Solving the Shadow IT Crisis in Travel [2025]
Shadow IT isn't new, but in the travel industry, it's becoming a massive headache. As travel companies embrace digital transformation, the unsanctioned use of technology—known as shadow IT—grows. This unapproved tech usage opens the door to security risks and inefficiencies. Let's dive into how we can tackle this issue head-on.
TL; DR
- Rising Risk: Shadow IT in travel poses significant security threats and operational inefficiencies, as highlighted by The Hacker News.
- Comprehensive Strategy: Implement a robust IT governance framework to manage technology usage, as suggested by Microsoft's AI governance framework.
- Best Practices: Conduct regular audits, employee training, and strategic tech adoption, as recommended by Wiz's vulnerability management best practices.
- Future Trends: AI and machine learning will play key roles in detecting and managing shadow IT, according to TechTarget's strategic approaches.
- Bottom Line: Proactive management of shadow IT ensures security and optimal performance, as discussed in TechRadar's analysis.

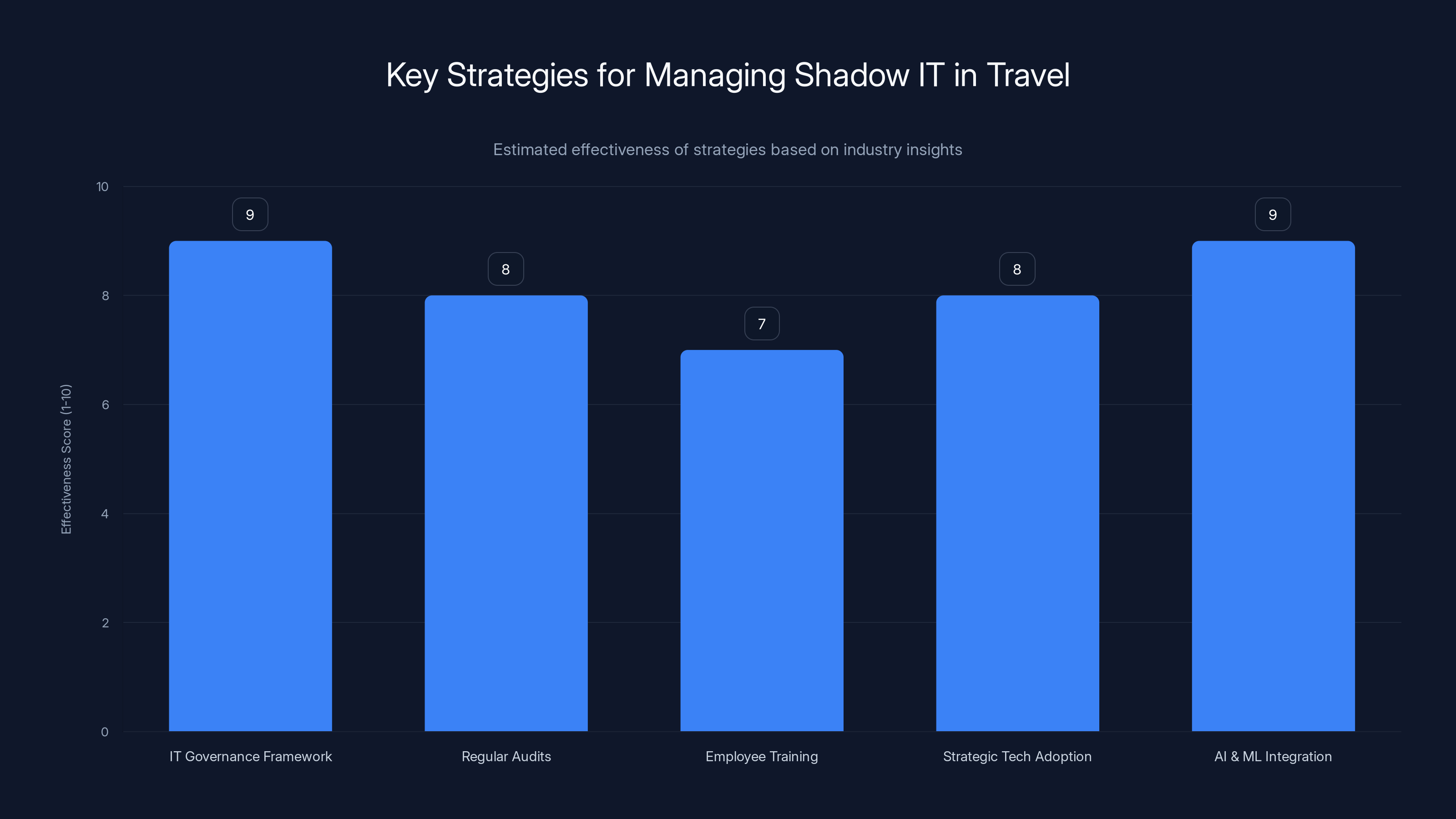
Implementing a robust IT governance framework and integrating AI/ML are estimated to be the most effective strategies for managing shadow IT in travel. Estimated data.
