Hacking Security Cameras: A New Weapon in Modern Warfare [2025]
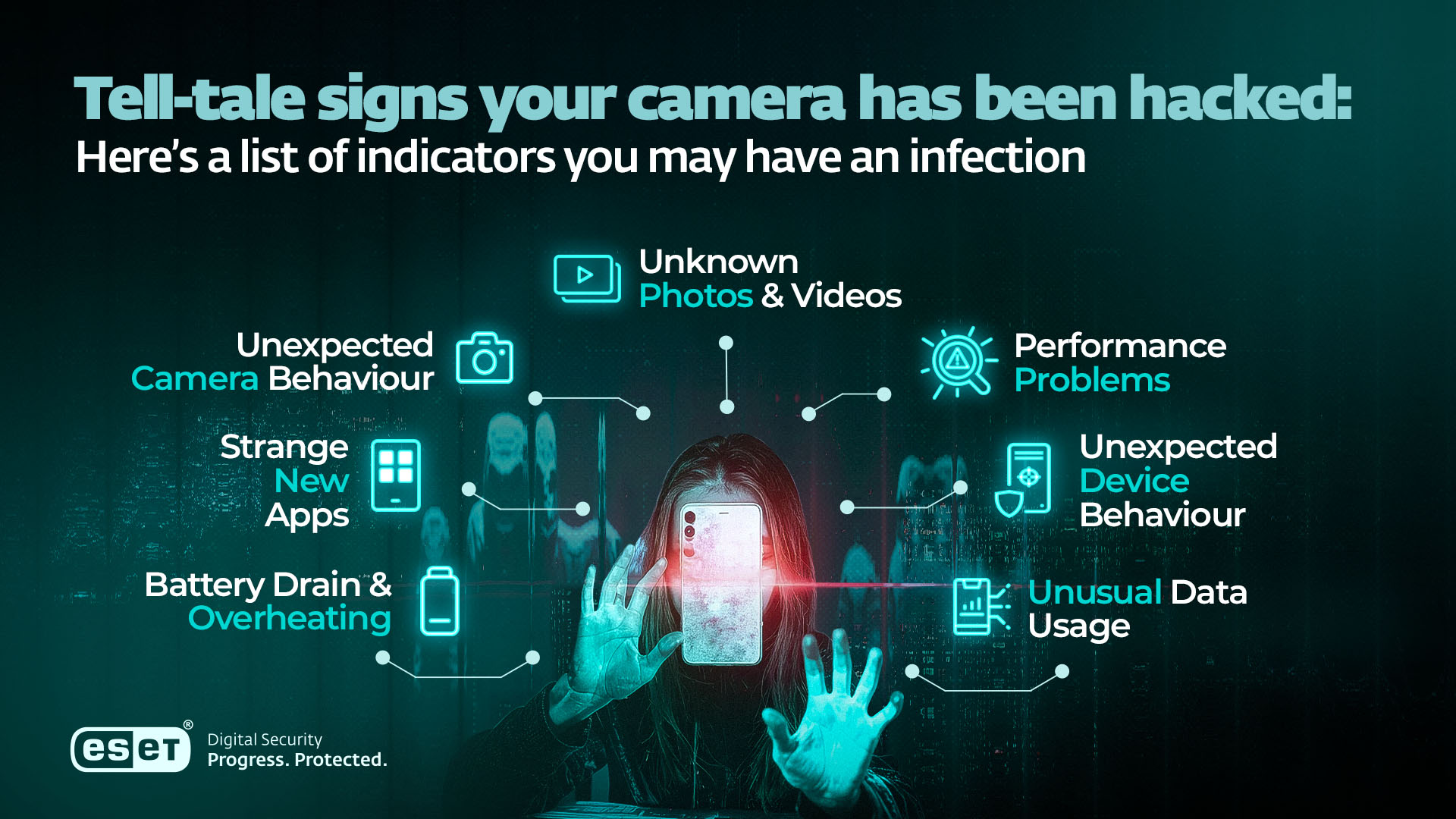
Last month, a new wave of cyberattacks targeted consumer-grade security cameras in urban areas worldwide. This isn't just about privacy concerns—it's a strategic move in modern warfare, where every hackable device becomes a potential surveillance asset.
