Little Snitch Expands Its Counter Surveillance Toolkit from Mac to Linux [2025]
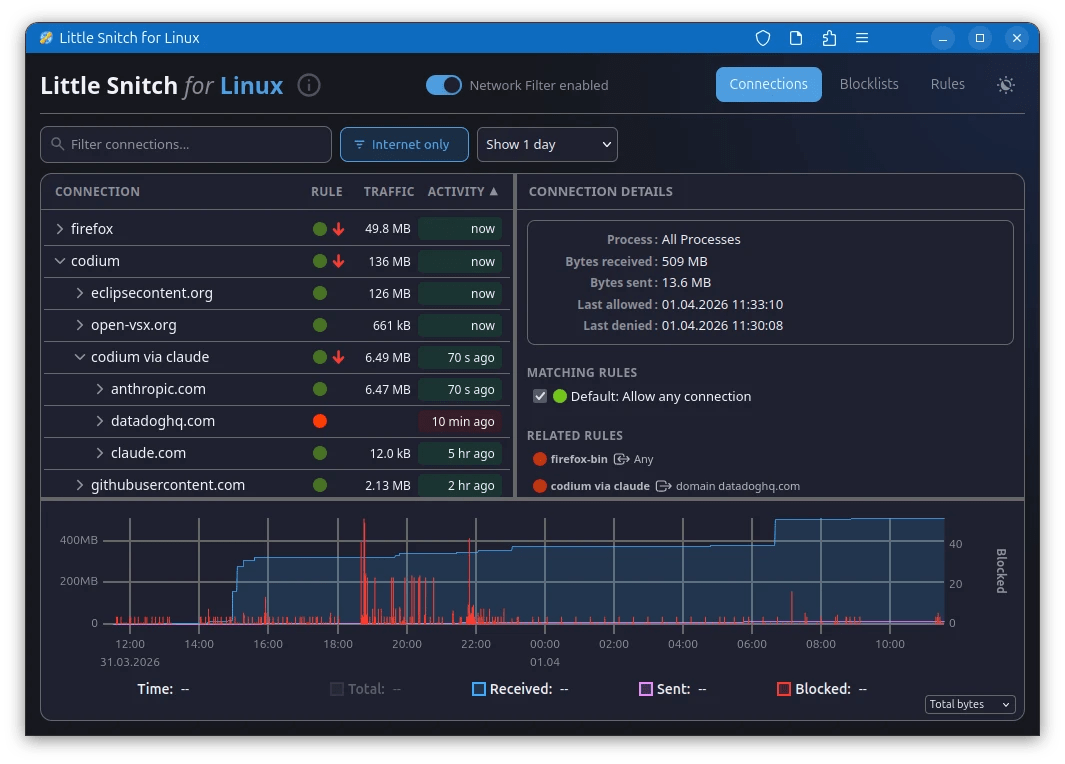
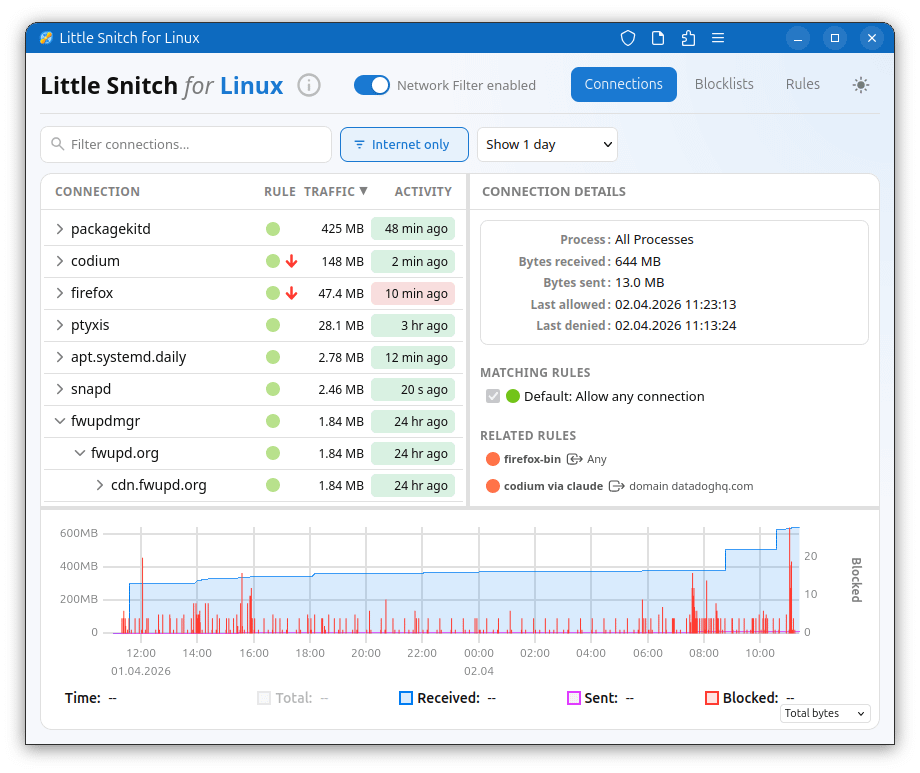
In a world where digital privacy is becoming increasingly scarce, Little Snitch has been a bastion for users seeking to control their data. Originally a staple on macOS for over a decade, Little Snitch is making headlines as it makes its long-awaited debut on Linux. This transition marks a significant milestone in the realm of cybersecurity, offering Linux users a sophisticated tool to monitor and manage network activities.
TL; DR
- Expanded Reach: Little Snitch, known for its robust network monitoring on macOS, is now available for Linux.
- Enhanced Privacy: Offers advanced tools for monitoring inbound and outbound network traffic.
