Why Encryption Breaking is 20x Cheaper and What CEOs Need to Do [2025]
Advancements in quantum computing and increased access to powerful hardware have made breaking encryption significantly more affordable. For CEOs, this shift presents a massive security challenge that demands immediate attention.
TL; DR
- Encryption-breaking technology is now 20x cheaper, increasing cybersecurity risks, as highlighted in a TechRadar report.
- Quantum computing enables rapid decryption of previously secure data, according to NVIDIA's recent announcements.
- CEOs must prioritize updating encryption protocols to stay ahead of these developments.
- Investment in quantum-resistant encryption is essential, as discussed in The Quantum Insider's analysis.
- Ongoing employee training can mitigate human error risks, a point emphasized in Nexford University's insights.

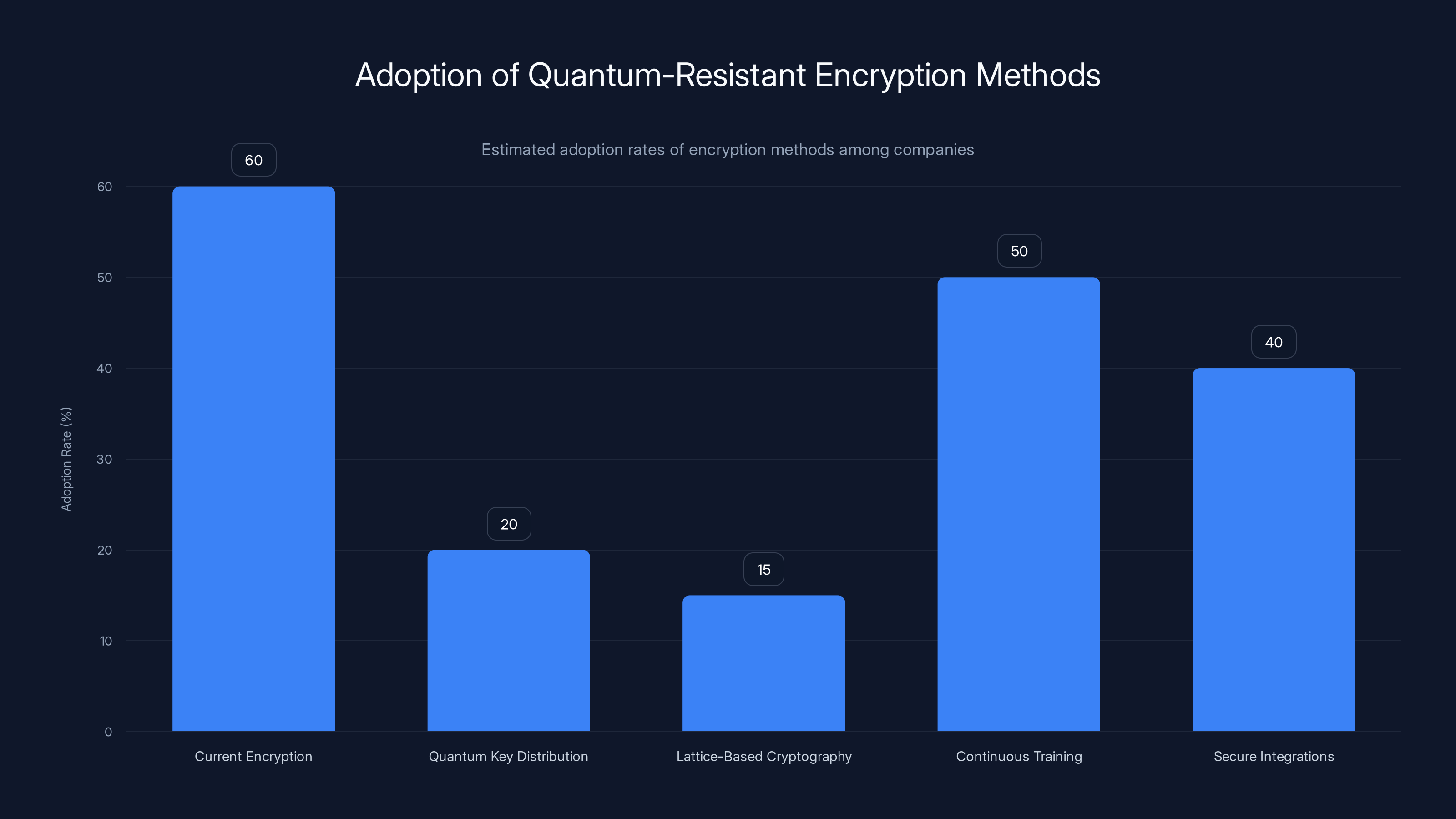
Current encryption methods are still predominant, but there's growing interest in quantum-resistant technologies like QKD and lattice-based cryptography. Continuous training and secure integrations are also gaining traction. (Estimated data)
Understanding the Shift in Encryption Breaking
Encryption has long been the backbone of data security, ensuring that sensitive information remains confidential. However, recent technological advancements have drastically reduced the cost of breaking encryption.
