Introduction
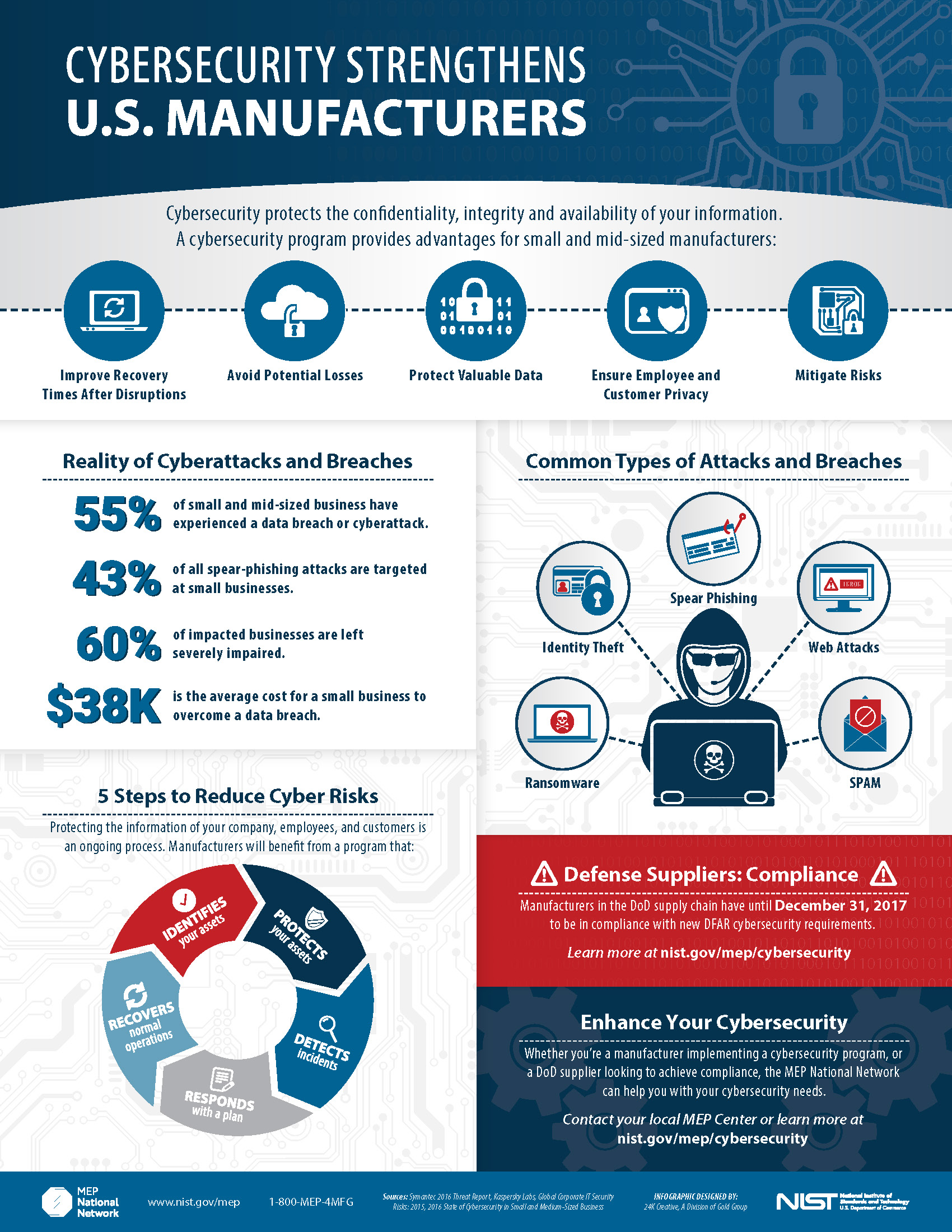
Highguard, a well-known cybersecurity firm, is shutting down operations this month. Founded in 2010, Highguard established itself as a leader in providing comprehensive security solutions for mid-sized businesses. The company's abrupt closure has sent shockwaves through the industry, leaving many businesses in a lurch, wondering how to protect their data and systems moving forward.
TL; DR
- Highguard's abrupt shutdown impacts thousands of businesses: Companies need to act swiftly to ensure continued cybersecurity.
- Transitioning to new cybersecurity solutions: Identify key features and avoid potential pitfalls during migration.
