Unraveling the 'Copy Fail' Vulnerability in Linux: AI Scanning's Role in Security [2025]
In the rapidly evolving world of technology, security vulnerabilities are a constant concern. Recently, a significant flaw known as the "Copy Fail" was uncovered in Linux systems, highlighting the crucial role AI scanning plays in modern cybersecurity. This article delves into the technical intricacies of this vulnerability, its potential impact, and how AI tools can both detect and mitigate such threats.
TL; DR
- AI scanning revealed a critical 'Copy Fail' vulnerability in Linux.
- The flaw affects file-handling operations, compromising system integrity.
- Exploit could lead to unauthorized access and data leaks.
- Best practices include regular updates and AI-driven monitoring.
- Future trends emphasize AI's growing role in cybersecurity.

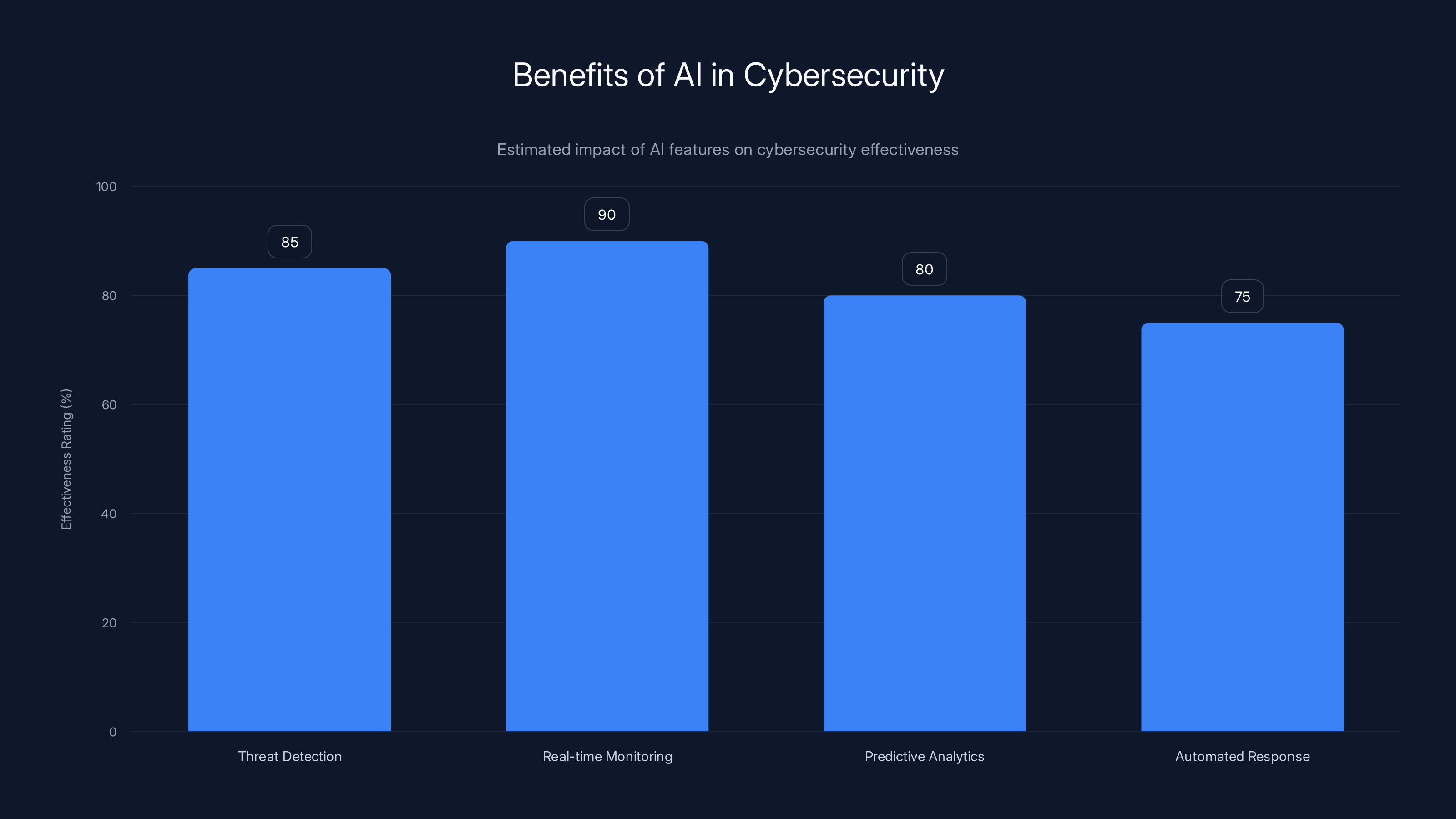
AI enhances cybersecurity with high effectiveness in threat detection and real-time monitoring. (Estimated data)
Understanding the 'Copy Fail' Vulnerability
The 'Copy Fail' vulnerability in Linux is a severe security flaw that involves incorrect handling of file copy operations. This bug can lead to unauthorized access, data corruption, and system instability. At its core, the issue is rooted in the mismanagement of file permissions and buffer overflows during copy processes.
