Hackers Are Turning to Easy, Fast AI Solutions to Roll Out Attacks: How to Keep Your Business Safe [2025]
Last Monday, a cybersecurity analyst at a major financial firm spotted an anomaly: a flurry of phishing emails that seemed too polished for the hacker's usual MO. They weren't more sophisticated in design but were disarmingly efficient in how quickly they spread. After a deep dive, the culprit was revealed—not a new hacker group or a novel virus, but an AI tool. This revelation is part of a growing trend: hackers are leveraging AI to expedite their attacks, prioritizing speed and volume over complexity, as noted by Infosecurity Magazine.
TL; DR
- Hackers use AI for rapid attack deployment, sacrificing sophistication for speed.
- AI-generated phishing and malware are becoming more common and harder to detect, according to Fortune Business Insights.
- Businesses need proactive defenses: AI-driven threat detection is crucial.
- Employee training and awareness are essential in preventing AI-based attacks.
- The future of cybersecurity will involve more AI, both for attackers and defenders.


AI-driven strategies like Threat Intelligence Platforms and Automated Incident Response are highly effective in enhancing cybersecurity. Estimated data.
The Rise of AI in Cybercrime
Why Hackers Love AI
AI isn't just for creating art or driving cars anymore; it's become a tool for hackers looking to accelerate their attack strategies. By using generative AI, cybercriminals can automate the creation of phishing emails, generate convincing fake identities, and even craft complex malware—all with minimal human intervention, as highlighted by the World Economic Forum.
The Mechanics of AI-Powered Attacks
Hackers use AI to automate tasks that traditionally required human input. For example, consider a phishing campaign. An AI can generate thousands of unique emails, each with slight variations in wording or design, making them harder for traditional spam filters to catch. Similarly, AI can create polymorphic malware that changes its code to avoid detection by antivirus software, as discussed in Forbes.
Case Study: AI in Action
In a recent incident involving a telecommunications company, hackers used AI to generate deepfake audio clips of the CEO. These clips were used to authorize fraudulent transactions, causing significant financial losses before the scheme was uncovered, as reported by Santa Fe New Mexican.
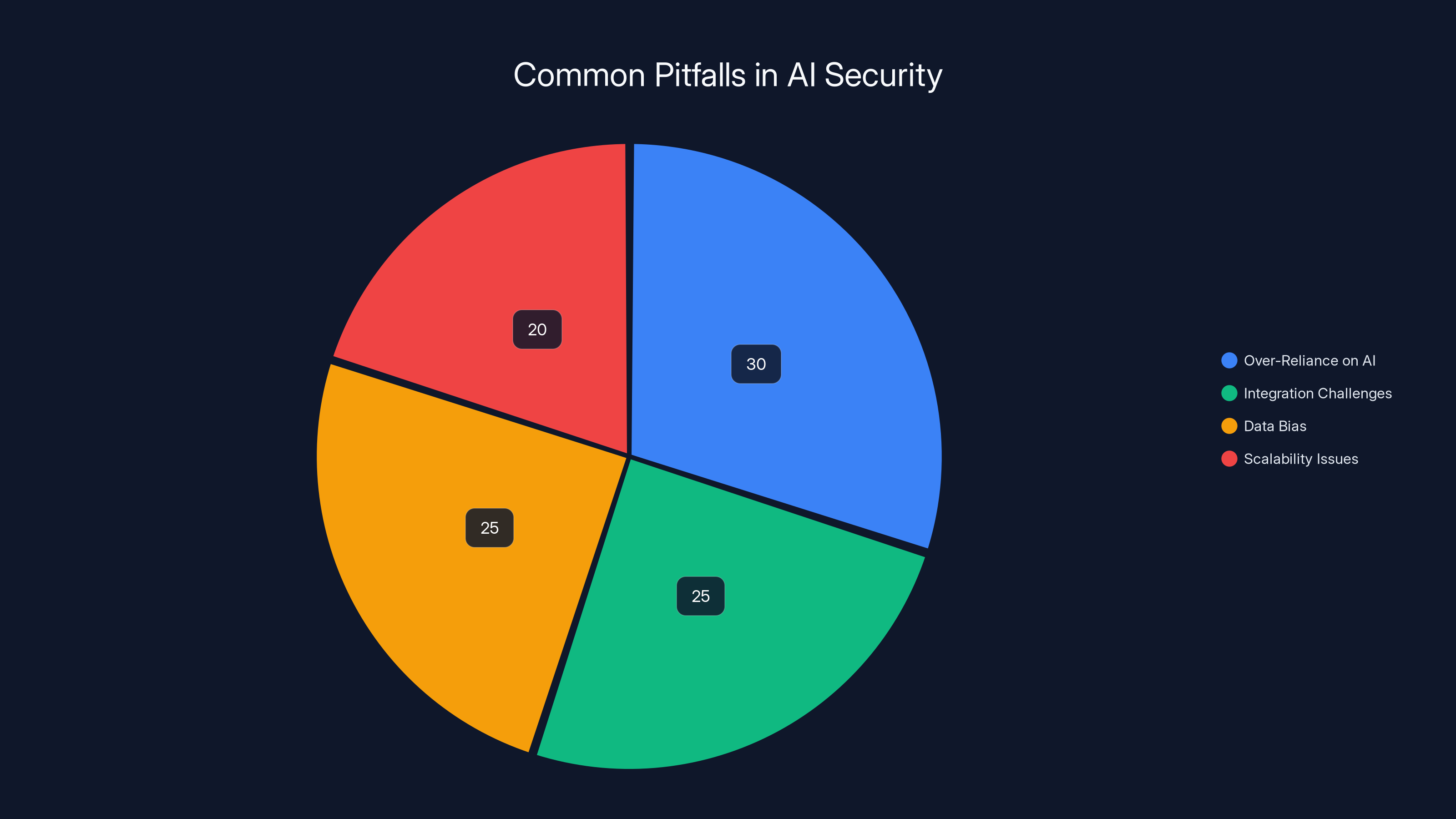
Over-reliance on AI and integration challenges are significant pitfalls in AI security, each contributing to about a quarter of the issues. Estimated data.
