GPT-5.5 vs Mythos: Unveiling the Real Cybersecurity Contenders [2025]
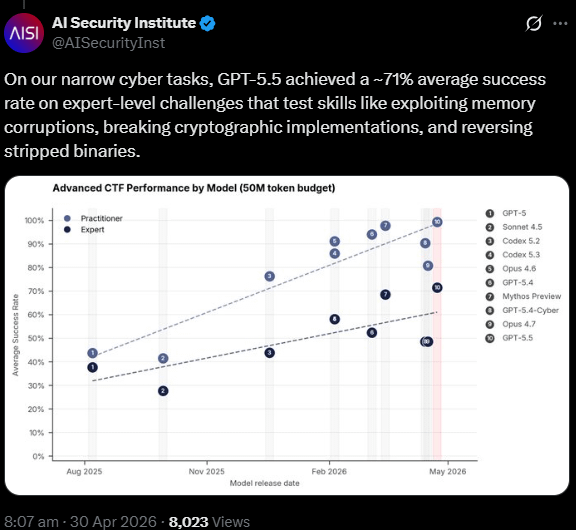
Last month, Anthropic's Mythos Preview model was heralded as a potential game-changer in the world of AI-driven cybersecurity. Yet, in a surprising twist, research from the UK's AI Security Institute (AISI) indicates that OpenAI's GPT-5.5 is equally potent in cybersecurity tasks. This revelation challenges preconceived notions about Mythos' capabilities and opens up a broader discussion on the current and future landscape of AI in cybersecurity.
TL; DR
- AI Match-Up: GPT-5.5 and Mythos performed similarly in cybersecurity tests, challenging the Mythos hype.
- Performance Metrics: GPT-5.5 excelled in 71.4% of expert-level tasks, slightly outdoing Mythos' 68.6%.