Technical Breakdown
When a file is copied in Linux, the system handles permissions and data integrity checks. The 'Copy Fail' vulnerability arises from a buffer overflow that occurs when these checks are bypassed. This allows attackers to execute arbitrary code or escalate privileges, creating a significant security risk.
bash# Example of a vulnerable copy command
cp source_file /destination_directory/
In this scenario, if the source file contains malicious code, and the overflow vulnerability is exploited, the destination directory may be compromised.
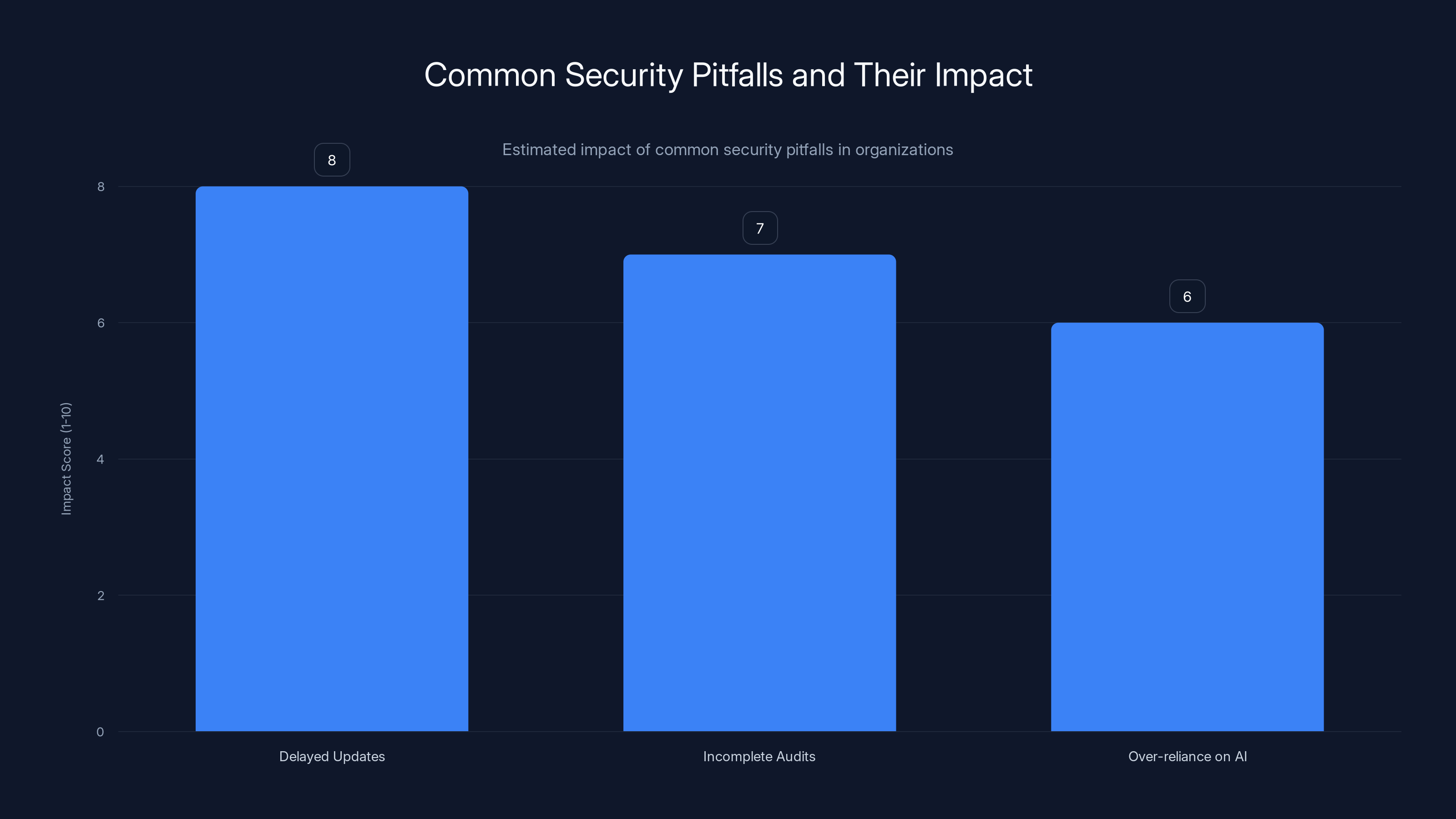
Delayed updates have the highest estimated impact on security breaches, highlighting the importance of automated systems. Estimated data.