- Best practices for cybersecurity resilience: Implement multi-layered defense strategies.
- Future trends: Expect a rise in decentralized security solutions and AI-driven threat detection.
- Immediate actions required: Conduct a thorough security audit and assess alternative vendors.

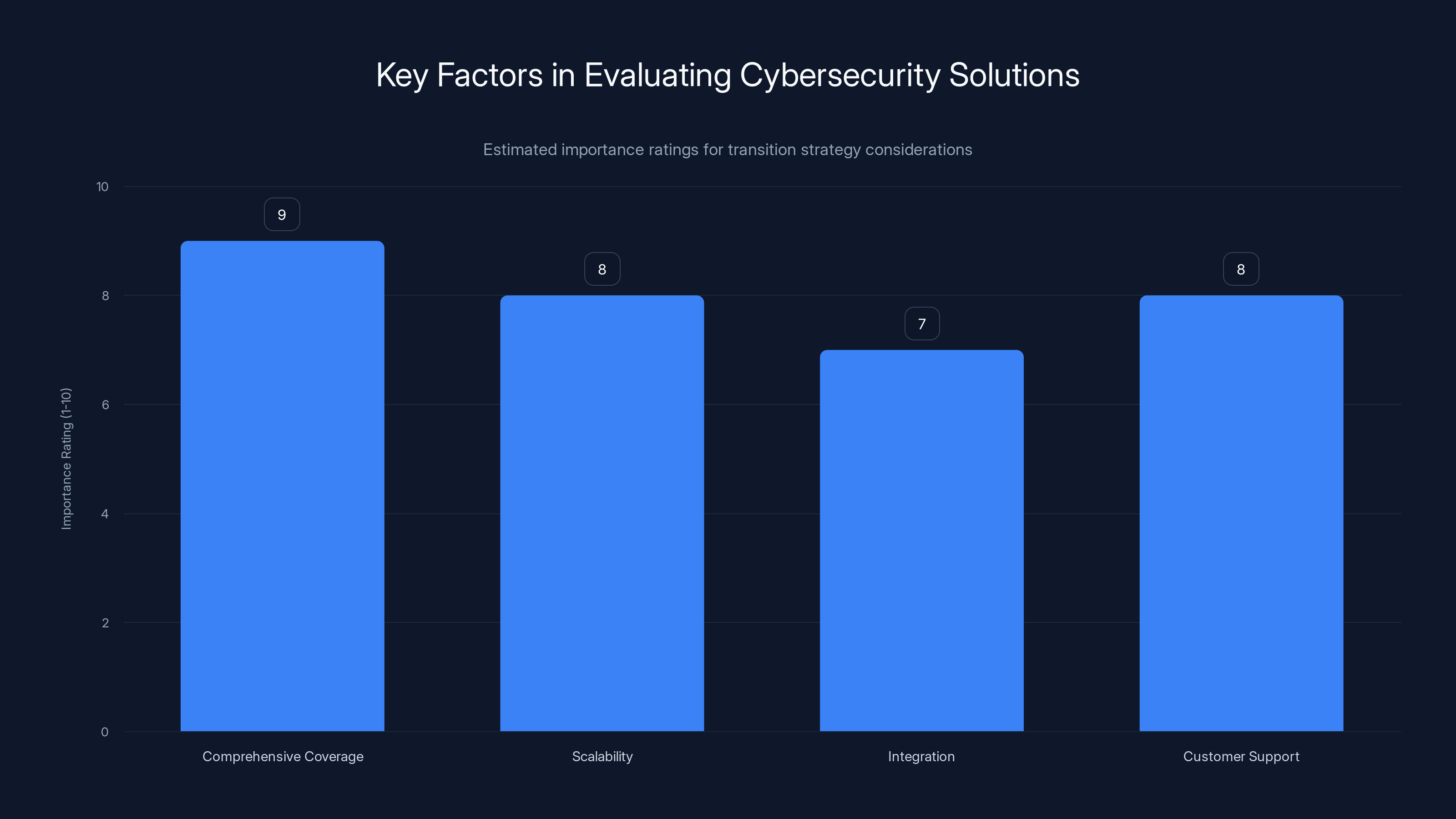
When transitioning from Highguard, comprehensive coverage and customer support are crucial, with ratings of 9 and 8 respectively. Estimated data.
