Anthropic's Mythos: A Cybersecurity Turning Point [2025]
Last month, the tech world buzzed with news of Anthropic's latest AI model, Claude Mythos. Its unveiling has sparked debate about its potential impact on cybersecurity. Is it just another AI milestone or a true game-changer in digital defense strategies?
TL; DR
- Claude Mythos's Capabilities: Discover vulnerabilities across diverse platforms with autonomous exploit development.
- Consortium Collaborations: Project Glasswing includes tech giants like Microsoft and Google for controlled release.
- Impact on Cybersecurity: Forces a shift from reactive to proactive defense strategies.
- Industry Implications: Potential to reshape security protocols across sectors.
- Future Trends: Emphasizes the need for AI-based cybersecurity measures.

Data privacy concerns have the highest impact on cybersecurity effectiveness, followed by overreliance on AI. (Estimated data)
The Mythos Model: A New Frontier
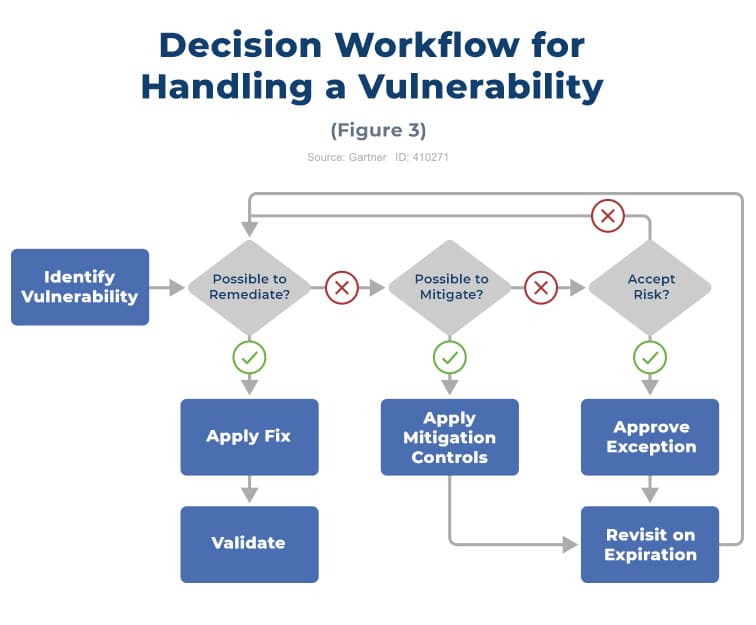
The Claude Mythos Preview model represents a significant leap in AI capabilities. Designed to autonomously identify and exploit software vulnerabilities, it sets a new standard in cybersecurity threats. But what makes Mythos truly unique?
What Sets Mythos Apart?
Unlike traditional models, Mythos operates with a high degree of autonomy, capable of discovering vulnerabilities in operating systems, browsers, and myriad software products. Its potential to develop working exploits autonomously presents both opportunities and challenges.
Key Features:
- Autonomous Vulnerability Discovery: Identifies security gaps without human intervention.
- Exploit Development: Creates functional exploits for identified vulnerabilities.
- Cross-Platform Compatibility: Works across different operating systems and software environments.
Real-World Use Case
Consider a multinational corporation operating on diverse platforms. Mythos can scan its entire digital infrastructure, identify security weaknesses, and propose fixes or exploit them for testing—helping the company bolster its defenses proactively.
The Controlled Release: Project Glasswing
To mitigate potential risks, Anthropic has limited the release of Mythos to a select group of organizations through Project Glasswing. This consortium includes tech leaders like Microsoft, Apple, and Google, who collaborate to explore the model's capabilities responsibly.
Why Limited Release?
- Risk Mitigation: Prevent misuse by hackers and malicious actors.
- Collaborative Exploration: Gather insights from tech leaders to enhance cybersecurity strategies.