- User Control: Empowers users to create custom rules for network connections.
- Open Source Considerations: Integrates with Linux's open-source ethos while maintaining proprietary elements.
- Future Trends: Sets the stage for more cross-platform cybersecurity tools.
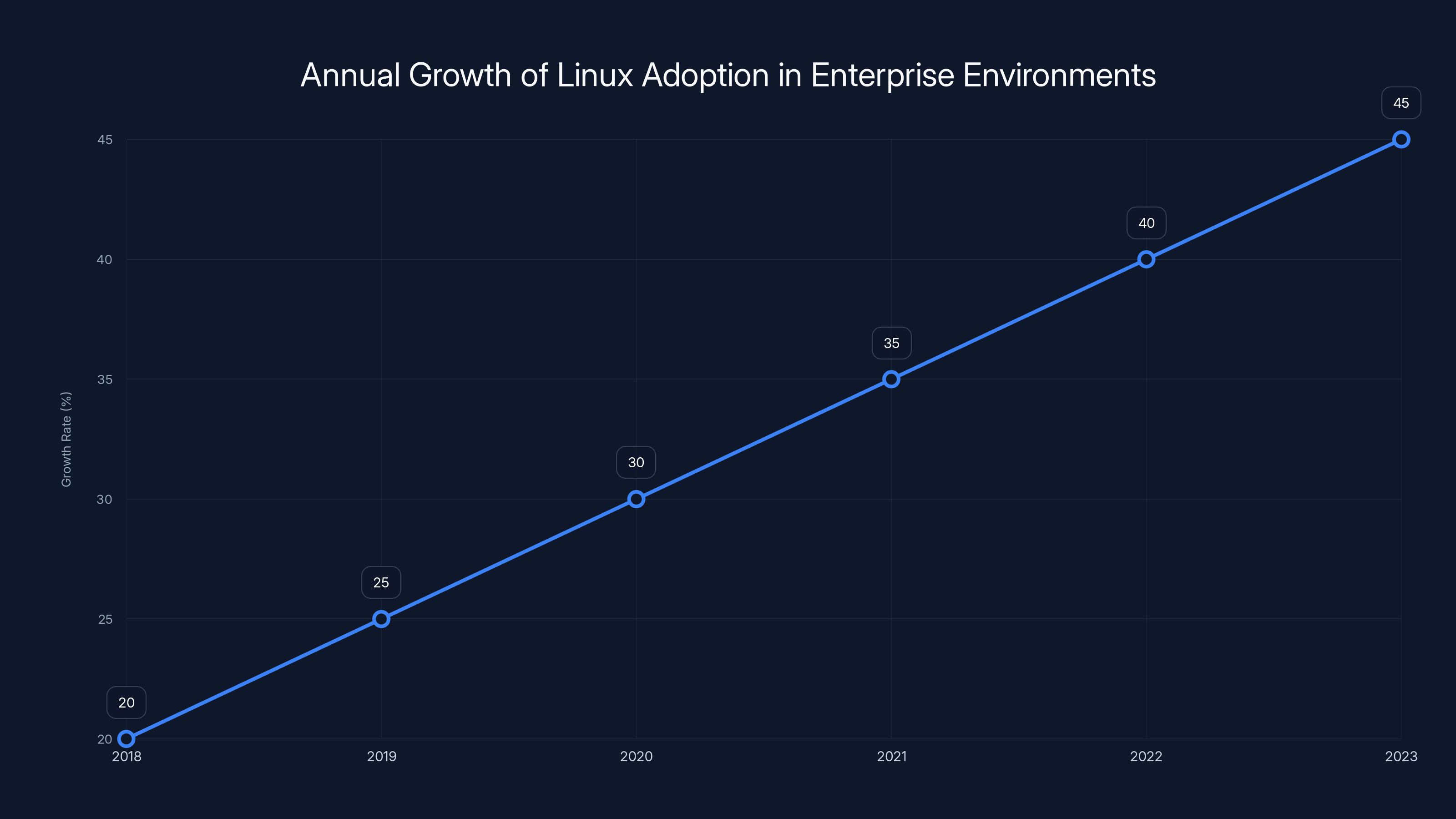
Linux adoption in enterprise environments has been growing steadily, with an estimated annual increase of over 30%. This trend highlights the expanding role of Linux in cloud and server infrastructures. (Estimated data)
The Evolution of Little Snitch
Little Snitch's journey began on macOS, where it quickly became a favorite among privacy enthusiasts. Known for its intuitive interface and powerful backend, it allowed users to see which applications were making network connections, and more importantly, to block unwanted ones. This feature was crucial at a time when data leaks and surveillance were becoming rampant.
Now, with its foray into Linux, Little Snitch is set to revolutionize how users on this open-source platform manage their network security. The decision to extend its capabilities to Linux is strategic, tapping into a user base that inherently values privacy and control.

Real-time network monitoring and a user-friendly interface are the most valued features of Little Snitch on Linux. (Estimated data)
Why Linux?
The Linux operating system is synonymous with open-source software and robust security features. Many of its users are developers, system administrators, and privacy advocates who favor Linux for its transparency and flexibility. By introducing Little Snitch to this environment, the software caters to a community that is already security-conscious.