Understanding Highguard's Role in Cybersecurity
Highguard served a critical role by offering endpoint protection, network security, and threat intelligence. Its solutions were robust, scalable, and tailored for mid-sized enterprises. The platform integrated seamlessly with existing IT infrastructure, making it a preferred choice for many organizations.
Key Features of Highguard
- Endpoint Protection: Highguard's endpoint security shielded devices from malware and unauthorized access.
- Network Security: The platform monitored network traffic to identify and mitigate threats in real-time.
- Threat Intelligence: Highguard provided insights into emerging threats, enabling proactive defense.
- User-Friendly Interface: The dashboard was intuitive, allowing IT teams to manage security protocols efficiently.
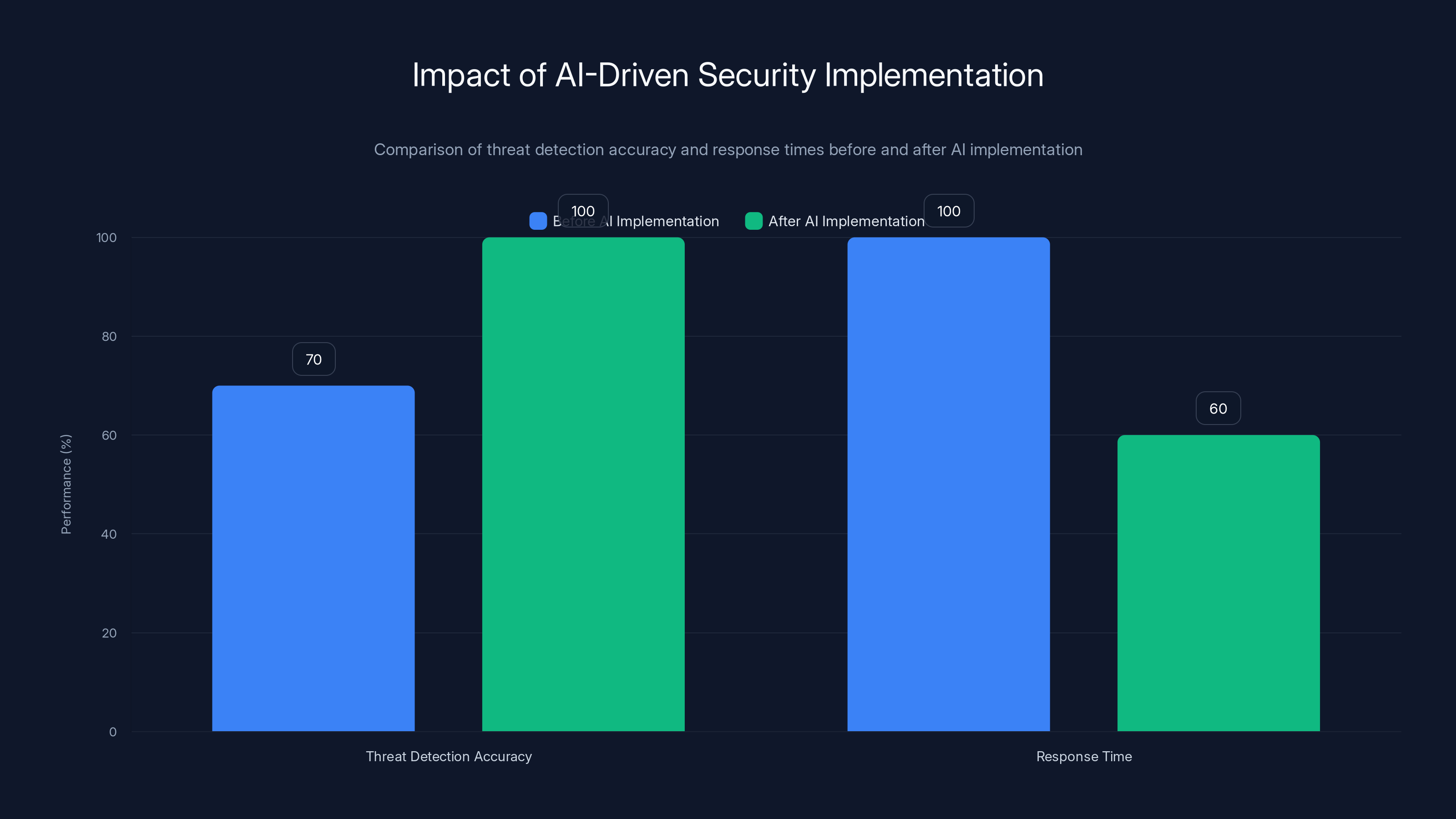
The AI-driven security system improved threat detection accuracy by 30% and reduced response times by 40%, showcasing significant enhancements in security operations.
