Introduction
In an era where cybersecurity is paramount, techniques like canary traps have become essential tools for securing sensitive information. Although often overshadowed by complex technologies like quantum encryption and biometric authentication, canary traps offer a straightforward yet effective method to identify unauthorized disclosures within sensitive datasets.
TL; DR
- Canary Traps in Brief: A method to detect leaks by embedding unique identifiers in distributed information.
- Canadian Elections: Utilize canary traps to secure electoral databases, ensuring integrity.
- Implementation Guide: Steps include data segmentation, unique identifier generation, and monitoring.
- Common Pitfalls: Includes identifier predictability and improper data segmentation.
- Future Trends: Increased adoption in various sectors beyond government.
- Bottom Line: Canary traps are a cost-effective way to enhance information security.
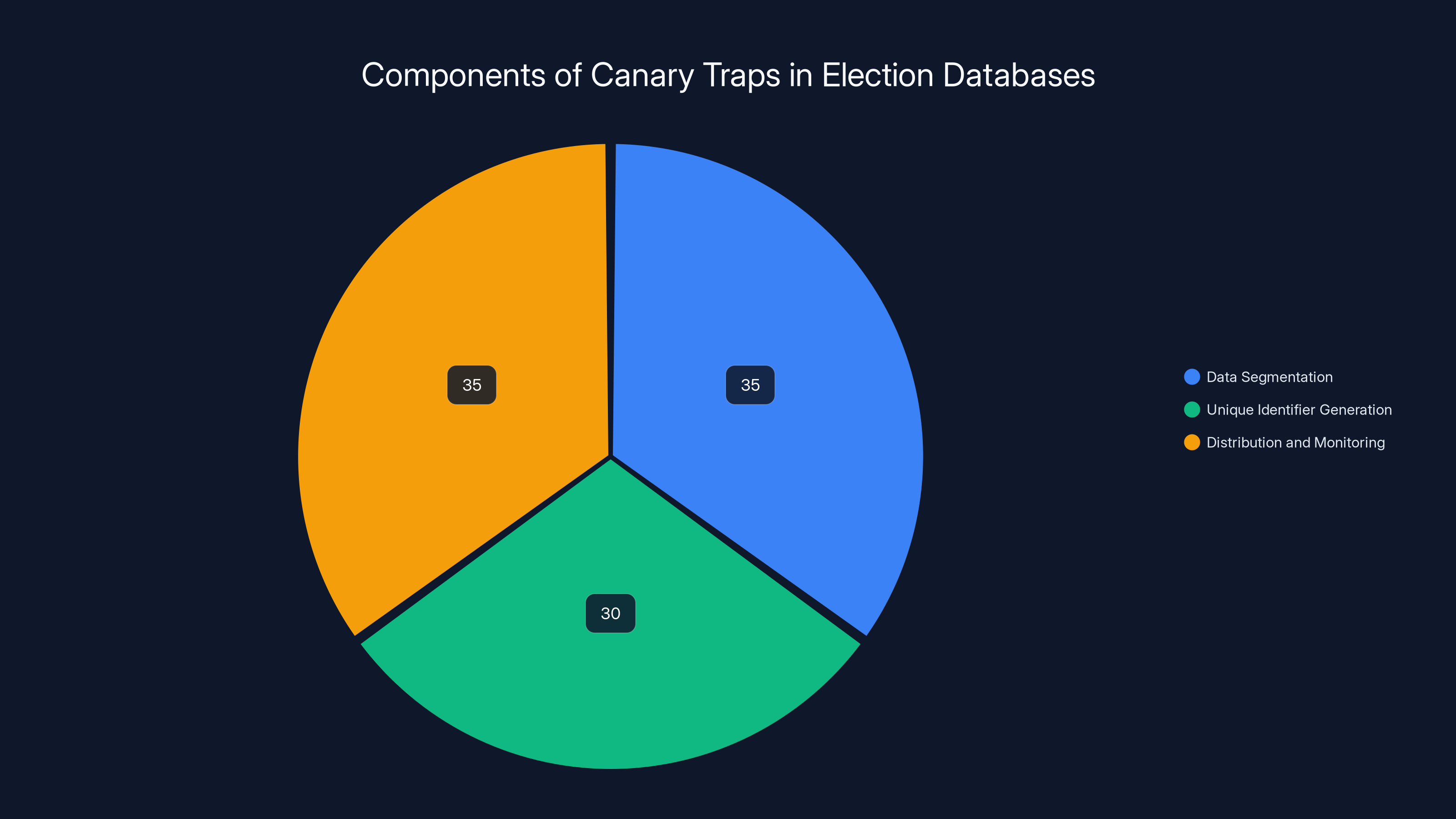
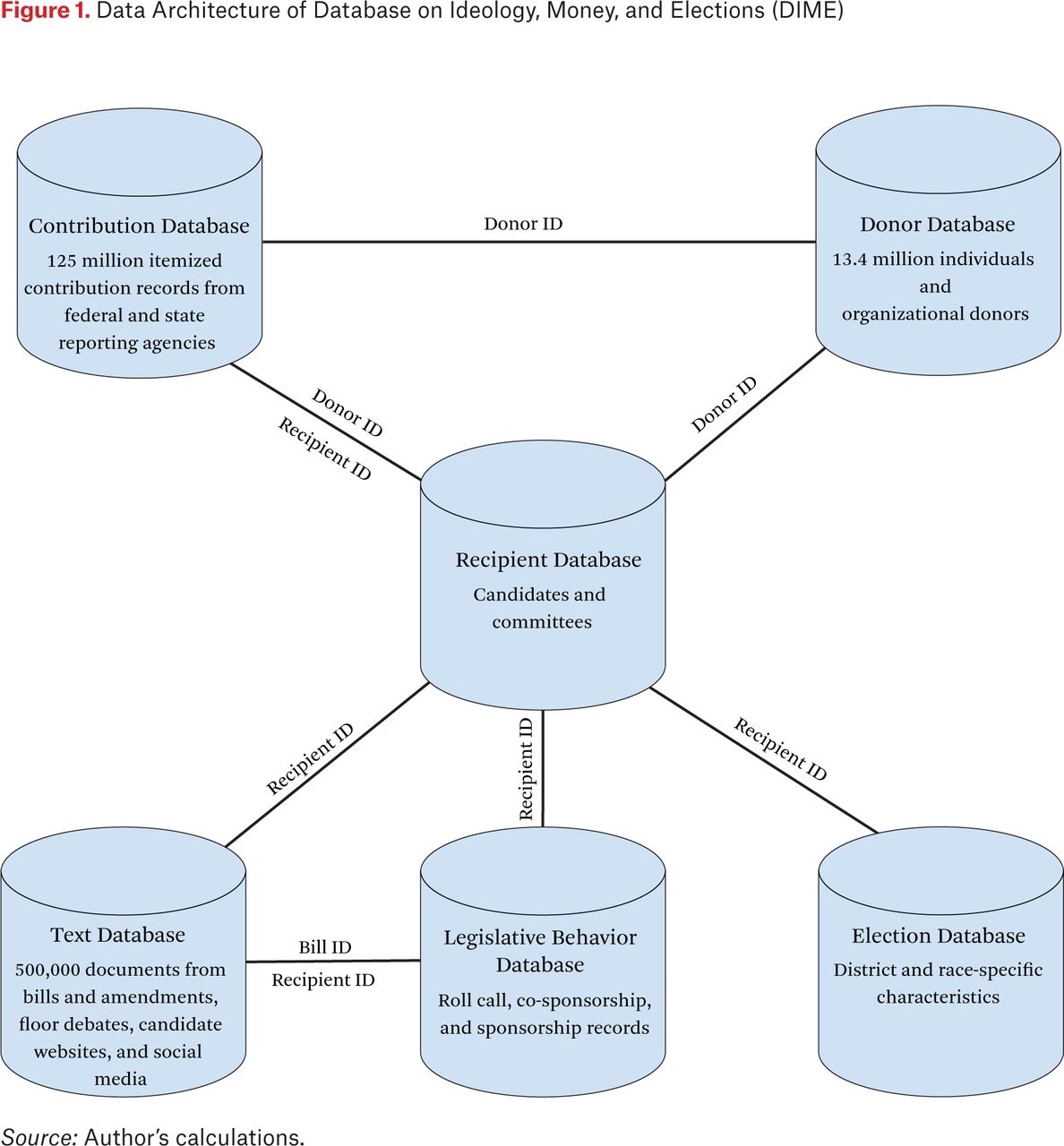
Estimated data shows equal emphasis on data segmentation and monitoring, with a slightly lower focus on identifier generation.
