Introduction
Imagine a vault designed to protect your most precious information. Secure, impenetrable, a fortress of privacy. But what if someone found an unguarded side entrance, a vulnerability that could compromise everything? This is the reality with Windows 11's Recall feature, and a tool called Total Recall Reloaded has brought this issue to light. According to XDA Developers, this tool has exposed significant weaknesses in the Recall feature, allowing unauthorized access to user data.
In this article, we dive deep into how Total Recall Reloaded exploits Windows 11's Recall database. We'll explore its implications, provide practical implementation guides, and discuss future trends in AI and security. Whether you're a developer, IT professional, or tech enthusiast, this guide will equip you with the knowledge to navigate these challenges effectively.

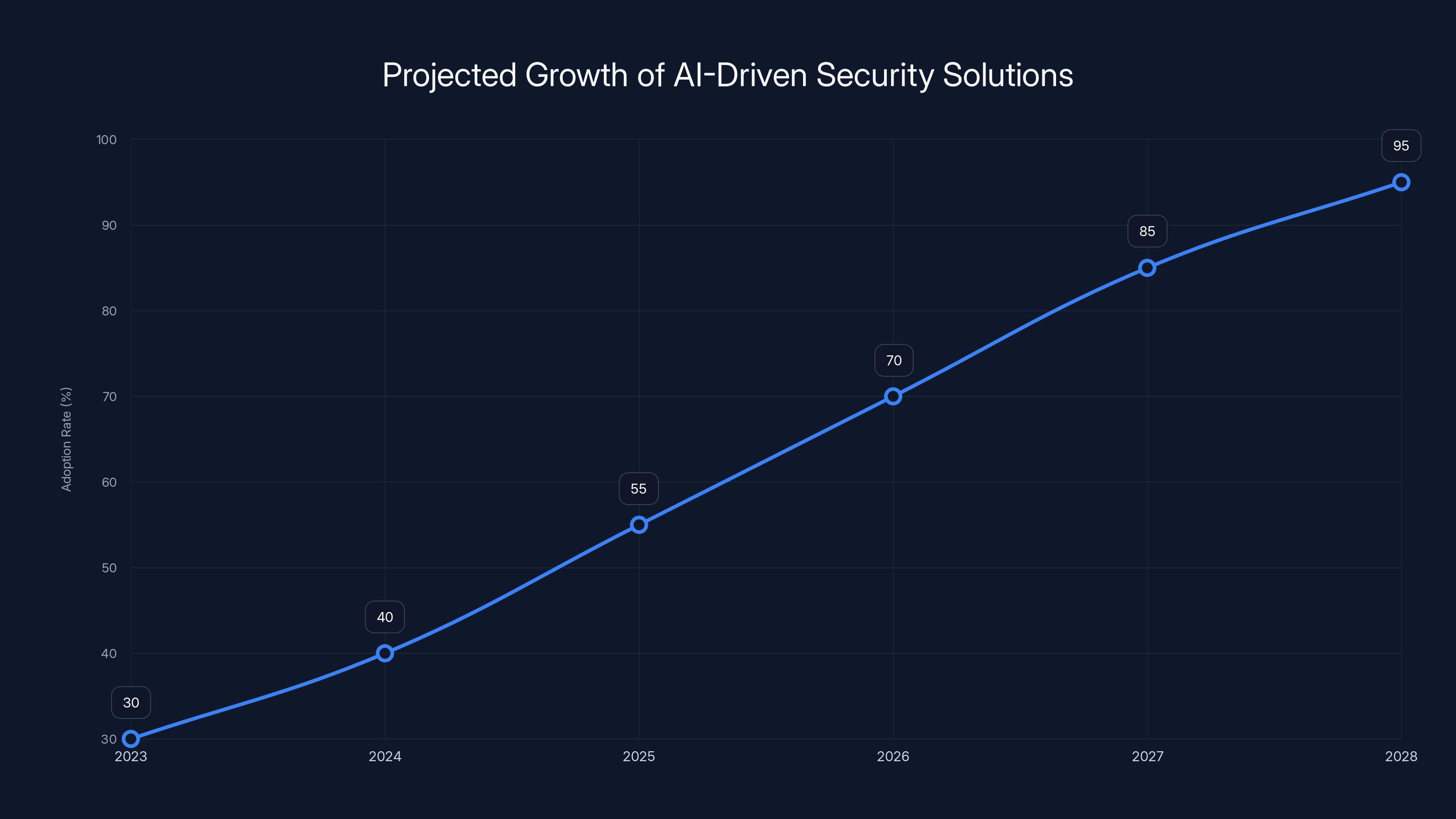
The adoption of AI-driven security solutions is projected to increase significantly, reaching 95% by 2028. (Estimated data)
TL; DR
- Vulnerability Exposed: Total Recall Reloaded reveals weaknesses in Windows 11's Recall feature, accessing unencrypted user activity data.