- Security Implications: Both models show potential in reverse engineering, web exploitation, and cryptography.
- Practical Applications: Explore how these AI models can enhance security measures for businesses.
- Future Outlook: AI's role in cybersecurity will expand, with emphasis on real-time threat detection and response.
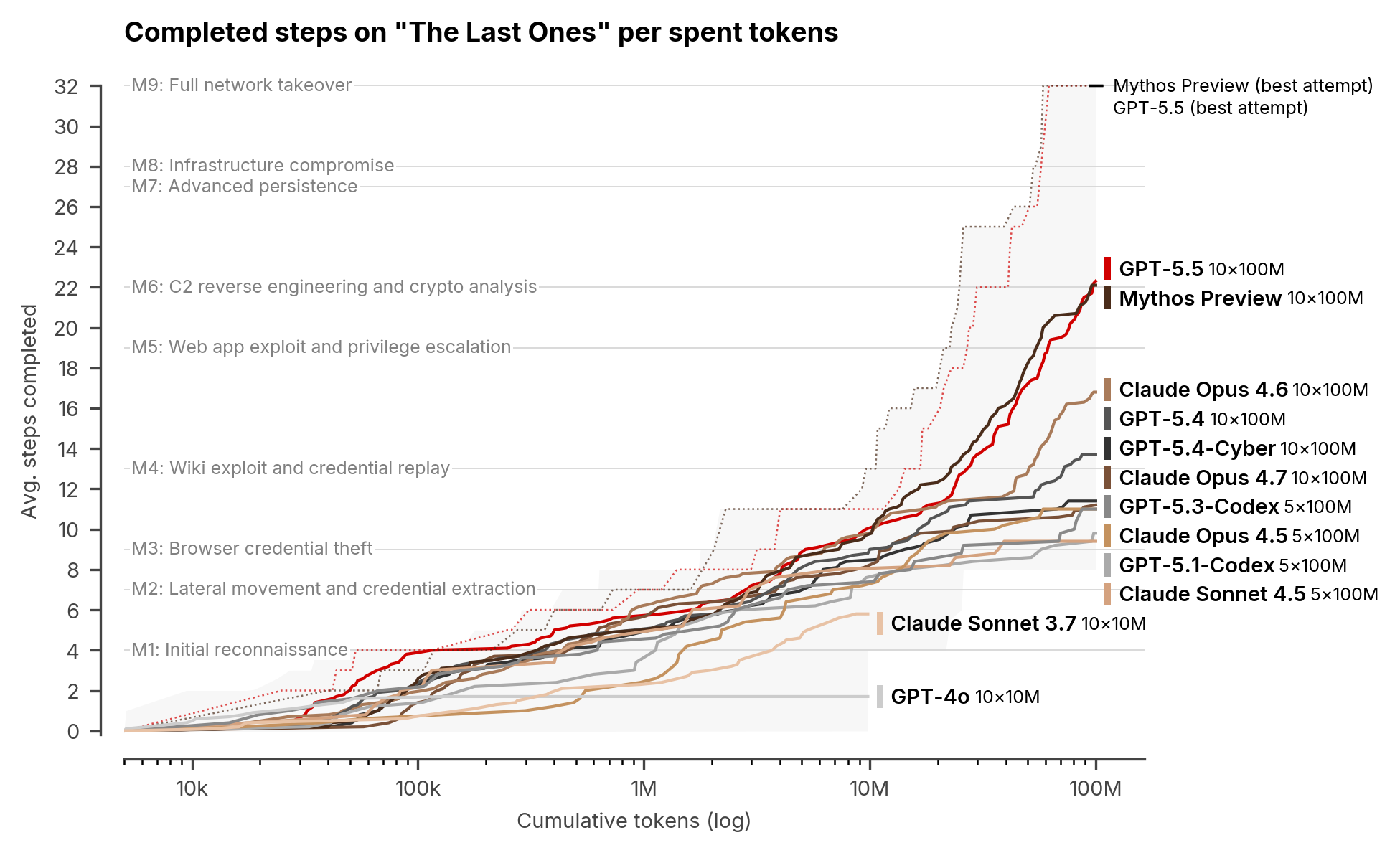
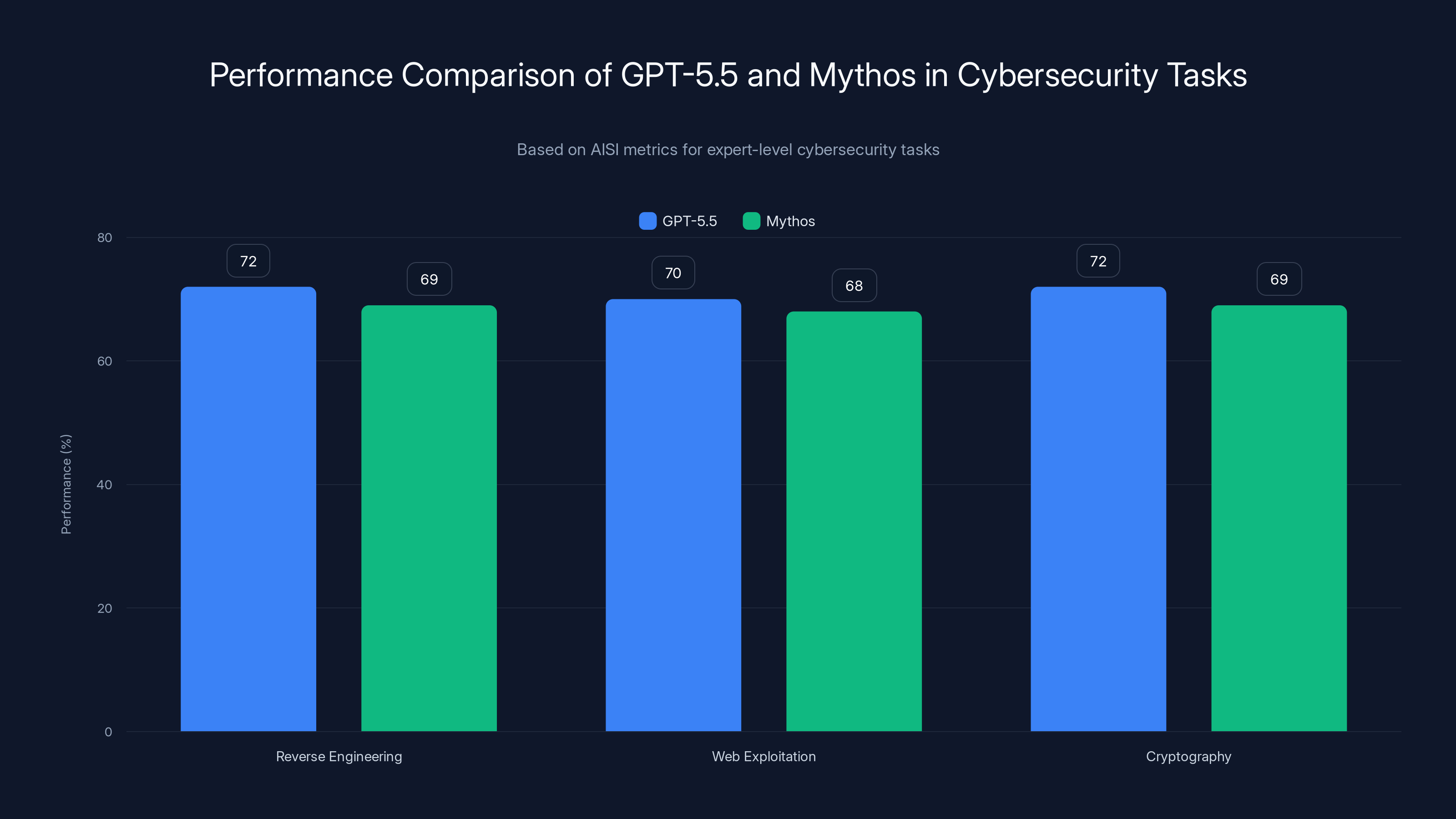
GPT-5.5 slightly outperforms Mythos in key cybersecurity tasks, excelling particularly in Reverse Engineering and Cryptography.
Understanding GPT-5.5 and Mythos in Cybersecurity
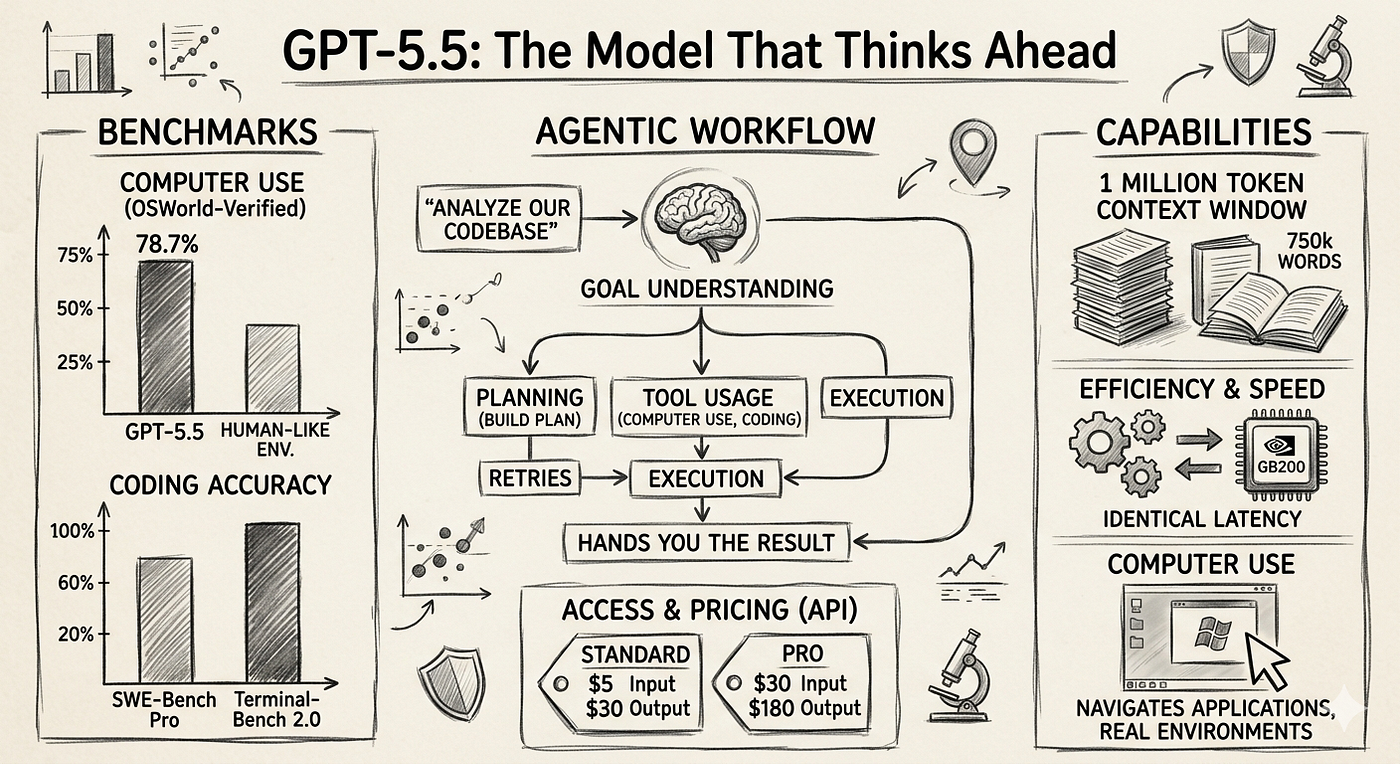
AI models like GPT-5.5 and Mythos are increasingly integral to cybersecurity efforts. These models leverage advanced machine learning techniques to analyze vast data sets, identify patterns, and predict potential threats. But how do they compare in practical applications?