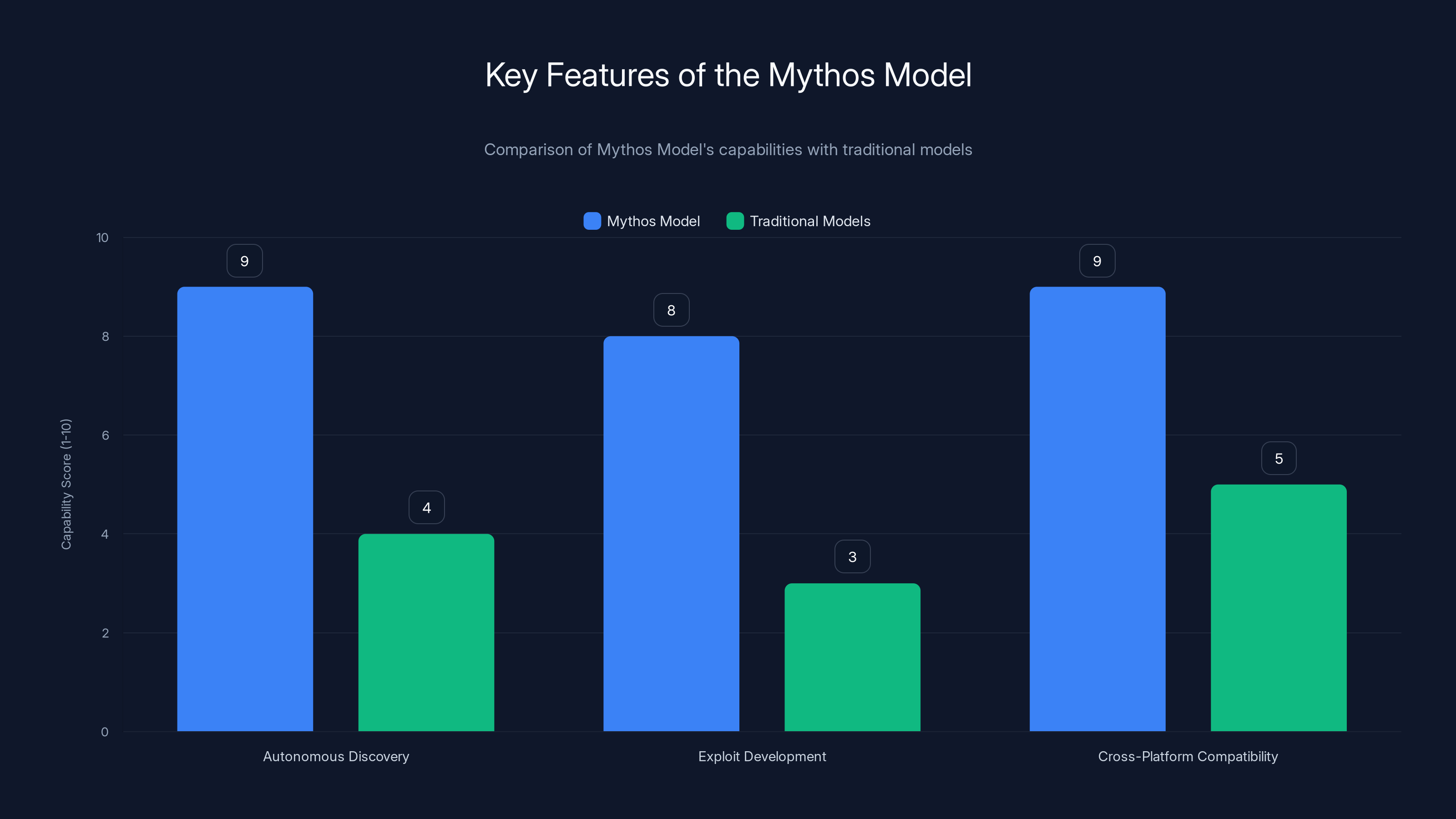
The Mythos Model significantly outperforms traditional models in key areas such as autonomous discovery and cross-platform compatibility. Estimated data based on feature descriptions.
