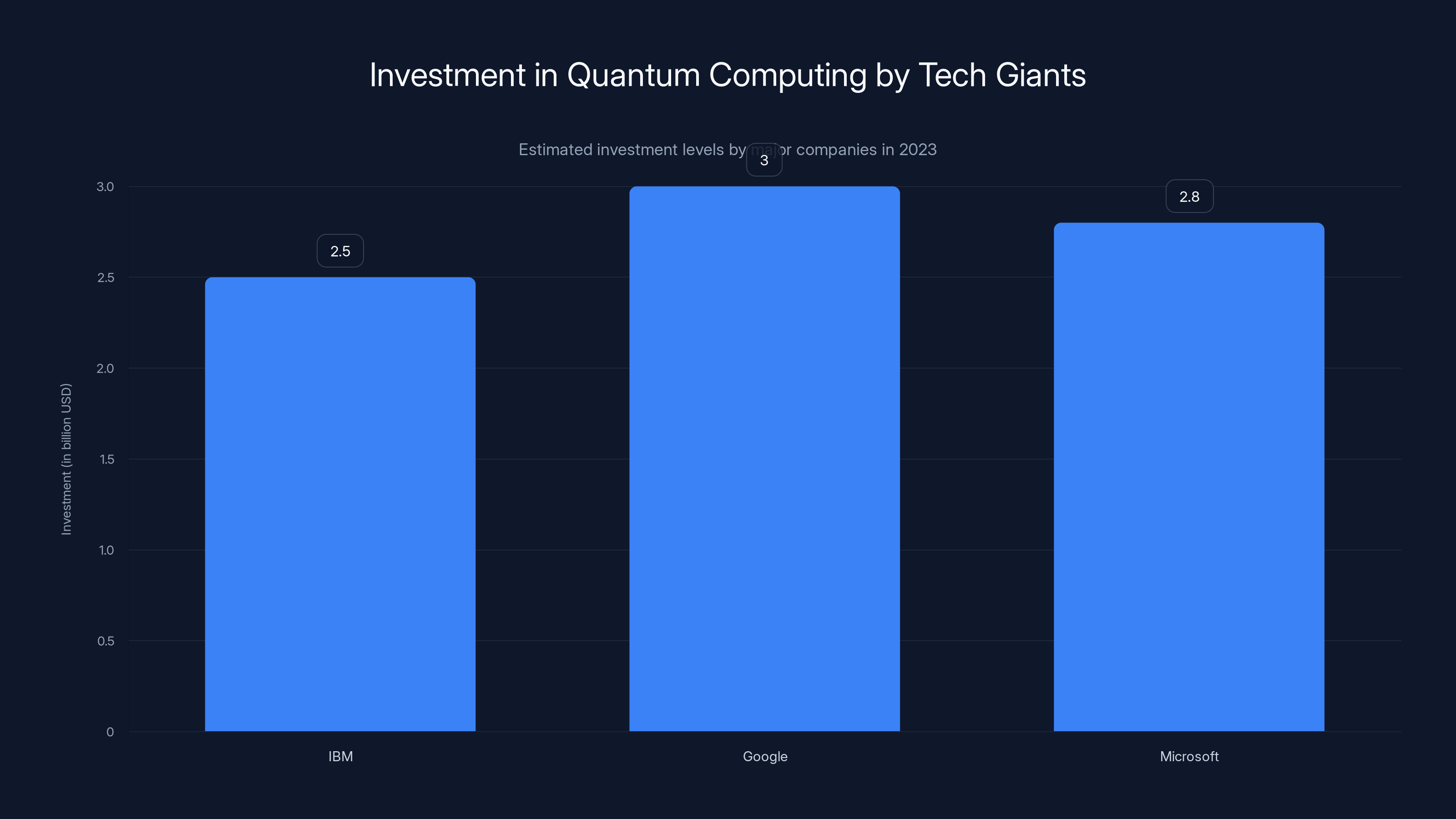
Estimated data shows that Google leads in quantum computing investment, closely followed by Microsoft and IBM. (Estimated data)
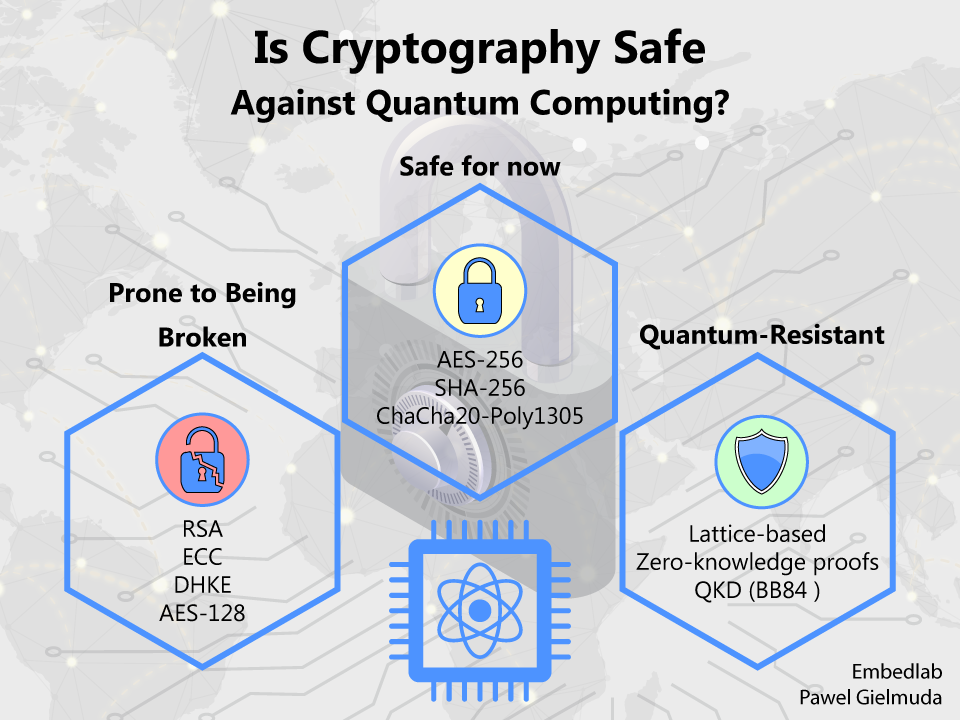
Quantum Computing's Impact on Cryptography
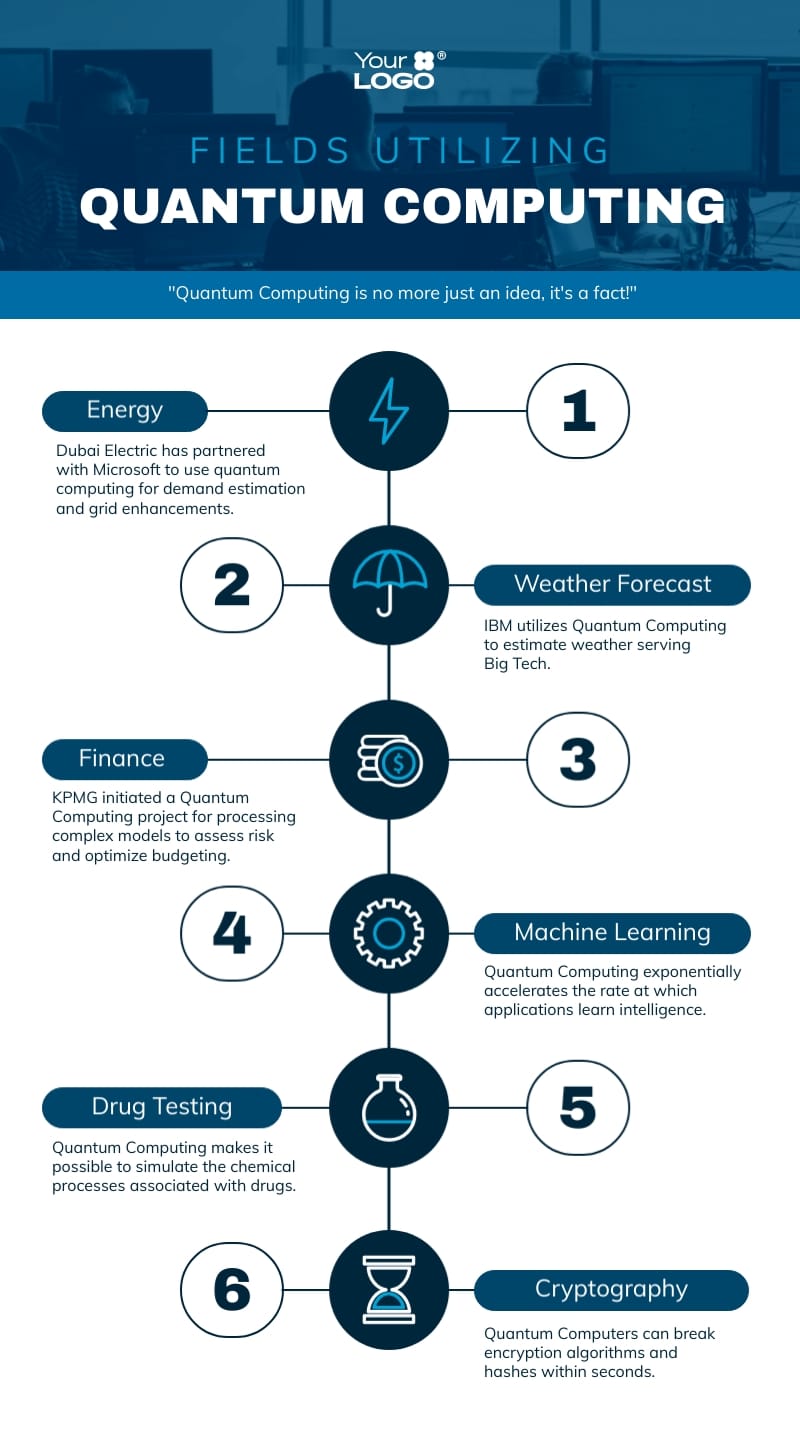
Cryptography is the backbone of digital security, protecting everything from online transactions to personal communications. Most modern cryptography relies on the difficulty of certain mathematical problems, such as factoring large numbers, which are computationally intensive for classical computers. However, quantum computers have the potential to solve these problems exponentially faster.
