Understanding the Chat GPT Desktop App Security Breach for Mac [2025]
Last month, a jolt went through the tech community when news broke: the Chat GPT desktop app for Mac was hit with a security breach. Many users were left wondering what it means for their data and how to better protect themselves in the future. In this comprehensive guide, we're diving deep into the details of the breach, examining its causes, implications, and best practices for safeguarding your digital environment.
TL; DR
- Security Breach Overview: Chat GPT's Mac app experienced a breach due to a compromised open-source library, as detailed in a report by 9to5Mac.
- Impact Assessment: No user data was accessed or compromised, according to OpenAI's investigation.
- Immediate Response: OpenAI issued a software update and engaged third-party forensic experts, as noted in Wiz's AI security tools guide.
- Best Practices: Regular software updates and cautious use of open-source code remain critical.
- Future Recommendations: Enhanced security protocols and proactive threat monitoring could mitigate future risks.
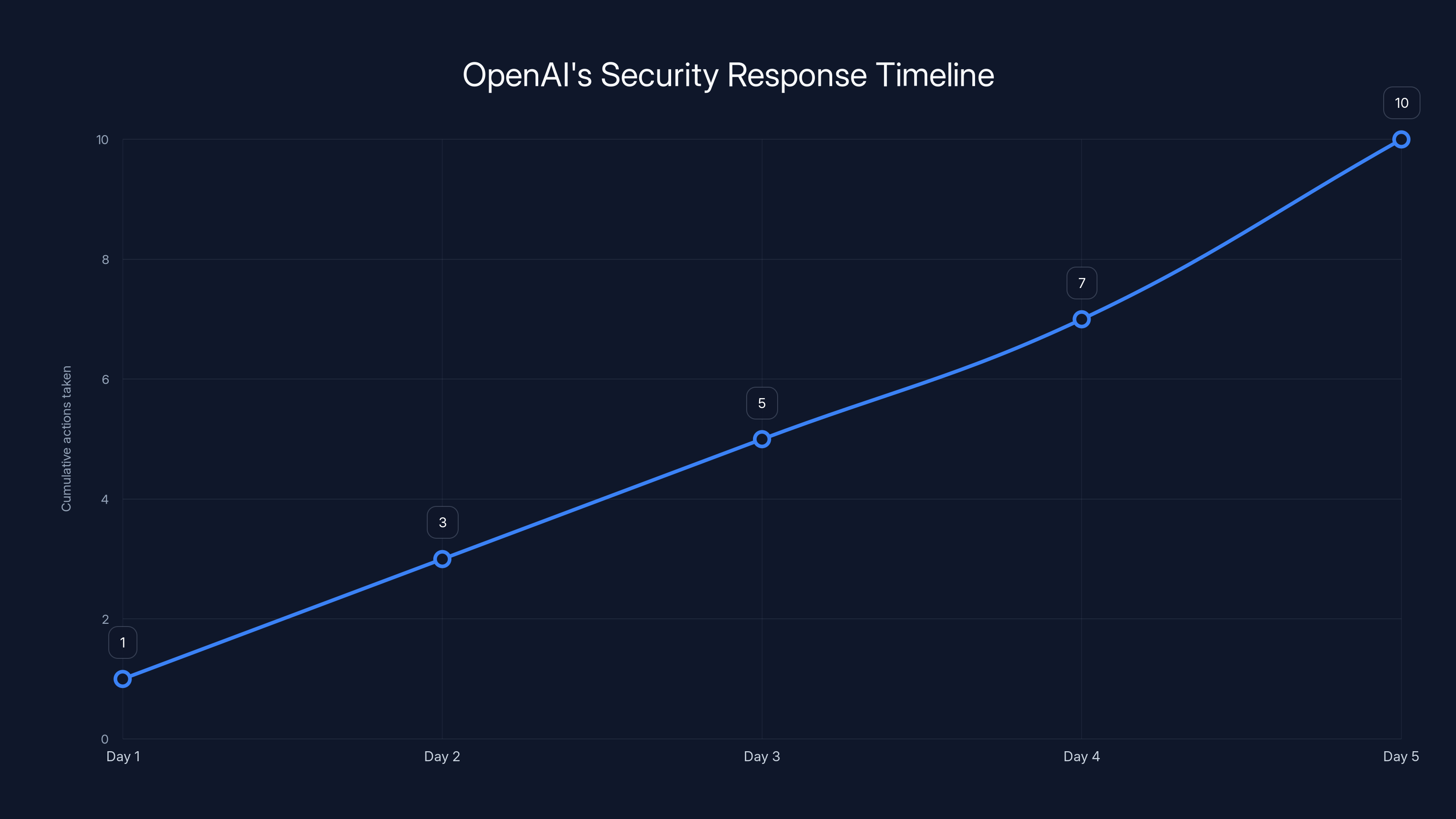
OpenAI's response to the breach was swift, with significant actions taken within the first five days to ensure security and transparency.