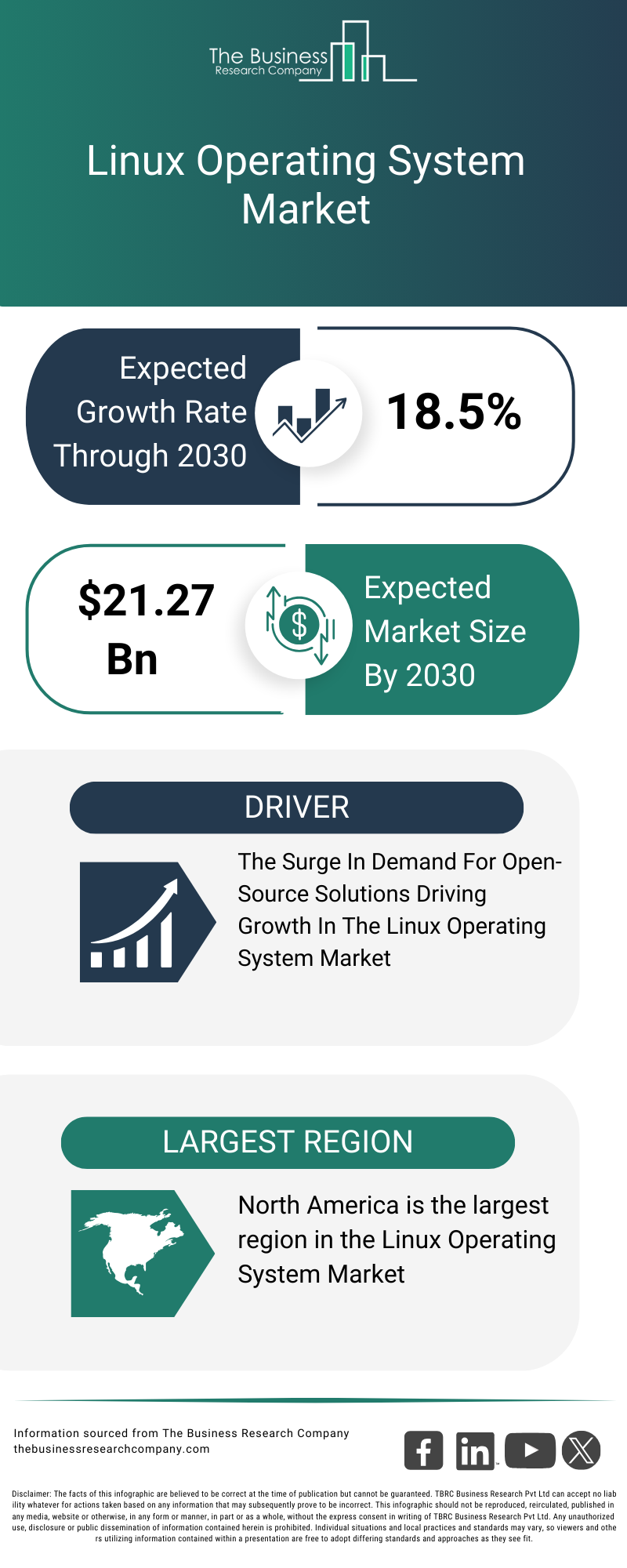
Linux Market Growth
Linux has seen significant growth, especially in enterprise environments. According to a report by the Linux Foundation, the adoption of Linux in cloud infrastructure and server environments has grown by over 30% annually in recent years. This growth presents a ripe opportunity for tools like Little Snitch to thrive.

