WordPress Vulnerability: How Hackers Exploit Simple Plugin Flaws [2025]
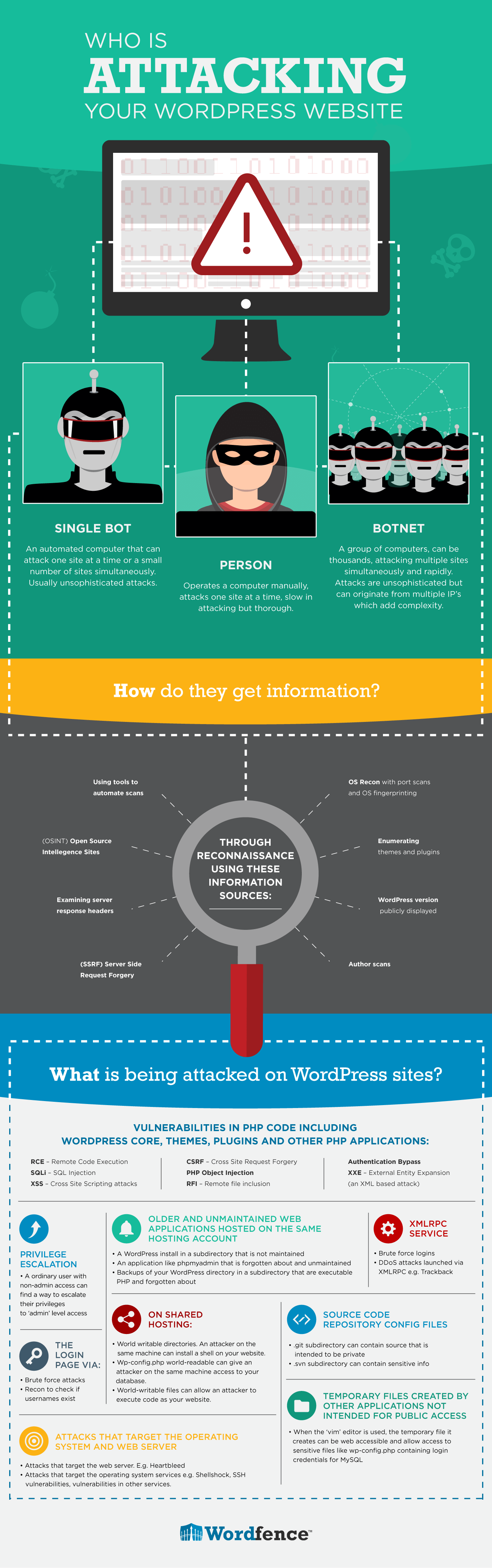
WordPress powers over a third of all websites on the internet, making it a prime target for cybercriminals. Recently, a vulnerability in a popular WordPress plugin exposed thousands of sites to potential takeover, allowing attackers to gain admin access without needing login credentials. This article delves into how such vulnerabilities occur, explores the technical details behind the threat, and provides actionable steps to protect your site.
TL; DR
- Admin Access Exploit: A flaw in a WordPress plugin allowed hackers to create admin accounts without needing credentials, as reported by SecurityWeek.
- Technical Root Cause: Attackers exploited exposed AJAX endpoints and nonce values to bypass authentication, according to GBHackers.
- Mitigation Strategies: Regular plugin updates and robust security practices can prevent such vulnerabilities.
- Future Trends: As WordPress evolves, security measures must adapt to counter increasingly sophisticated threats.
- Bottom Line: Vigilance and proactive security measures are essential to protect WordPress sites from exploitation.