Why Highguard's Shutdown Matters
The sudden closure of Highguard is more than just losing a vendor; it signifies a gap in the cybersecurity landscape. Businesses reliant on Highguard must now urgently seek alternative solutions to prevent vulnerabilities.
Immediate Impacts
- Data Vulnerability: Without Highguard's protection, businesses face increased risk of data breaches.
- Operational Disruptions: Transitioning to a new provider can lead to temporary service interruptions.
- Increased Costs: Finding and deploying a new solution involves both time and financial investment.
Transition Strategies for Businesses
Moving away from Highguard requires a strategic approach. Here are steps to ensure a smooth transition:
1. Conduct a Security Audit
Before switching to a new provider, conduct a comprehensive security audit to understand your organization's current cybersecurity posture. Identify gaps that Highguard covered and areas requiring immediate attention.
2. Evaluate Alternative Solutions
When selecting a new cybersecurity provider, consider the following:
- Comprehensive Coverage: Ensure the provider offers endpoint, network, and data security.
- Scalability: Choose a solution that can grow with your business needs.
- Integration: The new system should integrate smoothly with existing infrastructure.
- Customer Support: Reliable support is crucial during the transition phase.
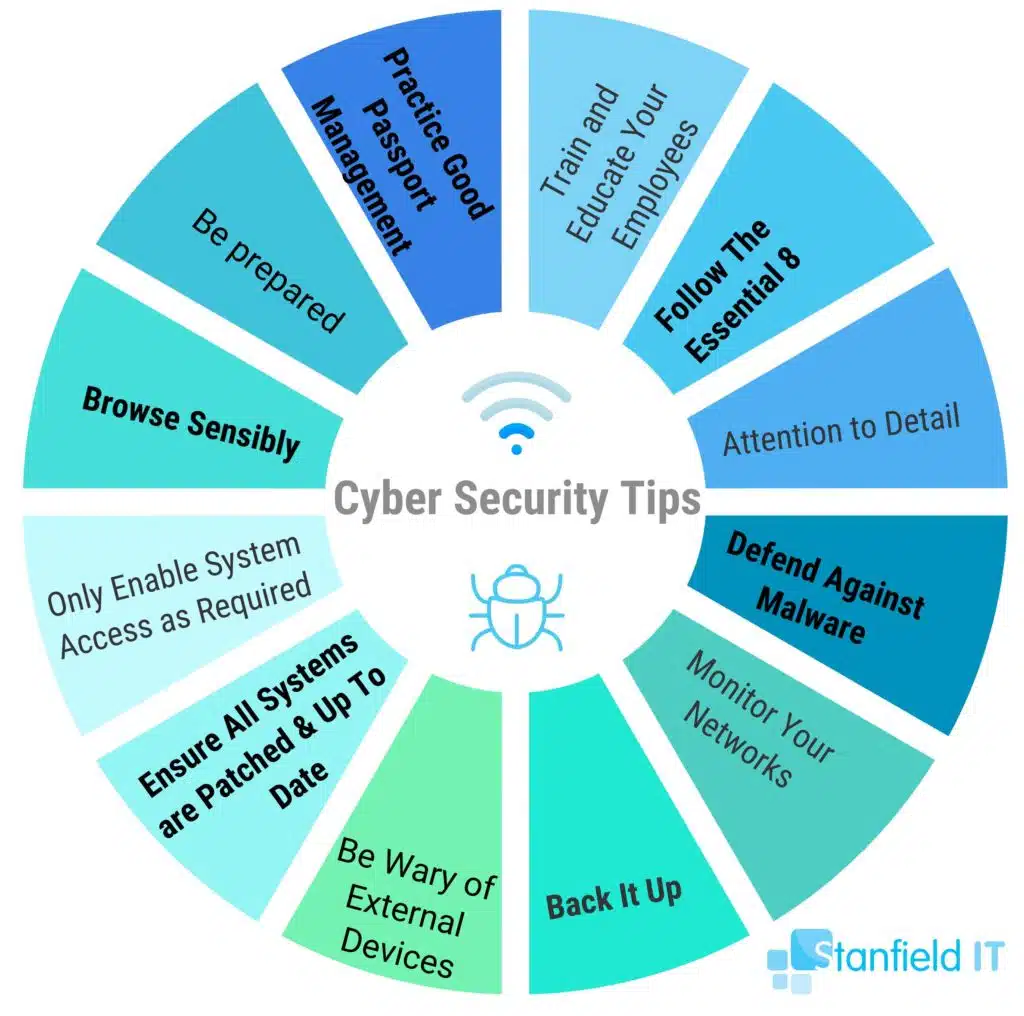
3. Implement a Multi-Layered Defense
Adopt a multi-layered approach to cybersecurity to enhance resilience. This includes:
- Firewalls and Intrusion Detection: Protect your network perimeter.