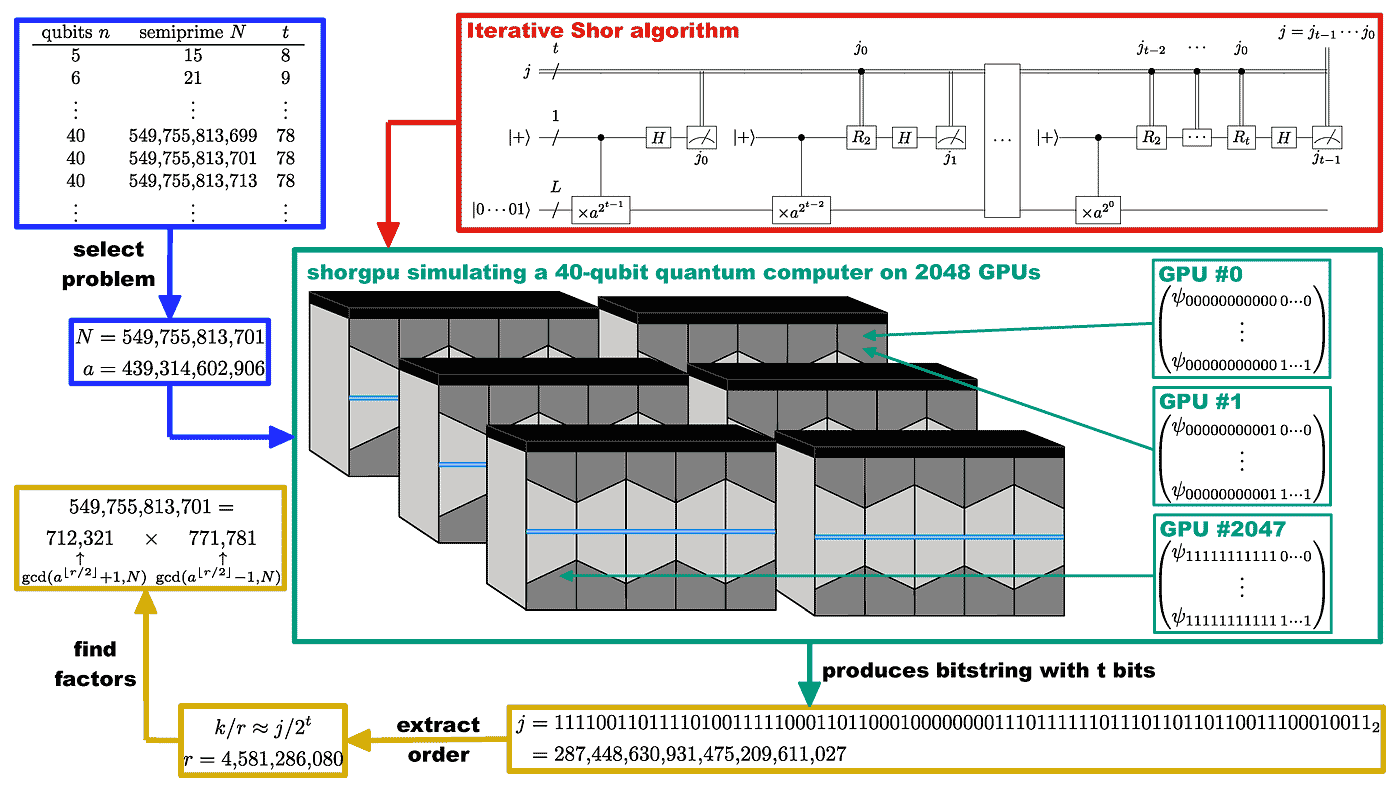
Shor's Algorithm: The Cryptographic Threat
One of the most significant quantum algorithms is Shor's algorithm, which can efficiently factor large integers. This poses a direct threat to encryption methods like RSA and ECC, widely used in securing digital communications and transactions. In the context of Bitcoin, the SHA-256 hashing algorithm, which underpins Bitcoin's security, could be vulnerable to quantum attacks if quantum computers reach sufficient power, as discussed in The Quantum Insider.
Bitcoin and the Quantum Threat
Bitcoin, the pioneering cryptocurrency, relies on the security of its underlying cryptographic algorithms. The SHA-256 algorithm is used to secure Bitcoin transactions and maintain the integrity of the blockchain. However, as quantum computing progresses, the robustness of SHA-256 is being called into question.
Why Bitcoin Encryption is at Risk
Quantum computers could theoretically perform brute force attacks on SHA-256 encryption significantly faster than classical computers. This could undermine the security of Bitcoin wallets, transactions, and the blockchain itself. Google's recent warning highlights that the timeline for this threat may be shorter than previously expected due to advancements in quantum technology, as reported by Google's research.
The Timeline to Quantum Vulnerability
Initially, experts believed that practical quantum computers capable of breaking SHA-256 encryption were decades away. However, recent advancements suggest that such capabilities could be realized within the next decade. This accelerated timeline necessitates urgent action from the Bitcoin community to safeguard against potential quantum attacks, as highlighted by The Quantum Insider.