TL; DR
- Security cameras are now strategic assets: Used for reconnaissance in conflict zones.
- Cyberattacks on cameras are increasing: Driven by state-sponsored groups.
- Technical vulnerabilities abound: Many cameras lack basic security measures.
- Mitigation requires robust strategies: Incorporating encryption and regular updates.
- Future trends suggest more integrated attacks: As IoT devices proliferate.
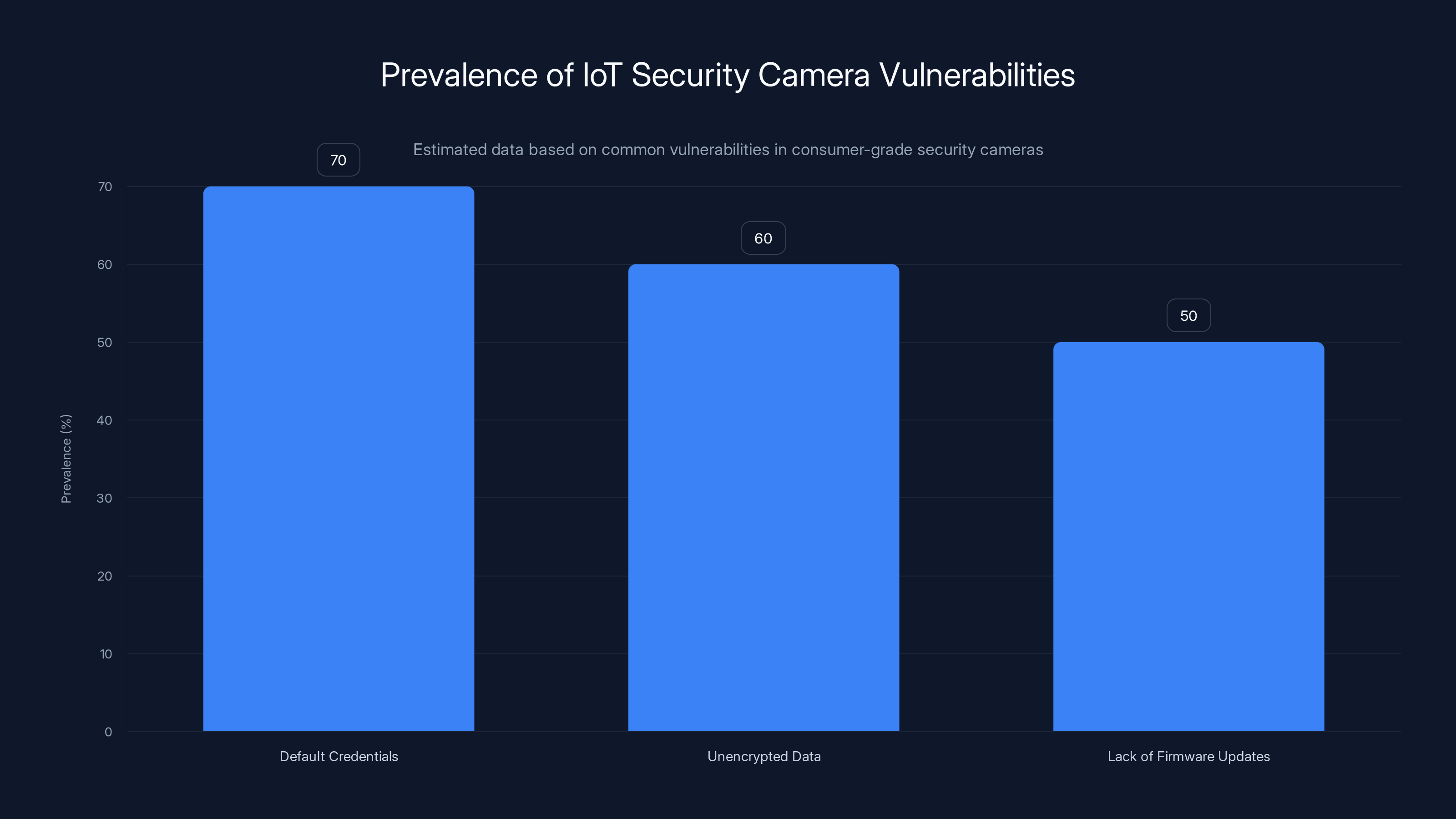
Default credentials are the most prevalent vulnerability in IoT security cameras, affecting approximately 70% of devices. Estimated data.