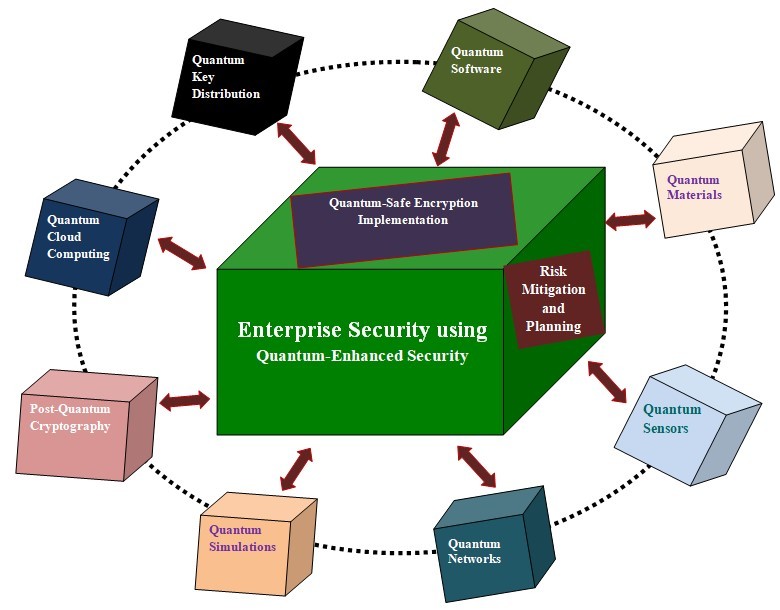
Quantum Computing's Role: Quantum computers can perform complex calculations at unprecedented speeds. Algorithms like Shor's algorithm can factor large numbers exponentially faster than classical computers, making traditional encryption vulnerable, as explained in The Quantum Insider's guide.
Accessible Hardware: The decline in hardware costs means more entities can access the computing power needed to break encryption. This democratization of technology poses a significant threat to data security, as noted by Capital Analytics Associates.