The Initial Breach: What Happened?
In early 2025, OpenAI's Chat GPT app for Mac users experienced an unexpected security breach. According to 9to5Mac, the breach involved two compromised employee devices within the company. The root cause? A compromised open-source library integrated into the app. The breach did not lead to any user data being accessed, according to OpenAI's official statements.
The Role of Open-Source Libraries
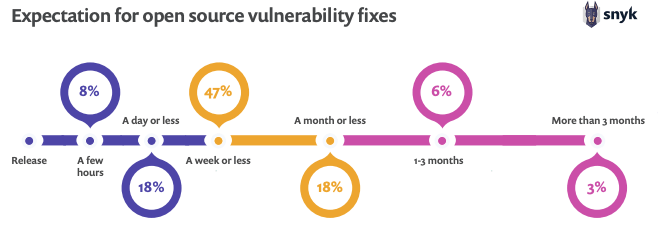
Open-source libraries are fundamental in software development, enabling developers to build applications rapidly by leveraging existing code. However, they come with risks. A single vulnerability in a library can be a gateway for malicious actors, as highlighted in Industrial Cyber's analysis of AI-enabled cyberattacks.
OpenAI's Response
Upon detecting the breach, OpenAI acted swiftly, engaging a third-party digital forensics and incident response firm to investigate. The company assured users that no systems were compromised and that only limited credential material was exfiltrated, as reported by Reuters.

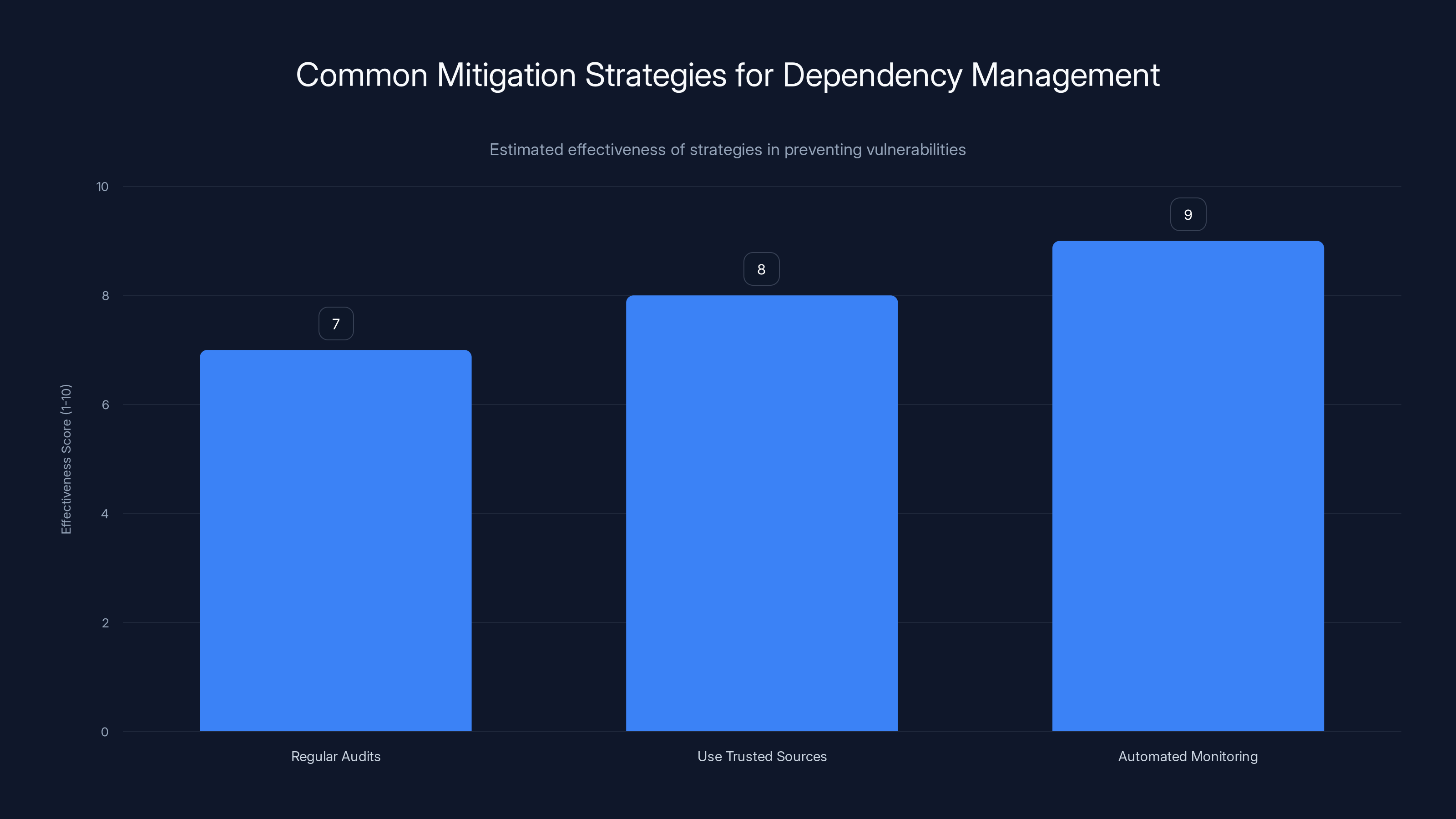
Automated monitoring is estimated to be the most effective strategy for managing dependencies and preventing vulnerabilities. Estimated data.
Why It Happened: A Technical Dive