- Anti-Malware Tools: Regularly update virus definitions and software.
- Data Encryption: Encrypt sensitive data to prevent unauthorized access.
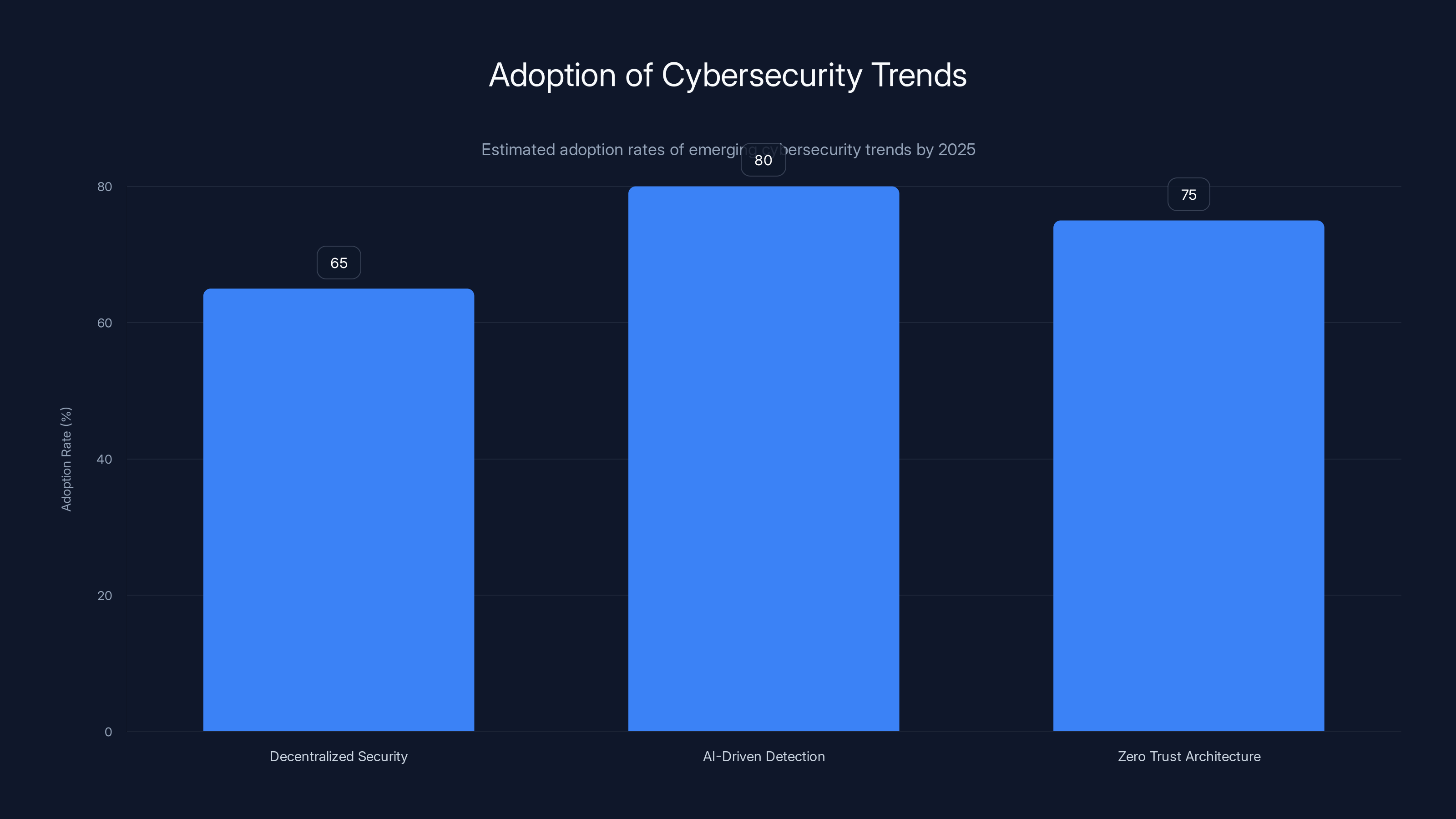
AI-driven threat detection is projected to have the highest adoption rate at 80% by 2025, followed closely by Zero Trust Architecture at 75%. Decentralized Security Solutions are expected to reach a 65% adoption rate. Estimated data.