The Rise of Cyber Warfare
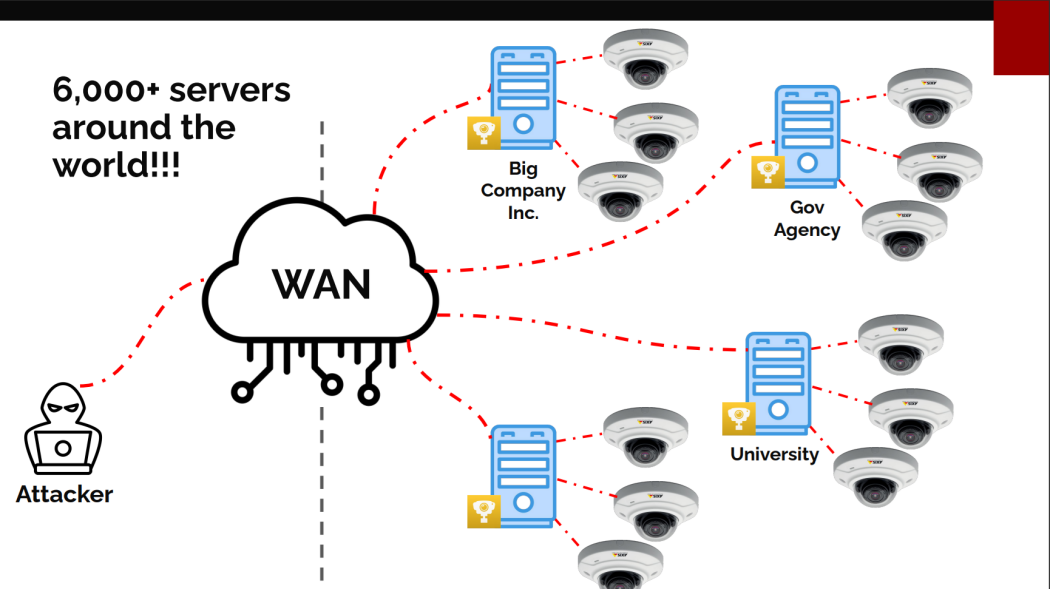
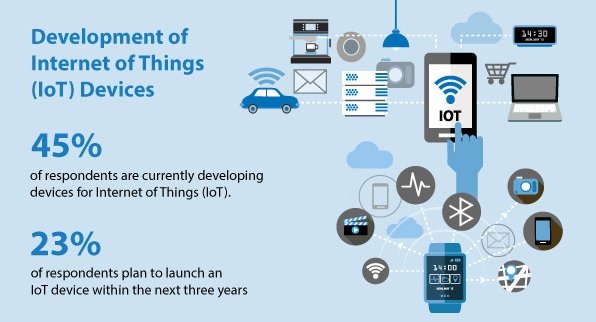
In recent years, cyber warfare has evolved from a niche concern to a central component of military strategy. With the proliferation of Internet of Things (IoT) devices, including security cameras, attackers now have new vectors to exploit. These devices are often poorly secured, making them easy targets for state-sponsored hackers.
The Strategic Value of Security Cameras
Security cameras provide real-time visual intelligence that can be critical in military operations. They offer a ground-level view that satellites and drones can't always provide. For example, during conflicts in Ukraine, hacked cameras have been used to monitor troop movements and assess damage from strikes.
Key Benefits of Hacking Security Cameras:
- Real-time surveillance: Immediate intelligence without the need for expensive hardware.
- Widespread availability: Cameras are ubiquitous in urban and high-value areas.
- Low cost: Accessing these feeds is cheaper than deploying traditional surveillance equipment.