This breach underscores a significant challenge in the tech industry: the reliance on third-party code. Let's explore the technical details and see where things might have gone wrong.
The Compromised Library
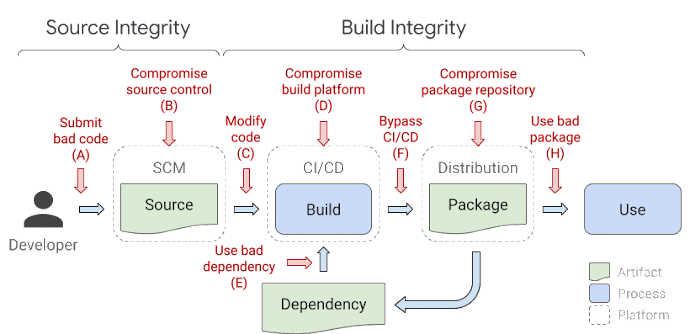
The specific library that was compromised hasn't been disclosed, but the situation highlights a common issue—dependencies. When libraries have dependencies, they can inadvertently inherit vulnerabilities from them, as explained in Rescana's report on supply chain attacks.
- Dependency Chains: Libraries often depend on other libraries, creating a complex web. A vulnerability in one can affect all applications using it.
- Supply Chain Attacks: Such attacks target the software's development process. They can be hard to detect and devastating in impact, as discussed in Industrial Cyber's insights on AI-driven supply chains.
Mitigation Strategies
For developers, understanding and managing dependencies is crucial. Here are some strategies:
- Regular Audits: Periodically review and update all libraries and their dependencies.
- Use Trusted Sources: Only integrate libraries from reputable sources and maintain a strict vetting process.
- Automated Monitoring: Use tools that scan for vulnerabilities in real time and alert you to potential risks, as recommended by NVIDIA's blog on mitigating indirect agent attacks.