- Security Challenge: The tool highlights the ongoing struggle between innovation and security in AI and machine learning, as noted by Digital Today.
- Practical Solutions: Implementing encryption and access controls are key to mitigating such vulnerabilities.
- Future Trends: Expect increased focus on secure AI implementation as technologies evolve, as discussed in KPMG's insights.
- Bottom Line: Vigilance and proactive measures are essential to safeguard user data in the AI-driven era.
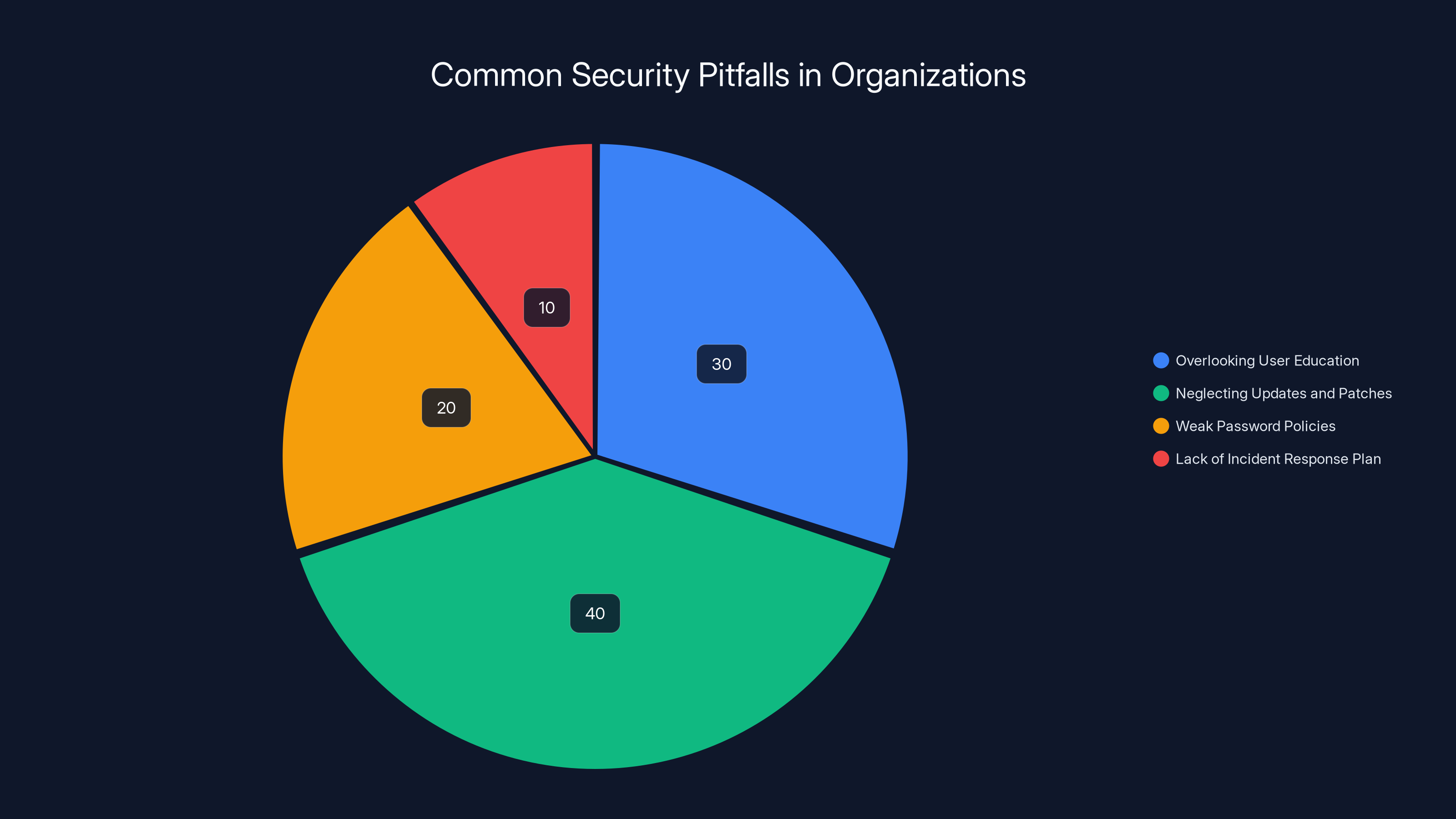