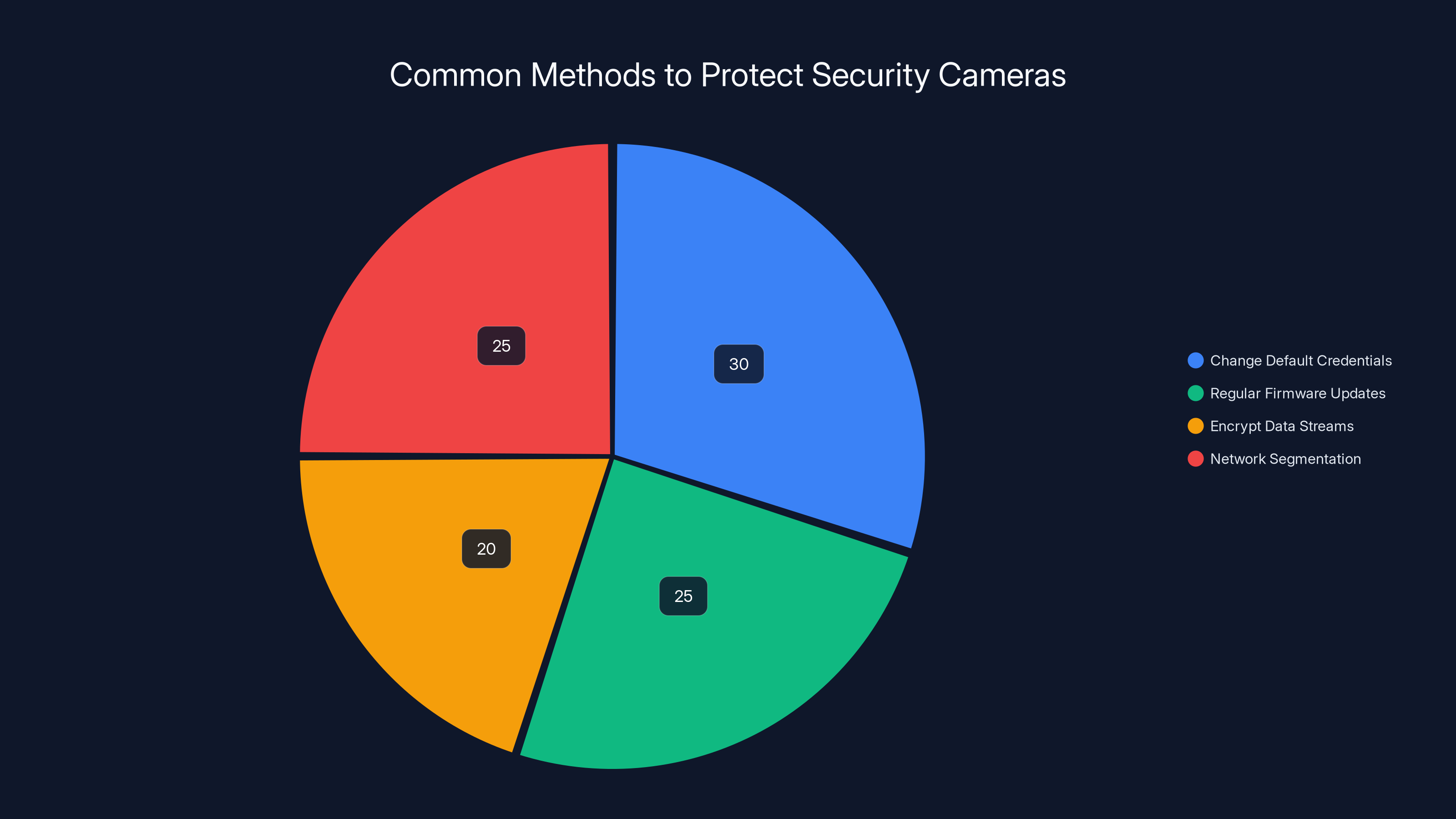
Changing default credentials and network segmentation are key methods, each accounting for about 25-30% of recommended security practices. Estimated data.
Technical Vulnerabilities in IoT Security Cameras
Most consumer-grade security cameras are designed with price and convenience in mind, often at the expense of security. Common vulnerabilities include:
- Default credentials: Many devices come with hardcoded usernames and passwords.
- Unencrypted data streams: Video feeds are often transmitted without encryption, making them easy to intercept.
- Lack of firmware updates: Manufacturers frequently fail to provide timely security patches.
