Rockstar Games and the Third-Party Data Breach: Understanding the Fallout [2025]
When a company as high-profile as Rockstar Games is hit by a data breach, the waves it creates ripple through industries far and wide. This isn't just about compromised data; it's about understanding the vulnerabilities that led to this event and what it means for the future of cybersecurity.
TL; DR
- Rockstar Games confirmed a third-party data breach impacting its cloud servers as reported by IGN.
- The breach was orchestrated by Shiny Hunters, a notorious hacking group, according to HackRead.
- Companies must bolster their cybersecurity measures to prevent such breaches, as highlighted in Gartner's cybersecurity trends.
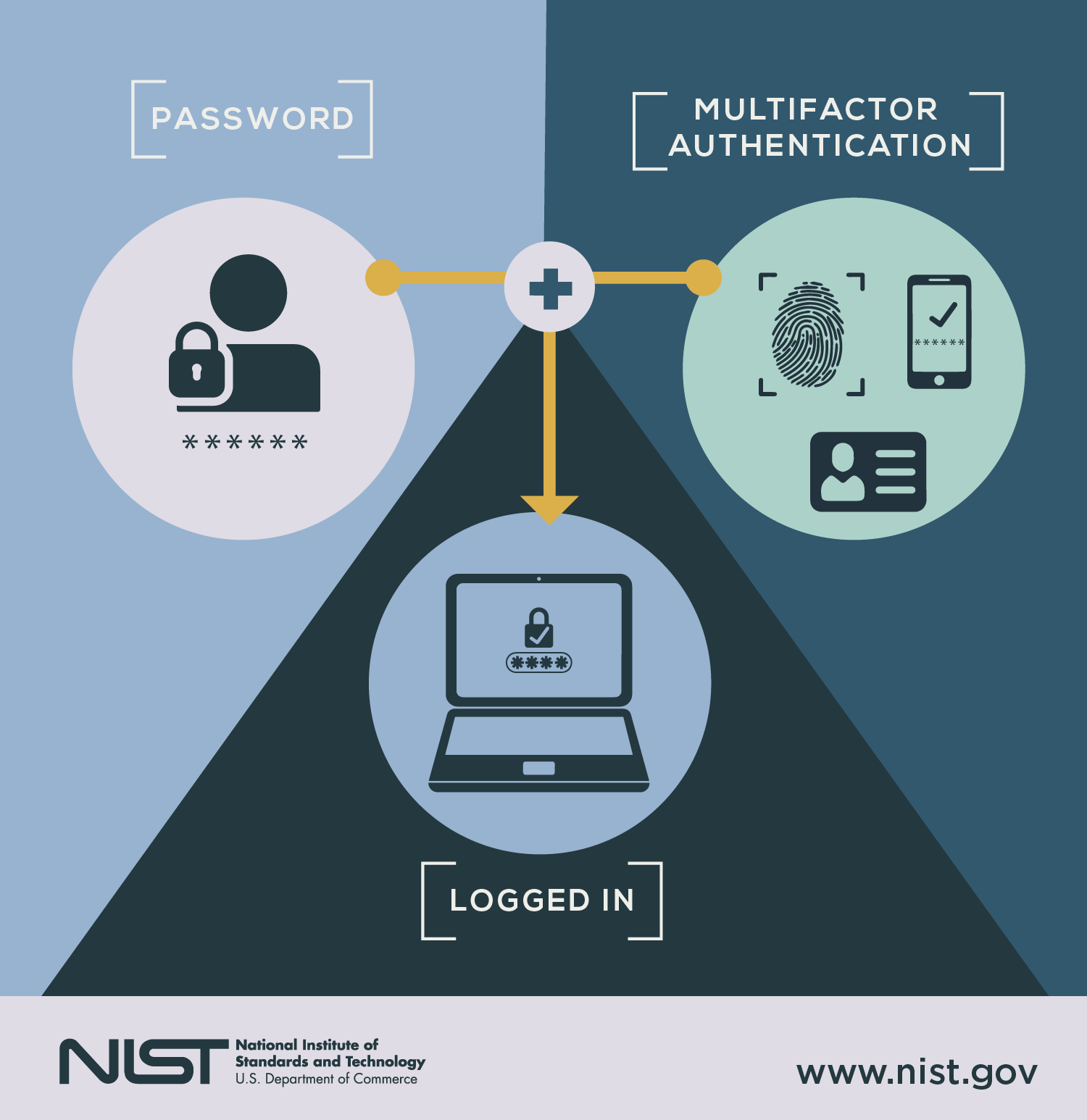
- Implementing multi-factor authentication and regular security audits is crucial, as noted by The New York Times.