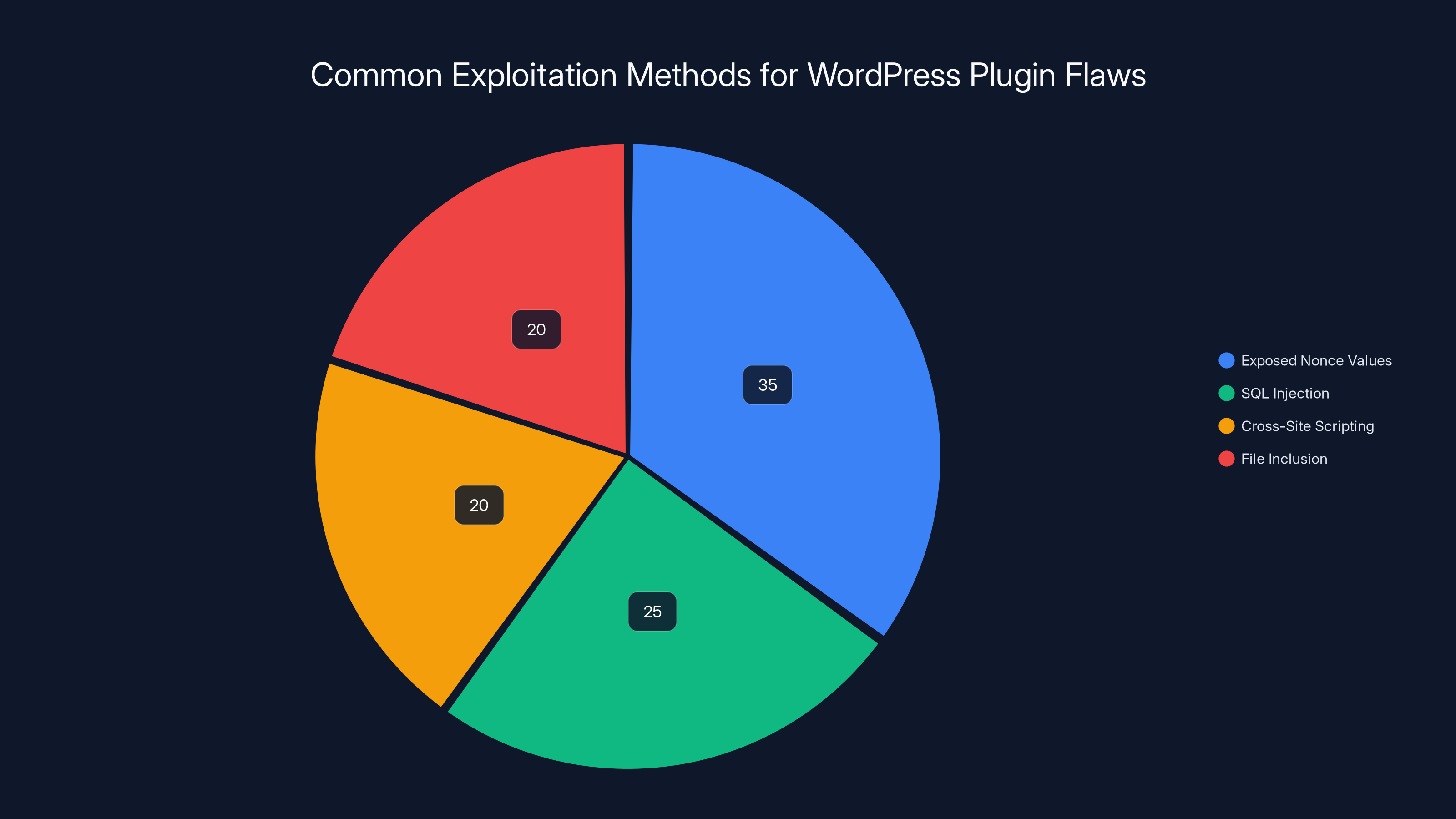
Exposed nonce values account for 35% of exploitation methods in WordPress plugins, highlighting the need for secure token handling. Estimated data.
Introduction
In today's digital landscape, website security is paramount. WordPress, being the most popular content management system, attracts both users and attackers. A recent vulnerability in a widely used plugin highlighted the risks posed by seemingly minor security flaws. This vulnerability enabled attackers to gain administrative control over websites, demonstrating the critical need for robust security measures, as detailed by The Next Web.