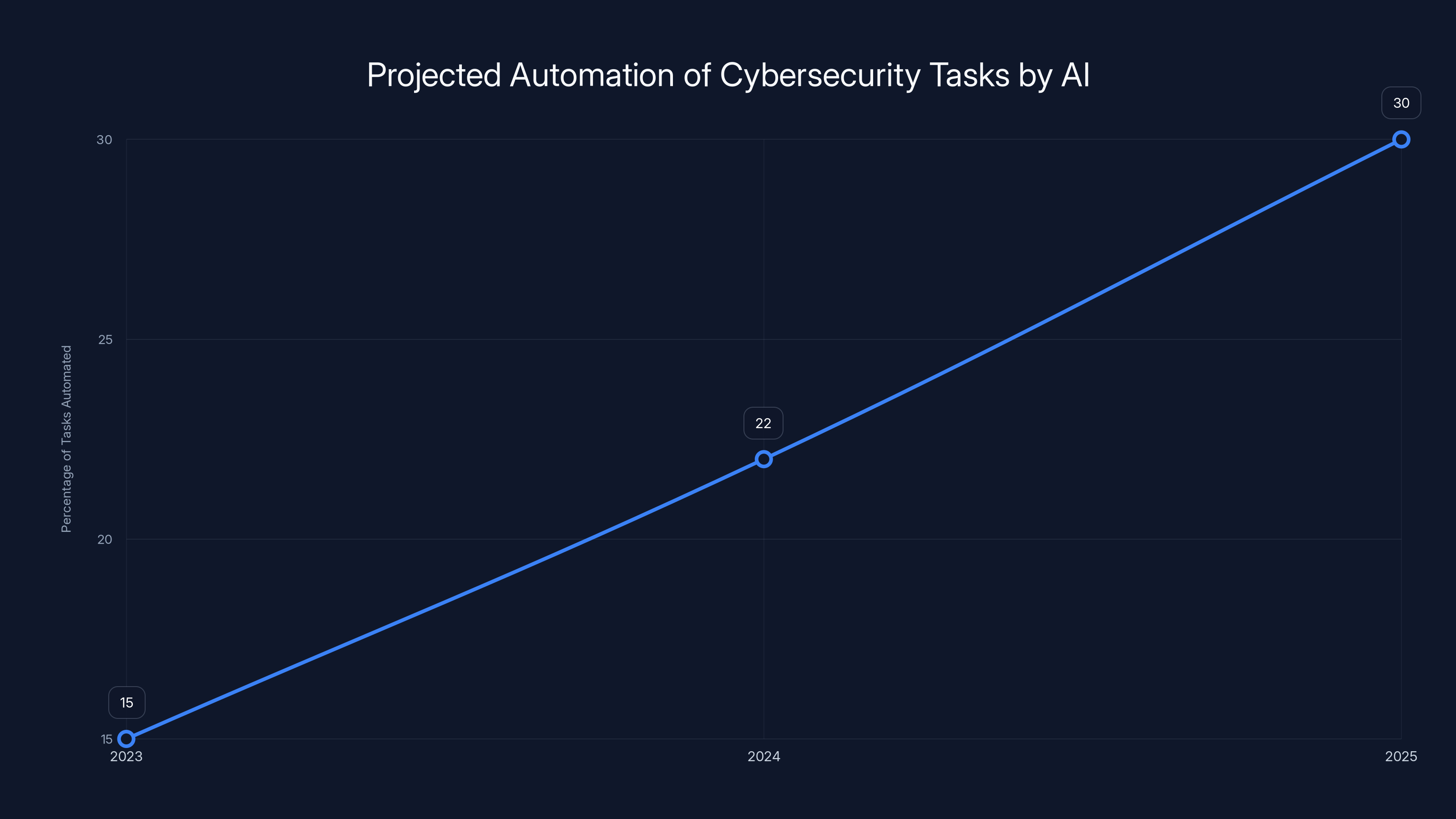
AI is projected to automate 30% of cybersecurity tasks by 2025, significantly reducing manual intervention. Estimated data.
The Mechanics of Encryption Breaking
How Encryption Works
Encryption converts data into a secure format using algorithms and keys. Only those with the correct key can decrypt the data. This process ensures that even intercepted data remains unreadable.
Breaking Encryption
Breaking encryption involves calculating the key used to encrypt the data. Quantum computing's ability to process vast amounts of data quickly makes this process feasible, as detailed in Data Innovation's report.