The Core Technologies
GPT-5.5 utilizes transformer-based architectures, which allow it to process and understand complex patterns in textual data. This is particularly useful in detecting phishing attempts, analyzing malware code, and predicting cyber threats based on historical data.
Mythos, on the other hand, is built on a similar foundation but incorporates unique algorithms aimed at enhancing its predictive capabilities in cybersecurity. Its design focuses on threat analysis and mitigation, often touted as more specialized than general-purpose AI models.
Performance Metrics
According to AISI, GPT-5.5 excelled in 71.4% of expert-level tasks, slightly surpassing Mythos' 68.6%. These tasks included:
- Reverse Engineering: Understanding and deconstructing software to identify vulnerabilities.
- Web Exploitation: Detecting and preventing unauthorized access to web applications.
- Cryptography: Analyzing encrypted data to ensure its integrity and security.
Real-World Use Cases
In practical scenarios, both GPT-5.5 and Mythos can be employed to bolster cybersecurity measures:
- Automated Threat Detection: AI models can monitor network traffic in real-time, identifying anomalies that may indicate a security breach.
- Phishing Detection: By analyzing email content, AI can flag potentially harmful communications before they reach inboxes.
- Vulnerability Assessment: AI can scan software systems to identify and prioritize vulnerabilities for patching.
