Hackers Drove Through Toronto with Fake Cell Towers, Hijacking Thousands of Phones [2025]
Imagine driving through Toronto, your mobile phone quietly connecting to a network that isn't what it seems. This isn't a plot from a sci-fi thriller—it's a real cyberattack that happened in the heart of Canada's bustling metropolis. Hackers deployed fake cell towers to hijack thousands of phones and disrupt millions of connections in plain sight, as detailed in a report by Tom's Hardware.
TL; DR
- Massive Mobile Disruption: Hackers used fake cell towers to hijack thousands of phones, causing over 13 million network disruptions.
- Technical Exploit: Utilized IMSI catchers to intercept mobile traffic and gather data.
- Security Implications: Highlights vulnerabilities in mobile networks and the need for enhanced security measures.
- Preventive Measures: Users and providers must adopt stronger encryption and real-time monitoring.
- Future Trends: Expect increased sophistication in mobile network attacks as technology evolves.

Estimated data shows that phone calls and messages are most affected during network disruptions, highlighting the critical need for robust mobile infrastructure.
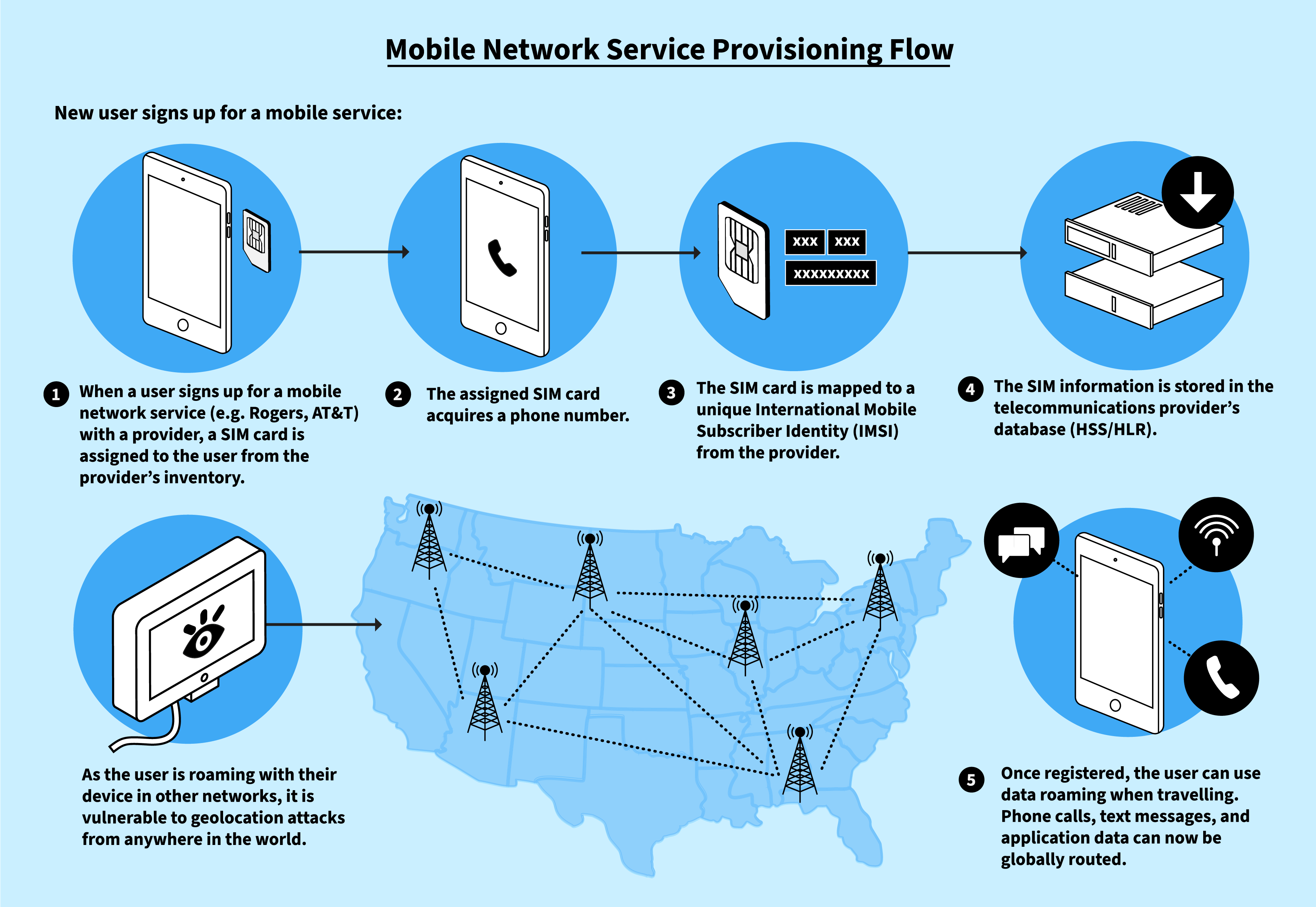
The Anatomy of a Cellular Hijack
What Happened in Toronto?
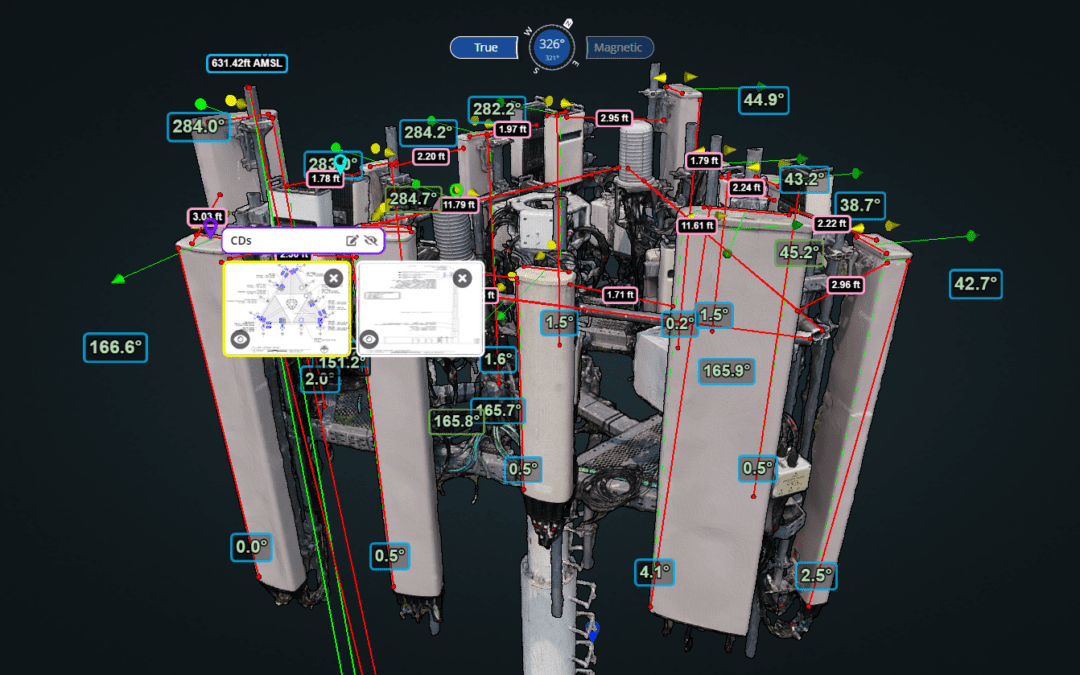
