From Boardroom Risk to Deal Flow: Why Cyber M&A is Accelerating in 2026
Introduction
Last year, the conversation around cyber security transformed dramatically. What was once seen as a technical challenge relegated to the IT department has now become a strategic priority for boardrooms worldwide. As we enter 2026, this shift is driving unprecedented levels of mergers and acquisitions (M&A) in the cyber sector. The reason? Cyber security is no longer just about preventing breaches; it's about ensuring business continuity, protecting reputation, and complying with increasingly stringent regulations.

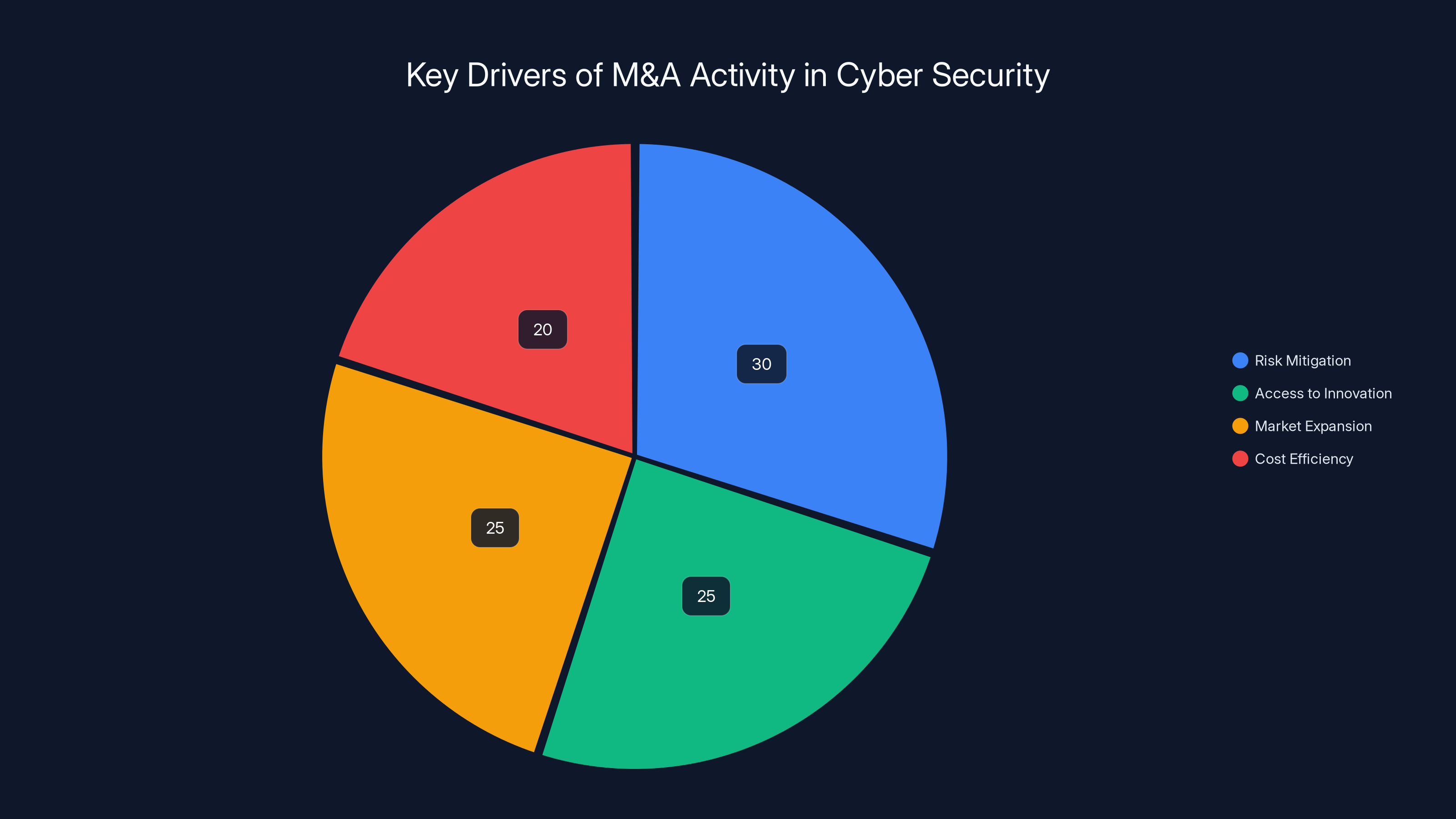
Risk mitigation is the leading driver of M&A activity in cyber security, followed closely by access to innovation and market expansion. Estimated data.
TL; DR
- Cyber Security Shift: It's now a boardroom priority, not just an IT issue.
- M&A Boom: Driven by the need for resilience and compliance.
- Regulatory Pressure: New laws are pushing firms to consolidate.
- Innovation Imperative: Companies seek cutting-edge tech through acquisitions.
- Future Trends: AI and machine learning are becoming central to M&A strategies.