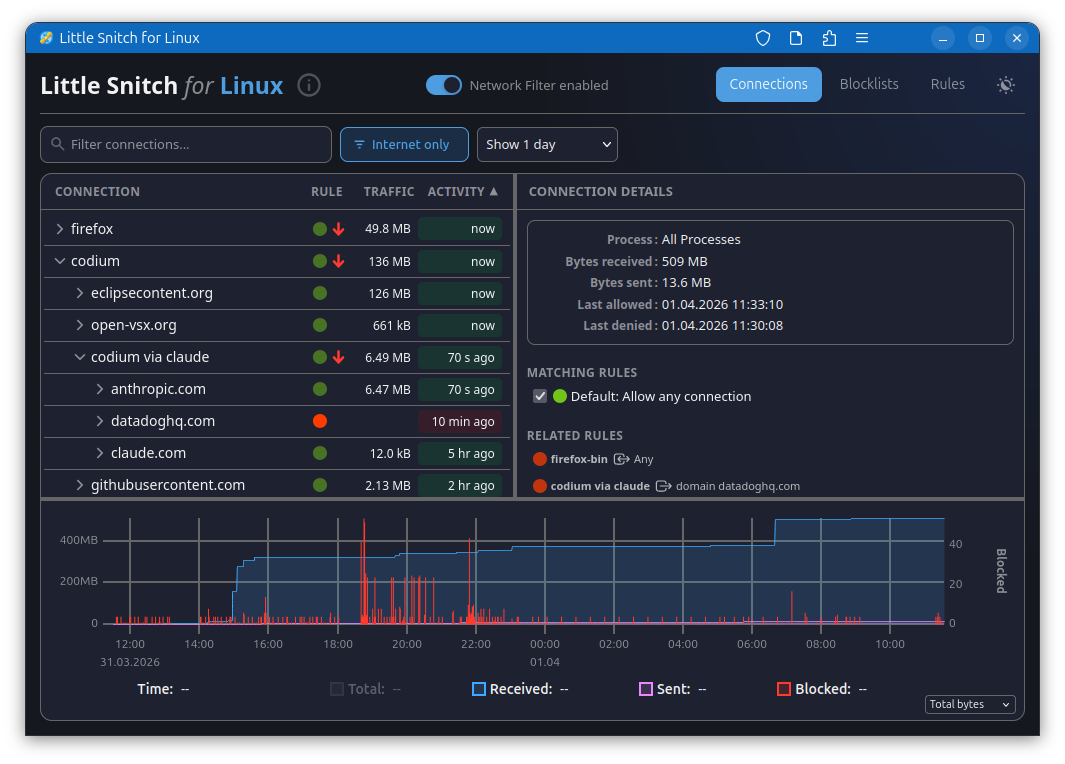
Key Features of Little Snitch on Linux
- Real-Time Network Monitoring: Provides users with a comprehensive view of all network traffic, allowing them to identify and block suspicious activities.
- Customizable Rulesets: Users can set detailed rules for how applications interact with the network, enabling precise control over data flow.
- Privacy Alerts: Instant notifications alert users to unauthorized attempts to access the internet.
- Connection History: Maintains a log of network connections for audit and review purposes.
- User-Friendly Interface: Despite Linux's reputation for complexity, Little Snitch offers a GUI that makes it accessible to both novices and experts.
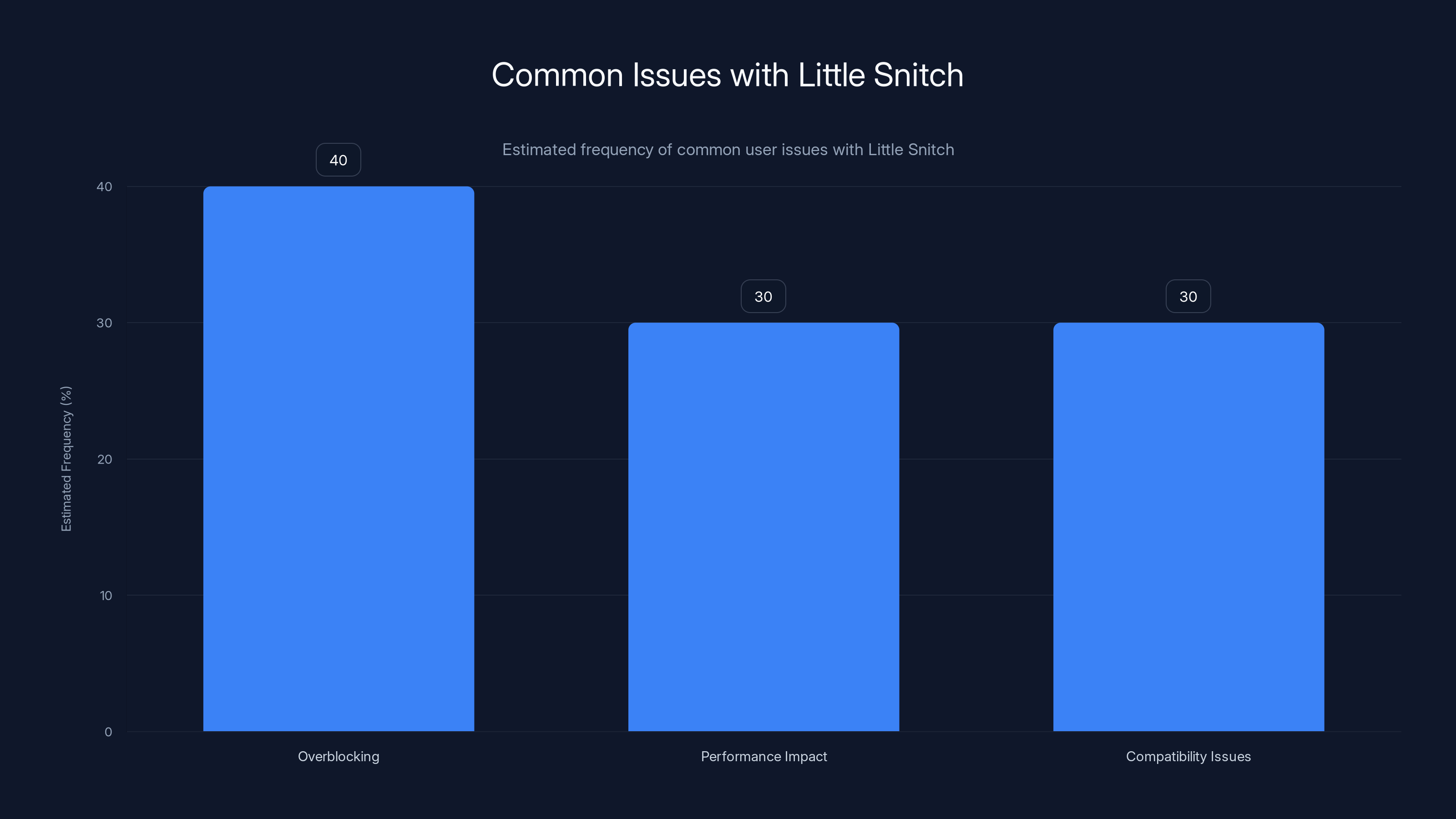
Overblocking is the most common issue faced by Little Snitch users, followed by performance impact and compatibility issues. Estimated data.
Implementation Guide: Setting Up Little Snitch on Linux
Installation Process
Installing Little Snitch on Linux is straightforward, thanks to its integration with popular package managers. Here’s a step-by-step guide:
-
Download the Package: Visit the official Little Snitch website to download the Linux package.
-
Install Dependencies: Ensure that your system has the necessary libraries, typically included in most distributions.
-
Run the Installer: Use terminal commands to execute the installer script. For example:
bashsudo dpkg -i littlesnitch-installer.deb -
Configure Initial Settings: Upon first launch, you’ll be prompted to configure basic settings, including default rules and alert preferences.
-
Reboot: A system restart might be required to finalize the installation.
QUICK TIP: Always back up your current firewall rules before installation to prevent conflicts.
Customizing Your Firewall
One of Little Snitch's strengths is its customizable firewall rules. Here’s how to tailor it to your needs:
- Define Application Rules: Specify which applications can access the internet. For instance, you might allow browsers but restrict telemetry services.
- Set Network Zones: Create zones for different network types—like home, work, and public—and apply rules accordingly.
- Use Profiles: Switch between profiles for different scenarios, such as traveling or working remotely.
Common Pitfalls and Solutions
While Little Snitch is powerful, users may encounter common issues. Here are solutions to some typical problems:
- Overblocking: New users might inadvertently block essential services. To resolve this, review blocked connections and whitelist necessary ones.
- Performance Impact: Monitoring all traffic can slow down older systems. Adjusting the level of detail in monitoring settings can mitigate this.