Common Exploits Used in Camera Hacking
- Credential stuffing: Using stolen credentials to access camera systems.
- Exploiting software vulnerabilities: Attackers exploit unpatched software flaws.
- Man-in-the-middle attacks: Intercepting unencrypted data streams to eavesdrop on camera feeds.
Mitigation Strategies:
- Immediately change default credentials upon setup.
- Ensure all data transmissions are encrypted using protocols like TLS.
- Regularly update firmware and apply security patches.

Case Studies: Real-World Examples
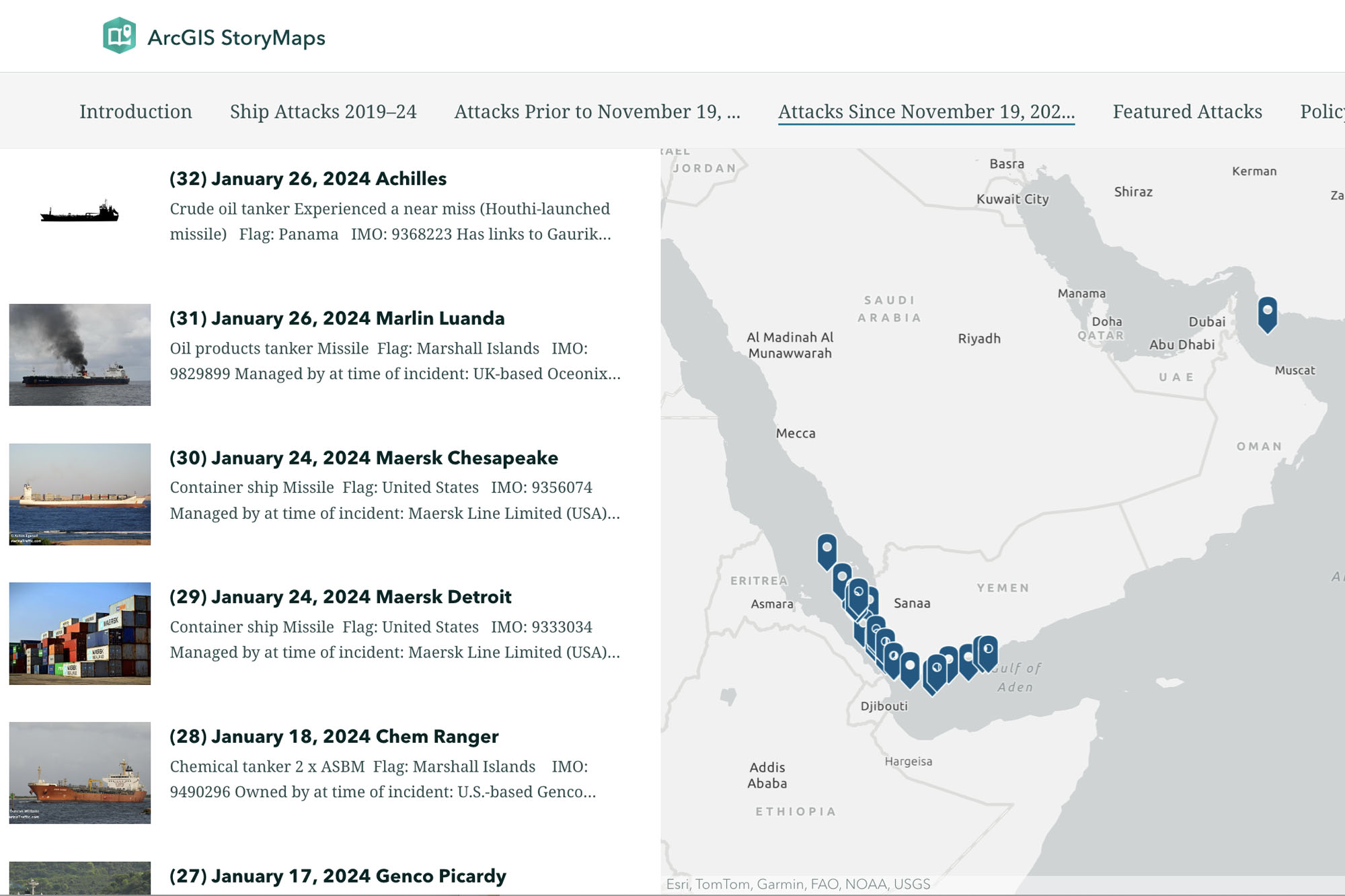
Ukraine: A Surveillance War
During the ongoing conflict in Ukraine, security cameras have been hacked to monitor troop movements and assess the impact of artillery strikes. These hacked feeds provide a tactical advantage by offering real-time intelligence.