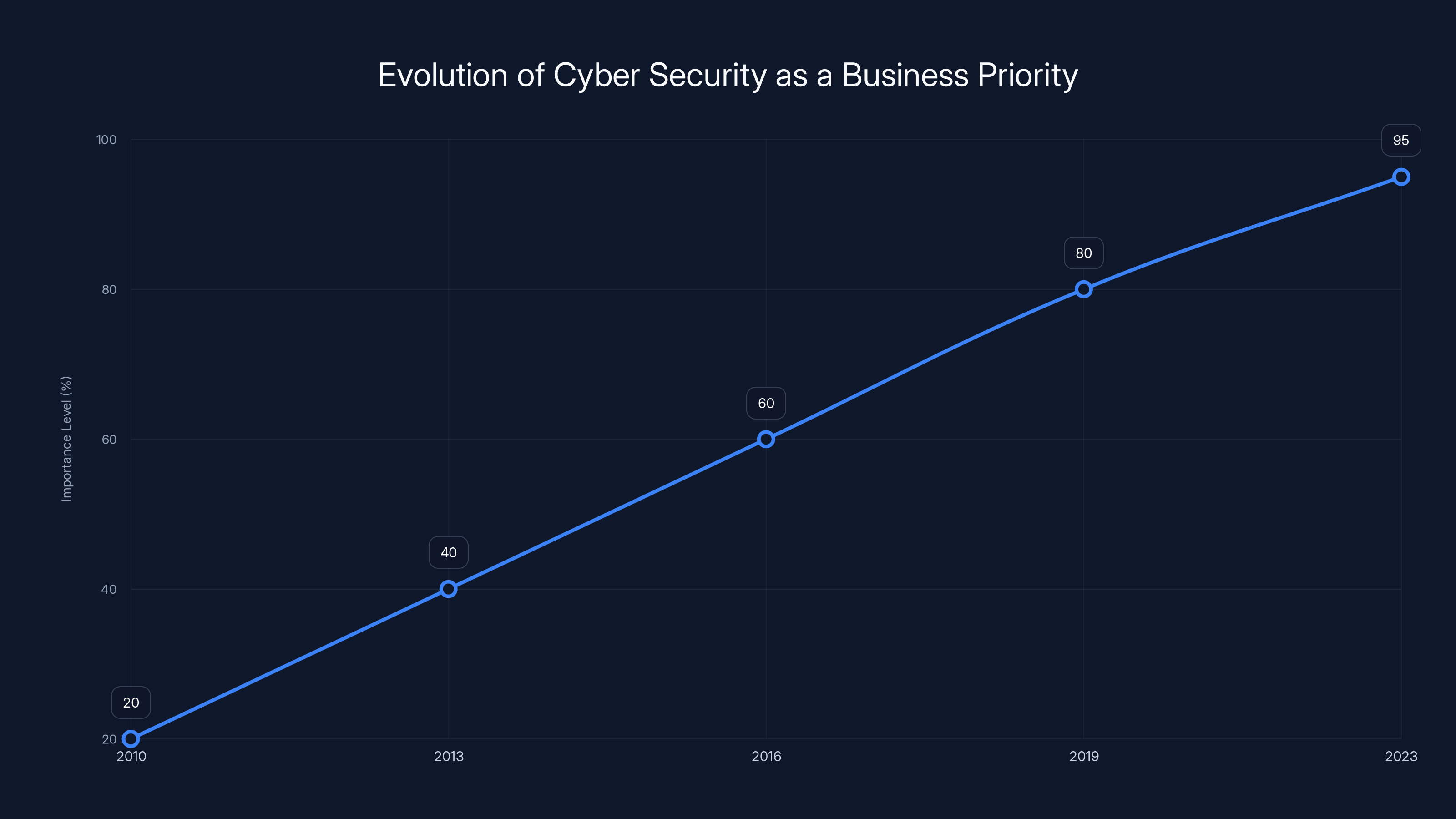
Cyber security has evolved from an IT concern to a top boardroom priority, with its importance significantly rising from 20% in 2010 to 95% in 2023. (Estimated data)
The Changing Landscape of Cyber Security
From IT Concern to Boardroom Priority
Cyber security has always been essential, but its role has evolved. In the past, it was primarily a concern for IT departments, tasked with managing firewalls and antivirus software. However, as cyber threats have grown more sophisticated, the stakes have increased. Today, a significant breach can lead to severe financial losses, damage to brand reputation, and legal consequences.
This evolution is largely due to the increase in high-profile cyber attacks. Events like the Solar Winds breach and the Colonial Pipeline attack have shown companies worldwide that no organization is immune. As a result, cyber security is now seen as a critical component of business strategy.
Regulatory Pressure and Compliance
Governments around the globe are introducing stricter regulations to protect data and privacy. The European Union's General Data Protection Regulation (GDPR) set the stage, and similar laws are being adopted worldwide. Compliance is no longer optional; it's mandatory, and the penalties for non-compliance are severe.
For multinational corporations, this means navigating a complex web of regulations across different jurisdictions. As a result, there's a growing demand for cyber solutions that can ensure compliance, leading companies to seek acquisitions that enhance their regulatory capabilities.