AI Scanning: The Game Changer
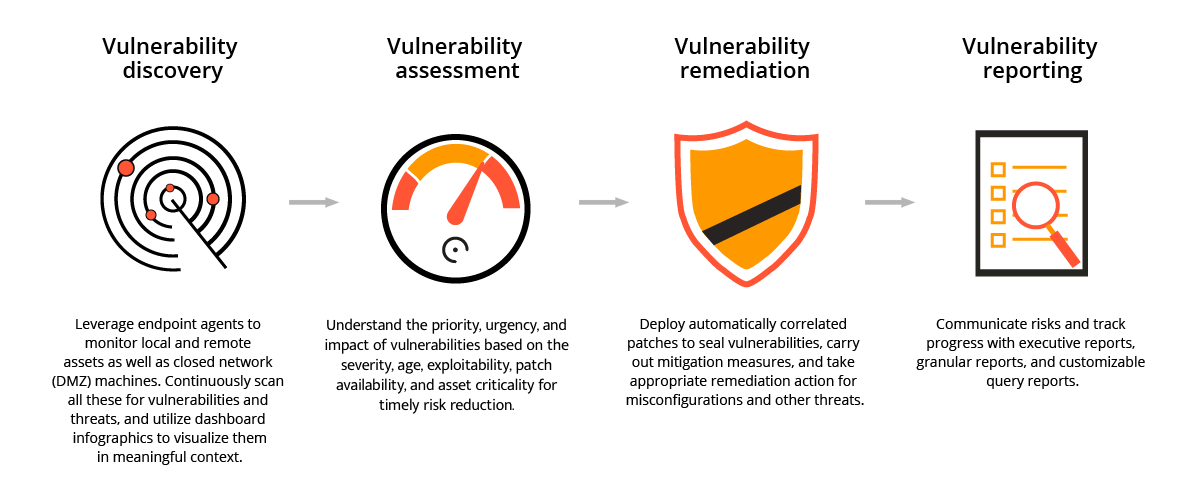
Artificial Intelligence (AI) has transformed the landscape of cybersecurity by providing advanced tools for threat detection. In the case of the 'Copy Fail' vulnerability, AI scanning tools were instrumental in identifying the flaw quickly and efficiently.
How AI Scanning Works
AI scanning tools use machine learning algorithms to analyze vast amounts of data, identifying patterns and anomalies that may indicate security threats. In this instance, AI was able to pinpoint irregularities in file handling operations, flagging the 'Copy Fail' vulnerability for further investigation.

Practical Implementation Guide
Addressing the 'Copy Fail' vulnerability requires both immediate action and long-term strategies. Here are some practical steps to mitigate the risk:
Immediate Steps
-
Patch Vulnerable Systems: Ensure that all Linux kernels are updated to the latest version where the vulnerability has been patched.
bashsudo apt-get update && sudo apt-get upgrade -
Audit File Permissions: Regularly audit file permissions to ensure they are correctly set and do not allow unauthorized access.
-
Use AI Monitoring Tools: Deploy AI-driven monitoring tools to continuously scan for unusual activities related to file operations.
Long-term Strategies
- Regular Software Updates: Stay informed about updates from Linux distributions and apply them promptly.
- Security Training: Educate staff on best practices for system security and the importance of regular security audits.
- AI and Machine Learning Integration: Invest in AI-based security solutions that can evolve with emerging threats.

Patching systems and integrating AI solutions are among the most effective measures against the 'Copy Fail' vulnerability. Estimated data based on typical security practices.
