Unseen IT Challenges: Avoiding Shadow IT and Boosting Productivity [2025]
Last year, a friend of mine, a CTO at a mid-sized tech company, faced a shocking revelation: over 30% of the company’s software wasn’t sanctioned by their IT department. This unsanctioned software, known as shadow IT, was creating a perfect storm of security risks and productivity losses. But here's the kicker: most of these issues were completely invisible to the IT department until a security audit unearthed them.
TL; DR
- Hidden IT problems can lead to significant productivity loss, with shadow IT being a major factor.
- Digital friction from connectivity and software issues often goes unreported.
- Shadow IT increases security risks and compliance challenges.
- Proactive monitoring and employee training are key to managing hidden IT issues.
- Future trends point to increased reliance on AI for IT management.
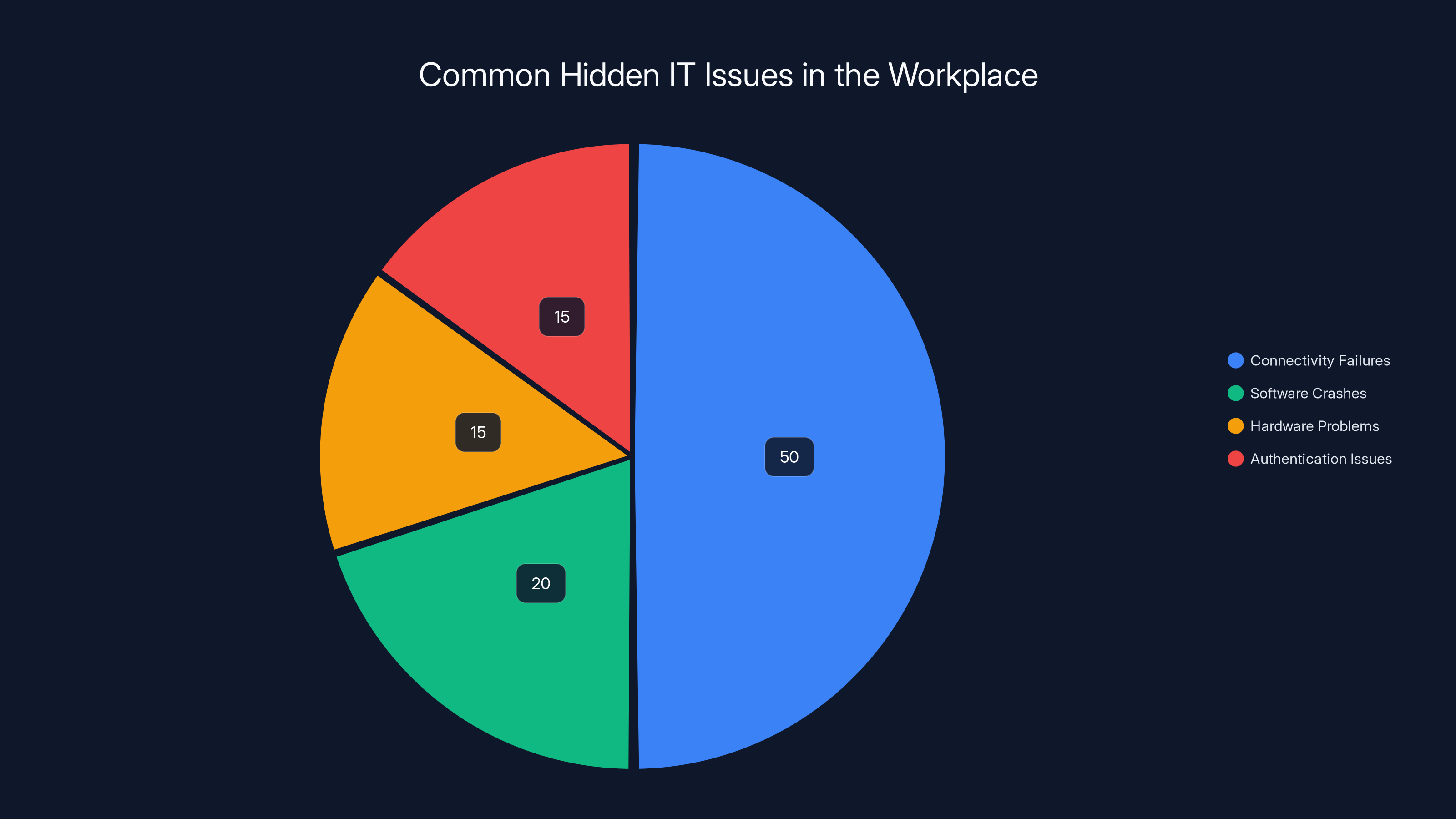
Connectivity failures are the most common hidden IT issue, affecting nearly half of employees. Estimated data based on typical workplace scenarios.
