AI-Generated Phishing Attacks: Beyond the Inbox and How to Protect Yourself [2025]
Phishing has long been a prevalent threat in the digital world, primarily targeting email inboxes. However, with the advent of sophisticated AI technologies, phishing attacks have extended their reach beyond traditional email, infiltrating other communication platforms such as instant messaging, collaboration tools, and even calendar invites. In this comprehensive guide, we'll explore how AI is reshaping phishing tactics and provide actionable strategies to protect yourself and your organization.
TL; DR
- AI-Driven Threats: Phishing attacks are increasingly powered by AI, making them more convincing and harder to detect, as noted in a Microsoft report.
- Beyond Email: Targets include calendars, team collaboration tools, and social media platforms, according to ITPro.
- Proactive Defense: Implement multi-factor authentication and robust cybersecurity training for all employees.
- AI Tools for Protection: Use AI-driven security solutions to detect and mitigate threats.
- Continuous Education: Regularly update your knowledge on the latest phishing methods and prevention techniques.

Introduction: The Evolving Landscape of Phishing
Phishing attacks have evolved significantly since their inception. Initially, they were simple email scams, often riddled with spelling errors and obvious red flags. But as technology advanced, so did the sophistication of these attacks. Today, AI-powered phishing is a reality, and it's changing the game.
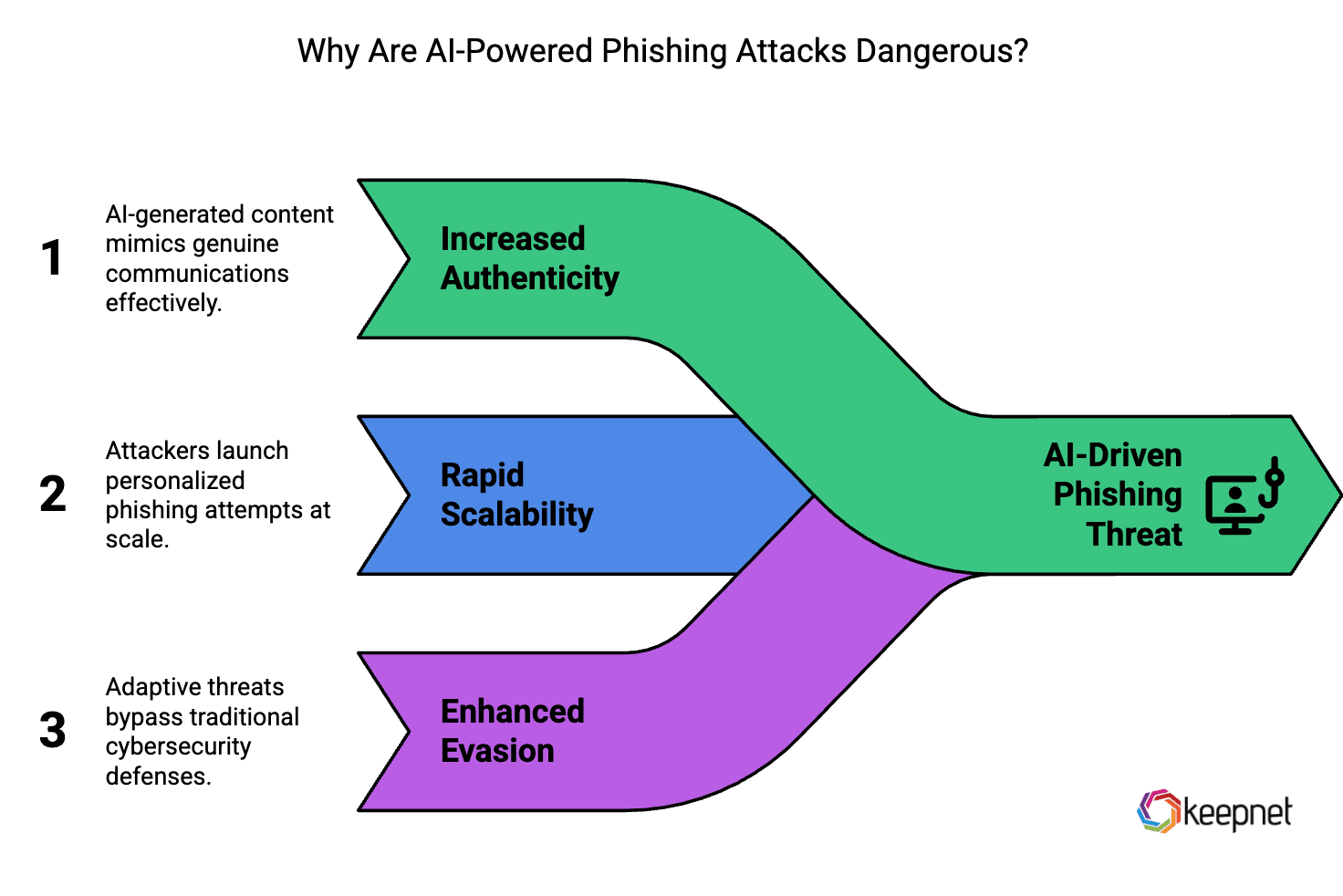
The Role of AI in Modern Phishing Attacks
AI has revolutionized how cybercriminals execute phishing attacks. By leveraging machine learning algorithms, attackers can automatically generate personalized phishing emails that mimic the communication style of trusted sources. AI can analyze massive datasets to identify potential targets and craft believable messages that increase the likelihood of success.
Key Features of AI-Driven Phishing:
- Personalization: Tailored messages that mimic authentic communication.
- Automation: Ability to launch large-scale campaigns with minimal human intervention.
- Adaptability: Continuous evolution of tactics to bypass security measures, as highlighted by SC World.