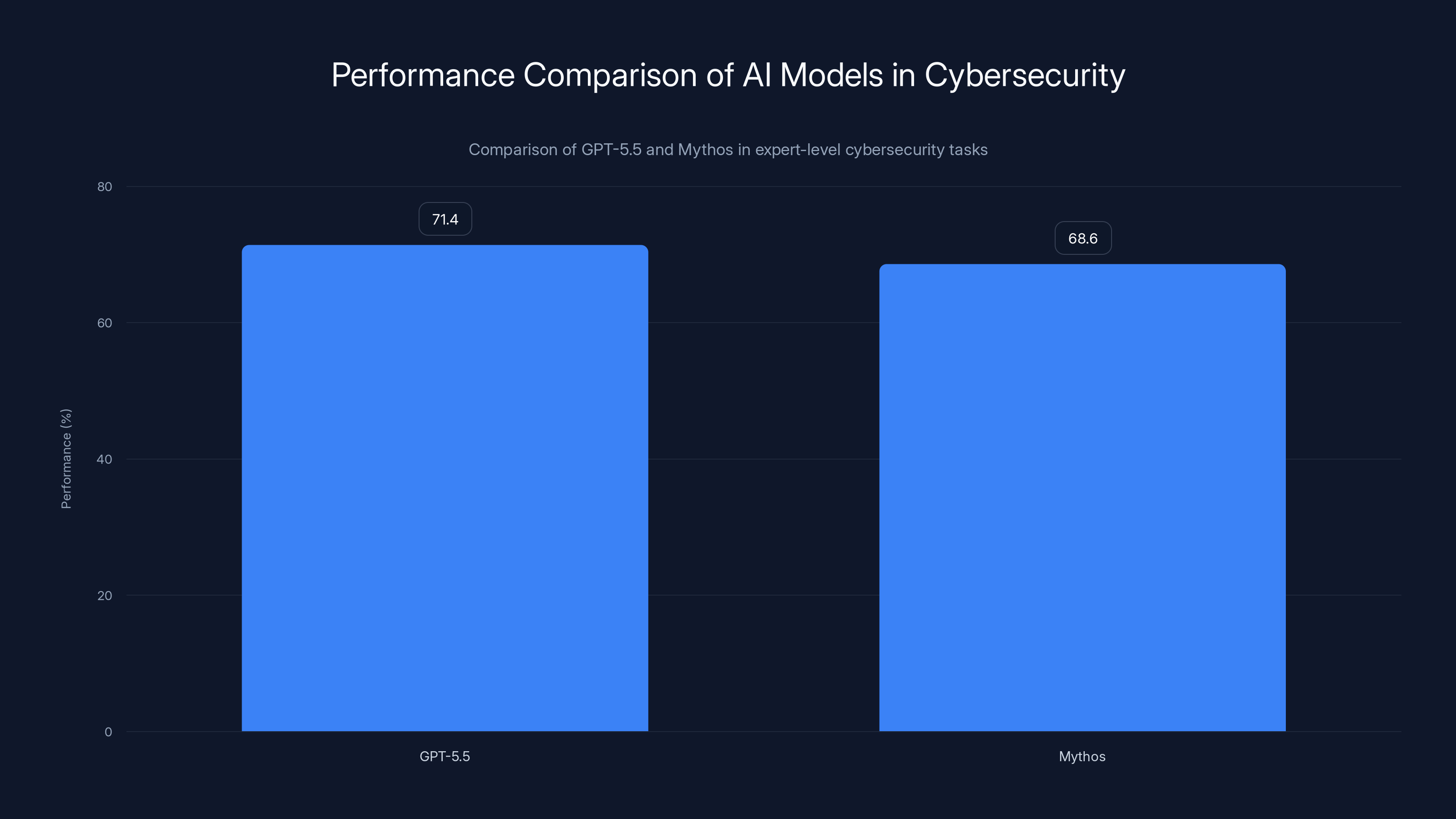
GPT-5.5 slightly outperformed Mythos in expert-level cybersecurity tasks with a 71.4% success rate compared to Mythos' 68.6%.
Implementation Guides for Businesses
Integrating AI models like GPT-5.5 into existing security frameworks requires a strategic approach. Here are steps businesses can take:
Step 1: Assess Current Security Posture
Begin by evaluating your existing security measures. Identify areas where AI can provide the most value, such as in threat detection or incident response.
Step 2: Choose the Right AI Model
Consider your specific needs when choosing between GPT-5.5 and Mythos. For general-purpose security, GPT-5.5 offers versatility, while Mythos may excel in targeted threat analysis.
Step 3: Integration and Testing
Work with IT and security teams to integrate the chosen AI model into your systems. Conduct thorough testing to ensure compatibility and effectiveness.
Step 4: Continuous Monitoring and Improvement
AI-driven cybersecurity is not a set-and-forget solution. Regularly monitor performance and update models to adapt to new threats.
[QUICK TIP: Regularly update AI models to keep pace with evolving cybersecurity threats.]
Common Pitfalls and Solutions
Pitfall 1: Over-Reliance on AI
While AI models are powerful, they are not infallible. Businesses should avoid placing blind trust in AI solutions without human oversight.