Real-World Implications for Businesses
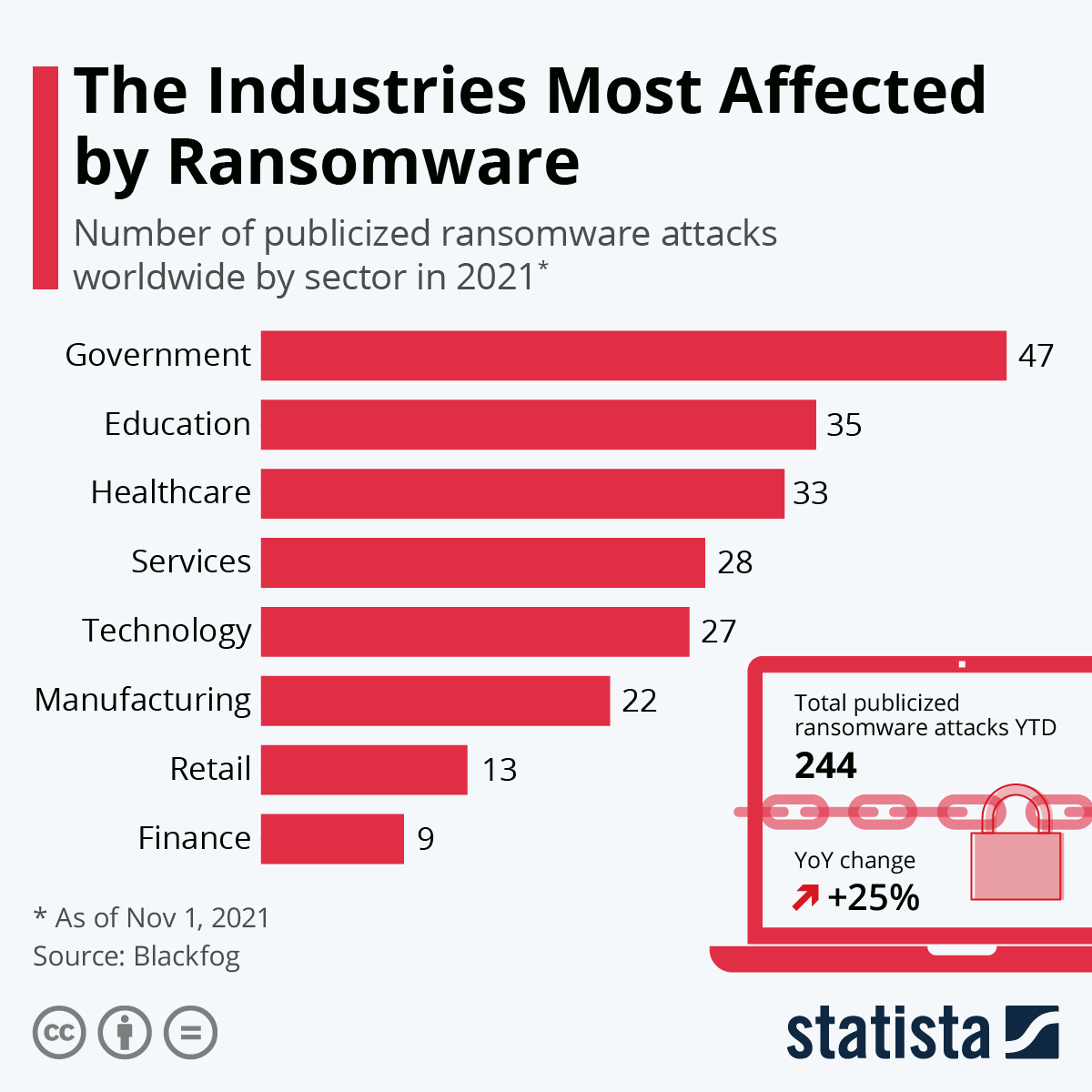
Financial Sector
Banks rely heavily on encryption for online transactions and customer data protection. With cheaper encryption-breaking technology, financial institutions face heightened risks of fraud and data breaches, as reported by Fortune Business Insights.
Healthcare
Healthcare providers store sensitive patient information electronically. A breach could compromise patient privacy and lead to costly legal battles, as seen in the Kettering Health ransomware attack.
Government
Governments store confidential information that, if leaked, could have national security implications. Thus, upgrading encryption protocols is critical, as emphasized in Mayer Brown's publication.