Neglecting updates and patches is the most common pitfall, estimated to account for 40% of security issues, highlighting the need for regular system maintenance. Estimated data.
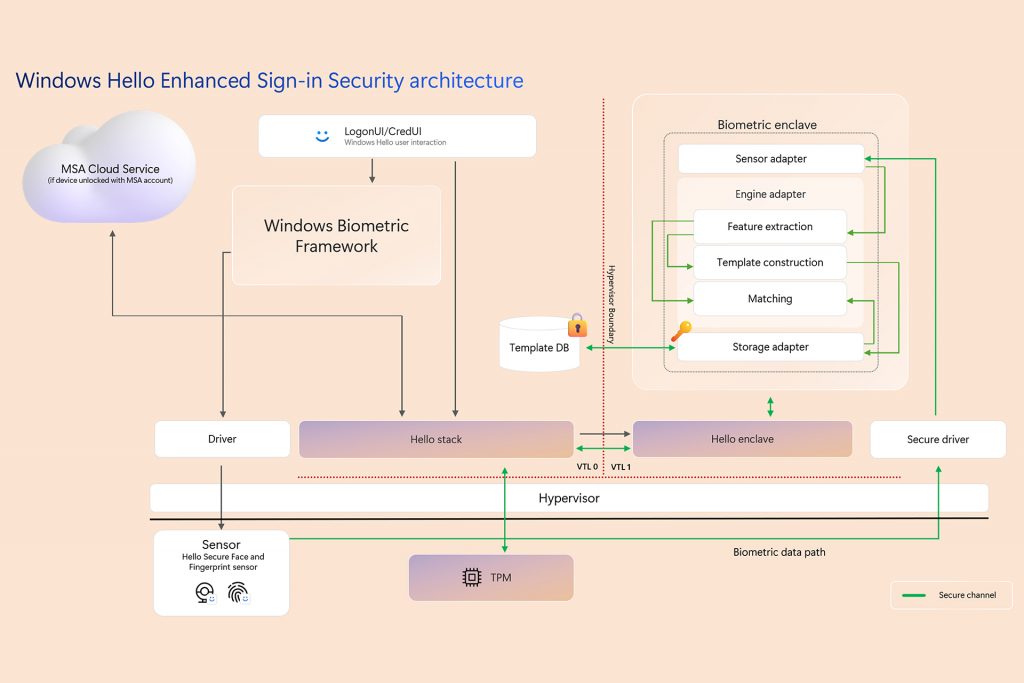
Understanding the Recall Feature
Windows 11 introduced the Recall feature as part of its Copilot+ suite, aiming to enhance user productivity by tracking PC usage through screenshots. While this feature promised convenience, it also opened a Pandora's box of security concerns. According to TechCrunch, Microsoft has faced challenges in balancing functionality with security.