Solution:
Implement a hybrid approach, combining AI capabilities with human expertise to interpret and act on AI-generated insights.
Pitfall 2: Data Privacy Concerns
AI models require vast amounts of data, raising potential privacy issues.
Solution:
Ensure compliance with data protection regulations like GDPR by anonymizing data and implementing strict access controls.

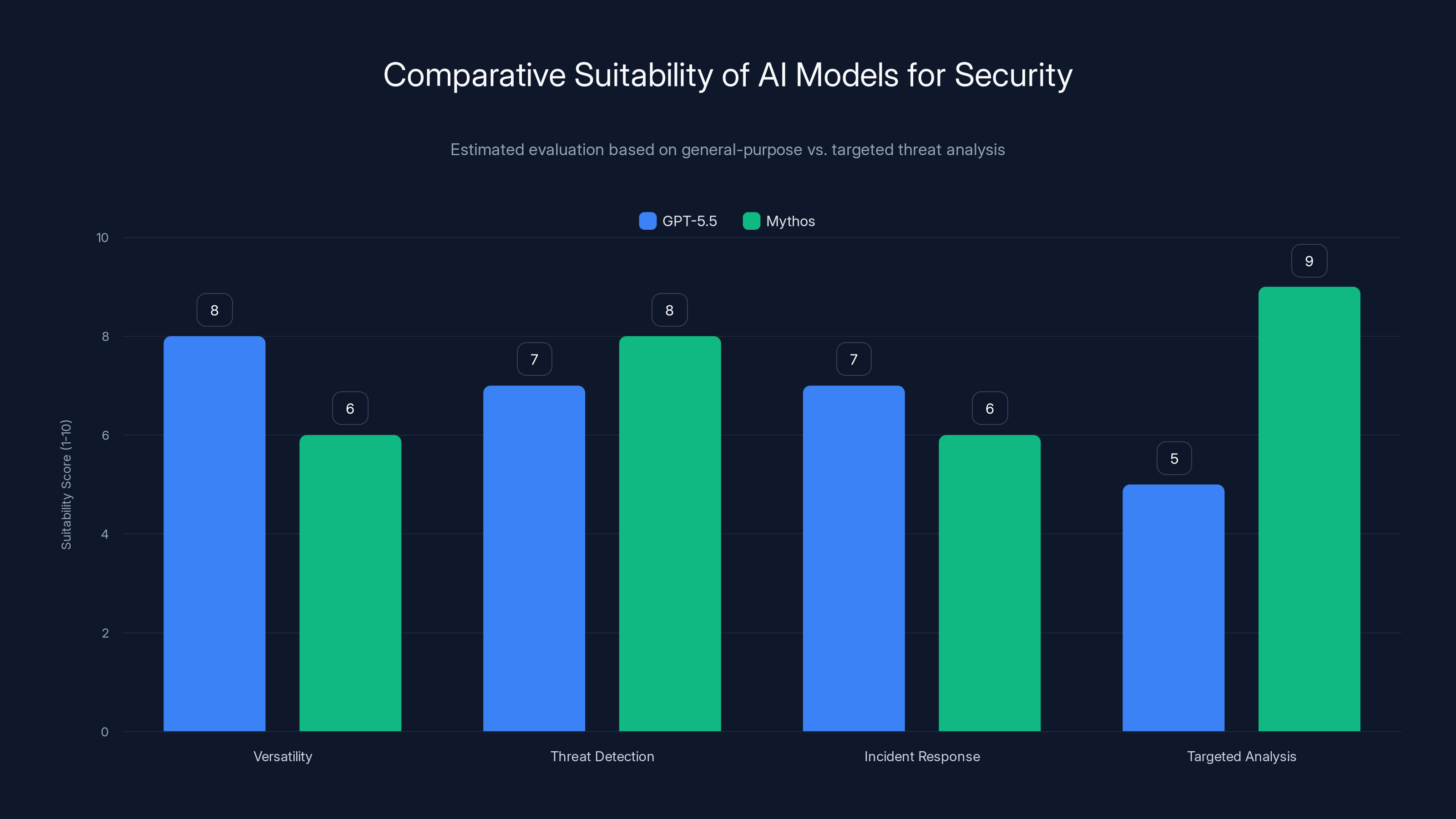
GPT-5.5 excels in versatility and incident response, while Mythos is stronger in threat detection and targeted analysis. Estimated data.