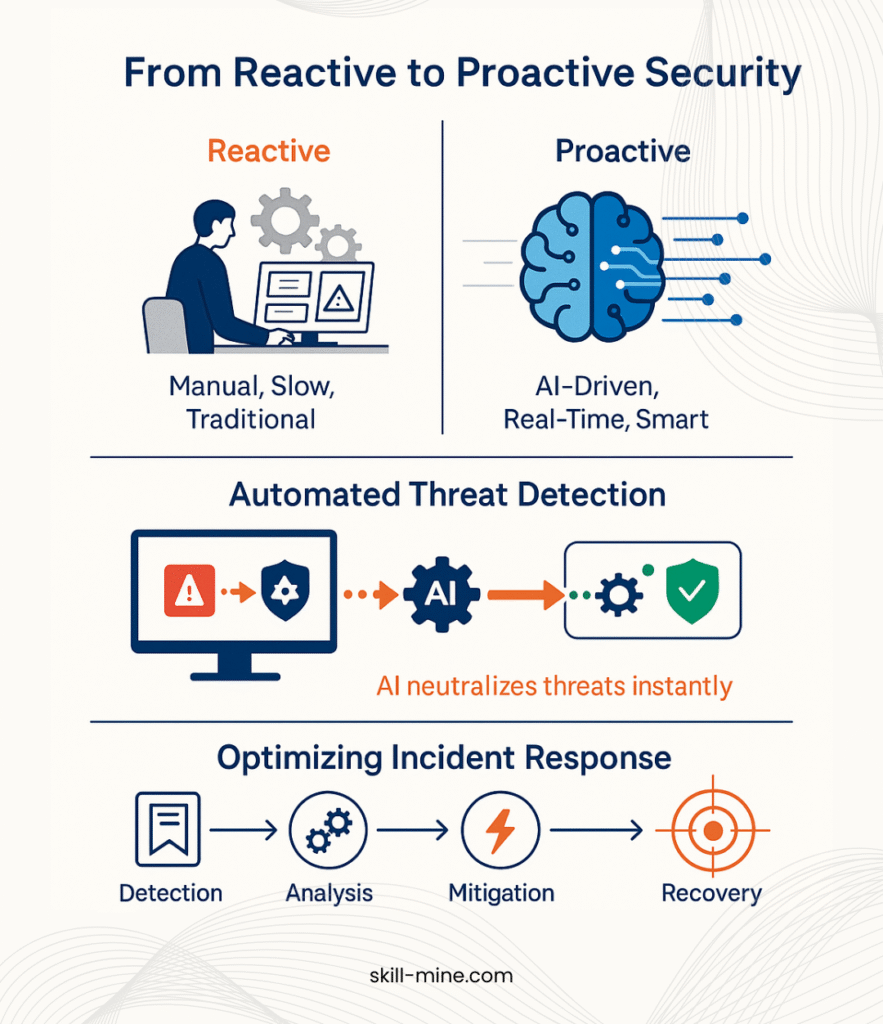
The Cybersecurity Paradigm Shift
Mythos forces a reevaluation of existing cybersecurity paradigms. Traditional defense mechanisms, largely reactive, are now contrasted with the proactive capabilities of AI like Mythos.
From Reactive to Proactive Defense
Historically, cybersecurity has been about patching vulnerabilities after they're discovered. Mythos challenges this by enabling organizations to anticipate and address potential threats before they can be exploited.
Benefits of Proactive Defense:
- Reduced Response Time: Quickly address vulnerabilities before attacks occur.
- Enhanced Threat Intelligence: Gain deeper insights into potential security breaches.
- Improved Resource Allocation: Focus efforts on preventing attacks rather than reacting.
Implementation Guide
For organizations looking to integrate AI-based security measures like Mythos, the process involves several steps:
- Assess Current Security Posture: Evaluate existing defenses to identify gaps.
- Develop AI Strategy: Determine how AI can address identified vulnerabilities.
- Collaborate with Experts: Engage cybersecurity professionals to guide AI integration.
- Continuous Monitoring: Implement ongoing surveillance to maintain robust security.
Common Pitfalls and Solutions
While Mythos offers unprecedented potential, there are challenges to consider:
Potential Pitfalls
- Overreliance on AI: Dependence on AI might lead to complacency in human oversight.