The Invisible Problem: Hidden IT Issues
Hidden IT problems are like the iceberg under the water—what you can't see can definitely hurt you. These issues often manifest as minor annoyances like slow networks, random app crashes, or authentication hiccups. Employees learn to live with them, thinking a quick reboot or workaround will solve the problem.
What Causes These Hidden IT Issues?
Several factors contribute to the rise of hidden IT problems:
- Connectivity Failures: These are the most common, with nearly half of all employees experiencing them regularly.
- Software Crashes: Often dismissed as a fluke, these can indicate deeper compatibility issues.
- Hardware Problems: Outdated hardware can bottleneck performance, yet remain unnoticed.
- Authentication Issues: Frustrating login problems lead to productivity stalls.
Why Do They Go Unreported?
Most employees don't report these issues because they seem too trivial. Reporting can also be perceived as time-consuming or futile if past reports have gone unresolved.

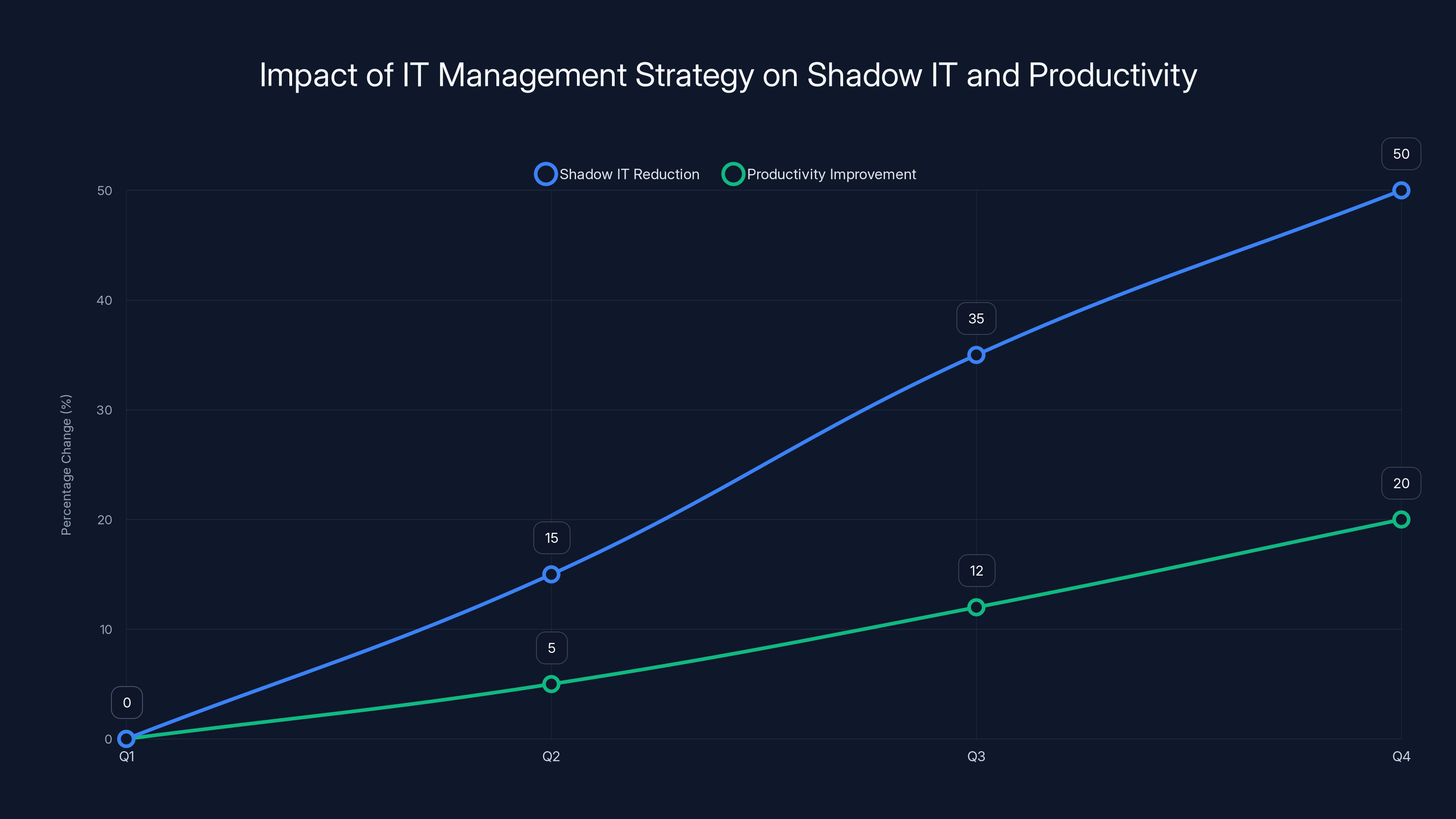
The corporation's strategy led to a 50% reduction in shadow IT and a 20% increase in productivity over one year. Estimated data.