Common Pitfalls and Solutions
While addressing vulnerabilities like 'Copy Fail,' organizations often encounter common pitfalls. Here are some solutions:
-
Pitfall 1: Delayed Updates
- Solution: Implement automated update systems to ensure that security patches are applied without delay.
-
Pitfall 2: Incomplete Security Audits
- Solution: Conduct comprehensive audits that include all aspects of system security, not just known vulnerabilities.
-
Pitfall 3: Over-reliance on AI
- Solution: Use AI as a tool to complement human expertise, not replace it. Regularly review AI findings for accuracy.
Future Trends in AI and Cybersecurity
As AI continues to evolve, its role in cybersecurity is expected to expand significantly. Here are some trends to watch:
- AI-Driven Threat Intelligence: AI will increasingly be used to analyze threat intelligence data, providing more accurate and timely warnings.
- Automated Response Systems: Future systems will likely incorporate AI to automate responses to detected threats, reducing response times.
- Enhanced Predictive Analytics: AI will enable more sophisticated predictive analytics, helping organizations anticipate and prepare for potential vulnerabilities.

Recommendations for Organizations
To stay ahead of vulnerabilities like 'Copy Fail,' organizations should adopt a proactive approach to cybersecurity. Here are some recommendations:
- Invest in AI Security Solutions: Prioritize investments in AI-based security tools that offer real-time threat detection and response capabilities.
- Foster a Security-First Culture: Encourage a culture where security is a priority, and all team members are aware of their role in maintaining system integrity.
- Collaborate with AI and Cybersecurity Experts: Partner with experts to stay informed about the latest threats and best practices.
Conclusion
The 'Copy Fail' vulnerability in Linux serves as a stark reminder of the ever-present security challenges faced by organizations. By leveraging AI scanning and adopting best practices, it's possible to mitigate risks and enhance system security. As AI technology continues to advance, its role in cybersecurity will only become more critical, offering new tools and strategies to combat emerging threats.
FAQ
What is the 'Copy Fail' vulnerability?
The 'Copy Fail' vulnerability is a security flaw in Linux systems that involves incorrect handling of file copy operations, leading to potential unauthorized access and data corruption.
How does AI scanning help in detecting vulnerabilities like 'Copy Fail'?
AI scanning tools analyze data for patterns and anomalies, quickly identifying security threats such as the 'Copy Fail' vulnerability by recognizing irregularities in file operations.
What are the benefits of using AI in cybersecurity?
AI offers enhanced threat detection, real-time monitoring, and predictive analytics, helping organizations identify and respond to security threats more effectively.
How can organizations protect themselves from vulnerabilities like 'Copy Fail'?
Organizations can protect themselves by keeping systems updated, using AI monitoring tools, conducting regular security audits, and fostering a security-first culture.
What future trends should we expect in AI and cybersecurity?
Future trends include AI-driven threat intelligence, automated response systems, and enhanced predictive analytics, all contributing to more effective cybersecurity strategies.
Why is it important to stay updated with security patches?
Staying updated with security patches is crucial to closing vulnerabilities and preventing potential exploits that could compromise system integrity.
Use Case: Generating automated security reports with AI to streamline vulnerability management.
Try Runable For FreeKey Takeaways
- AI scanning revealed a critical vulnerability in Linux.
- The 'Copy Fail' flaw affects file-handling operations.
- Exploit could lead to unauthorized access and data leaks.
- Regular updates and AI-driven monitoring are best practices.
- AI's role in cybersecurity is expected to grow significantly.
- Organizations should adopt a proactive approach to security.
- Investing in AI security solutions is crucial for future preparedness.
Related Articles
- How AI Tools Have Made Vulnerability Exploitation Faster and Easier [2025]
- QR Code Phishing Tactics Surge: Navigating the 2026 Cybersecurity Landscape
- OpenAI's New Cyber Tool: Access Restrictions and Industry Implications [2025]
- GPT-5.5 vs Mythos: Unveiling the Real Cybersecurity Contenders [2025]
- The Rise of AI Content Outsourcing: Christian Creators Turn to Fiverr [2025]
- Surprising Results: Why Neither ChatGPT Nor Claude is the Smartest Free AI [2025]
![Unraveling the 'Copy Fail' Vulnerability in Linux: AI Scanning's Role in Security [2025]](https://tryrunable.com/blog/unraveling-the-copy-fail-vulnerability-in-linux-ai-scanning-/image-1-1777655050756.jpg)