How AI-Driven Attacks Bypass Traditional Defenses
The Limitations of Conventional Cybersecurity
Traditional cybersecurity defenses often rely on recognizing known threats. However, AI can generate new, previously unseen threats at a speed that outpaces the development of defense mechanisms, as explained by ET Edge Insights.
The Role of Machine Learning
Machine learning helps AI understand and predict patterns. Hackers use this to analyze network traffic and identify vulnerabilities, adapting their attacks in real-time to exploit these weaknesses, as noted by Nokia.
Example: A machine learning model could be trained to recognize common security protocols and adjust its attack methods to bypass them.

Strategies for Protecting Your Business
Proactive Threat Detection with AI
To combat AI-powered threats, businesses must employ AI in their defenses. AI-driven security systems can analyze vast amounts of data in real-time, identifying anomalies that could indicate a breach, as highlighted by AWS.
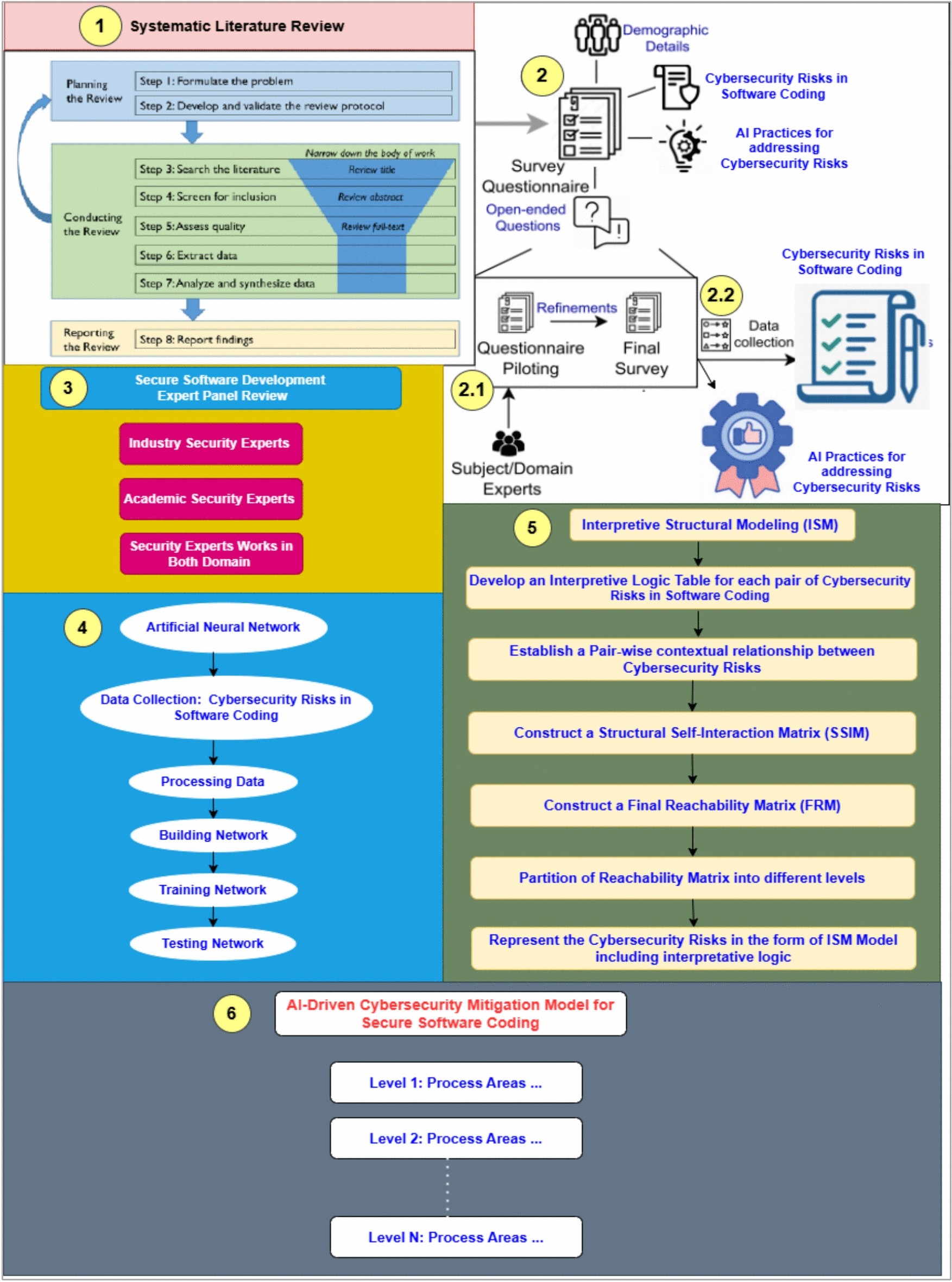
Implementing AI in Cybersecurity
- Automated Incident Response: Use AI to automate responses to detected threats, reducing the time between detection and mitigation.