The Recall feature captures user activity in real-time, storing screenshots and metadata in a database. This data can theoretically help users recall past actions, but it also presents a significant vulnerability if not properly secured.
The Anatomy of a Vulnerability
Recall stores its data in unencrypted files on the user's disk, making it susceptible to unauthorized access. This design flaw is what Total Recall Reloaded exploits, allowing for the extraction of sensitive information without any sophisticated hacking techniques, as reported by TweakTown.
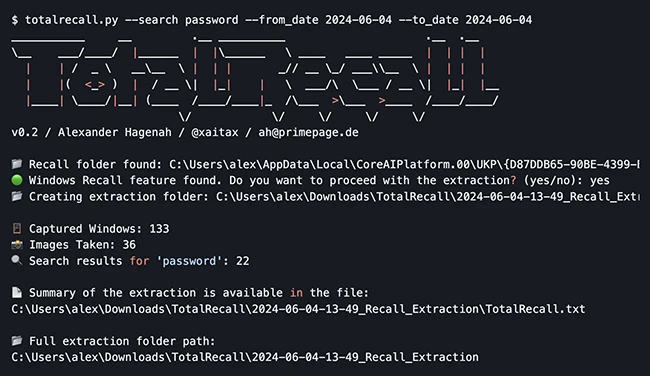
Total Recall Reloaded: The Tool Behind the Curtain
Total Recall Reloaded is a tool designed to take advantage of the Recall feature's vulnerabilities. By exploiting the unencrypted storage of user data, it can access and extract information that should be private. As GeekWire highlights, this tool underscores the ongoing privacy concerns surrounding Microsoft's Recall feature.
How It Works
Total Recall Reloaded utilizes a combination of scripting and automation to locate and access Recall's database files. By navigating through the file system, it identifies and extracts screenshots and metadata, potentially exposing sensitive information.
Use Cases and Implications
While Total Recall Reloaded can be seen as a security threat, it also serves as a wake-up call for developers and IT professionals. Understanding its operation can guide the creation of more secure systems in the future.
- Corporate Espionage: Unauthorized access to business data can lead to competitive disadvantages, as discussed in TradingView's analysis.