The M&A Surge in Cyber Security
Why Companies Are Merging
The acceleration of M&A activity in the cyber sector can be attributed to several factors:
- Risk Mitigation: By acquiring specialized cyber firms, companies can mitigate risks more effectively.
- Access to Innovation: Buying companies with cutting-edge technologies allows for rapid integration of new capabilities.
- Market Expansion: Acquisitions enable companies to expand their market reach and customer base.
- Cost Efficiency: Consolidating resources and streamlining operations can lead to significant cost savings.
Key Players in the Market
Several high-profile acquisitions have taken place recently, highlighting the trend:
- Microsoft's Acquisition of Risk IQ: Aimed at enhancing threat intelligence capabilities.
- Google's Purchase of Mandiant: Focused on expanding incident response and threat detection.
- Cisco's Acquisition of Kenna Security: To improve vulnerability management offerings.
These moves are not just about acquiring technology but also about gaining expertise and expanding into new markets.


Integration delays are often the most impactful challenge in M&A, followed by cultural mismatches and overvaluation. Estimated data based on typical M&A experiences.
Technical Details and Best Practices
Integrating Acquired Technologies
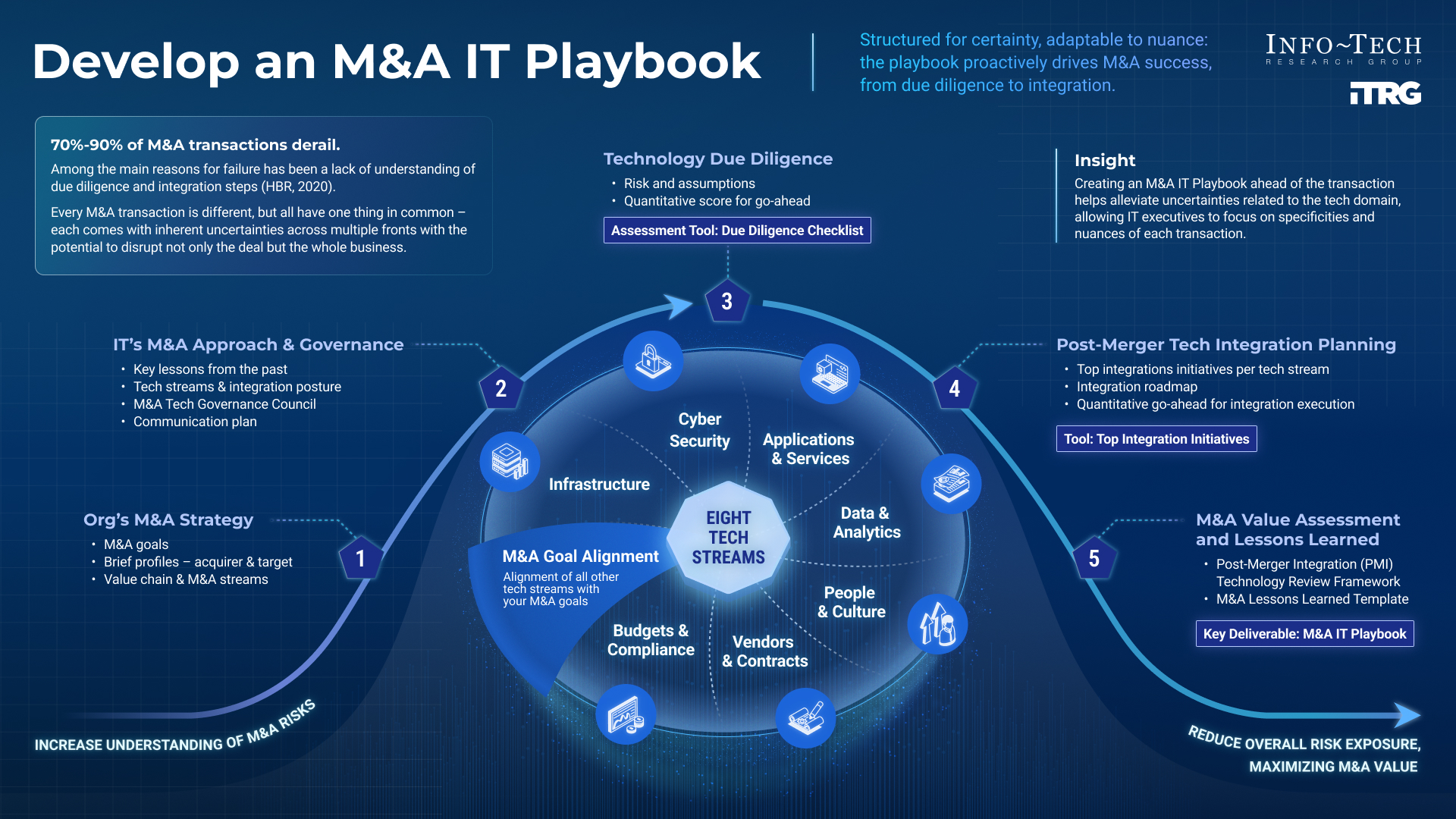
One of the challenges of M&A is integrating different technologies and systems. Successful integration requires a comprehensive strategy:
- Assessment: Evaluate the compatibility of systems and identify potential integration challenges.
- Planning: Develop a roadmap for integration, prioritizing critical systems and processes.
- Execution: Use phased approaches to minimize disruption and ensure a smooth transition.
Common Pitfalls and Solutions
M&A activities are fraught with challenges. Here are some common pitfalls and how to avoid them:
- Cultural Mismatches: Ensure alignment of organizational cultures to avoid internal conflicts.
- Overvaluation: Conduct thorough due diligence to prevent overpaying for acquisitions.
- Integration Delays: Establish clear timelines and dedicated teams to oversee integration efforts.