What is Shadow IT?
Shadow IT refers to the use of information technology systems, devices, applications, and services without explicit IT department approval. In the travel industry, this might include employees using unauthorized apps for booking, data sharing, or communication. While this can increase flexibility and efficiency, it also introduces significant risks, as noted by EPC Group's report on unauthorized AI tool usage.
Risks Associated with Shadow IT
- Security Vulnerabilities: Unapproved tools may not meet security standards, leaving sensitive data exposed, as highlighted by The Hacker News.
- Data Loss: Without IT oversight, data can be lost or mishandled.
- Compliance Issues: Violating industry regulations can lead to severe penalties, as discussed in CoSN's report on responsible technology use.
- Operational Inefficiencies: Disparate systems can create bottlenecks and miscommunications.

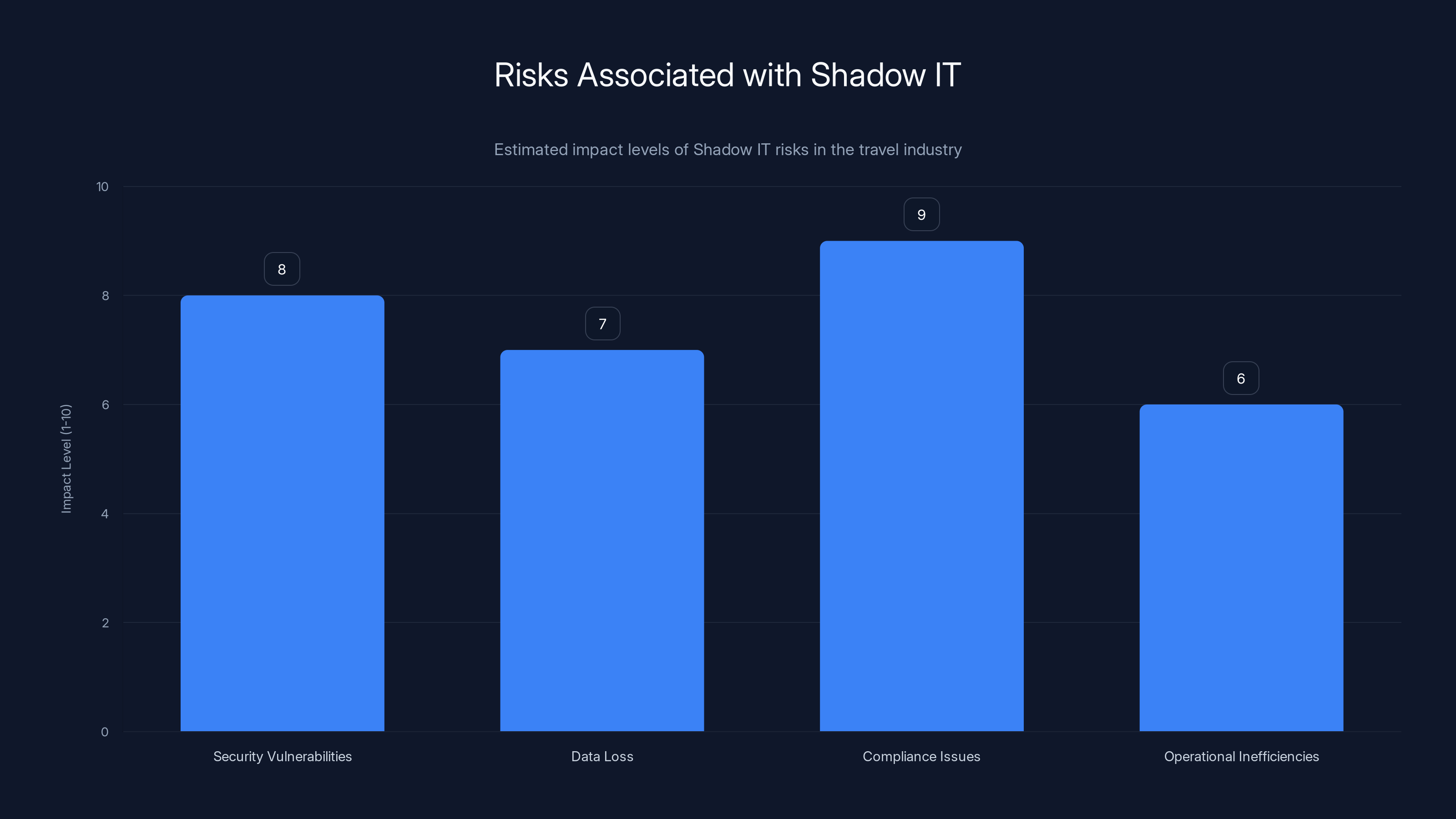
Security vulnerabilities and compliance issues are the most significant risks associated with Shadow IT in the travel industry. (Estimated data)
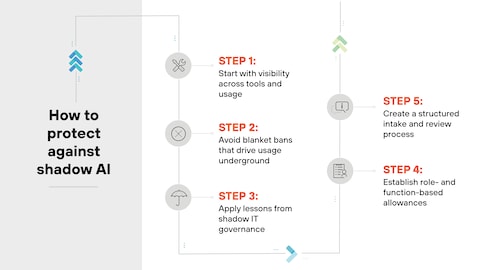
Implementing a Comprehensive Strategy
Addressing shadow IT requires a multi-faceted approach. Here's a detailed guide:
1. Develop a Robust IT Governance Framework
Creating a clear framework is the first step in managing shadow IT. This involves:
- Policy Creation: Define acceptable use policies for technology, as outlined by Microsoft's governance framework.