The Broader Implications: User Trust and Data Security
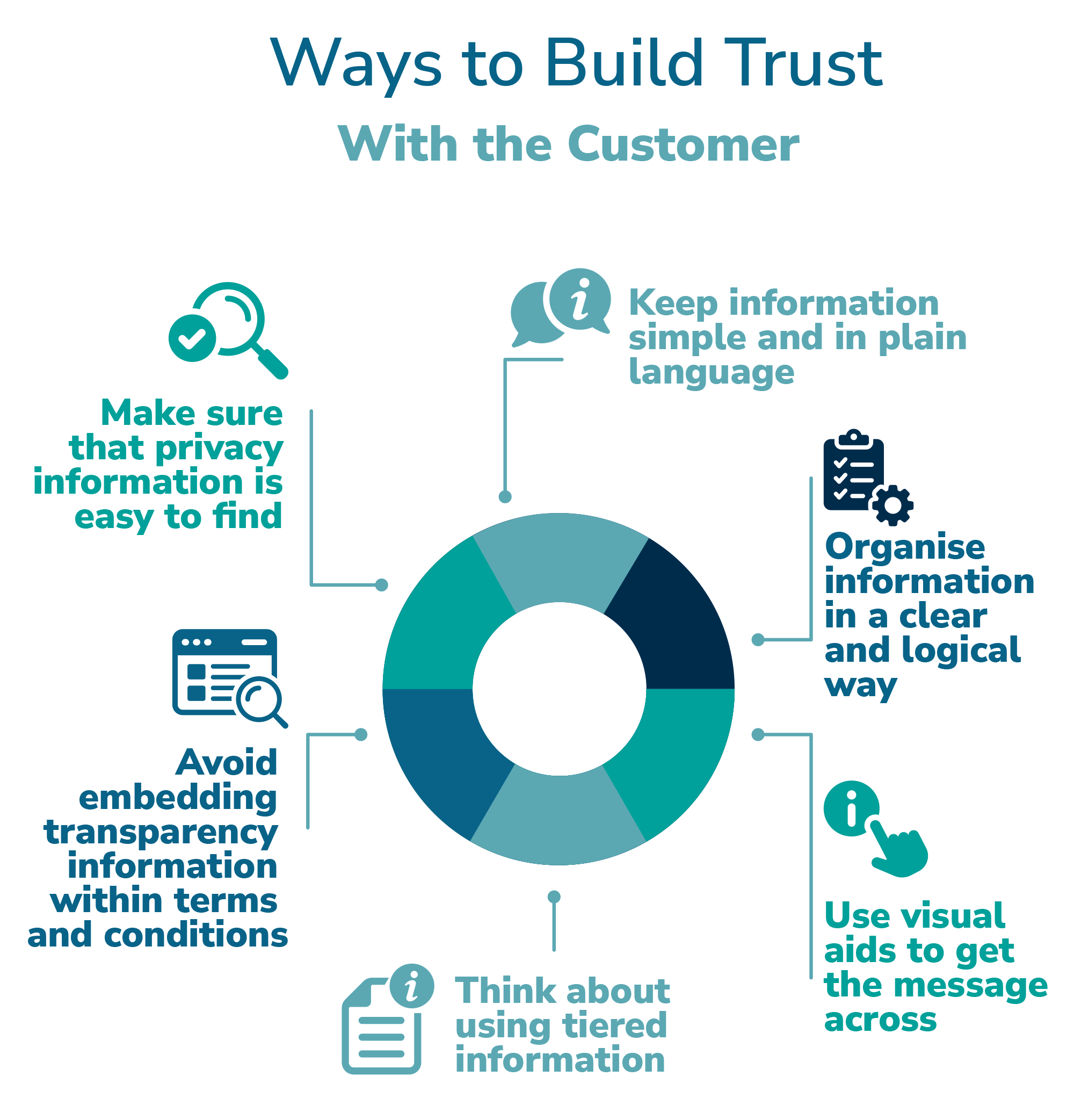
Security breaches, even those contained quickly, can shake user confidence. For OpenAI, maintaining transparency and taking swift action helped mitigate damage, but broader implications remain.
User Trust
Transparency is key. Users need to trust that a company is actively protecting their data. OpenAI's open communication about the breach is a positive step, as noted in The Information's newsletter.
Data Security Practices
Even though no user data was accessed, the breach serves as a reminder of the importance of robust data security measures. Here are some best practices:
- Encryption: Always encrypt sensitive data, both in transit and at rest.
- Access Controls: Implement strict access controls to limit who can see or modify sensitive information.