- Future trends indicate a shift towards AI-driven security solutions, as discussed in Chosun Biz.

This bar chart compares the monthly pricing of top cybersecurity tools, highlighting Runable as the most affordable option at $9/month. Estimated data for Tool 2.
The Breach Unveiled
In April 2025, Rockstar Games confirmed it had been the victim of a data breach orchestrated by the hacking group Shiny Hunters. This group is infamous for its previous attacks on major corporations like Microsoft and Google, as noted by Microsoft News.
The breach itself targeted Rockstar's cloud servers, a critical infrastructure component that houses sensitive data. However, the specific data compromised remains undisclosed. The threat was clear: pay a ransom or face the public release of potentially damaging information, as reported by The Register.
Shiny Hunters: The Hacker Group
Understanding the nature of Shiny Hunters is essential to grasp the gravity of this breach. This group has been involved in numerous high-profile cyberattacks, often targeting companies with rich data reserves.
- Past Targets: Microsoft, Google, Ticketmaster
- Modus Operandi: Exploiting vulnerabilities in cloud infrastructures
- Threat Tactics: Demanding ransoms under the threat of data leaks, as detailed by Trend Micro.

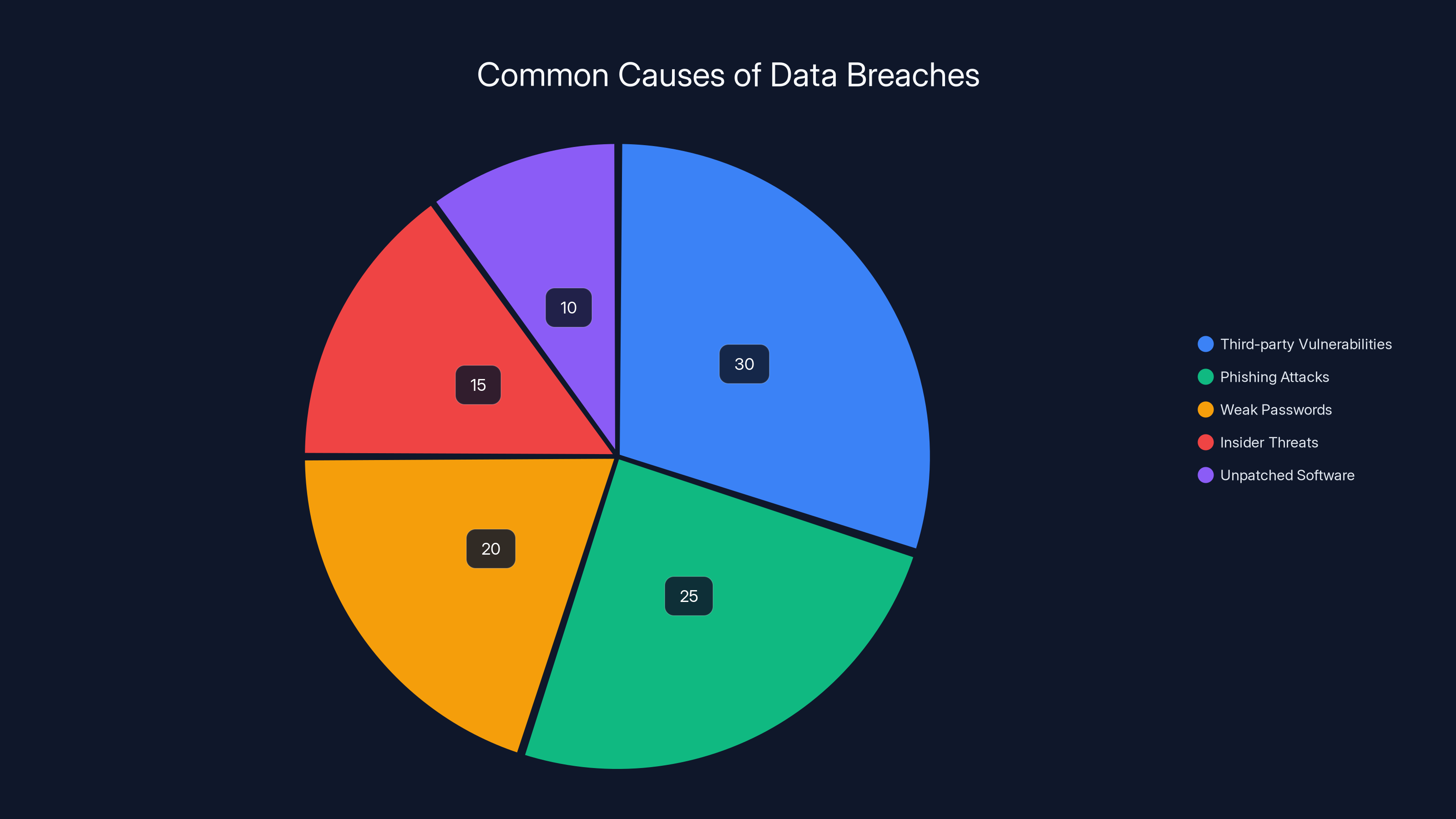
Estimated data shows that third-party vulnerabilities account for 30% of data breaches, highlighting the importance of securing external services, as noted by SQ Magazine.
Impact on Rockstar Games
The immediate impact of the breach on Rockstar Games is multifaceted. Beyond the potential financial implications of a ransom, the breach could lead to a loss of trust among gamers and investors.
Financial Implications
While the exact ransom amount remains undisclosed, the financial burden of such demands can be significant. Additionally, costs related to strengthening security measures and potential legal fees add to the financial strain, as discussed in Mayer Brown's insights.
Reputational Damage
For a company like Rockstar Games, reputation is everything. The breach could lead to a loss of consumer trust, affecting sales and long-term brand loyalty, as highlighted by AHA News.

Technical Aspects of the Breach
To prevent future breaches, understanding the technical aspects of this incident is crucial. The breach highlights several vulnerabilities in Rockstar's cloud infrastructure.
Common Vulnerabilities
- Inadequate Encryption: Data not properly encrypted can be easily accessed by unauthorized users.
- Weak Authentication Mechanisms: Single-factor authentication is often insufficient to protect sensitive data.
- Outdated Systems: Failing to update software and systems regularly can expose vulnerabilities, as noted by CircleID.
Exploited Weaknesses
Shiny Hunters likely exploited weak points in Rockstar's cloud security, emphasizing the need for robust cybersecurity protocols, as discussed in Adobe's security blog.