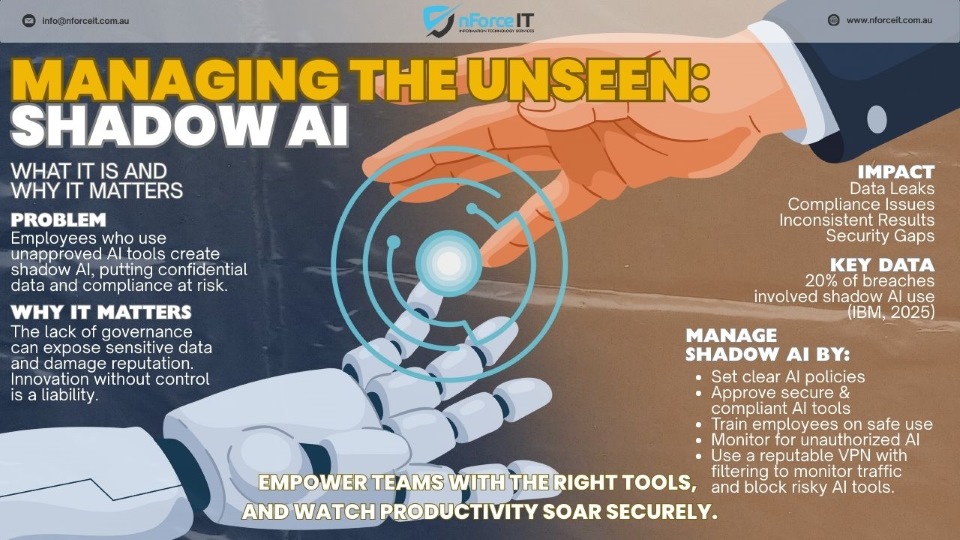
Shadow IT: A Ticking Time Bomb
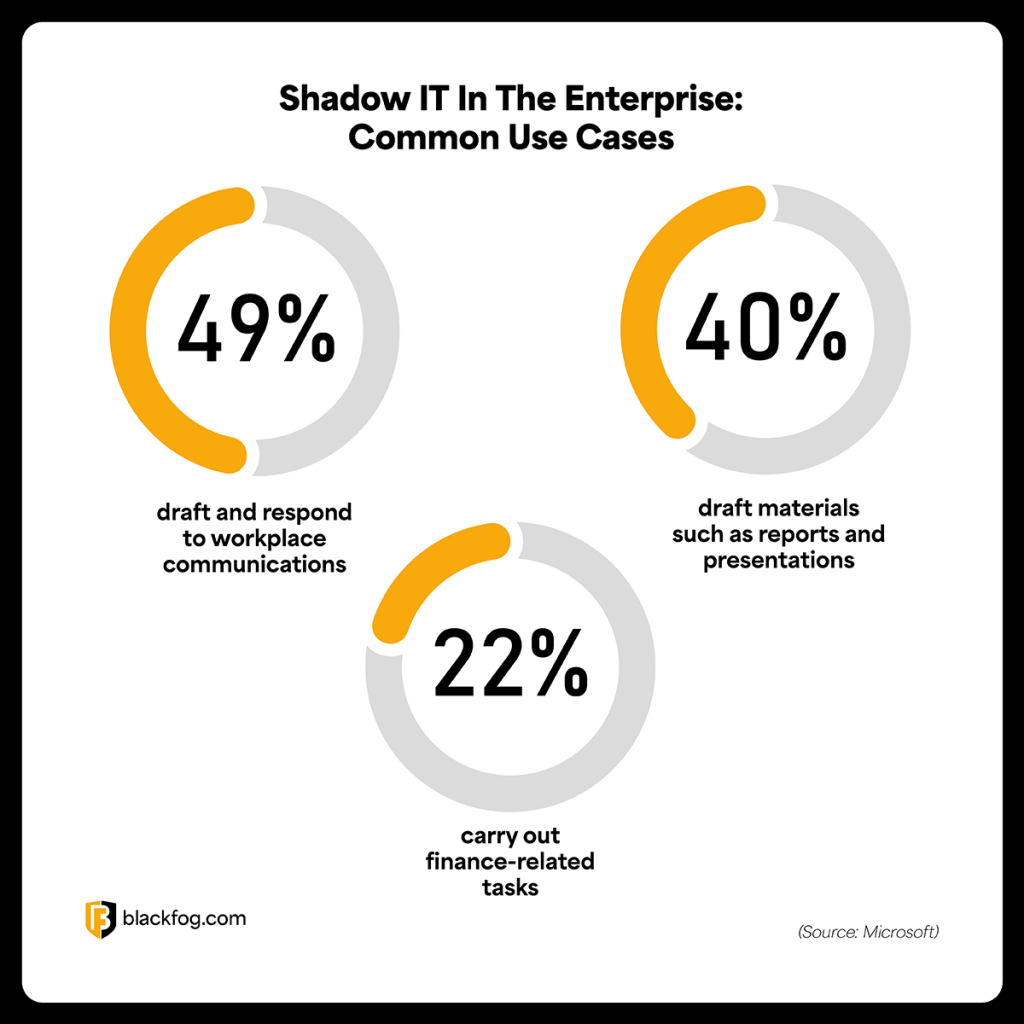
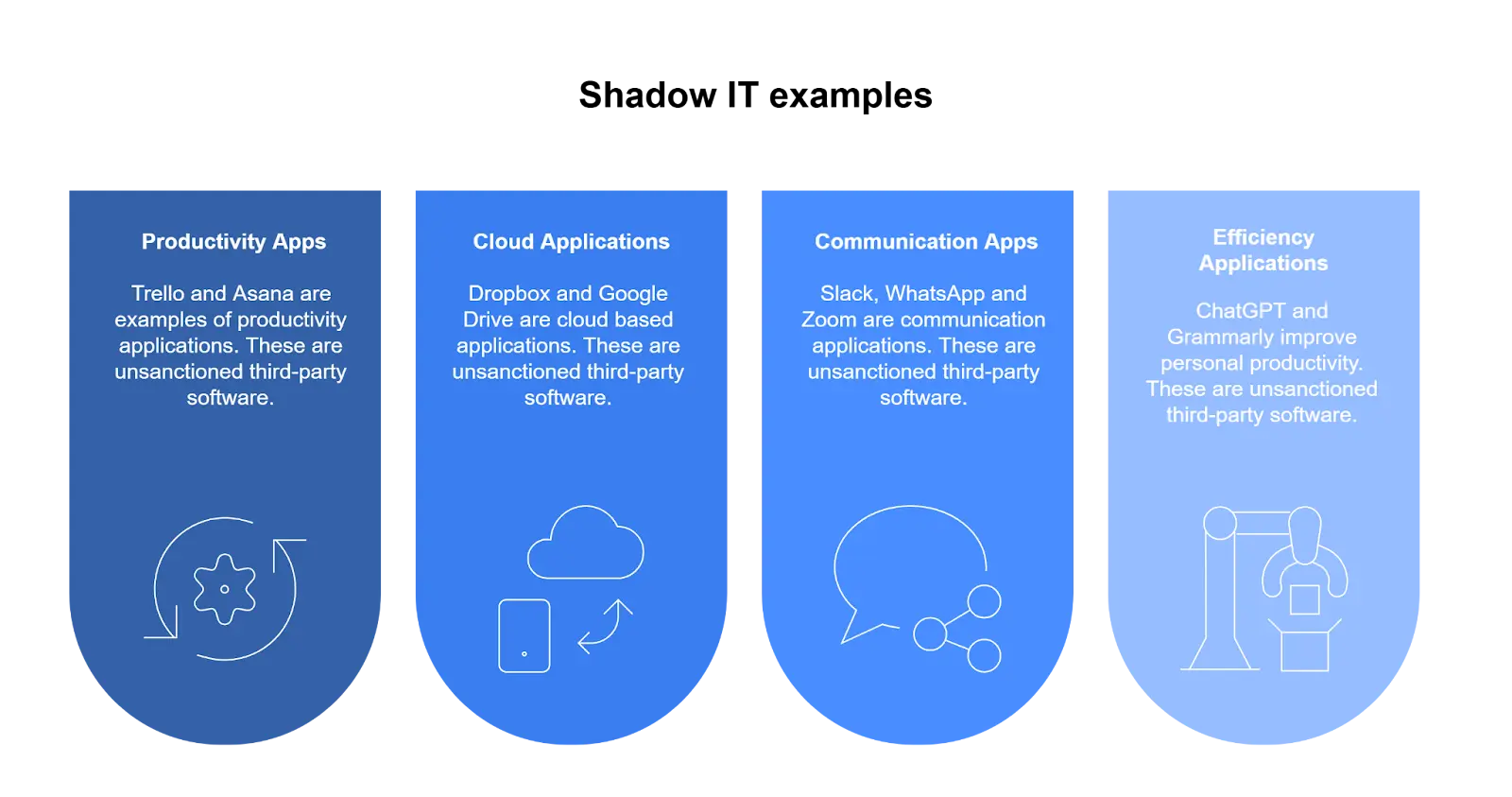
Shadow IT refers to employees using unauthorized software and systems. It’s a practice that often starts innocently—employees just trying to get their work done more efficiently—but can lead to significant security and compliance risks.
The Risks of Shadow IT
- Security Vulnerabilities: Unsanctioned apps can open the door to data breaches.
- Compliance Issues: Regulatory compliance becomes impossible if IT can't control or even know about all software in use.