- Regular Backups: Ensure that data is regularly backed up and that recovery procedures are in place.
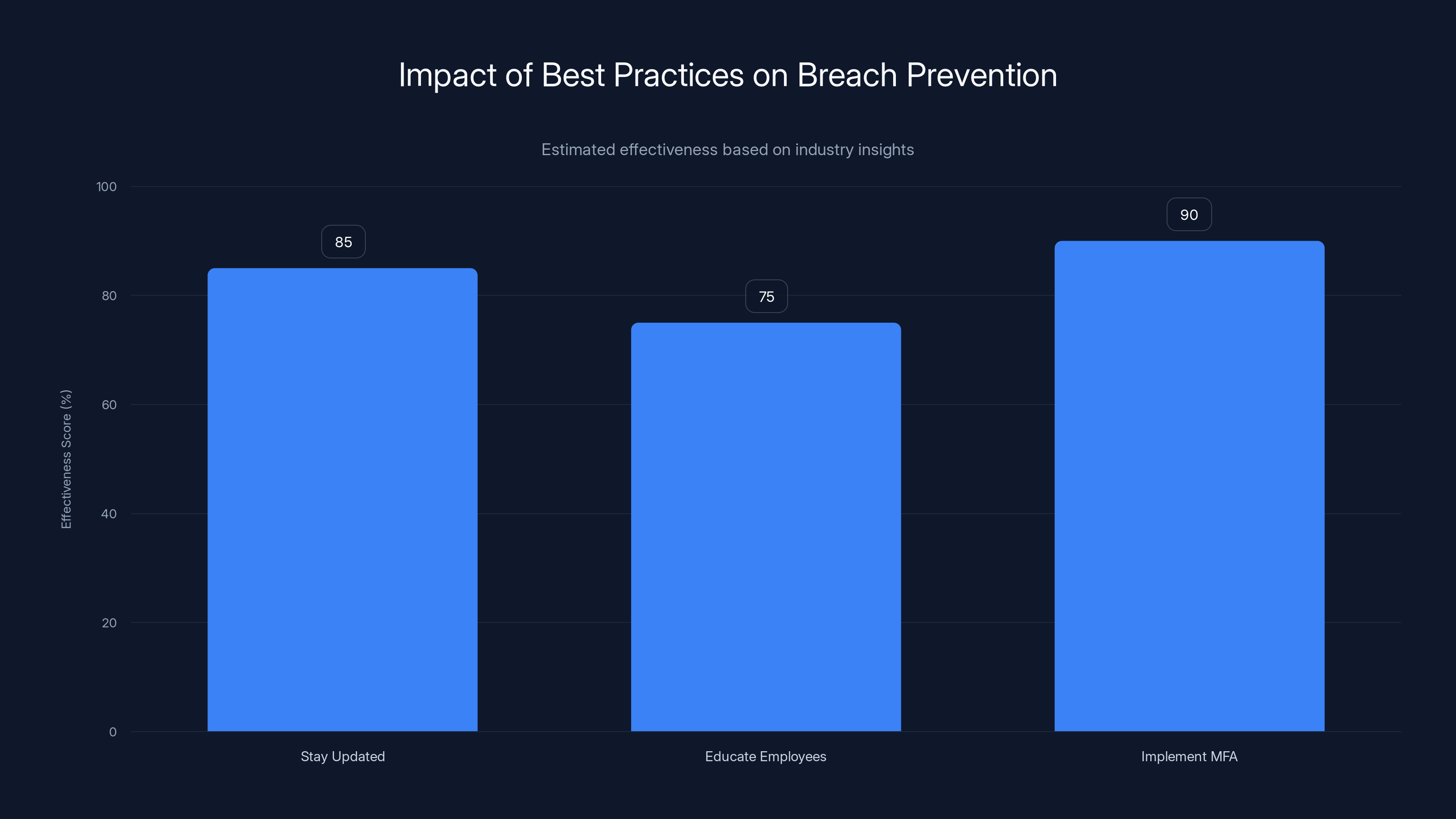
Implementing multi-factor authentication is estimated to be the most effective practice, with an effectiveness score of 90%. Estimated data.