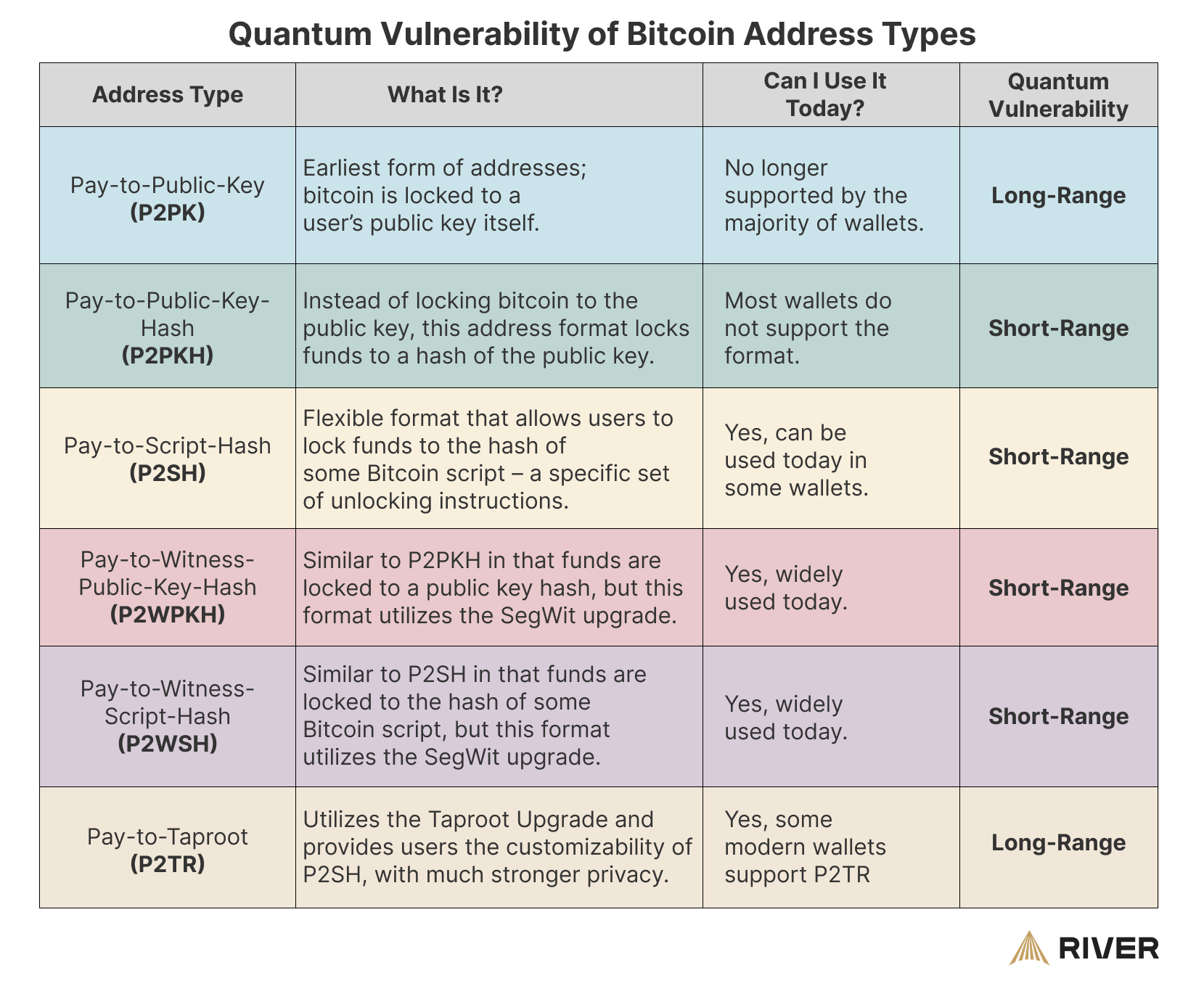
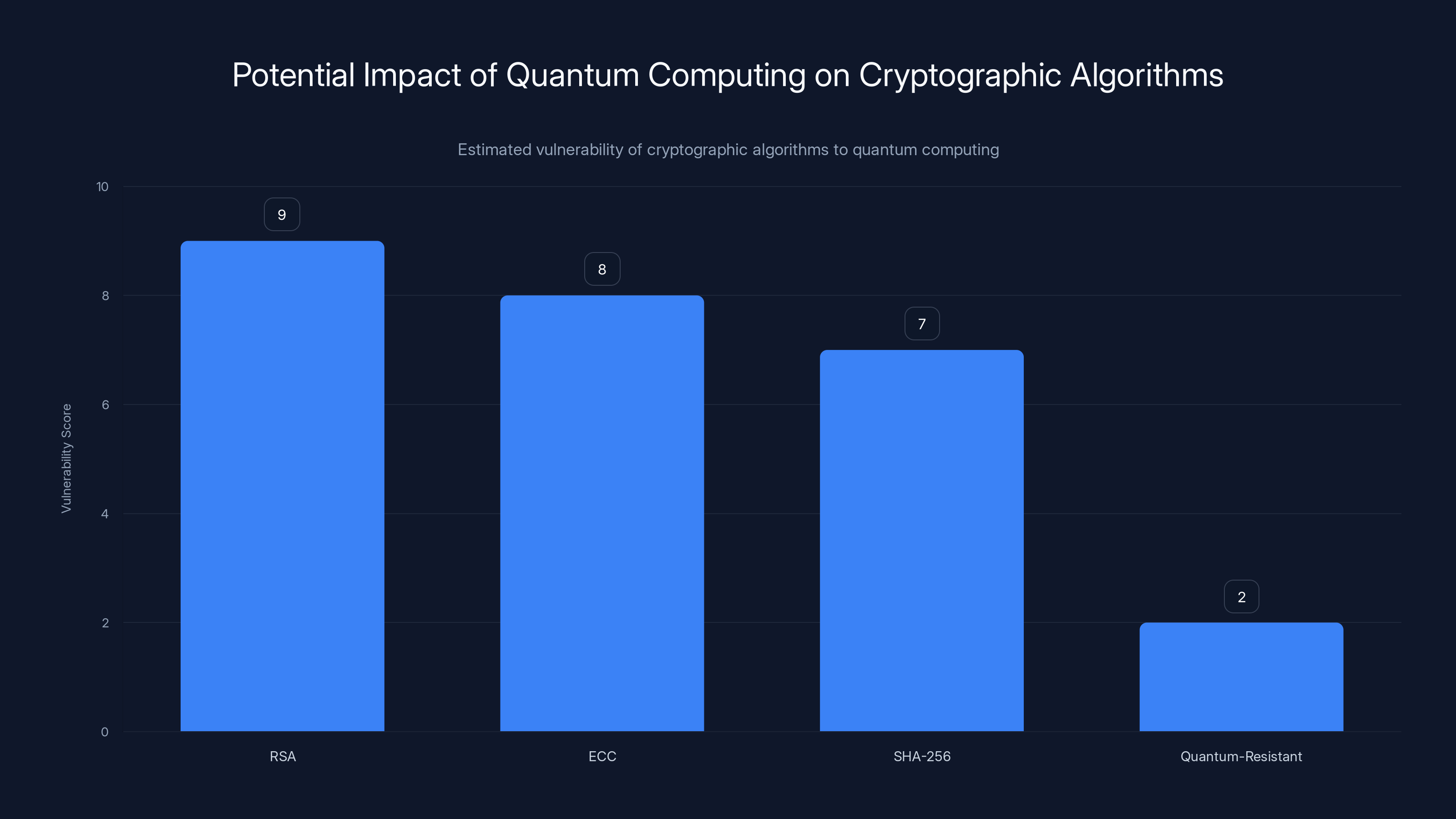
RSA and ECC are highly vulnerable to quantum attacks, while SHA-256 has moderate vulnerability. Quantum-resistant algorithms offer much lower risk. Estimated data.
Preparing for a Quantum Future: Best Practices
As the quantum threat to Bitcoin becomes increasingly real, the cryptocurrency community must take proactive steps to enhance security and resilience. Here are some best practices to consider:
1. Transition to Quantum-Resistant Algorithms
Cryptographers are developing quantum-resistant algorithms that can withstand attacks from quantum computers. These algorithms are designed to be secure against both classical and quantum threats. Transitioning to these algorithms will be crucial for maintaining the security of Bitcoin and other cryptocurrencies, as emphasized by NIST's Post-Quantum Cryptography Standardization Project.
2. Diversify Cryptographic Strategies
Relying solely on a single cryptographic method can be risky. Implementing a diverse range of cryptographic techniques can provide added layers of security. Consider integrating lattice-based, hash-based, and multivariate polynomial cryptographic methods to protect sensitive data.
The Role of Governments and Regulatory Bodies
Governments and regulatory bodies have a critical role to play in preparing for a quantum future. By setting standards and guidelines for quantum-resistant cryptography, they can ensure a coordinated and effective response to the emerging threat.