Future Trends in Cyber M&A
The Role of AI and Machine Learning
Artificial intelligence (AI) and machine learning (ML) are becoming central to cyber security strategies. These technologies offer advanced threat detection and response capabilities, making them attractive targets for M&A.
Cloud Security
As more businesses move their operations to the cloud, securing these environments becomes critical. Cloud security solutions are in high demand, and companies are racing to acquire firms that offer these capabilities.
Io T Security
The Internet of Things (Io T) brings convenience but also new vulnerabilities. Acquiring companies with expertise in Io T security can provide a competitive edge.

Recommendations for Companies Considering M&A
Conduct Thorough Due Diligence
Before any acquisition, companies should conduct extensive due diligence to understand the target's financial health, technological capabilities, and cultural fit.
Focus on Strategic Alignment
Ensure that any acquisition aligns with the company's long-term strategic goals, not just short-term gains.
Invest in Integration
Successful M&A requires investment in integration. Allocate resources to ensure that systems, processes, and cultures are effectively merged.
Conclusion
The acceleration of cyber M&A in 2026 reflects the growing importance of cyber security in the business world. As companies seek to protect themselves against evolving threats and comply with regulations, the trend of acquiring cyber capabilities will continue. By focusing on strategic alignment, thorough due diligence, and effective integration, companies can successfully navigate the complex landscape of cyber M&A.
FAQ
What is driving the increase in cyber M&A?
The increase in cyber M&A is driven by the need for enhanced security, regulatory compliance, and access to innovative technologies.
How can companies ensure successful integration after a cyber M&A?
Companies can ensure successful integration by conducting thorough assessments, developing a clear roadmap, and investing in dedicated integration teams.
What role does AI play in cyber security M&A?
AI plays a critical role in enhancing threat detection and response capabilities, making it a key factor in cyber security M&A strategies.
Why is regulatory compliance important in cyber M&A?
Regulatory compliance is crucial to avoid legal penalties and to ensure that companies can operate across different jurisdictions.
How do cultural differences impact cyber M&A?
Cultural differences can lead to internal conflicts and integration challenges, making it important to assess cultural alignment before proceeding with an acquisition.
What are the future trends in cyber security?
Future trends in cyber security include increased focus on AI and ML, cloud security, and Io T security, as companies seek to protect their digital assets.

Key Takeaways
- Cyber security is now a boardroom priority, with significant impacts on business strategy.
- The rise in M&A activity is driven by the need for enhanced security and compliance.
- AI and machine learning are becoming central to cyber security strategies.
- Successful M&A requires thorough due diligence and strategic alignment.
- Future trends include increased focus on cloud and IoT security.
Related Articles
- Global Reach: PureVPN's Expansion with 40+ New Server Locations [2025]
- AI's Theoretical Limits and Its Real-World Impact on Jobs [2025]
- ChatGPT 5.3: Unpacking the Cringe Factor with Real Prompts [2025]
- Hacking Security Cameras: A New Weapon in Modern Warfare [2025]
- UK Government Delays AI Copyright Rules Amid Artist Outcry [2025]
- Navigating the Challenges of Age Verification for App Stores [2025]