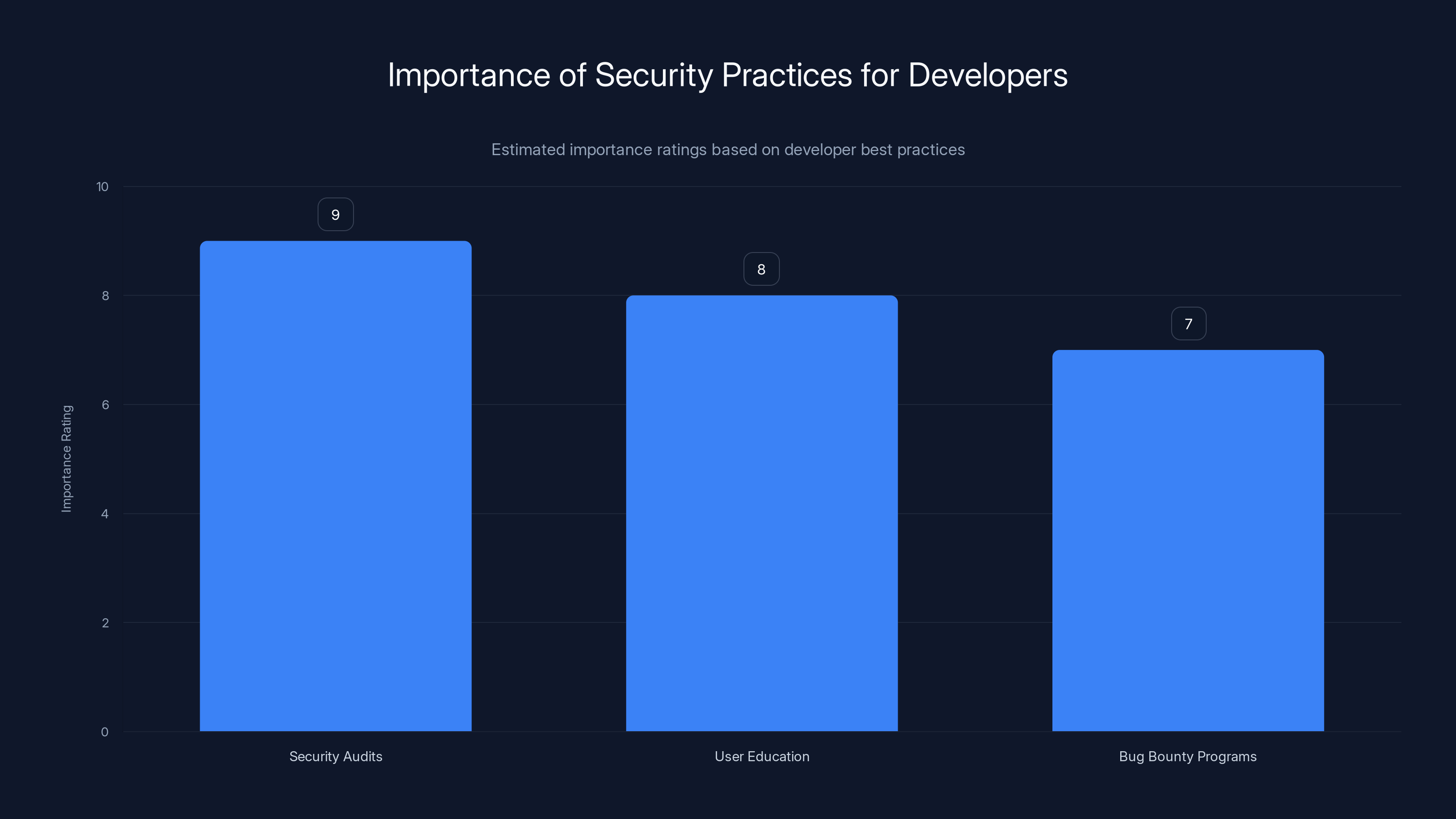
Security audits are rated as the most critical practice for developers, followed by user education and participation in bug bounty programs. Estimated data.