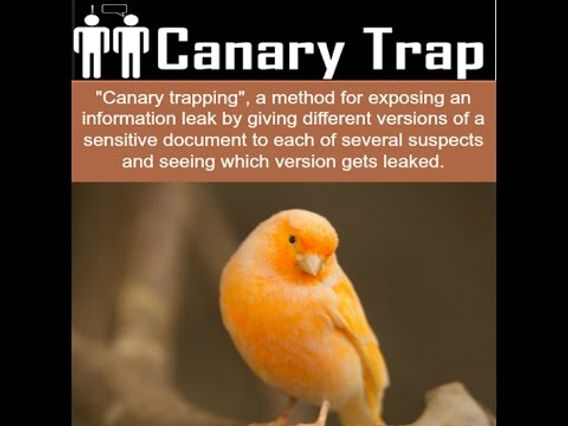
Understanding Canary Traps
A canary trap involves embedding unique, subtle changes into copies of sensitive documents or databases before distribution. These changes act as 'canaries,' revealing the source of any leak if the information is released publicly.
How It Works
Here's the thing: To set up a canary trap, you assign a unique identifier to each recipient's copy of the document or dataset. For example, if a document is leaked, you can trace it back to the specific individual by identifying the unique marker within that document.
Historical Context
The concept of canary traps isn't new. It's a technique historically used in espionage to identify double agents. In the digital age, it has found new life in protecting sensitive data from leaks.
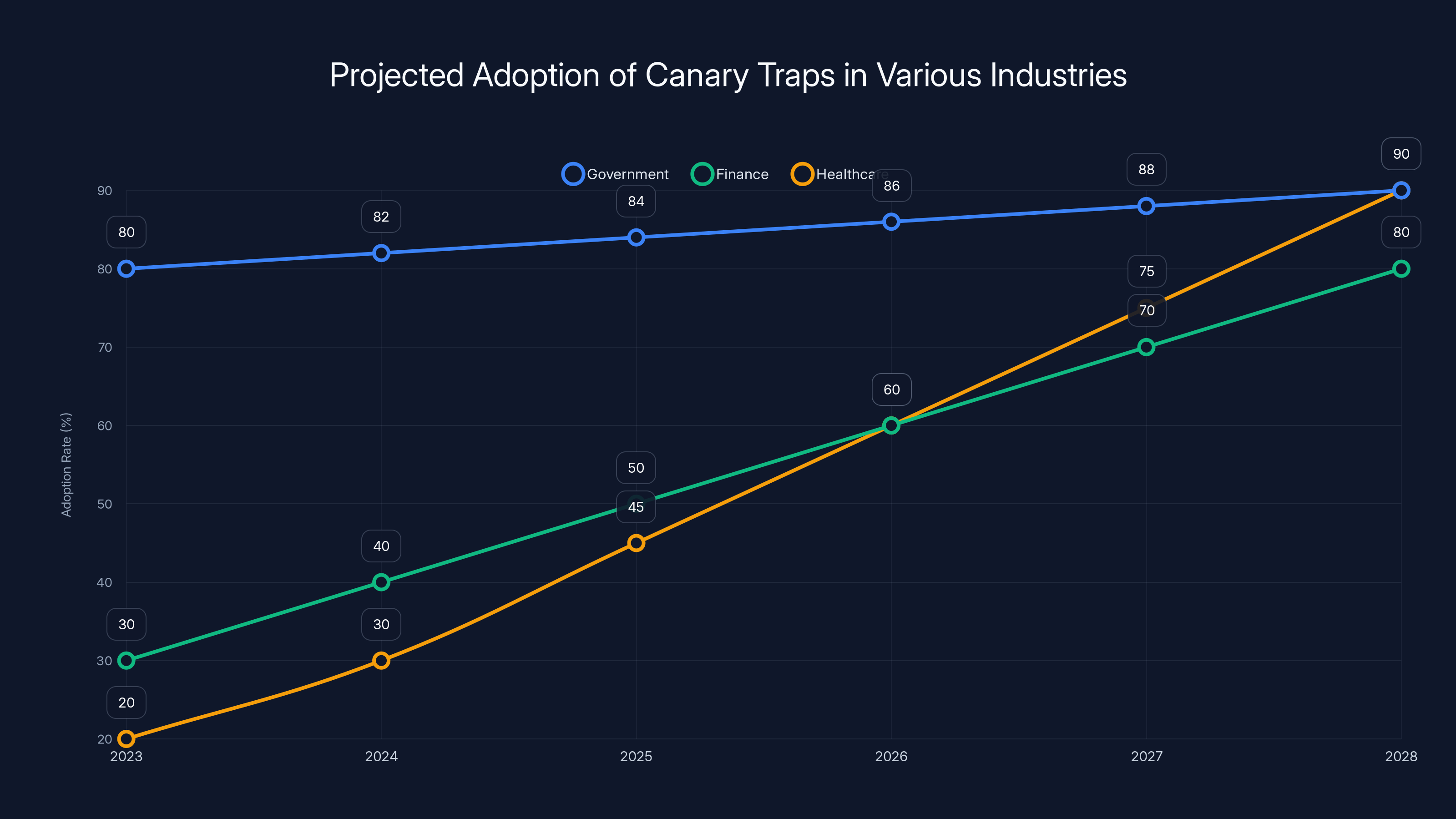
Estimated data suggests that the adoption of canary traps will significantly increase in finance and healthcare sectors by 2028, driven by the need to prevent data breaches.