Potential Pitfalls and Solutions
Transitioning from Highguard can present challenges. Here are common pitfalls and how to avoid them:
Pitfall 1: Incomplete Data Migration
Solution: Perform a thorough data backup before initiating the transition. Test the new system with a subset of data to ensure compatibility and functionality.
Pitfall 2: Underestimating Training Needs
Solution: Provide comprehensive training for your IT and security teams on the new system. Ensure they understand new protocols and tools.
Pitfall 3: Delayed Implementation
Solution: Set realistic timelines and allocate resources effectively. Engage with the new provider early to prevent delays.

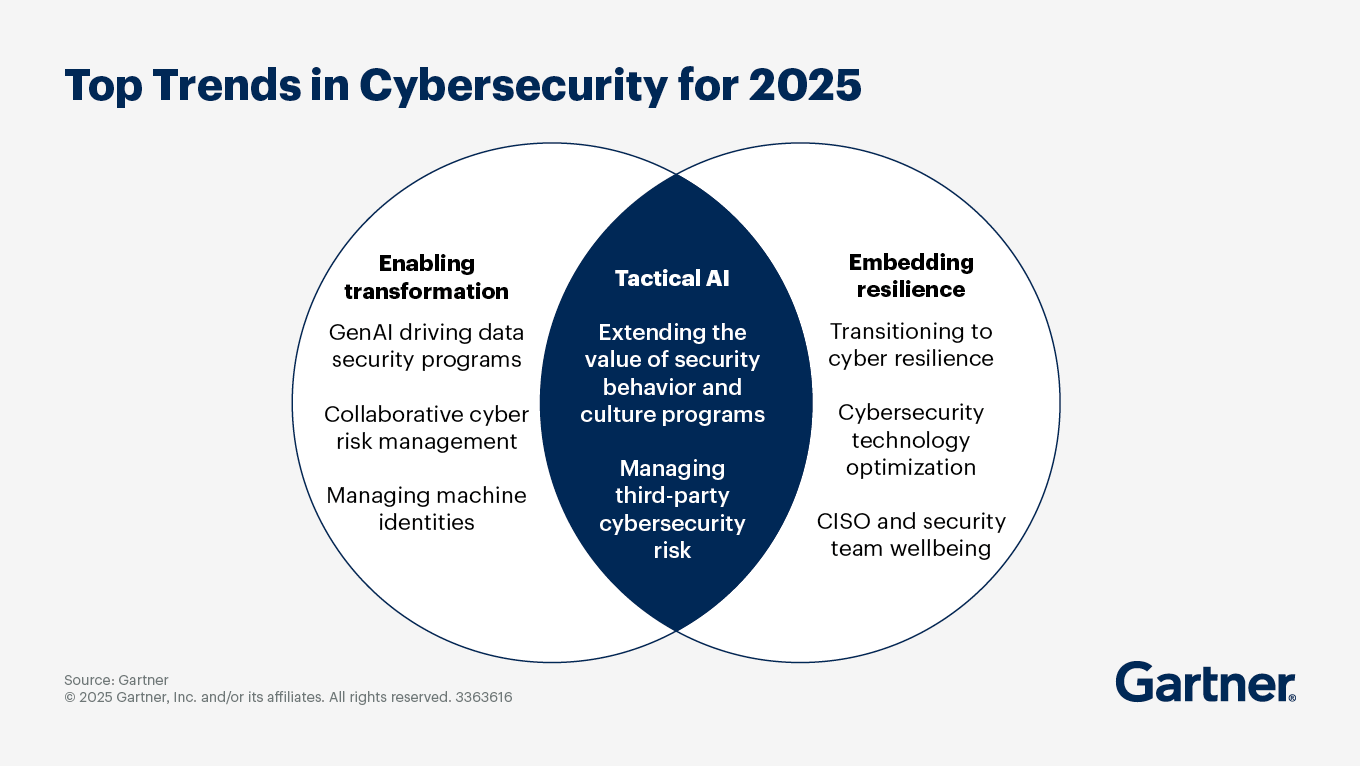
Future Trends in Cybersecurity
As businesses adapt to the post-Highguard landscape, several trends are emerging:
1. Decentralized Security Solutions
With the advent of remote work, decentralized security solutions are gaining popularity. These solutions focus on securing individual devices and networks rather than relying on centralized systems.