- Behavioral Analytics: Monitor user behavior to identify deviations that could indicate compromised credentials.
- Threat Intelligence Platforms: Leverage AI to gather and analyze global threat data, improving anticipatory defenses, as discussed by Cybersecurity Insiders.
Training Your Team
Human error remains a significant vulnerability. Regular training sessions can help employees recognize phishing attempts and other AI-generated threats.
Training Best Practices:
- Conduct phishing simulations to test employee awareness.
- Provide clear guidelines on identifying and reporting suspicious activities.
- Encourage a culture of vigilance and continuous learning.

AI significantly enhances threat detection and response time, offering high impact ratings in cybersecurity. Estimated data.
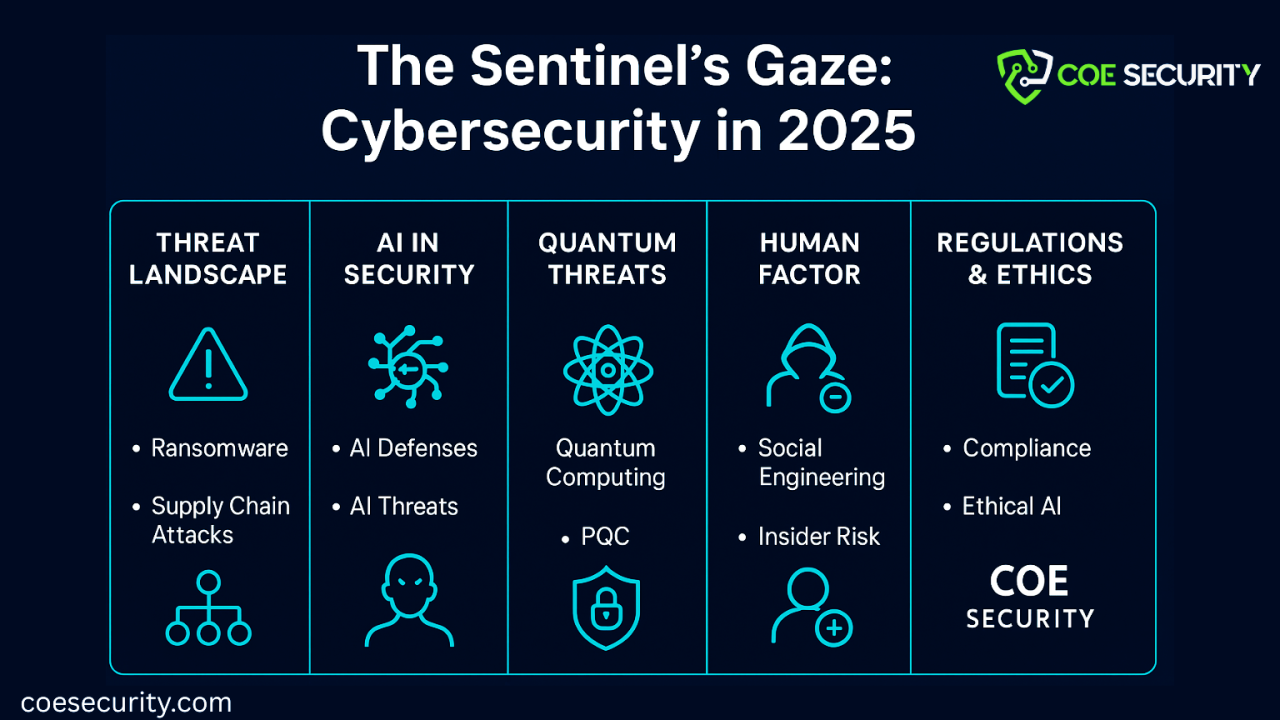
The Future of Cybersecurity: AI on Both Sides
The Arms Race of AI
As both attackers and defenders adopt AI, the cybersecurity landscape is becoming an AI arms race. Companies must be prepared to invest in AI research and development to stay ahead of cybercriminals, as emphasized by NVIDIA.