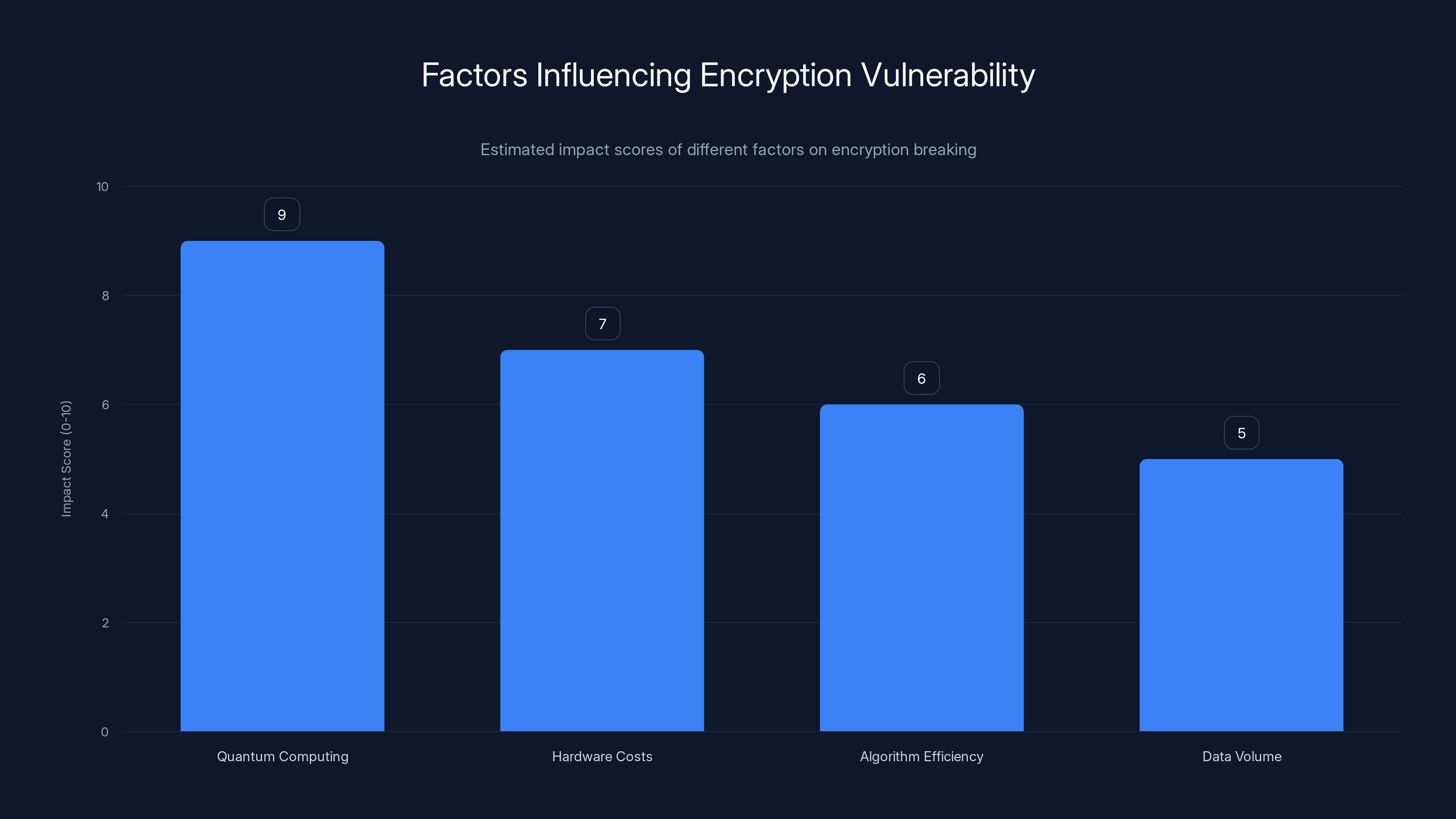
Quantum computing has the highest impact on encryption vulnerability, followed by reduced hardware costs. Estimated data based on technological trends.
Best Practices for CEOs
1. Assess Current Encryption Standards
Evaluate existing encryption methods and identify vulnerabilities. Transitioning to quantum-resistant algorithms should be a priority, as suggested by The Quantum Insider.
2. Invest in Quantum-Resistant Encryption
Quantum Key Distribution (QKD): This method uses quantum mechanics to secure data, making it nearly impossible to intercept without detection, as outlined in The Quantum Insider's analysis.
Lattice-Based Cryptography: This approach is believed to be resistant to quantum attacks and provides a viable alternative to current methods, as noted in The Quantum Insider's report.