Implementing Canary Traps in Election Databases
Canada's electoral systems have adopted canary traps to maintain the integrity of their databases. Let's break down how they do it:
- Data Segmentation: Divide the database into segments, assigning unique identifiers to each.
- Unique Identifier Generation: Use algorithms to generate identifiers that are difficult to replicate or predict.
- Distribution and Monitoring: Distribute segmented data with identifiers and monitor for unauthorized disclosures.
Example Scenario
Imagine an electoral database containing voter information: names, addresses, and districts. A canary trap might involve altering a non-critical field that doesn't affect the data's utility, such as a voter ID suffix, but uniquely for each copy.
Best Practices
Designing Effective Identifiers
- Randomness: Ensure identifiers are generated randomly to prevent guessing.
- Non-Invasive Changes: Alter data fields that won't impact the database's functionality.
- Regular Updates: Change identifiers regularly to prevent long-term predictability.
Monitoring and Response
- Automated Detection: Implement tools that automatically scan public platforms for data leaks.
- Rapid Response: Have protocols in place to respond quickly once a leak is detected.
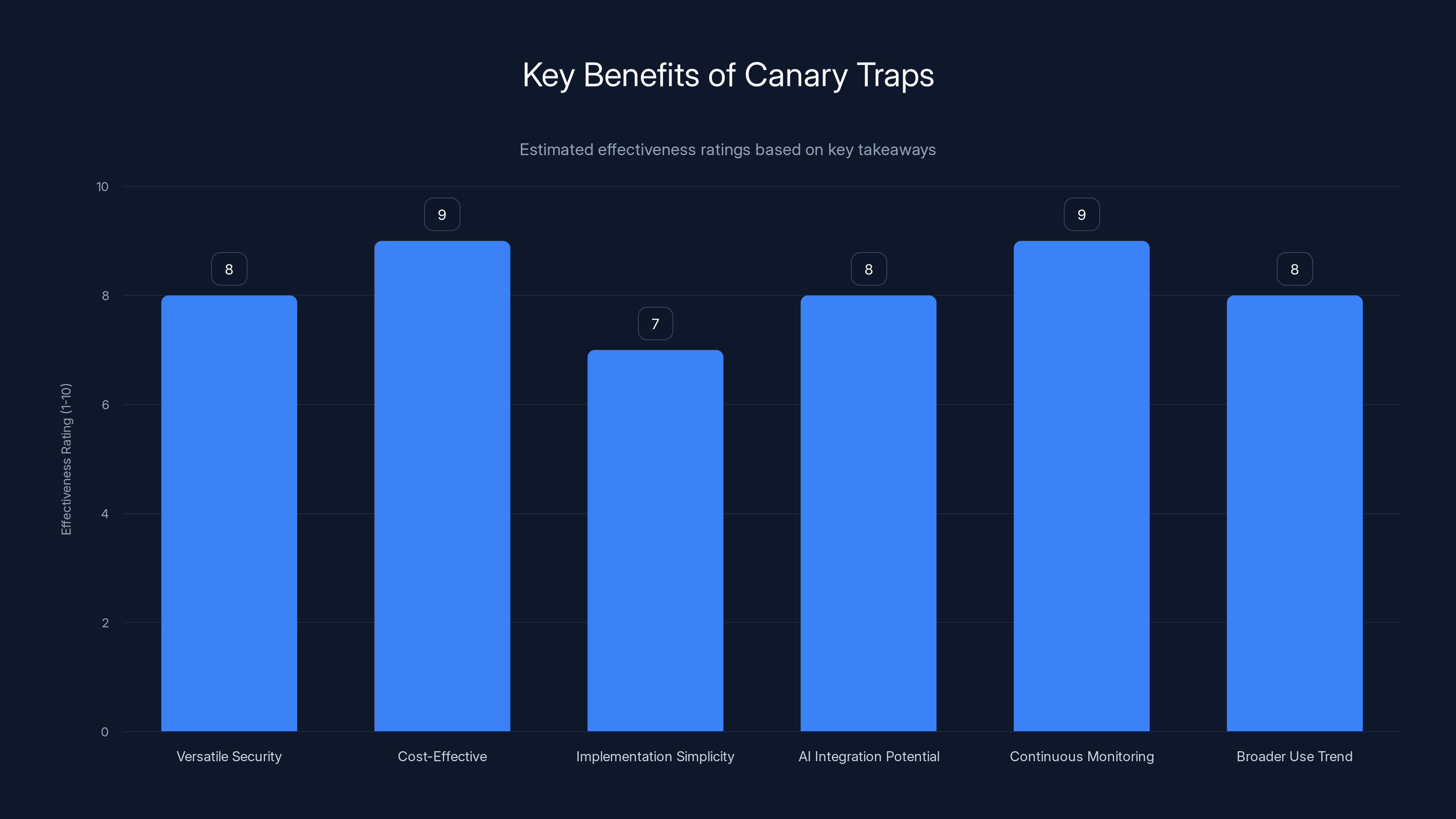
Canary traps are highly effective due to their versatility, cost-effectiveness, and ease of implementation. Future AI integration and continuous monitoring enhance their potential. (Estimated data)
Common Pitfalls and Solutions
Predictable Patterns
If identifiers follow a predictable pattern, they can be easily guessed by malicious actors. Use cryptographic methods to ensure randomness.
Insufficient Monitoring
Without proper monitoring, a canary trap is ineffective. Utilize real-time scanning tools to detect leaks promptly.
Future Trends
Broader Adoption
While currently prominent in government sectors, canary traps are likely to see increased use in industries like finance and healthcare, where data breaches can have severe consequences.
Integration with AI
AI can enhance canary trap effectiveness by automating the detection of leaks and predicting potential vulnerabilities before they are exploited.

Conclusion
The simplicity and effectiveness of canary traps make them a valuable tool in the arsenal against data leaks. As technology evolves, so too will the sophistication of these traps, ensuring they remain relevant in a rapidly changing digital landscape.