How Hackers Exploit WordPress Plugin Flaws
Understanding the Vulnerability
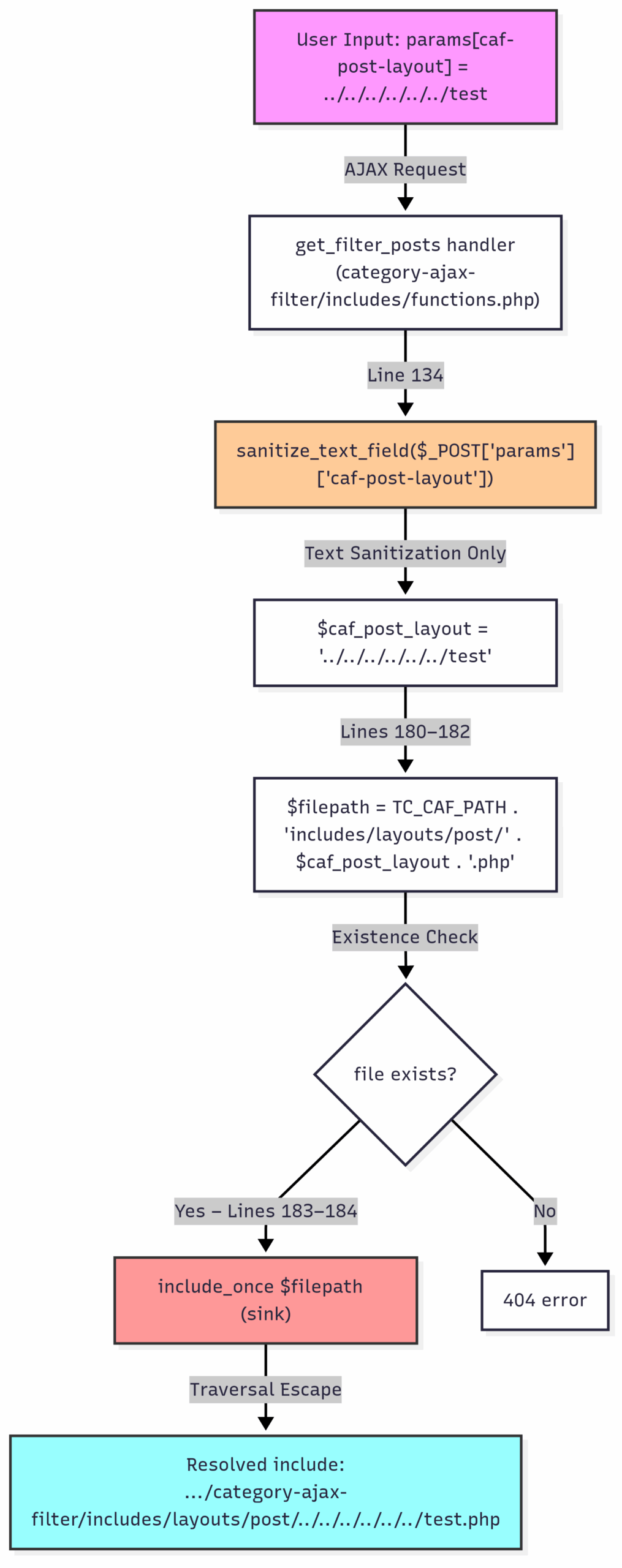
The vulnerability in question stemmed from a flaw in the plugin's handling of AJAX requests. AJAX, or Asynchronous JavaScript and XML, allows web applications to send and retrieve data from a server asynchronously. In this case, the plugin's AJAX endpoint was not properly secured, allowing attackers to bypass authentication mechanisms, as noted by eSecurity Planet.
Exposed Nonce Values: Nonces are unique tokens used in WordPress to validate requests and prevent cross-site request forgery (CSRF) attacks. Unfortunately, the plugin exposed nonce values, enabling attackers to forge requests and escalate privileges.
The Attack Vector
- Identifying the Vulnerability: Attackers scanned websites using the vulnerable plugin to identify exploitable endpoints.
- Crafting Malicious Requests: Using exposed nonce values, attackers crafted requests that appeared legitimate to the server.
- Bypassing Authentication: The server processed these requests, allowing attackers to create new admin accounts without credentials.
Real-World Example
Consider a popular e-commerce site using the vulnerable plugin. An attacker could exploit the flaw to create an admin account, gaining access to sensitive customer data and the ability to alter the site's content or redirect users to malicious sites.