- Data Loss: Without proper backup and recovery, data in shadow systems can be lost permanently.
Addressing Shadow IT
To combat shadow IT, organizations need to:
- Conduct Regular Audits: Identify all software in use across the organization.
- Implement Strict Software Policies: Clearly define acceptable software usage.
- Educate Employees: Make sure they understand the risks and policies related to shadow IT.
Lost Productivity: The Silent Killer
Lost productivity due to hidden IT problems is a silent killer in many organizations. A study by McKinsey found that knowledge workers spend 28% of their workweek managing emails and 20% looking for internal information or tracking down colleagues—tasks that could be streamlined with better IT solutions.
Causes of Lost Productivity
- Ineffective Communication Tools: Outdated or poorly integrated communication tools can slow down collaboration.
- Inefficient Workflow Processes: Processes that aren’t automated lead to wasted time.
- Fragmented Systems: Systems that don’t talk to each other create silos and slow down productivity.
Solutions for Improving Productivity
- Adopt Integrated Tools: Use platforms that combine communication, collaboration, and project management.
- Automate Repetitive Tasks: Utilize AI and machine learning to automate mundane tasks.
- Enhance IT Support: Ensure IT support is proactive, not reactive.
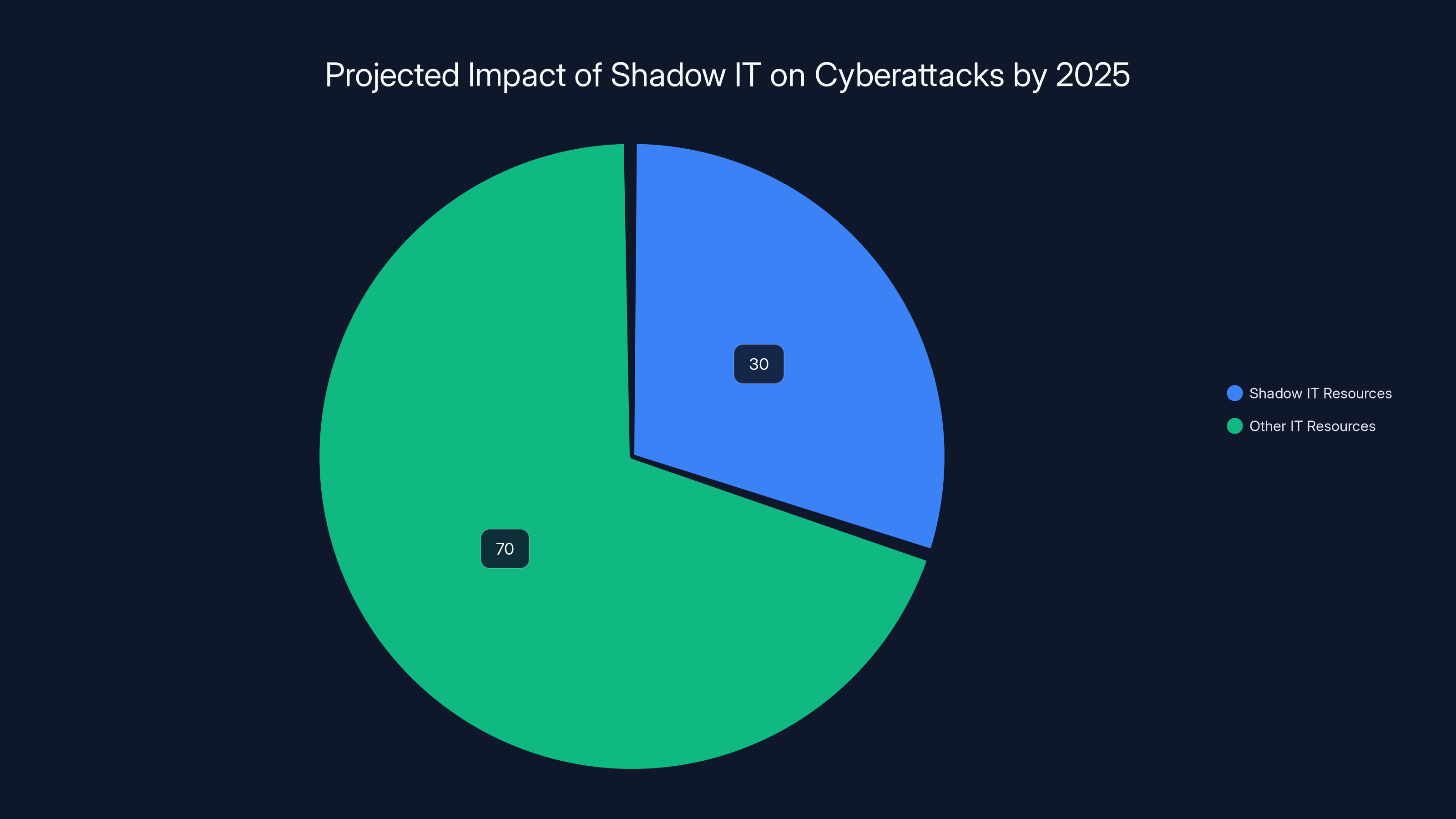
By 2025, it's estimated that 30% of successful cyberattacks will target shadow IT resources, highlighting the critical need for organizations to manage unauthorized software usage. (Estimated data)
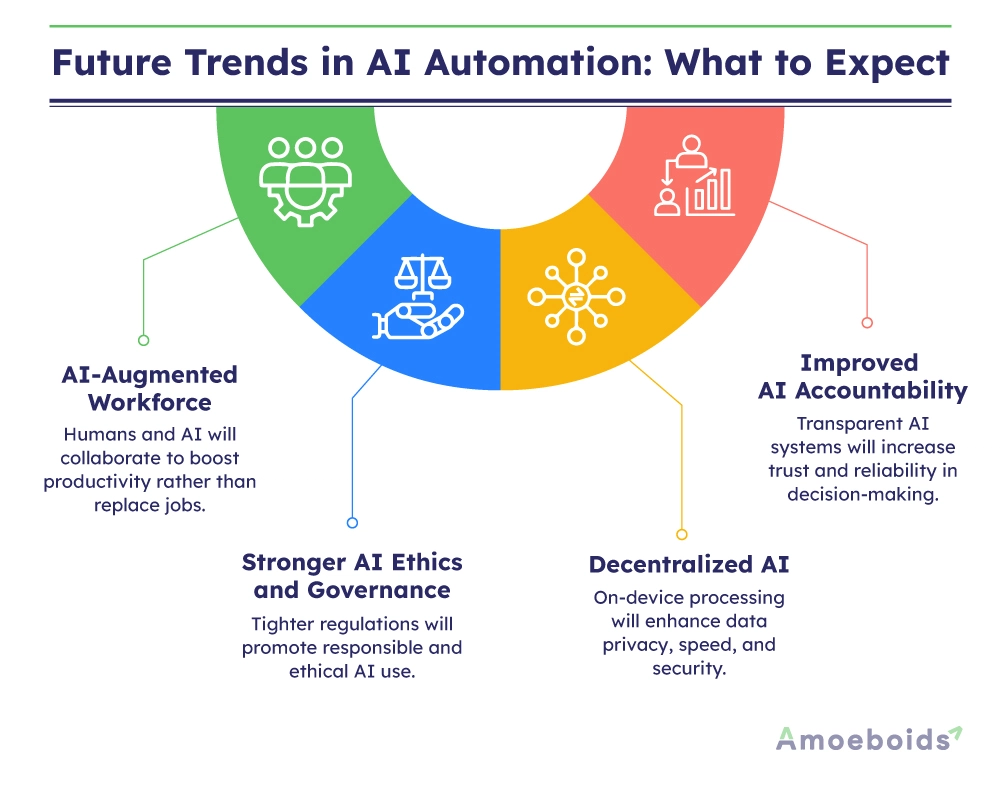
Future Trends in IT Management
The future of IT management is intertwined with AI and automation. As systems become more complex, the ability to manage them efficiently will rely heavily on these technologies.