AI-Generated Phishing Beyond the Inbox
Calendar and Collaboration Tool Exploits
In recent years, cybercriminals have expanded their reach to exploit calendar and collaboration tools. Malicious actors can send fake meeting invites with embedded phishing links or malicious attachments. These attacks are particularly insidious because they mimic legitimate business communications, as discussed in Microsoft's security blog.
Common Tactics:
- Fake Calendar Invites: Invites containing phishing links or malicious attachments.
- Team Collaboration Attacks: Phishing messages sent through platforms like Microsoft Teams or Slack.
Social Media and Instant Messaging Threats
Social media platforms and instant messaging apps are also common targets for AI-driven phishing. Attackers can create fake profiles, initiate conversations, and eventually direct victims to phishing websites, as noted by Yahoo Tech.
Best Practices for Protection:
- Verify Sender Identities: Always confirm the identity of the sender before clicking on any links.
- Use Privacy Settings: Adjust privacy settings to limit information exposure on social media platforms.

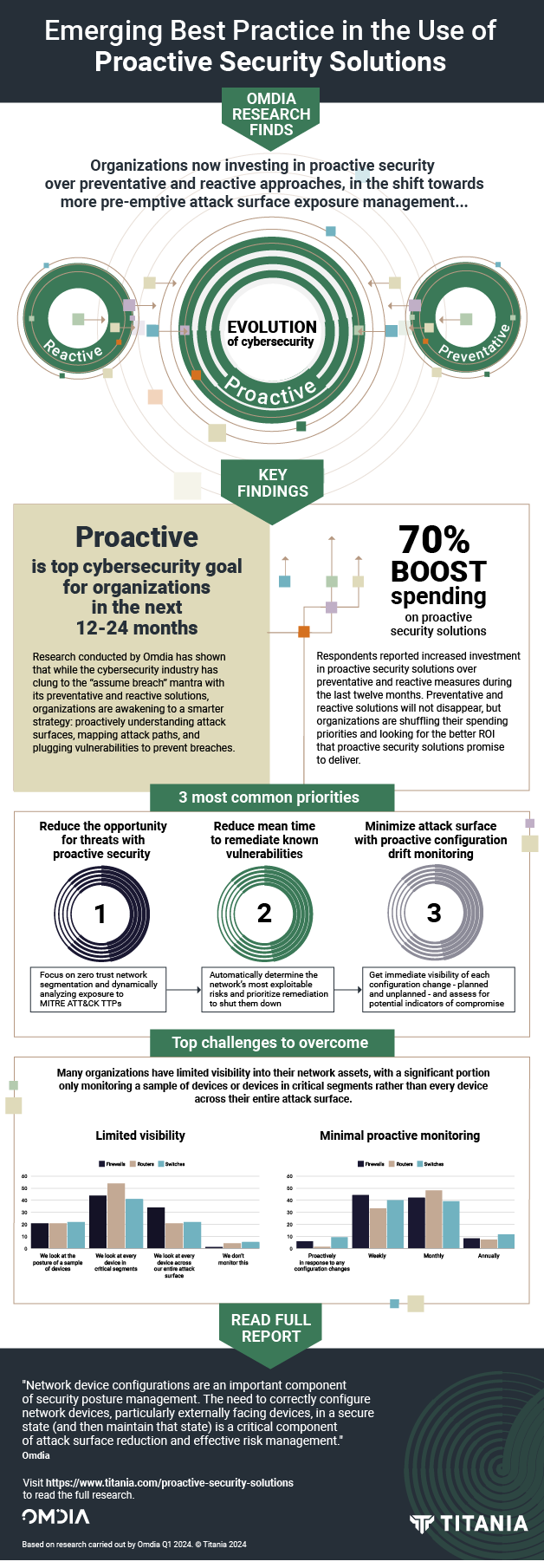
Implementing Proactive Defense Strategies
Multi-Factor Authentication (MFA)
One of the most effective ways to mitigate phishing risks is implementing multi-factor authentication (MFA). By requiring additional verification steps, MFA makes it more difficult for attackers to gain unauthorized access, even if they have compromised login credentials.
Types of MFA:
- SMS Verification: Receiving a code via text message.
- App-Based Authentication: Using apps like Google Authenticator.
- Biometric Verification: Fingerprint or facial recognition.
Cybersecurity Training
Regular cybersecurity training is essential for employees to recognize and respond to phishing attempts. Training should cover the latest phishing tactics, how to identify phishing messages, and the importance of not clicking on unsolicited links or attachments, as emphasized by HIPAA Journal.
Training Topics:
- Recognizing Phishing Emails: Look for red flags like poor grammar and mismatched URLs.
- Reporting Procedures: Encourage immediate reporting of suspicious messages to IT.