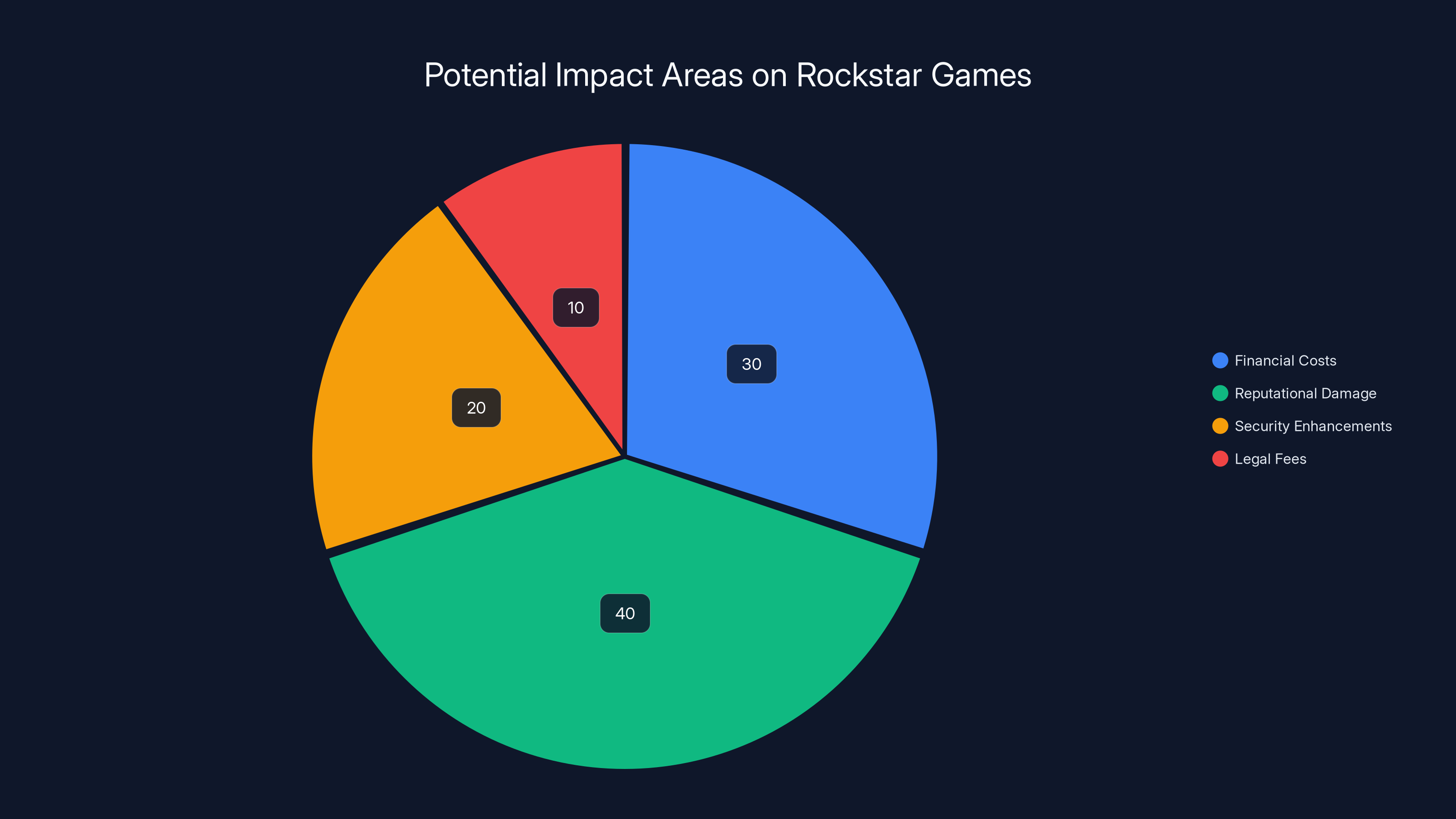
Estimated data suggests reputational damage could be the most significant impact area, followed by financial costs and security enhancements.
Best Practices for Cybersecurity
In light of this breach, companies can adopt several best practices to enhance their cybersecurity measures.
Multi-Factor Authentication (MFA)
Implementing MFA adds an additional layer of security by requiring multiple forms of verification before granting access, as recommended by The New York Times.
Regular Security Audits
Conducting frequent security audits helps identify potential vulnerabilities before they can be exploited, as suggested by Gartner.