Iran: Strategic Use of Surveillance
In Iran, state-sponsored hackers have targeted cameras to monitor potential military targets in Israel and other Middle Eastern countries. This strategy allows them to gather intelligence without deploying additional resources.
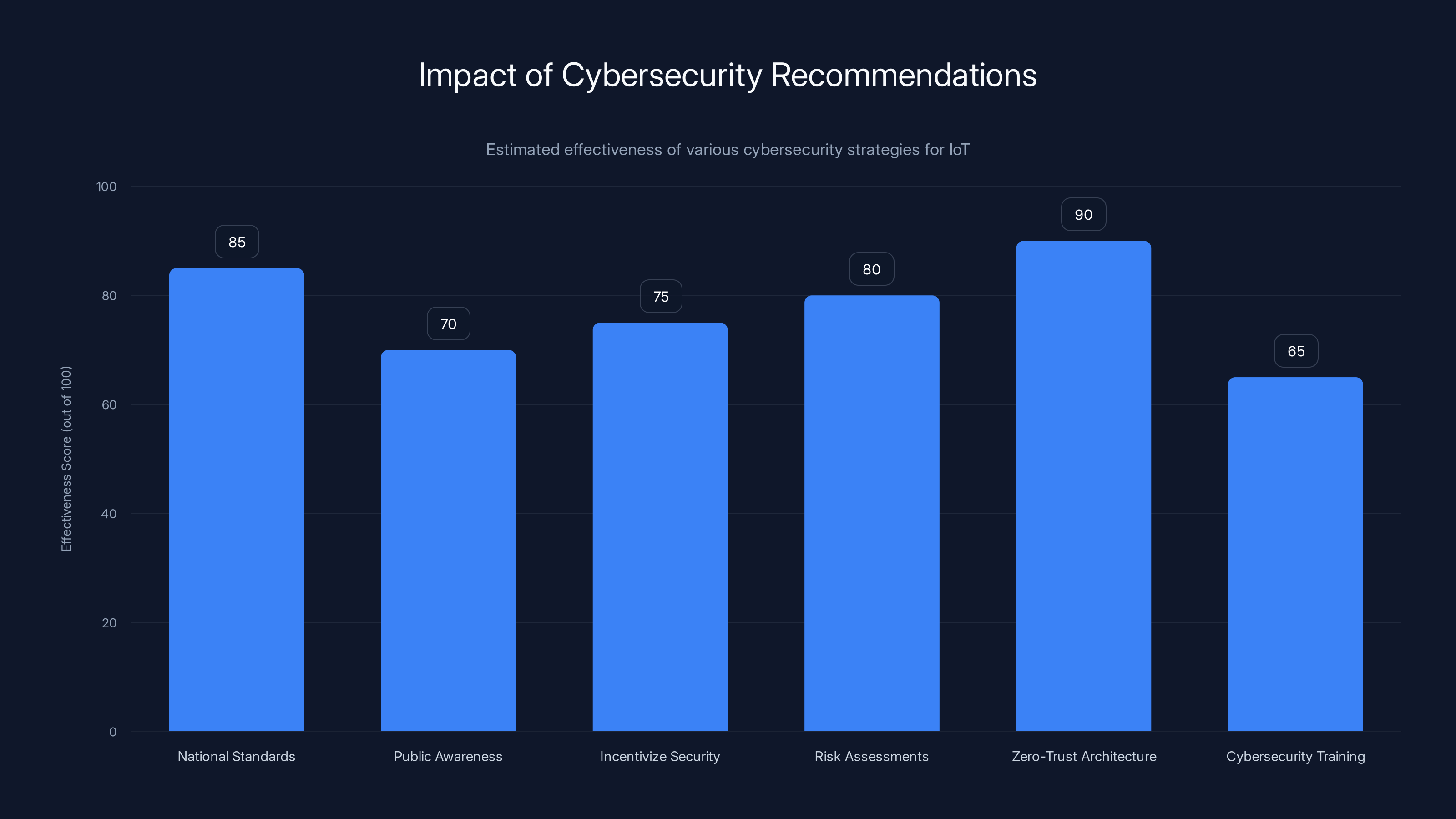
Estimated data shows that implementing a zero-trust architecture is perceived as the most effective strategy for enhancing IoT security, followed by establishing national standards.