Best Practices for Prevention
Preventing similar breaches requires a proactive approach. Here are some best practices:
Stay Updated
Regularly update all software, including operating systems and applications. Updates often include security patches for known vulnerabilities, as emphasized in the EU's regulatory framework for AI.
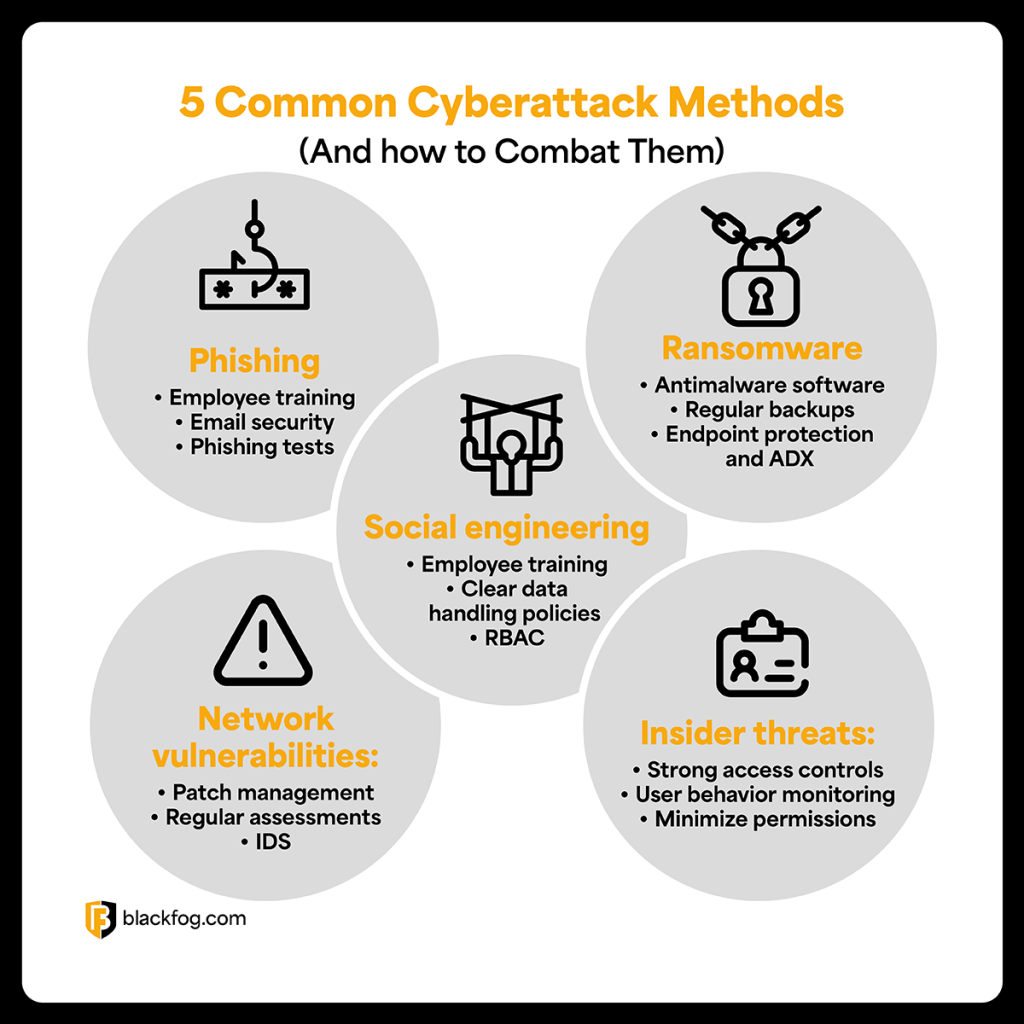
Educate Employees
Human error remains a significant risk in cybersecurity. Regular training sessions can help employees identify phishing attempts and other threats.
Implement Multi-Factor Authentication (MFA)
MFA provides an additional layer of security. Even if credentials are compromised, MFA can prevent unauthorized access, as highlighted in PR Newswire's announcement.
Common Pitfalls and How to Avoid Them
As organizations strive to secure their systems, common pitfalls can undermine these efforts. Understanding these can help you avoid them.
Pitfall 1: Complacency
Assuming that your systems are secure can lead to complacency. Regular security assessments are vital.