Leveraging AI for Defense
Just as AI is being used offensively, it can also be a powerful defensive tool. AI-driven security solutions can help detect and mitigate phishing attempts in real time.
AI-Driven Security Solutions
- Anomaly Detection: Identifies unusual patterns in communication that may indicate phishing.
- Behavioral Analysis: Monitors user behavior to detect anomalies that could signal a compromised account.
- Natural Language Processing (NLP): Analyzes text to identify phishing attempts based on language patterns, as detailed in Fortune Business Insights.
Future Trends in Phishing and Cybersecurity
As AI continues to evolve, so too will phishing tactics. Staying ahead of these trends is crucial for maintaining robust cybersecurity.
Predicted Trends
- Increased Use of Deepfakes: AI-generated deepfake technology could be used to create convincing phishing content.
- Io T Exploitation: As Io T devices proliferate, they may become targets for phishing attacks, as predicted by PPC Land.

Conclusion: Staying Ahead of AI-Driven Threats
The rise of AI-generated phishing attacks presents new challenges for individuals and organizations. By understanding the tactics used by cybercriminals and implementing comprehensive security measures, you can protect yourself and your organization from these sophisticated threats.
FAQ
What is AI-generated phishing?
AI-generated phishing involves using artificial intelligence to automate and enhance phishing attacks, making them more convincing and harder to detect.
How can I identify an AI-generated phishing attack?
Look for signs like unusually personalized messages, unexpected links, and requests for sensitive information. Always verify the sender's identity.
What tools can help protect against phishing?
Tools like multi-factor authentication, AI-driven security solutions, and regular cybersecurity training are effective in mitigating phishing risks.
How does AI contribute to phishing attacks?
AI allows attackers to analyze large datasets to craft highly personalized and automated phishing messages, increasing the likelihood of success.
Is email still a major target for phishing?
Yes, email remains a primary target, but attackers are also exploiting other platforms like calendars and collaboration tools, as highlighted by Stay Safe Online.
How often should I update my cybersecurity training?
Cybersecurity training should be updated at least annually or whenever there are significant changes in phishing tactics.
What is multi-factor authentication?
Multi-factor authentication adds an extra layer of security by requiring additional verification steps, such as a code sent to your phone, to access an account.
Can AI be used defensively against phishing?
Yes, AI-driven security solutions can detect and mitigate phishing attempts by analyzing patterns and identifying anomalies in communication.
The Best AI-Based Security Tools at a Glance
| Tool | Best For | Standout Feature | Pricing |
|---|---|---|---|
| Runable | AI automation | AI agents for presentations, docs, reports, images, videos | $9/month |
| Tool 1 | AI orchestration | Integrates with 8,000+ apps | Free plan available; paid from $19.99/month |
| Tool 2 | Data quality | Automated data profiling | By request |
Quick Navigation:
- Runable for AI-powered presentations, documents, reports, images, videos
- Tool 1 for AI orchestration
- Tool 2 for Data quality
Key Takeaways
- Phishing attacks are increasingly AI-driven, targeting beyond email.
- Calendar and collaboration tools are new phishing targets.
- Implement MFA and regular cybersecurity training to mitigate risks.
- Use AI-driven security solutions for real-time threat detection.
- Continuous education on phishing tactics is crucial.
- AI can be used both offensively and defensively in cybersecurity.
- Future trends include deepfake and IoT phishing threats.
- Proactive defense strategies are essential for protection.
Related Articles
- Autonomous AI Tools Revolutionize Pentagon Operations [2025]
- Unraveling the 'Copy Fail' Vulnerability in Linux: AI Scanning's Role in Security [2025]
- QR Code Phishing Tactics Surge: Navigating the 2026 Cybersecurity Landscape
- GPT-5.5 vs Mythos: Unveiling the Real Cybersecurity Contenders [2025]
- AI Agents: New Risks Requiring Continuous Monitoring and Oversight [2025]
- Ultimate Guide to Using a $2 VPN for Enhanced Security on All Devices [2025]
![AI-Generated Phishing Attacks: Beyond the Inbox and How to Protect Yourself [2025]](https://tryrunable.com/blog/ai-generated-phishing-attacks-beyond-the-inbox-and-how-to-pr/image-1-1777894475978.jpg)