Collaborative Efforts
Collaboration between governments, academic institutions, and industry leaders is essential to address the quantum threat. Initiatives like the NIST Post-Quantum Cryptography Standardization Project are crucial in developing and standardizing new cryptographic methods.

Future Trends and Recommendations
As quantum computing continues to evolve, staying informed and adaptable will be key to navigating the shifting landscape of cybersecurity. Here are some trends and recommendations to consider:
1. Continuous Research and Development
Ongoing research into quantum computing and cryptography is essential to staying ahead of potential threats. Investing in R&D will help develop innovative solutions to emerging challenges, as noted by HPCwire.
2. Education and Awareness
Raising awareness about the quantum threat is crucial for ensuring that stakeholders are prepared to take action. Educational initiatives and workshops can help disseminate knowledge about quantum computing and its implications.
3. Building Robust Infrastructure
Developing infrastructure that can withstand quantum attacks is vital for maintaining the integrity of digital systems. This includes upgrading hardware and software to support quantum-resistant protocols.
Conclusion: Embracing the Quantum Challenge
The advent of quantum computing presents both challenges and opportunities for the digital world. While the threat to Bitcoin encryption is real, it also serves as a catalyst for innovation and collaboration. By embracing the quantum challenge and taking proactive measures, the cryptocurrency community can secure its future in a rapidly evolving technological landscape.
FAQ
What is quantum computing?
Quantum computing is a type of computing that uses quantum bits (qubits) to process information. Unlike classical bits, qubits can exist in multiple states simultaneously, enabling quantum computers to perform complex calculations at unprecedented speeds.
How does quantum computing threaten Bitcoin encryption?
Quantum computing poses a threat to Bitcoin encryption because it can solve complex mathematical problems, like those used in cryptographic algorithms, much faster than classical computers. This could potentially compromise the security of Bitcoin transactions and wallets, as explained by The Quantum Insider.
What are quantum-resistant algorithms?
Quantum-resistant algorithms are cryptographic methods designed to remain secure against both classical and quantum attacks. They are being developed to replace current algorithms that may be vulnerable to quantum threats.
How soon could quantum computers break Bitcoin encryption?
While it was initially believed that practical quantum computers capable of breaking Bitcoin encryption were decades away, recent advancements suggest that this could happen within the next decade, as noted by The Quantum Insider.
What can individuals and organizations do to prepare for quantum threats?
Individuals and organizations can prepare for quantum threats by transitioning to quantum-resistant algorithms, diversifying cryptographic strategies, and collaborating with governments and industry leaders to develop robust security standards.
Why is collaboration important in addressing the quantum threat?
Collaboration between governments, academia, and industry is essential in developing and standardizing new cryptographic methods that can withstand quantum attacks. Joint efforts ensure a coordinated and effective response to the emerging threat.
What role do governments play in quantum cybersecurity?
Governments play a critical role in setting standards and guidelines for quantum-resistant cryptography, ensuring that national and global security measures keep pace with technological advancements.
Key Takeaways
- Quantum computing advancements may compromise Bitcoin encryption sooner than expected.
- Transitioning to quantum-resistant algorithms is critical for securing digital transactions.
- Collaboration between governments and the tech industry is essential to address quantum threats.
- Continuous R&D in quantum cryptography will help mitigate emerging cybersecurity risks.
- Educating stakeholders about quantum threats can facilitate proactive security measures.
Related Articles
- Understanding the Debate Over Age Verification for Online Content [2025]
- Unlock Massive Savings on TechCrunch Disrupt 2026 Tickets [2025]
- The Future of Friendship: New Apps Revolutionizing How We Connect [2025]
- Beware: How Hackers Exploit LinkedIn's Job Alerts to Steal Your Login Details [2025]
- Mastering Game Audio: How Battlefield 6's Team Redefines Soundscapes [2025]
- Can a MacBook Neo Handle Everyday Work? Expert Review and Insights [2025]
![Quantum Computing's Looming Threat to Bitcoin Encryption [2025]](https://tryrunable.com/blog/quantum-computing-s-looming-threat-to-bitcoin-encryption-202/image-1-1775514849865.jpg)