Best Practices for Securing WordPress Sites
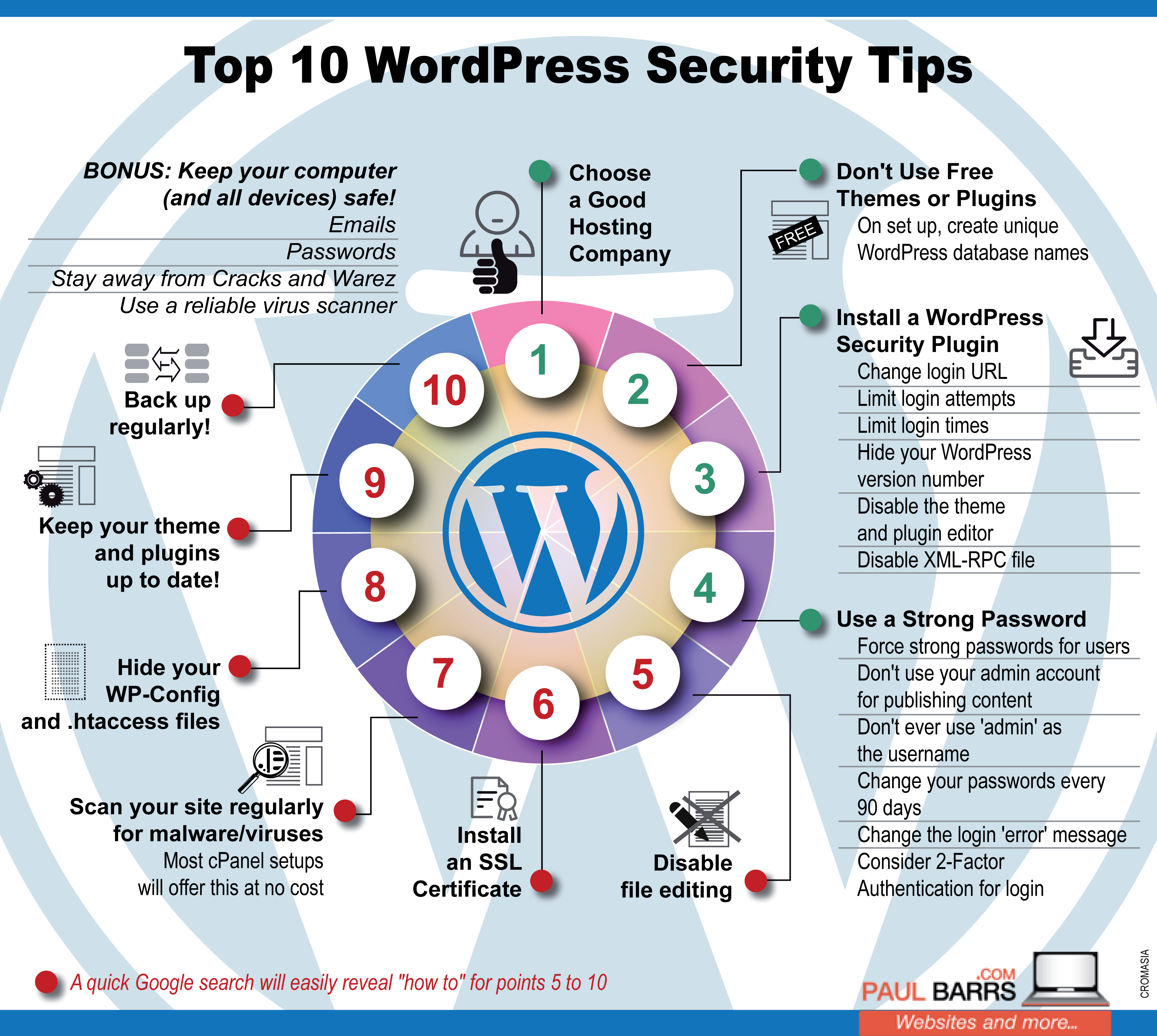
Regular Updates
One of the simplest yet most effective security measures is to keep WordPress core, themes, and plugins updated. Developers frequently release updates to patch known vulnerabilities, as emphasized by TechRadar.