Emerging Technologies
- Quantum Computing: Could potentially break traditional encryption methods, requiring new security protocols.
- Blockchain: Offers opportunities for secure data exchange and identity verification.

Common Pitfalls in AI Security
Over-Reliance on AI
While AI can enhance cybersecurity, it shouldn't replace human oversight. AI systems are only as good as the data they are trained on, and biases or errors in this data can lead to security gaps, as discussed by Stimson Center.
Integration Challenges
Integrating AI into existing IT infrastructure can be complex. Companies must ensure compatibility and scalability to maximize AI's potential, as noted by Wiz.

Practical Implementation Guide: Setting Up AI-Driven Security
Step-by-Step Guide
- Assess Your Current Security Posture: Identify existing vulnerabilities and areas for improvement.
- Choose the Right AI Tools: Evaluate AI security solutions based on your specific needs and budget.
- Pilot and Test: Implement AI solutions on a small scale to test effectiveness and integration.
- Monitor and Adjust: Continuously monitor AI systems and adjust algorithms based on performance and emerging threats.

Conclusion: Staying Ahead in the AI Era
The integration of AI into cybercrime is a double-edged sword. While it offers hackers unprecedented speed and efficiency, it also provides businesses with powerful tools to defend against these threats. By understanding the mechanics of AI-driven attacks and implementing robust, AI-enhanced security measures, businesses can safeguard their digital assets in this rapidly evolving landscape, as highlighted by the World Economic Forum.
Use Case: Automate your security reports with Runable's AI-powered platform, saving time and enhancing accuracy.
Try Runable For Free
FAQ
What is AI in cybercrime?
AI in cybercrime refers to the use of artificial intelligence technologies by hackers to automate and enhance the effectiveness of their attacks. This includes generating phishing emails, creating deepfake content, and developing sophisticated malware, as explained by Cybersecurity Insiders.
How does AI improve cyber attacks?
AI improves cyber attacks by automating the creation of convincing phishing emails, adapting malware to bypass security systems, and analyzing large datasets to identify vulnerabilities, as noted by Infosecurity Magazine.
What are the benefits of using AI in cybersecurity?
AI in cybersecurity offers real-time threat detection, automated incident response, and predictive analytics to anticipate and mitigate potential attacks before they occur, as highlighted by NVIDIA.
How can businesses protect against AI-driven attacks?
Businesses can protect against AI-driven attacks by implementing AI-powered security systems, conducting regular employee training, and staying updated with the latest threat intelligence, as discussed by ET Edge Insights.
What are the challenges of integrating AI in cybersecurity?
Challenges include over-reliance on AI, potential integration issues with existing systems, and the need for continuous monitoring and updating of AI models, as noted by Stimson Center.
What is the future of AI in cybersecurity?
The future of AI in cybersecurity involves an arms race between hackers and defenders, with emerging technologies like quantum computing and blockchain playing significant roles in shaping security strategies, as emphasized by the World Economic Forum.
Key Takeaways
- Hackers utilize AI for fast, scalable attack deployment.
- AI-generated phishing and malware are increasingly common.
- Businesses must employ proactive AI-driven threat detection.
- Employee training is crucial in preventing AI-based attacks.
- The cybersecurity landscape is becoming an AI arms race.
Related Articles
- The Impact of Highguard's Shutdown: Navigating the Transition for Businesses [2025]
- The Ultimate Guide to Apple iPhone 17e Preorders: Unlocking the Best Discounts and Deals [2025]
- Navigating AI Dependencies: Lessons from the Pentagon Vendor Cutoff [2025]
- Shark's New Robot Vacuum Revolutionizes Home Cleaning with Innovative Mopping Feature [2025]
- Exploring the Future of Cleaning: A Deep Dive into Shark PowerDetect UV Robot Vacuum [2025]
- A Possible US Government iPhone-Hacking Toolkit Is Now in the Hands of Foreign Spies and Criminals | WIRED
![Hackers Are Turning to Easy, Fast AI Solutions to Roll Out Attacks: How to Keep Your Business Safe [2025]](https://tryrunable.com/blog/hackers-are-turning-to-easy-fast-ai-solutions-to-roll-out-at/image-1-1772638723843.jpg)