2. AI-Driven Threat Detection
Artificial intelligence is revolutionizing threat detection by analyzing vast amounts of data to identify patterns and anomalies. Expect increased adoption of AI-driven solutions for real-time monitoring.
3. Zero Trust Architecture
The Zero Trust model, which assumes no implicit trust and requires verification for every access request, is becoming standard. This approach enhances security by minimizing potential attack vectors.
Recommendations for Businesses
To stay secure in the changing cybersecurity landscape, businesses should:
- Regularly Update Security Protocols: Stay informed about the latest threats and adjust your security measures accordingly.
- Invest in Employee Training: Cybersecurity is everyone’s responsibility. Regular training can prevent human error, which is often a significant vulnerability.
- Collaborate with Industry Peers: Sharing insights and experiences with other businesses can provide valuable lessons and strategies.
Case Studies
Case Study 1: Transitioning from Highguard to a New Provider
A mid-sized tech company successfully transitioned from Highguard to a new provider by carefully evaluating their security needs and involving their IT team in the decision-making process. They conducted a phased implementation to minimize disruptions.
Case Study 2: Implementing AI-Driven Security
A financial institution adopted an AI-driven security system post-Highguard. The system improved threat detection accuracy by 30% and reduced response times by 40%.

Conclusion
Highguard's shutdown is a wake-up call for businesses to reassess their cybersecurity strategies. By conducting thorough audits, evaluating new solutions, and implementing best practices, companies can safeguard their digital assets and ensure continuity in the face of evolving threats.
FAQ
What is Highguard?
Highguard was a cybersecurity firm known for providing comprehensive security solutions for businesses, including endpoint protection and threat intelligence.
How can businesses transition from Highguard?
Businesses should conduct a security audit, evaluate alternative solutions, and implement a multi-layered defense strategy to transition smoothly from Highguard.
What are the future trends in cybersecurity?
Future trends include decentralized security solutions, AI-driven threat detection, and the adoption of Zero Trust architecture.
Why is employee training important in cybersecurity?
Training employees helps prevent human error, which is a common vulnerability in cybersecurity. It ensures that all staff are aware of best practices and potential threats.
How does AI improve threat detection?
AI enhances threat detection by analyzing large data sets to identify patterns and anomalies, allowing for real-time monitoring and quicker responses to threats.
What is Zero Trust architecture?
Zero Trust architecture assumes no implicit trust within the network. It requires verification for every access request, reducing potential attack vectors and enhancing security.
Key Takeaways
- Highguard's closure affects thousands of businesses, necessitating urgent action.
- Conducting a security audit is crucial for identifying vulnerabilities during the transition.
- Evaluate new providers based on comprehensive coverage, scalability, and integration capabilities.
- A multi-layered defense strategy enhances cybersecurity resilience.
- AI-driven threat detection and Zero Trust architecture are future trends to watch.
- Employee training is vital to minimizing human error in cybersecurity.
Related Articles
- Beware of Google Tasks Scams: Protect Your Workplace from Phishing Attacks [2025]
- Understanding and Mitigating the Cisco Catalyst SD-WAN Vulnerability [2025]
- Unmasking Pseudonymous Users: How LLMs Are Changing Privacy Dynamics [2025]
- Unmasking the Latest Phishing Threat: Fake Google Security Pages [2025]
- The Silent Threat: How Hackers Exploit .arpa Domains for Phishing Schemes [2025]
- Oh Great, Here Comes 6G: What You Need to Know [2025]
![The Impact of Highguard's Shutdown: Navigating the Transition for Businesses [2025]](https://tryrunable.com/blog/the-impact-of-highguard-s-shutdown-navigating-the-transition/image-1-1772570225647.jpg)