In a brazen display of cyber warfare, hackers drove through Toronto with equipment designed to mimic cell towers. These devices, known as IMSI catchers or Stingrays, trick phones into connecting by masquerading as legitimate cell towers. According to CyberScoop, such tools exploit long-known vulnerabilities in telecom networks.
Here's the thing: once connected, these devices can intercept calls, texts, and even inject malware into the phones. This particular attack resulted in a staggering 13 million disruptions, leaving a trail of chaos across the city's digital landscape.
How Do Fake Cell Towers Work?
IMSI catchers exploit a fundamental vulnerability in mobile communication protocols. By mimicking the radio frequency of legitimate towers, they intercept the International Mobile Subscriber Identity (IMSI) numbers. This allows them to track the device and manipulate its connection.
The process is disturbingly simple:
- Detection: The device scans for nearby phones.
- Impersonation: It broadcasts a stronger signal than legitimate towers.
- Interception: Phones connect, believing it to be an official network.
- Data Capture: Calls, messages, and internet traffic are intercepted.
The Tools of the Trade
These attacks typically involve a few pieces of specialized equipment:
- IMSI Catchers: The core device used for intercepting mobile signals.
- Signal Amplifiers: Boost the strength of the fake signal to outcompete real towers.
- Software Suites: Analyze and process the intercepted data.