3. Continuous Employee Training
Human error is a significant factor in data breaches. Regular training on cybersecurity best practices can reduce these risks, as emphasized by Nexford University.
4. Secure Third-Party Integrations
Businesses often rely on third-party services that may not have robust encryption. Ensure all partners adhere to high security standards, as recommended by Capital Analytics Associates.
5. Monitor and Adapt
Stay informed about the latest encryption-breaking advancements and adjust strategies accordingly, as advised by Data Innovation.
Common Pitfalls and Solutions
Overreliance on Outdated Encryption
Pitfall: Many companies continue using encryption methods that are no longer secure.
Solution: Regular audits and updates to encryption technologies can mitigate this risk, as suggested by The Quantum Insider.
Neglecting Insider Threats
Pitfall: Focusing solely on external threats can overlook the danger posed by insiders.
Solution: Implement strict access controls and monitor employee activity, as recommended by Mayer Brown.

Future Trends in Encryption and Security
Quantum Computing
As quantum computing becomes more mainstream, expect further reductions in encryption-breaking costs. Companies need to stay ahead of these developments, as noted by The Quantum Insider.
AI-Powered Security Systems
AI can detect anomalies and potential breaches faster than human analysts, offering a proactive approach to security, as highlighted in Data Innovation's report.

Conclusion
The decreasing cost of encryption-breaking technology is a wake-up call for CEOs. By understanding the risks and implementing robust security measures, businesses can protect their sensitive data and maintain trust, as emphasized by TechRadar.
FAQ
What is the role of quantum computing in encryption breaking?
Quantum computing can solve complex algorithms much faster than classical computers, making it possible to break traditional encryption methods, as explained in The Quantum Insider's guide.
How can businesses protect themselves from quantum threats?
Invest in quantum-resistant encryption techniques like Quantum Key Distribution (QKD) and Lattice-Based Cryptography, as recommended by The Quantum Insider.
Why are employee training programs crucial?
Training programs reduce the risk of human error, which is a significant factor in data breaches, as highlighted by Nexford University.
What sectors are most at risk from cheaper encryption-breaking technology?
Financial, healthcare, and government sectors face significant risks due to the sensitive nature of the data they handle, as reported by Fortune Business Insights.
How often should encryption protocols be reviewed?
Ideally, encryption protocols should be reviewed annually or whenever significant technological advancements occur, as advised by Data Innovation.
What are the benefits of AI in cybersecurity?
AI can quickly detect and respond to security threats, offering a more proactive defense against potential breaches, as noted in Data Innovation's report.
Key Takeaways
- Encryption-breaking technology is now 20x cheaper, increasing cybersecurity risks, as highlighted by TechRadar.
- Quantum computing enables rapid decryption of previously secure data, as noted by NVIDIA.
- CEOs must prioritize updating encryption protocols to stay ahead.
- Investment in quantum-resistant encryption is essential, as discussed in The Quantum Insider.
- Ongoing employee training can mitigate human error risks, as emphasized by Nexford University.
- AI can automate 30% of cybersecurity tasks by 2025, as reported by Data Innovation.
- Regular audits and updates to encryption technologies are crucial, as suggested by The Quantum Insider.
- Secure third-party integrations are vital for overall cybersecurity, as recommended by Capital Analytics Associates.
Related Articles
- Understanding Cybersecurity Threats in the Medical Sector: Lessons from Recent Breaches [2025]
- How Hackers Exploit Trusted Email Platforms and What You Can Do [2025]
- VECT: The Ransomware That's Secretly Destroying Your Data [2025]
- Understanding the Threat: Attack of the Killer Script Kiddies [2025]
- The Rise of Taylor Swift Deepfakes: Exploring the Impact and Mitigation Strategies [2025]
- GitHub's Race Against Time: Fixing a Critical Vulnerability in Record Time [2025]
![Why Encryption Breaking is 20x Cheaper and What CEOs Need to Do [2025]](https://tryrunable.com/blog/why-encryption-breaking-is-20x-cheaper-and-what-ceos-need-to/image-1-1777624442877.jpg)