AI and Machine Learning
AI and machine learning are already transforming IT support. Predictive analytics can anticipate potential issues before they become problems, allowing IT to act preemptively.
Increased Automation
Automation will be key in managing both shadow IT and recognized IT assets. Tools like Runable offer AI-powered platforms for creating presentations, documents, reports, images, videos, and slides, enabling teams to streamline content creation and workflow automation.
The Role of Cloud Computing
Cloud computing continues to grow, offering scalable and flexible solutions that can reduce the need for shadow IT. Organizations can leverage cloud platforms to provide employees with the tools they need legally and securely.
Common Pitfalls and How to Avoid Them
While implementing IT solutions to address hidden problems, organizations often fall into common traps.
Overlooking User Training
Without proper training, new tools can become just another layer of complexity.
- Solution: Invest in comprehensive training programs that ensure all employees are comfortable with new technologies.
Ignoring Employee Feedback
IT departments often ignore valuable insights that employees can provide.
- Solution: Create a feedback loop where employees can easily share their experiences and suggestions.
Failing to Update Policies
Outdated IT policies can lead to increased shadow IT and security risks.
- Solution: Regularly review and update IT policies to reflect current technologies and threats.
Case Study: A Real-World Example
Consider a multinational corporation that realized shadow IT was costing them millions annually in inefficiencies and data breaches. By implementing a robust IT management strategy focused on transparency, education, and proactive monitoring, they reduced shadow IT by 50% in one year and improved productivity by 20%.
Best Practices for IT Management
Adopting best practices in IT management can significantly reduce the risks associated with hidden IT problems.
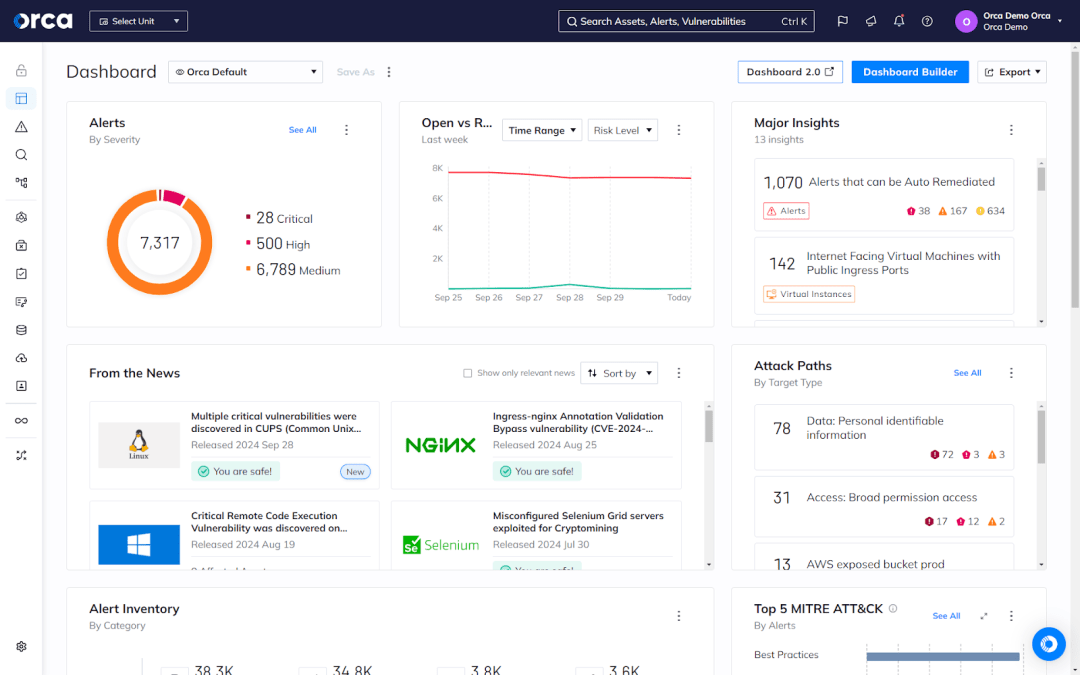
Proactive Monitoring
Use advanced monitoring tools to track all network activities in real-time, identifying potential issues before they escalate.