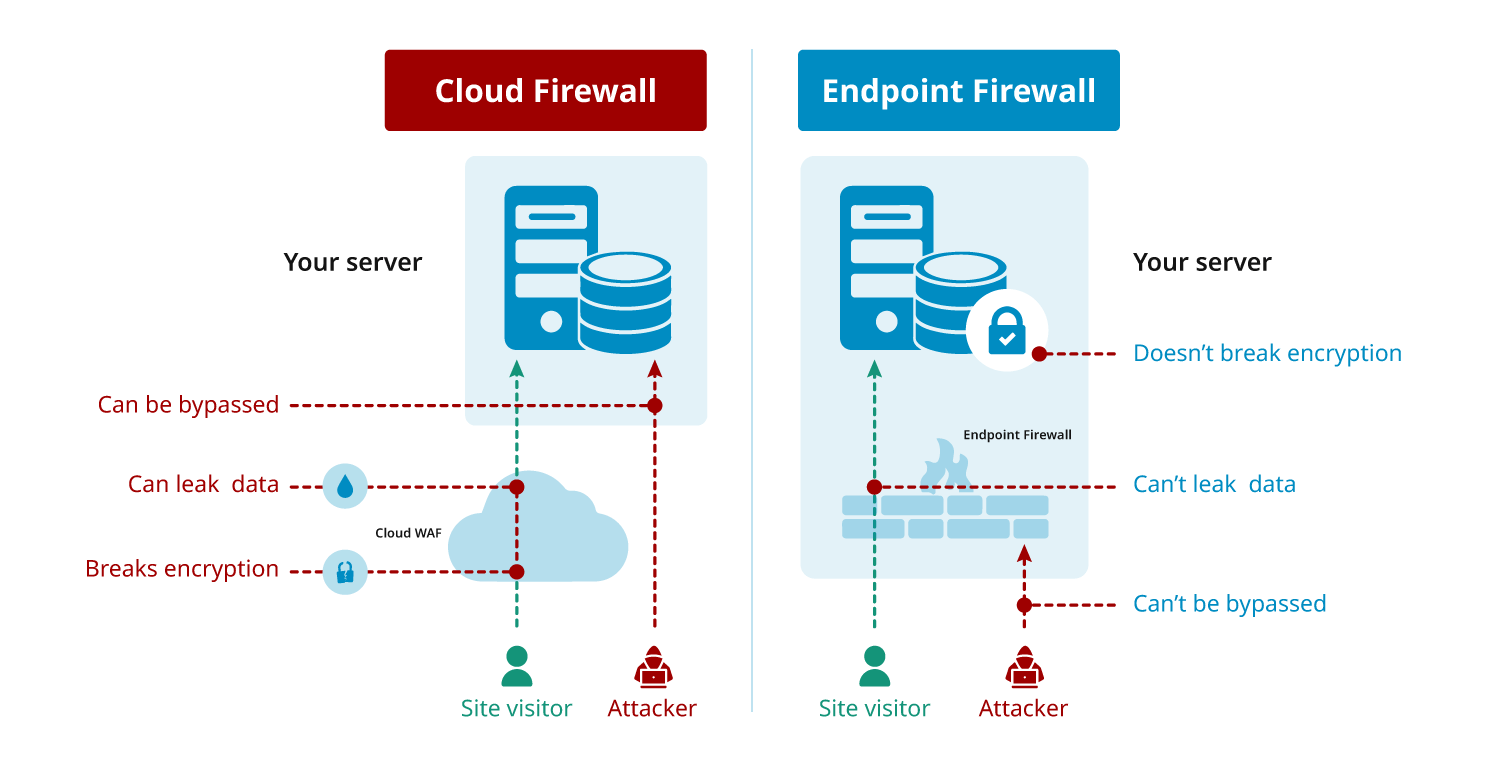
Implementing Security Plugins
Security plugins like Sucuri and Wordfence offer features like firewall protection, malware scanning, and login attempt monitoring.
Strong Password Policies
Ensure all users adhere to strong password policies. Use a password manager to generate and store complex passwords securely.
Regular Backups
Implement a regular backup strategy to ensure you can quickly restore your site in case of a breach. Tools like Updraft Plus make this process straightforward.