- Role Definition: Clearly outline IT roles and responsibilities.
- Risk Management: Assess and mitigate potential risks from shadow IT.
2. Conduct Regular Audits
Frequent audits help identify unauthorized tools within the organization. Consider these steps:
- Inventory Assessment: Regularly update lists of approved and unapproved technologies.
- Usage Analysis: Monitor network traffic to identify unauthorized applications, as suggested by Vanta's enterprise features.
Training and Awareness
3. Employee Training Programs
Training employees about the risks of shadow IT is crucial. Focus on:
- Awareness Campaigns: Educate staff on the importance of using approved tools.
- Security Workshops: Provide training on secure technology practices, as emphasized by StateScoop's digital resource initiatives.
4. Foster a Culture of Trust
Create an environment where employees feel comfortable discussing their tech needs. This can:
- Encourage Transparency: Employees are more likely to report shadow IT if they trust the process.
- Promote Collaboration: Work with staff to find solutions that meet their needs without compromising security.

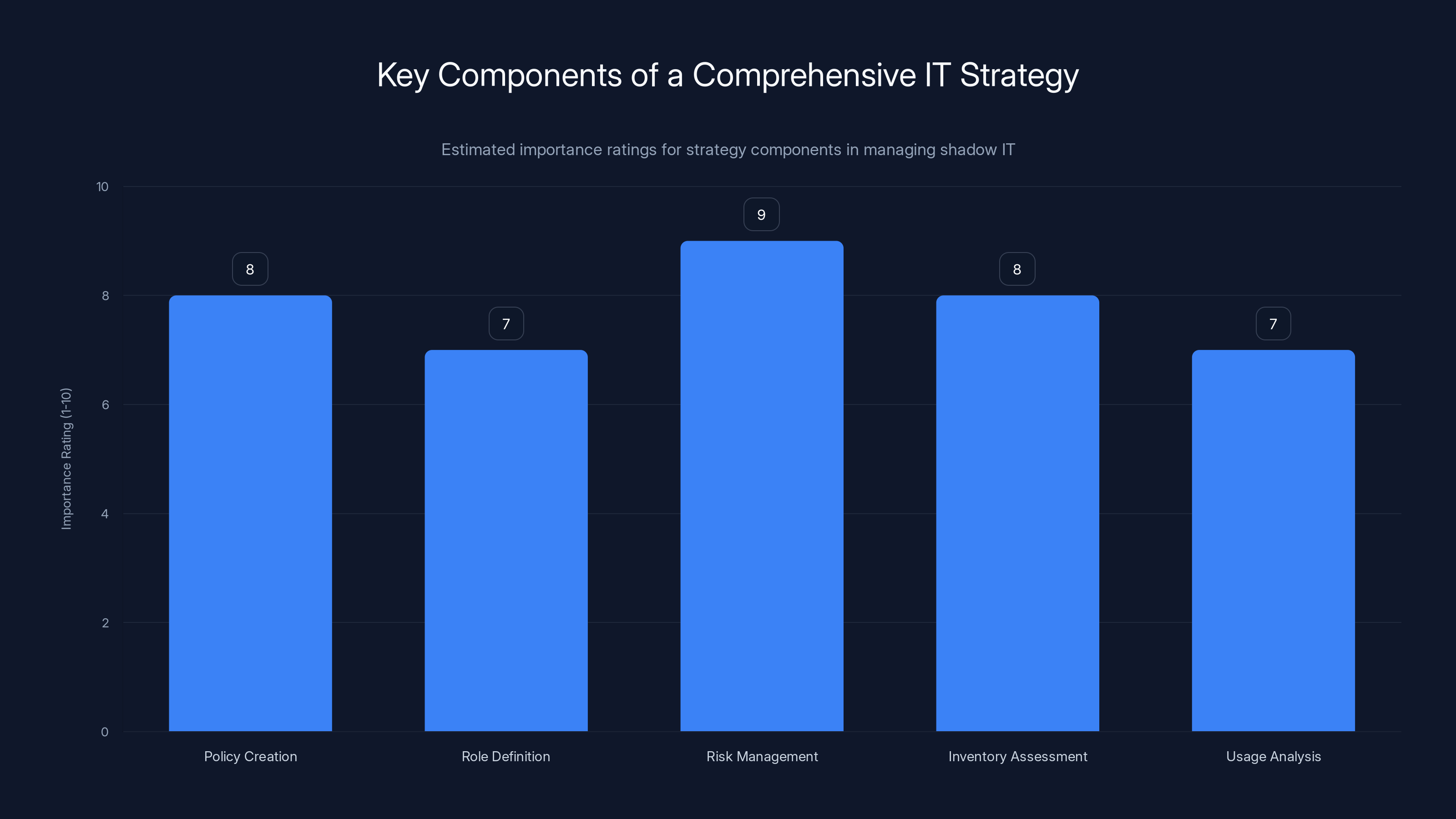
Risk management and policy creation are crucial components in managing shadow IT, with high importance ratings. Estimated data.
Embracing Technology
5. Adopt Strategic Technology Solutions
Integrate tools that meet business needs while ensuring security. For example:
- Runable: An AI-powered platform that helps streamline presentations, documents, and reports, reducing the need for unauthorized tools. Try Runable For Free
- Cloud-Based Solutions: Offer secure, scalable options that reduce the need for shadow IT.
6. Leverage AI and Machine Learning
AI can help identify shadow IT by:
- Pattern Recognition: Detect unusual usage patterns that may indicate unauthorized tools, as noted by Nature's study on AI pattern recognition.
- Automated Alerts: Notify IT teams of potential shadow IT activities.
Common Pitfalls and Solutions
Overlooking Small Applications
Small apps can seem harmless but pose significant risks. Mitigate this by:
- Comprehensive Audits: Include all applications in audits, regardless of size.
- Education: Teach employees about the risks of using unapproved apps.
Relying Solely on Technology
Technology alone can't solve shadow IT. Complement tech solutions with:
- Human Oversight: Regularly review and update policies based on audit findings.