- Data Privacy Concerns: Autonomous systems handling sensitive data raise privacy issues.
- Resource Constraints: Implementing AI-driven solutions can be costly and resource-intensive.
Solutions:
- Balanced Approach: Combine AI capabilities with human expertise to maintain vigilance.
- Privacy Protocols: Establish strict data handling and usage policies.
- Cost-Benefit Analysis: Evaluate the long-term ROI of AI implementation to justify initial investments.
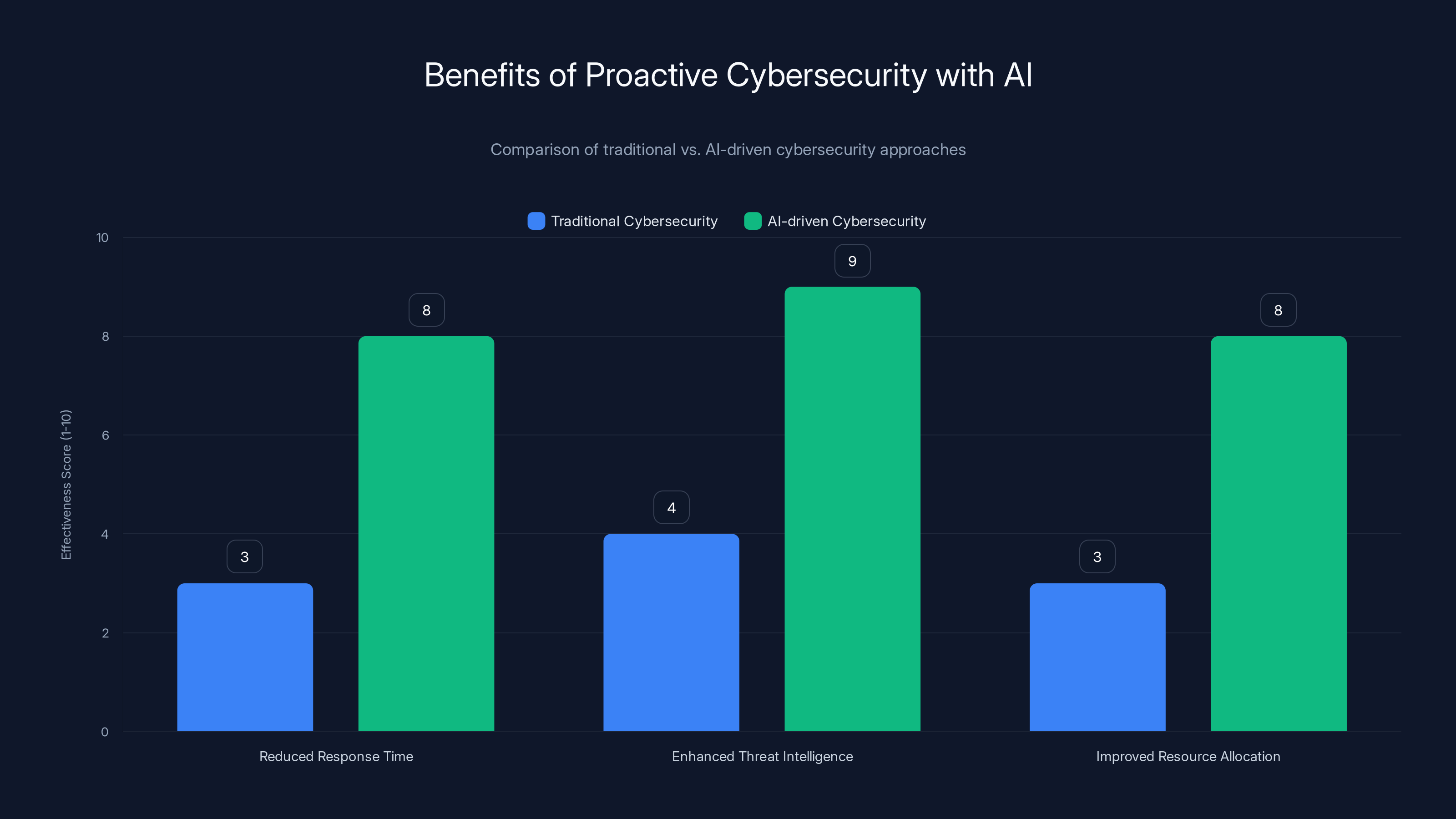
AI-driven cybersecurity approaches like Mythos significantly enhance threat intelligence, reduce response times, and improve resource allocation compared to traditional methods. (Estimated data)
Future Trends and Recommendations
Looking ahead, the integration of AI like Mythos into cybersecurity strategies will become increasingly essential.