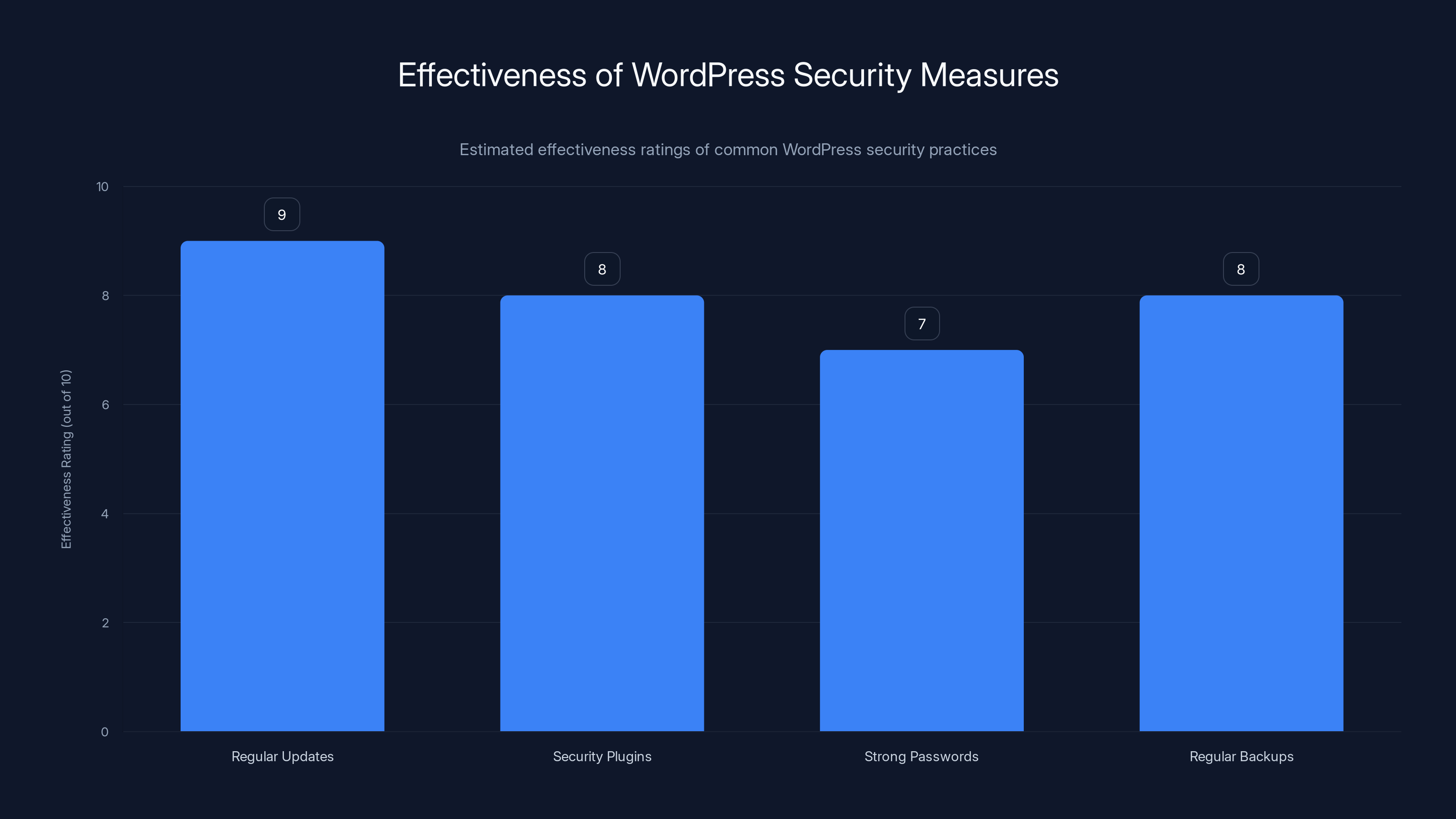
Regular updates and security plugins are among the most effective measures for securing WordPress sites. Estimated data based on typical security assessments.
Implementing Technical Security Measures
Securing AJAX Endpoints
Developers should ensure that AJAX endpoints are accessible only to authorized users by implementing proper authentication checks.
Using Nonces Correctly
Nonces should be unique, time-sensitive, and validated on the server side to prevent unauthorized access.
File Permissions and User Roles
Set strict file permissions on your server and assign user roles carefully to minimize the risk of unauthorized access.
Common Pitfalls and Solutions
Overlooking Plugin Security
Many site owners install plugins without considering their security implications. Always vet plugins before installation and monitor them for updates.
Ignoring Security Alerts
Security alerts from plugins or hosting providers should never be ignored. Address them promptly to mitigate potential risks.