Future Trends in AI-Driven Cybersecurity
Real-Time Threat Detection
AI's ability to process data at lightning speed will enhance real-time threat detection, allowing businesses to respond to attacks as they occur.
Personalized Security Measures
AI will enable more personalized security strategies, adapting to the unique risk profile of each organization.
Collaboration Between AI Models
Future AI solutions might involve collaboration between different models, combining their strengths for more comprehensive security coverage.
DID YOU KNOW: AI-driven cybersecurity solutions can reduce incident response times by up to 50%?

Recommendations for Businesses
- Stay Informed: Keep abreast of developments in AI and cybersecurity to make informed decisions.
- Invest in Training: Equip your team with the skills needed to leverage AI tools effectively.
- Collaborate with Experts: Partner with cybersecurity experts to design robust AI-driven security strategies.
- Evaluate Regularly: Continually assess the effectiveness of AI solutions and make adjustments as needed.
[QUICK TIP: Partner with cybersecurity firms to gain insights into the latest AI trends and tools.]
Conclusion
The landscape of AI in cybersecurity is rapidly evolving. Both GPT-5.5 and Mythos represent significant advancements, each with its strengths and potential applications. As businesses navigate the complexities of cybersecurity, leveraging these AI tools will be crucial in staying ahead of threats. By understanding their capabilities and limitations, organizations can implement effective strategies that protect their assets and maintain trust.
FAQ
What is GPT-5.5?
GPT-5.5 is an advanced AI model developed by OpenAI, designed to perform complex tasks, including cybersecurity applications, by analyzing patterns in data and predicting potential threats.
How does Mythos differ from GPT-5.5?
Mythos is tailored specifically for cybersecurity tasks, emphasizing threat analysis and mitigation, whereas GPT-5.5 is a more general-purpose model with broad applications across various domains.
What are the benefits of using AI in cybersecurity?
AI enhances threat detection, reduces response times, and provides predictive insights to prevent potential attacks. It allows for more efficient monitoring and analysis of security data.
How can businesses integrate AI into their cybersecurity strategies?
Businesses should assess their security needs, select the appropriate AI model, integrate it with existing systems, and continuously monitor and update the model to adapt to new threats.
What are the potential risks of AI in cybersecurity?
Key risks include over-reliance on AI without human oversight, data privacy concerns, and the need for continuous updates to keep pace with evolving threats.
How will AI-driven cybersecurity evolve in the future?
AI will enable real-time threat detection, personalized security measures, and collaboration between different AI models for comprehensive coverage, enhancing overall security posture.
Key Takeaways
- GPT-5.5 and Mythos perform similarly in cybersecurity contexts.
- AI models excel in tasks like reverse engineering and web exploitation.
- Integrating AI into security frameworks requires strategic planning.
- AI enhances real-time threat detection and response capabilities.
- Future AI trends include personalized security and model collaboration.
Related Articles
- The Emergence and Evolution of Credit Card-Sized E-Readers [2025]
- How AI Tools Have Made Vulnerability Exploitation Faster and Easier [2025]
- Top Tech of the Month: The Best New Gadgets We've Tested for May 2026
- Why Encryption Breaking is 20x Cheaper and What CEOs Need to Do [2025]
- Apple's Record Sales Amidst Leadership Change and Looming Chip Shortage [2025]
- How Hackers Exploit Trusted Email Platforms and What You Can Do [2025]
![GPT-5.5 vs Mythos: Unveiling the Real Cybersecurity Contenders [2025]](https://tryrunable.com/blog/gpt-5-5-vs-mythos-unveiling-the-real-cybersecurity-contender/image-1-1777651439155.jpg)