FAQ
What is a canary trap?
A canary trap is a method of detecting information leaks by embedding unique identifiers into distributed documents or datasets.
How do canary traps work in election databases?
They involve assigning unique identifiers to segments of data, allowing tracing back to the source if the data is leaked.
What are the benefits of using canary traps?
Canary traps provide a cost-effective way to enhance security by identifying leakers without needing complex technology.
Can canary traps be used outside government?
Yes, industries like finance and healthcare can benefit from using canary traps to protect sensitive data.
How can AI improve the effectiveness of canary traps?
AI can automate leak detection and enhance the security measures associated with canary traps by predicting vulnerabilities.
What are common pitfalls of implementing canary traps?
Common pitfalls include predictable identifiers and insufficient monitoring, both of which can reduce the effectiveness of the trap.
Key Takeaways
- Versatile Security Measure: Canary traps are applicable in various sectors beyond government.
- Cost-Effective: They require minimal resources compared to other security measures.
- Implementation Simplicity: Relatively easy to set up with the right protocols.
- Enhanced by AI: Future potential lies in integrating AI for improved security.
- Continuous Monitoring: Essential for effective leak detection and prevention.
- Trend Towards Broader Use: Expect increased adoption due to proven effectiveness.
Related Reading
- Advanced Techniques in Cybersecurity
- AI in Data Security: The Next Frontier
- Protecting Personal Data in the Digital Age
References
- Canadian Election Security Practices
- Historical Use of Canary Traps
- AI and Cybersecurity
Related Articles
- The Privacy Paradox: How US Healthcare Marketplaces Shared Sensitive Data with Ad Tech Giants [2025]
- China's CPU-Only Supercomputer Aiming for Exascale Performance [2025]
- The Best Star Wars Day Deals [2025]
- Analyzing Hisense's Bold Price Strategy for RGB LED TVs [2025]
- Do Lightsaber Blades Have Mass? Exploring the Science Behind the Iconic Star Wars Weapon [2025]
- AI-Generated Phishing Attacks: Beyond the Inbox and How to Protect Yourself [2025]
![How Canada Uses Canary Traps for Election Security: An In-Depth Analysis [2025]](https://tryrunable.com/blog/how-canada-uses-canary-traps-for-election-security-an-in-dep/image-1-1777925031741.jpg)