Encryption and regular updates are rated as the most important practices for mobile security, highlighting their critical role in protecting user data. (Estimated data)
Real-World Impact: Beyond the Numbers
The Immediate Consequences
For residents of Toronto, the impact was immediate and disruptive. Phone calls dropped, messages went unsent, and data connections slowed to a crawl. Businesses reliant on mobile connectivity experienced significant interruptions. As noted by Network World, mobile networks in urban areas handle billions of connections daily, and a single disruption can cascade, affecting critical services like emergency response and financial transactions.
Long-Term Implications
This attack underscores a glaring vulnerability in mobile networks. As cities become more connected, the potential for damage from such attacks increases. Mobile carriers and users alike must recognize and mitigate these risks.
Best Practices for Mobile Security
For Users
- Encryption: Use apps with end-to-end encryption for calls and messages.
- Awareness: Be cautious of unexpected network behavior.
- Updates: Regularly update your phone's operating system to patch vulnerabilities.
For Providers
- Network Monitoring: Implement real-time monitoring for unusual activity.
- Stronger Encryption: Upgrade encryption protocols to withstand interception.
- Public Awareness Campaigns: Educate users about potential threats and preventive measures.

Downgrade attacks are the most common exploit used by IMSI catchers, followed by man-in-the-middle attacks. Estimated data based on typical exploit patterns.
Technical Deep Dive: How IMSI Catchers Exploit Networks
Understanding the GSM Protocol
The Global System for Mobile Communications (GSM) is the standard for mobile networks worldwide. It offers reliability, but its design includes vulnerabilities that IMSI catchers exploit. According to Chosun, these vulnerabilities are often targeted by cybercriminals.
Key GSM Features:
- Open Channel Communication: Initially designed for ease of connection, not security.
- Weak Encryption: Early GSM versions use A5/1 encryption, easily broken with modern computing power.
IMSI Catcher Exploits
- Downgrade Attacks: Force phones to use older, less secure protocols.
- Man-in-the-Middle: Intercept communications between the phone and the legitimate tower.
- Denial of Service: Overwhelm the phone with connection requests.

Case Study: Lessons from the Toronto Attack
What We Learned
The Toronto incident serves as a wake-up call for both consumers and providers. Real talk: the risk isn't just theoretical; it's here and now. As PR Newswire highlights, proactive defense measures are crucial in the enterprise AI age.
Key Takeaways:
- Proactive Defense: Relying solely on existing protocols is insufficient.
- Cross-Industry Collaboration: Tech companies, carriers, and government agencies must work together.
- User Education: Consumers need practical guidance on protecting their devices.
Future Trends in Cellular Security
The Evolution of Mobile Threats
As technology advances, so do the tools and techniques of cybercriminals. Future attacks will likely become more sophisticated, targeting specific individuals or networks. The data security market is expected to adapt rapidly to these evolving threats.
Emerging Solutions
- AI-Driven Security: Utilize AI to predict and counteract attacks in real-time.
- Blockchain-Based Verification: Apply blockchain for secure, decentralized network authentication.
- Quantum Encryption: Develop quantum-resistant protocols to safeguard against future threats.
Practical Implementation Guides
Setting Up Personal Security
- Install Security Apps: Use apps like Signal or WhatsApp for secure communication.
- Regular Audits: Conduct regular audits of installed apps and permissions.
For Organizations
- Implement Network Segmentation: Isolate sensitive data from general access.
- Regular Training: Conduct cybersecurity training for employees.
- Threat Simulation: Regularly test network defenses with simulated attacks.
Common Pitfalls and Solutions
Pitfall: Complacency
- Solution: Stay informed about the latest security threats and trends.
Pitfall: Weak Passwords
- Solution: Use complex passwords and change them regularly.
Pitfall: Ignoring Updates
- Solution: Enable automatic updates for all devices and applications.
Conclusion: A Call to Action
The Toronto attack highlights a critical issue in our increasingly connected world: the vulnerability of mobile networks. Here's the bottom line: security must evolve alongside technology to protect against these sophisticated threats.
Both individuals and organizations must take proactive steps to safeguard their communications. This means adopting new technologies, staying informed, and working together to create a more secure digital environment.
FAQ
What are fake cell towers?
Fake cell towers, or IMSI catchers, are devices that mimic legitimate cell towers to intercept mobile communications.
How do IMSI catchers affect mobile security?
They exploit vulnerabilities in mobile protocols to intercept calls, messages, and data, posing significant security risks.
Can individuals protect themselves from IMSI catchers?
Yes, by using encrypted communication apps, regularly updating devices, and being aware of unusual network behavior.
What should mobile providers do to prevent such attacks?
Providers should enhance encryption protocols, implement real-time network monitoring, and educate users about security threats.
Are IMSI catchers legal?
The legality of IMSI catchers varies by country, but unauthorized use is generally illegal.
What is the future of mobile security?
Future security measures will likely include AI-driven defenses, blockchain-based verification, and quantum encryption to counteract evolving threats.
How significant was the Toronto attack?
The attack caused over 13 million network disruptions, highlighting vulnerabilities in mobile infrastructure and the need for improved security measures.

Key Takeaways
- Massive attack in Toronto disrupted 13 million connections using fake cell towers.
- IMSI catchers exploit vulnerabilities in mobile communication protocols.
- Enhanced encryption and real-time monitoring are crucial for security.
- Future trends include AI-driven security and quantum encryption.
- Consumers must adopt secure communication apps and update devices regularly.
Related Articles
- How AI Tools Have Made Vulnerability Exploitation Faster and Easier [2025]
- Dangerous New Linux Exploit Gives Attackers Root Access to Countless Computers | WIRED
- Birdfy's Smart Bird Feeder: A Perfect Mother's Day Gift [2025]
- Quantum Communication Overcomes Fiber Optic Barrier [2025]
- Understanding the Impact of Canceled Digital Rights Conferences on Global Policy [2025]
- Unraveling the 'Copy Fail' Vulnerability in Linux: AI Scanning's Role in Security [2025]
![Hackers Drove Through Toronto with Fake Cell Towers, Hijacking Thousands of Phones [2025]](https://tryrunable.com/blog/hackers-drove-through-toronto-with-fake-cell-towers-hijackin/image-1-1777674862042.png)