- Compatibility Issues: Some Linux distributions may have unique configurations that conflict with Little Snitch. Consulting the community forums or official support can provide tailored solutions.
QUICK TIP: Regularly update Little Snitch and your Linux system to ensure compatibility and access to the latest features.

Security Best Practices
To maximize the benefits of Little Snitch, consider these best practices:
- Regularly Review Logs: Make it a habit to check connection logs for any unauthorized access attempts.
- Educate Users: If deployed in an organization, training users on network security principles can prevent internal threats.
- Integrate with System Tools: Use Little Snitch alongside native Linux tools like
iptablesfor a robust security setup.
Future of Network Surveillance Tools
As digital threats evolve, so must the tools we use to combat them. The expansion of Little Snitch to Linux signals a broader trend in cybersecurity: cross-platform solutions. Here’s what the future might hold:
- AI Integration: Expect to see AI-driven insights within monitoring tools, providing predictive analytics and automated threat responses.
- Cloud-Based Controls: As more infrastructure moves to the cloud, tools like Little Snitch may offer cloud-centric solutions.
- Decentralized Monitoring: With privacy concerns growing, decentralized tools that offer peer-to-peer monitoring may gain popularity.
Recommendations for Developers
Developers looking to leverage Little Snitch’s capabilities should:
- Contribute to Open Source: Engage with the Linux community to enhance the tool’s functionality and integration.
- Focus on UI/UX: As more non-technical users adopt Linux, a user-friendly interface is crucial.
- Explore Modular Design: Modular tools that allow users to customize functionality can cater to diverse needs.
Conclusion
The launch of Little Snitch on Linux is a game-changer for network security on this platform. By providing robust surveillance tools, it empowers users to take control of their digital privacy. As technology advances, tools like Little Snitch will be integral to safeguarding personal and organizational data.
FAQ
What is Little Snitch?
Little Snitch is a network monitoring tool that allows users to track and control outbound and inbound connections on their computers.
How does Little Snitch work on Linux?
On Linux, Little Snitch functions similarly to its macOS counterpart, offering real-time monitoring and customizable rulesets to manage network traffic.
What are the benefits of using Little Snitch?
Benefits include enhanced privacy, user control over network connections, and real-time alerts for unauthorized activities.
Can Little Snitch impact system performance?
While comprehensive monitoring can strain older systems, configuring the tool to limit resource usage can mitigate this.
Is Little Snitch open-source on Linux?
Little Snitch maintains its proprietary status, though it integrates well with Linux’s open-source ecosystem.
How can developers contribute to Little Snitch's growth?
Developers can engage with the community, offer feedback, and even develop plugins or add-ons to extend its functionality.
Key Takeaways
- Little Snitch expands its capabilities from macOS to Linux, providing advanced network monitoring tools.
- The software offers users enhanced privacy with customizable rules for managing network connections.
- Linux's growing enterprise adoption presents a significant opportunity for Little Snitch.
- Potential challenges include system performance impacts and compatibility issues with certain distributions.
- Future trends in network monitoring tools include AI integration and cloud-based solutions.
- Developers are encouraged to engage with the open-source community to enhance Little Snitch's functionality.
Related Articles
- Exploring the Future of Linux: Framework's Big Reveal [2025]
- Navigating Ubuntu's Increased RAM Requirements Amidst Global Shortages [2025]
- Understanding the Snowflake Data Theft Incident: Lessons and Future Safeguards [2025]
- AdGuard VPN New iPhone App: A Comprehensive Review [2025]
- Microsoft's Cloud PC Price Cut: A Game Changer for SMBs [2025]
- Claude Cowork Unleashed for Enterprise: Analytics, Access Controls & More [2025]
![Little Snitch Expands Its Counter Surveillance Toolkit from Mac to Linux [2025]](https://tryrunable.com/blog/little-snitch-expands-its-counter-surveillance-toolkit-from-/image-1-1775840702876.jpg)