- Personal Privacy: Users' personal information, such as passwords and private communications, is at risk.
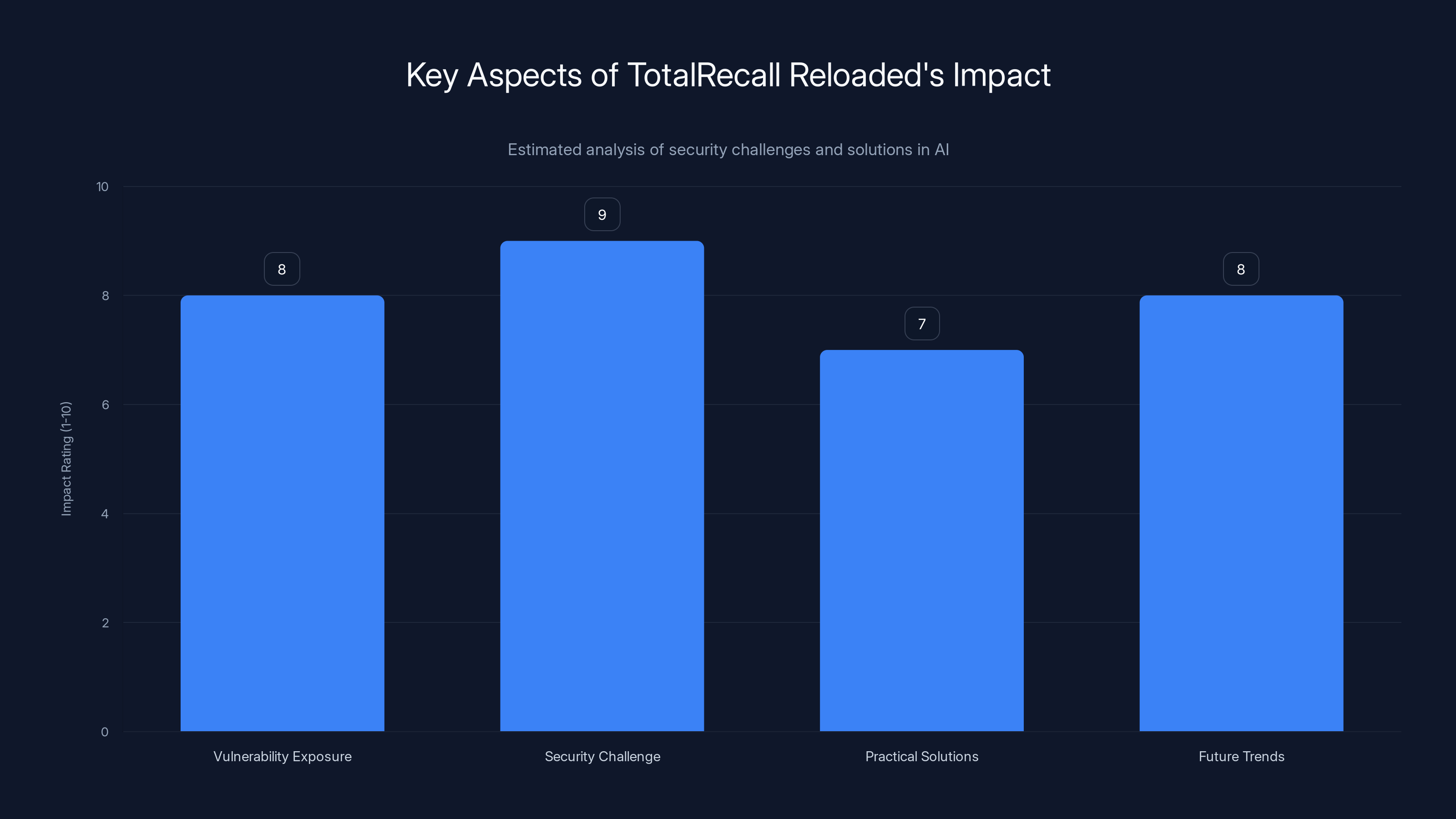
Estimated data shows high impact ratings for security challenges and future trends, emphasizing the need for vigilance.
Practical Implementation Guides
Addressing the vulnerabilities exposed by Total Recall Reloaded requires a proactive approach. Here are some practical steps for securing the Recall feature and similar technologies.
Encrypting Data at Rest
Encryption is a fundamental security measure that can protect sensitive data stored on disk. Implementing robust encryption protocols ensures that even if data is accessed, it remains unreadable without the proper decryption keys. GBHackers emphasizes the importance of encryption in protecting against vulnerabilities.
plaintext# Example of AES Encryption in Python from Crypto. Cipher import AES def encrypt_data(data, key): cipher = AES.new(key, AES. MODE_EAX) ciphertext, tag = cipher.encrypt_and_digest(data) return cipher.nonce, ciphertext, tag
Implementing Access Controls
Restricting access to sensitive data is crucial. By implementing role-based access controls (RBAC), organizations can ensure that only authorized users have access to specific data.
- Define Roles: Clearly outline user roles and their access privileges.
- Monitor Access: Use logging and monitoring tools to track data access and identify anomalies.
Regular Security Audits
Conducting regular security audits helps identify and address vulnerabilities before they can be exploited. Audits should include:
- Code Reviews: Ensure that code adheres to security best practices.
- Penetration Testing: Simulate attacks to identify potential weaknesses.