Pitfall 2: Ignoring Small Vulnerabilities
Small security gaps can be exploited by attackers. Address all vulnerabilities, no matter how minor they seem.
Pitfall 3: Inadequate Monitoring
Without continuous monitoring, you might miss signs of a breach. Implement automated monitoring solutions to catch anomalies early.
Future Trends in Cybersecurity
As cyber threats evolve, so must cybersecurity strategies. Here are some trends shaping the future of digital security.
AI and Machine Learning
AI and machine learning are becoming pivotal in cybersecurity, offering predictive analytics and automated threat detection.
- Behavioral Analytics: AI can analyze user behavior to detect anomalies and potential threats.
- Automated Responses: Machine learning models can automate responses to identified threats, reducing response times, as discussed in 24/7 Wall St.'s analysis.
Zero Trust Architecture
The Zero Trust model assumes that threats could be inside or outside the network, enforcing strict verification for all users and devices.
- Micro-Segmentation: Divides networks into smaller segments, each requiring separate access controls.
- Least Privilege Access: Users are given the minimum levels of access necessary for their roles.
Recommendations for Enhancing Security
To bolster your security posture, consider these recommendations:
Conduct Regular Security Audits
Regular audits can identify weaknesses in your security infrastructure, allowing you to address them promptly.
Invest in Threat Intelligence
Subscribe to threat intelligence services to stay informed about the latest threats and vulnerabilities.
Enhance Incident Response
Develop a comprehensive incident response plan to ensure you can respond swiftly and effectively to breaches.
Conclusion
The Chat GPT app's security breach serves as a wake-up call for developers and users alike. While OpenAI has managed the situation effectively, it highlights the importance of vigilance and proactive security measures. By staying informed and implementing best practices, we can better protect our digital environments in an increasingly interconnected world.
FAQ
What caused the Chat GPT app security breach?
The breach was caused by a compromised open-source library used in the app, affecting two employee devices at OpenAI, as reported by 9to5Mac.
Was any user data compromised?
According to OpenAI, no user data was accessed or compromised during the breach.
How did OpenAI respond to the breach?
OpenAI quickly issued a software update and engaged third-party digital forensics experts to investigate the breach, as noted by Wiz.
What are the best practices for securing my applications?
Regular updates, employee training, and implementing MFA are essential practices for securing applications, as emphasized in the EU's AI regulatory framework.
What is Zero Trust architecture?
Zero Trust is a security model that requires strict identity verification for every user and device, regardless of network location.
How can AI help in cybersecurity?
AI can enhance cybersecurity by providing predictive analytics, detecting anomalies, and automating responses to threats, as discussed in 24/7 Wall St..
What should I do if I suspect a security breach?
Immediately isolate the affected systems, inform your security team, and conduct a thorough investigation to assess the impact.
Why are open-source libraries risky?
While they offer valuable functionality, open-source libraries can introduce vulnerabilities if not properly managed and monitored, as highlighted in Rescana's report.
Key Takeaways
- ChatGPT's Mac app breach was due to a compromised open-source library.
- No user data was compromised, per OpenAI's investigation.
- OpenAI has released a software update and hired cybersecurity experts.
- Regular software updates are crucial for security.
- AI and machine learning are key to modern cybersecurity strategies.
- Implementing multi-factor authentication enhances security.
- Zero Trust Architecture is gaining traction in cybersecurity.
- Conducting regular security audits can prevent future breaches.
Related Articles
- Family Sues OpenAI Over ChatGPT's Alleged Drug Advice [2025]
- Daybreak: OpenAI's Cybersecurity Solution to Anthropic's Claude Mythos
- Navigating the New Cyber Threat Landscape: GenAI's Impact on Cybersecurity Awareness [2025]
- The Trust in Sam Altman: Navigating AI Leadership and Regulation [2025]
- Elon Musk's Influence on OpenAI Leadership Dynamics [2025]
- Mastering the Backwards Calendar with ChatGPT: A Transformative Approach to Weekly Planning [2025]
![Understanding the ChatGPT Desktop App Security Breach for Mac [2025]](https://tryrunable.com/blog/understanding-the-chatgpt-desktop-app-security-breach-for-ma/image-1-1778780064432.jpg)