Employee Engagement
Engage employees in the IT management process by involving them in decision-making and providing clear communication channels.
Regular Training
Continuous training ensures that employees are aware of the latest technologies and security protocols.
Policy Enforcement
Strictly enforce IT policies to prevent unauthorized software installations and data breaches.
The Road Ahead: Future Recommendations
Looking forward, organizations should prepare for an evolving IT landscape that includes greater reliance on AI, increased automation, and enhanced security protocols.
Embrace AI and Machine Learning
These technologies offer predictive insights that can transform IT management, making it more efficient and effective.
Focus on Security
With the rise of remote work, security must remain a top priority. Implementing robust security measures will protect against both external and internal threats.
Invest in Scalable Solutions
Scalable solutions ensure that IT can keep pace with the growing demands of the organization without resorting to shadow IT.
Conclusion
Hidden IT problems are a significant risk to productivity and security, but they can be managed effectively through proactive strategies, employee engagement, and the adoption of AI and automation technologies. By addressing these issues head-on, organizations can reduce shadow IT, improve security, and enhance overall productivity.
Use Case: Automate your weekly reports with AI to save time and reduce the reliance on unsanctioned software.
Try Runable For Free
Key Takeaways
- Hidden IT issues lead to significant productivity loss and security risks.
- Shadow IT is a major factor in creating security vulnerabilities and compliance challenges.
- Proactive monitoring and employee training are crucial in managing IT problems.
- AI and machine learning are transforming IT management by offering predictive insights.
- Cloud computing offers scalable solutions to reduce the reliance on shadow IT.
- Implementing best practices in IT management can significantly reduce risks.
- Engaging employees in IT decision-making enhances overall IT strategy effectiveness.
Related Articles
- The Rise of AI Content Outsourcing: Christian Creators Turn to Fiverr [2025]
- Revolutionizing the Genetic Code: Reducing to 19 Amino Acids [2025]
- Flying Drumsticks: South Korea's Ambitious Drone and Robot Delivery System [2025]
- The Unprecedented Growth of AWS and the Future of AI in Cloud Computing [2025]
- Why One Outage Can Still Take Down Half the Internet [2025]
- 2025 Guide: The Ultimate Fruit Fly Gadget & Alternatives
FAQ
What is Unseen IT Challenges: Avoiding Shadow IT and Boosting Productivity [2025]?
Last year, a friend of mine, a CTO at a mid-sized tech company, faced a shocking revelation: over 30% of the company’s software wasn’t sanctioned by their IT department
What does tl; dr mean?
This unsanctioned software, known as shadow IT, was creating a perfect storm of security risks and productivity losses
Why is Unseen IT Challenges: Avoiding Shadow IT and Boosting Productivity [2025] important in 2025?
But here's the kicker: most of these issues were completely invisible to the IT department until a security audit unearthed them
How can I get started with Unseen IT Challenges: Avoiding Shadow IT and Boosting Productivity [2025]?
- Hidden IT problems can lead to significant productivity loss, with shadow IT being a major factor
What are the key benefits of Unseen IT Challenges: Avoiding Shadow IT and Boosting Productivity [2025]?
- Digital friction from connectivity and software issues often goes unreported
What challenges should I expect?
- Shadow IT increases security risks and compliance challenges
![Unseen IT Challenges: Avoiding Shadow IT and Boosting Productivity [2025]](https://tryrunable.com/blog/unseen-it-challenges-avoiding-shadow-it-and-boosting-product/image-1-1777642719120.jpg)