Common Pitfalls and Solutions
Implementing security measures can be challenging, and there are common pitfalls to watch out for.
Overlooking User Education
Users are often the weakest link in security. It's essential to educate them about the importance of security measures and how to recognize potential threats.
Neglecting Updates and Patches
Outdated software is a prime target for attacks. Ensure that all systems and applications are regularly updated with the latest security patches. The Verge reports that neglecting updates is a significant contributor to security breaches.
Future Trends and Recommendations
As AI and machine learning technologies continue to evolve, so too will the security challenges they present. Here are some trends and recommendations to watch for in the future.
AI-Driven Security Solutions
AI can be both a target and a tool for security. Leveraging AI for security purposes can enhance threat detection and response times. Wiz.io discusses how AI can improve security measures through anomaly detection and automated responses.
- Anomaly Detection: AI can identify unusual patterns that may indicate a security breach.
- Automated Responses: AI systems can automatically respond to threats, reducing response times.
Increased Focus on Secure AI Implementation
As AI becomes more integrated into everyday applications, ensuring its secure implementation will be paramount. This includes:
- Secure Development Practices: Incorporating security into the software development lifecycle.
- Ethical AI Use: Ensuring that AI technologies are used responsibly and ethically.
Conclusion
The Total Recall Reloaded tool has exposed significant vulnerabilities in Windows 11's Recall feature. As we continue to integrate AI and machine learning into our systems, security must remain a top priority. OpenTools highlights the importance of AI in revolutionizing cybersecurity defense.
By implementing encryption, access controls, and regular audits, we can mitigate these risks and protect sensitive data. As the landscape of technology continues to evolve, staying informed and proactive will be key to navigating the challenges ahead.
FAQ
What is Total Recall Reloaded?
Total Recall Reloaded is a tool designed to exploit vulnerabilities in Windows 11's Recall feature, allowing unauthorized access to unencrypted user data.
How does Total Recall Reloaded work?
It uses scripting and automation to locate and access Recall's database files, extracting screenshots and metadata stored on the user's disk.
What are the security implications of the Recall feature?
The unencrypted storage of user data presents significant privacy and security risks, making it susceptible to unauthorized access.
How can I protect my data from similar vulnerabilities?
Implement encryption for data at rest, use access controls, conduct regular security audits, and educate users on security best practices.
What are the future trends in AI and security?
Expect increased use of AI-driven security solutions, a focus on secure AI implementation, and ongoing development of ethical AI practices.
Why is user education important in maintaining security?
Educated users are less likely to fall victim to phishing and other social engineering attacks, reducing the risk of security breaches.
How does AI enhance security measures?
AI can improve threat detection through anomaly detection and automate responses to security threats, enhancing overall security posture.
What role does encryption play in data security?
Encryption protects data by making it unreadable without the correct decryption key, safeguarding it from unauthorized access.
Key Takeaways
- TotalRecall Reloaded exposes security vulnerabilities in Windows 11's Recall feature.
- Implementing encryption and access controls is crucial for data protection.
- AI-driven security solutions can enhance threat detection and response.
- User education is vital in reducing the risk of security breaches.
- Future trends include secure AI implementation and ethical AI practices.
Related Articles
- Microsoft's Ongoing Windows Recall: Navigating Security Concerns [2025]
- Google's Gemini AI App Launch on Mac: A New Era in AI Integration [2025]
- Microsoft Recall Tool: Unpacking Security Concerns and Denials [2025]
- Claude's Current Challenges: Understanding the Issues and Future Prospects [2025]
- Mastering Windows 11: Bringing macOS's Most Useful Feature to Your Desktop [2025]
- Amazon's AI Bio Discovery Tool: Revolutionizing Drug Discovery [2025]
![Cracking the Code: Exploring TotalRecall Reloaded and Windows 11's Recall Database [2025]](https://tryrunable.com/blog/cracking-the-code-exploring-totalrecall-reloaded-and-windows/image-1-1776287049585.jpg)