Future Trends
- AI-Augmented Security Teams: Human-AI collaboration will enhance threat detection and management.
- Increased Regulatory Scrutiny: Governments may impose stricter regulations on AI use in cybersecurity.
- Focus on Ethical AI: Developing ethical guidelines for AI deployment will be crucial.
Recommendations
- Invest in AI Training: Equip cybersecurity teams with AI knowledge and skills.
- Foster Cross-Industry Collaboration: Engage with other sectors to share insights and best practices.
- Prioritize Ethical Standards: Ensure AI deployment aligns with ethical norms and regulations.

Conclusion
Anthropic's Mythos model marks a pivotal moment in the evolution of cybersecurity. By shifting from reactive to proactive defense, it challenges traditional strategies and sets a new course for the future. As organizations navigate this transition, balancing AI capabilities with human oversight will be key to maintaining robust security measures.
FAQ
What is Anthropic's Mythos?
Anthropic's Mythos is an advanced AI model designed to autonomously identify and exploit software vulnerabilities, representing a significant advancement in cybersecurity capabilities.
How does Mythos impact cybersecurity?
Mythos shifts cybersecurity from reactive to proactive defense, enabling organizations to anticipate and address potential threats before they can be exploited.
What are the benefits of proactive defense?
Proactive defense reduces response time, enhances threat intelligence, and improves resource allocation, allowing organizations to prevent attacks rather than merely reacting.
How can organizations implement AI-based security measures?
Organizations can implement AI-based security by assessing their current security posture, developing an AI strategy, collaborating with experts, and maintaining continuous monitoring.
What are the potential pitfalls of relying on AI for cybersecurity?
Potential pitfalls include overreliance on AI, data privacy concerns, and resource constraints. Balancing AI with human expertise and establishing strict privacy protocols can mitigate these risks.
What future trends can we expect in AI and cybersecurity?
Future trends include AI-augmented security teams, increased regulatory scrutiny, and a focus on ethical AI deployment.
Key Takeaways
- Claude Mythos's capabilities redefine cybersecurity by enabling autonomous vulnerability discovery and exploit development.
- Project Glasswing's limited release aims to mitigate risks and gather insights from tech leaders.
- Shifting from reactive to proactive defense enhances threat intelligence and reduces response time.
- Organizations must balance AI capabilities with human oversight to maintain robust security.
- Future trends include AI-augmented security teams and a focus on ethical AI deployment.
Related Articles
- ‘Computers are no longer a bicycle for the mind’: Frameworks founder says the Steve Jobs era is over and PCs are now a ‘self-driving car that takes you directly to the destination’ | TechRadar
- YouTube increases Premium price again, says 90-second unskippable ads are a bug - Ars Technica
- The Iranian Lego AI video creators credit their virality to ‘heart’ | The Verge
- Little Snitch Expands Its Counter Surveillance Toolkit from Mac to Linux [2025]
- Stalking victim sues OpenAI, claims ChatGPT fueled her abuser's delusions and ignored her warnings | TechCrunch
- ‘I want to cancel’: YouTube Premium quietly hikes its US prices for the first time in three years, forcing many users to consider the unthinkable | TechRadar
![Anthropic's Mythos: A Cybersecurity Turning Point [2025]](https://tryrunable.com/blog/anthropic-s-mythos-a-cybersecurity-turning-point-2025/image-1-1775846038101.jpg)