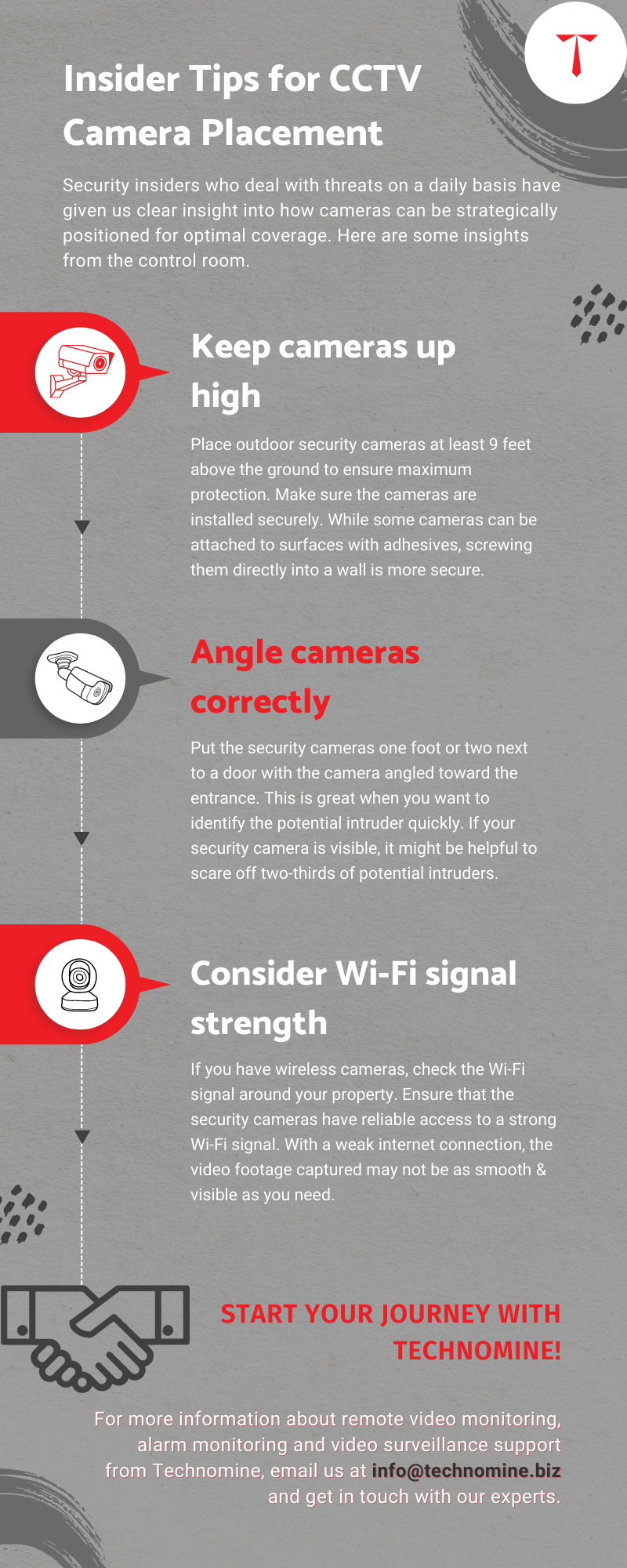
Practical Implementation Guides for Securing Cameras
Steps to Secure Your Security Cameras
- Change Default Settings: Alter default usernames and passwords immediately.
- Regular Firmware Updates: Schedule regular updates to ensure the latest security patches are applied.
- Encrypt Data Streams: Use encryption protocols like TLS to protect data in transit.
- Network Segmentation: Isolate camera networks from critical infrastructure to limit access.