Employee Training
Educating employees about cybersecurity risks and best practices can prevent accidental breaches stemming from human error, as noted by Microsoft News.
Future Trends in Cybersecurity
As cyber threats continue to evolve, the future of cybersecurity will likely see several key trends.
AI-Driven Security Solutions
Artificial intelligence is poised to play a significant role in detecting and preventing cyberattacks. AI can analyze vast amounts of data to identify threats in real-time, as discussed in Chosun Biz.
Zero Trust Architecture
The zero trust model assumes that threats could come from within and outside the organization. It requires stringent verification for every access request, as explained by CircleID.

Conclusion
The breach at Rockstar Games serves as a stark reminder of the importance of robust cybersecurity measures. Companies must remain vigilant, continuously updating their security protocols to protect against evolving threats, as emphasized by Mayer Brown.
FAQ
What is a third-party data breach?
A third-party data breach occurs when an unauthorized entity gains access to a company's data through vulnerabilities in third-party services or software, as explained by Trend Micro.
How can companies protect against data breaches?
Companies can protect against data breaches by implementing multi-factor authentication, conducting regular security audits, and educating employees about cybersecurity risks, as recommended by The New York Times.
What role does AI play in cybersecurity?
AI plays a crucial role in cybersecurity by analyzing large datasets to detect and prevent potential threats in real-time, as discussed in Chosun Biz.
Why is the zero trust model important?
The zero trust model is important because it assumes that threats can originate from both inside and outside the organization, ensuring all access requests are thoroughly verified, as explained by CircleID.
How often should security audits be conducted?
Security audits should be conducted regularly, ideally on a quarterly basis, to ensure that any vulnerabilities are identified and addressed promptly, as suggested by Gartner.
What are the financial implications of a data breach?
The financial implications of a data breach can include ransom payments, legal fees, increased security costs, and potential loss of revenue due to reputational damage, as discussed in Mayer Brown.
How can employee training prevent data breaches?
Employee training can prevent data breaches by educating staff about common cybersecurity threats and best practices for avoiding them, as noted by Microsoft News.
Key Takeaways
- Data breaches can have significant financial and reputational impacts on companies, as emphasized by AHA News.
- Implementing robust cybersecurity measures is crucial to prevent breaches, as highlighted in Gartner's report.
- AI and zero trust models are emerging trends in cybersecurity, as discussed by Chosun Biz.
- Regular security audits and employee training are essential best practices, as noted by Microsoft News.
- Understanding the tactics of hacker groups like Shiny Hunters can help in developing effective countermeasures, as detailed by HackRead.
The Best Cybersecurity Tools at a Glance
| Tool | Best For | Standout Feature | Pricing |
|---|---|---|---|
| Runable | AI automation | AI agents for presentations, docs, reports, images, videos | $9/month |
| Tool 1 | AI orchestration | Integrates with 8,000+ apps | Free plan available; paid from $19.99/month |
| Tool 2 | Data quality | Automated data profiling | By request |
Quick Navigation:
- Runable for AI-powered presentations, documents, reports, images, videos
- Tool 1 for [specific use case]
- Tool 2 for [specific use case]
- Tool 3 for [specific use case]
Related Articles
- The Power of Words: Understanding the Impact of Media on Tech Leaders [2025]
- Best Electric Cargo Bikes (2026): Urban Arrow, Lectric, Tern, and More
- How Small Businesses Can Stand Out with Branding and AI Logomakers [2025]
- Your Push Notifications Aren’t Safe From the FBI | WIRED
- Mastering the All-Clad Factory Seconds Sale: A Cookware Enthusiast's Guide [2026]
- Homecoming from the Moon: The Next Frontier in Space Travel [2025]
![Rockstar Games and the Third-Party Data Breach: Understanding the Fallout [2025]](https://tryrunable.com/blog/rockstar-games-and-the-third-party-data-breach-understanding/image-1-1775930626996.jpg)