- Employee Engagement: Involve staff in decision-making processes for technology adoption.
Future Trends
The landscape of shadow IT is evolving. Here's what to expect:
- Increased AI Use: AI will become more prevalent in detecting and managing shadow IT, as highlighted by TechTarget.
- Enhanced Security Measures: Expect more robust security protocols as threats evolve.
- Greater Integration: Tools like Runable will offer seamless integration to meet diverse needs.

Conclusion
In the travel industry, managing shadow IT is critical. By implementing comprehensive strategies, leveraging technology, and fostering a culture of trust, companies can mitigate risks and ensure efficient operations.
FAQ
What is shadow IT?
Shadow IT refers to the use of unauthorized tech within an organization, often leading to security and compliance risks.
How can companies manage shadow IT?
Implementing a robust governance framework and conducting regular audits are key strategies.
What role does AI play in managing shadow IT?
AI helps detect unauthorized tech usage through pattern recognition and automated alerts.
Why is employee training important?
Training increases awareness, helping employees understand the risks and importance of using approved tools.
What are future trends in shadow IT management?
Expect increased use of AI, enhanced security measures, and better integration of approved tools.

Key Takeaways
- Shadow IT presents security and operational risks in the travel industry.
- A robust IT governance framework is essential for managing shadow IT.
- Regular audits and employee training are critical components of a comprehensive strategy.
- AI and machine learning will play significant roles in future shadow IT management.
- Fostering a culture of trust encourages transparency and collaboration.

Related Articles
- Autonomous Agentic Assistants: Revolutionizing Scheduling with Canva AI 2.0 [2025]
- Agentic Swarms: Revolutionizing AI Deployment and Security [2025]
- Navigating Seamlessly: Google's AI Mode Update and Its Impact on Web Browsing [2025]
- How Gemini Leverages Google Photos for Personalized AI Image Creation [2025]
- Mastering AI Observability: A Deep Dive into InsightFinder's Approach [2025]
- Navigating Bluesky's Regional Server Challenges: An In-Depth Analysis [2025]
![Solving the Shadow IT Crisis in Travel [2025]](https://tryrunable.com/blog/solving-the-shadow-it-crisis-in-travel-2025/image-1-1776423887233.jpg)