- Monitor for Anomalies: Use intrusion detection systems to monitor for unusual activity.
Future Trends in Cyber Surveillance
The Evolution of IoT in Warfare
As IoT devices become more integrated into everyday life, their role in cyber warfare is likely to increase. Future conflicts may see more sophisticated attacks that leverage AI and machine learning to automate the hacking process.
Predicted Trends:
- AI-driven attacks: Automated systems will identify and exploit vulnerabilities faster than humans can.
- Integration with other systems: Hacked cameras may be used in conjunction with other hacked IoT devices to create comprehensive surveillance networks.
- Increased targeting of civilian infrastructure: As more devices are connected to the internet, the potential targets for hackers increase exponentially.

Recommendations for Policymakers and Organizations
Developing a Comprehensive Cybersecurity Framework
- National Standards: Establish national cybersecurity standards for IoT devices to ensure minimum security requirements are met.
- Public Awareness Campaigns: Educate consumers and businesses about the risks associated with insecure IoT devices.
- Incentivize Security Practices: Provide incentives for manufacturers to prioritize security in their design and development processes.
Best Practices for Organizations
- Conduct regular risk assessments: Identify potential vulnerabilities and develop mitigation strategies.
- Implement a zero-trust architecture: Assume all devices are potential threats and verify every access attempt.
- Invest in cybersecurity training: Ensure all employees are aware of best practices for maintaining security.
Conclusion
The integration of hacked security cameras into military strategy highlights the evolving nature of warfare in the digital age. As these devices become more prevalent, their role in cyber warfare will only grow. By understanding the vulnerabilities and implementing robust security measures, we can mitigate the risks and protect critical infrastructure from being exploited in conflicts.
FAQ
What makes security cameras appealing targets for hackers?
Security cameras provide real-time surveillance capabilities and are often poorly secured, making them easy targets for cyberattacks.
How can individuals and organizations protect their security cameras from being hacked?
By changing default credentials, ensuring regular firmware updates, encrypting data streams, and using network segmentation.
Why are state-sponsored actors interested in hacking security cameras?
These actors use hacked cameras to gather intelligence and monitor military targets without deploying additional resources.
What are the implications of increased IoT device hacking in warfare?
As IoT devices become more prevalent, their role in cyber warfare will grow, leading to more integrated and sophisticated attacks.
How can governments and organizations develop effective cybersecurity strategies?
By establishing national cybersecurity standards, conducting regular risk assessments, and implementing zero-trust architectures.
What future trends are expected in the realm of cyber surveillance?
AI-driven attacks, increased integration with other systems, and a rise in targeting civilian infrastructure are anticipated trends.
How do hacked security cameras provide a tactical advantage in conflicts?
They offer real-time intelligence on troop movements and military targets, providing a strategic edge in warfare situations.
What role do consumer-grade security cameras play in modern warfare?
These cameras serve as valuable assets for surveillance and reconnaissance, offering low-cost and readily available intelligence.
Key Takeaways
- Security cameras have become strategic assets in modern warfare.
- Cyberattacks on cameras are increasing due to state-sponsored groups.
- Many cameras lack basic security, making them vulnerable to hacks.
- Mitigating risks requires encryption and regular updates.
- Future trends indicate more integrated attacks with IoT proliferation.
- Governments need to establish national cybersecurity standards.
- AI-driven attacks will automate the exploitation of vulnerabilities.
- Zero-trust architectures are essential for robust cybersecurity.
Related Articles
- Understanding the IPVanish VPN Flaw: What It Means for Mac Users [2025]
- AI Agents Revolutionize VPN Connectivity: How ExpressVPN Is Changing the Game [2025]
- The Fall of LeakBase: Inside the Seizure of a Major Data Leak Forum [2025]
- LexisNexis Data Breach: What You Need to Know [2025]
- Massive Data Breach on French Medical Platform: Lessons and Future Implications [2025]
- Why Amazon.com is Experiencing Issues and Failing to Load Prices [2025]
![Hacking Security Cameras: A New Weapon in Modern Warfare [2025]](https://tryrunable.com/blog/hacking-security-cameras-a-new-weapon-in-modern-warfare-2025/image-1-1772798784650.jpg)