Overreliance on Automated Tools
While security plugins and automated tools are beneficial, they should not replace manual security audits and best practices.
Future Trends in WordPress Security
AI-Powered Security Solutions
As cyber threats become more sophisticated, AI and machine learning will play a critical role in detecting and mitigating attacks in real-time.
Enhanced Authentication Mechanisms
The adoption of two-factor authentication (2FA) and biometric logins will become more widespread to secure user accounts.
Greater Collaboration Between Developers
Plugin developers and security experts will need to collaborate more closely to identify and patch vulnerabilities swiftly.
Recommendations for Developers
Conduct Regular Security Audits
Regularly audit your plugins for potential vulnerabilities and ensure compliance with security best practices.
Educate Users
Provide users with guidance on maintaining a secure WordPress environment, emphasizing the importance of updates and strong passwords.
Participate in Bug Bounty Programs
Consider participating in bug bounty programs to incentivize security researchers to identify and report vulnerabilities in your code.

Conclusion
The recent WordPress plugin vulnerability serves as a stark reminder of the importance of web security. By understanding how these vulnerabilities occur and implementing robust security measures, site owners can protect their websites from exploitation. As the WordPress ecosystem evolves, staying informed and proactive will be key to maintaining a secure online presence.
FAQ
What is a WordPress plugin vulnerability?
A WordPress plugin vulnerability is a security flaw within a plugin that can be exploited by attackers to gain unauthorized access or perform malicious actions on a website.
How do hackers exploit WordPress plugin vulnerabilities?
Hackers exploit these vulnerabilities by identifying insecure endpoints, crafting malicious requests, and bypassing authentication mechanisms to gain access or escalate privileges.
What are the best practices for securing WordPress sites?
Best practices include keeping software updated, using security plugins, implementing strong password policies, and conducting regular backups.
How can developers prevent plugin vulnerabilities?
Developers can prevent plugin vulnerabilities by conducting regular security audits, using nonces correctly, and ensuring proper authentication checks for AJAX endpoints.
What is the role of AI in WordPress security?
AI plays a role in detecting and mitigating cyber threats in real-time, offering advanced protection against sophisticated attacks.
How important are backups for WordPress sites?
Backups are crucial as they allow site owners to quickly restore their websites in case of a breach or data loss.
What is two-factor authentication (2FA)?
Two-factor authentication (2FA) is an additional security layer that requires users to provide two forms of identification before accessing an account.
How often should WordPress sites be updated?
WordPress sites should be updated as soon as new versions of the core software, themes, or plugins are released to patch vulnerabilities.
What are nonce values in WordPress?
Nonce values in WordPress are unique tokens used to verify requests and prevent CSRF attacks by ensuring that requests are legitimate and not forged.
Why is collaboration important in WordPress security?
Collaboration between developers and security experts is important to quickly identify and patch vulnerabilities, ensuring a safer web ecosystem.
Key Takeaways
- A vulnerability allowed hackers to gain admin access using exposed AJAX endpoints and nonce values.
- Regular updates and strong security measures are vital for WordPress site protection.
- AI and machine learning are becoming integral to real-time threat detection and mitigation.
- Developers should conduct security audits and collaborate to address vulnerabilities promptly.
- Two-factor authentication and regular backups are critical components of a robust security strategy.
Related Articles
- How to Protect Your macOS from North Korean Cyber Threats [2025]
- How FIFA World Cup Partners Could Be Exposing Fans to Email Attacks: An In-Depth Analysis [2025]
- France's Move to Linux: A Bold Shift from Windows 11 and What It Means for Microsoft's Future [2025]
- It Takes 2 Minutes to Hack the EU’s New Age-Verification App | WIRED
- The 7 Biggest Tech Stories of the Week: From Cutting-Edge Cameras to the 'Most Beautiful Phone of 2026' [2025]
- How to Watch the World Snooker Championship 2026 Live Streams for Free [2026]
![WordPress Vulnerability: How Hackers Exploit Simple Plugin Flaws [2025]](https://tryrunable.com/blog/wordpress-vulnerability-how-hackers-exploit-simple-plugin-fl/image-1-1776530100485.jpg)



