How One Man's Accidental Hack Revealed Vulnerabilities in Modern Robotics [2025]
When a hobbyist hacker inadvertently accessed 7,000 Romo robovacs, it wasn't just the tech world that took notice. This incident highlighted a growing concern about the security of interconnected devices, especially in the rapidly expanding field of consumer robotics. Let's break down what happened, why it matters, and what the future holds.
TL; DR
- Accidental Hack: A hacker unintentionally accessed 7,000 Romo robovacs, exposing security flaws.
- Industry Response: The incident prompted companies like DJI to address these vulnerabilities seriously.
- Consumer Implications: Highlights the need for improved security in smart home devices.
- Developer Insights: Developers must prioritize security and adopt best practices.
- Future Trends: Expect more stringent regulations and security-focused design.
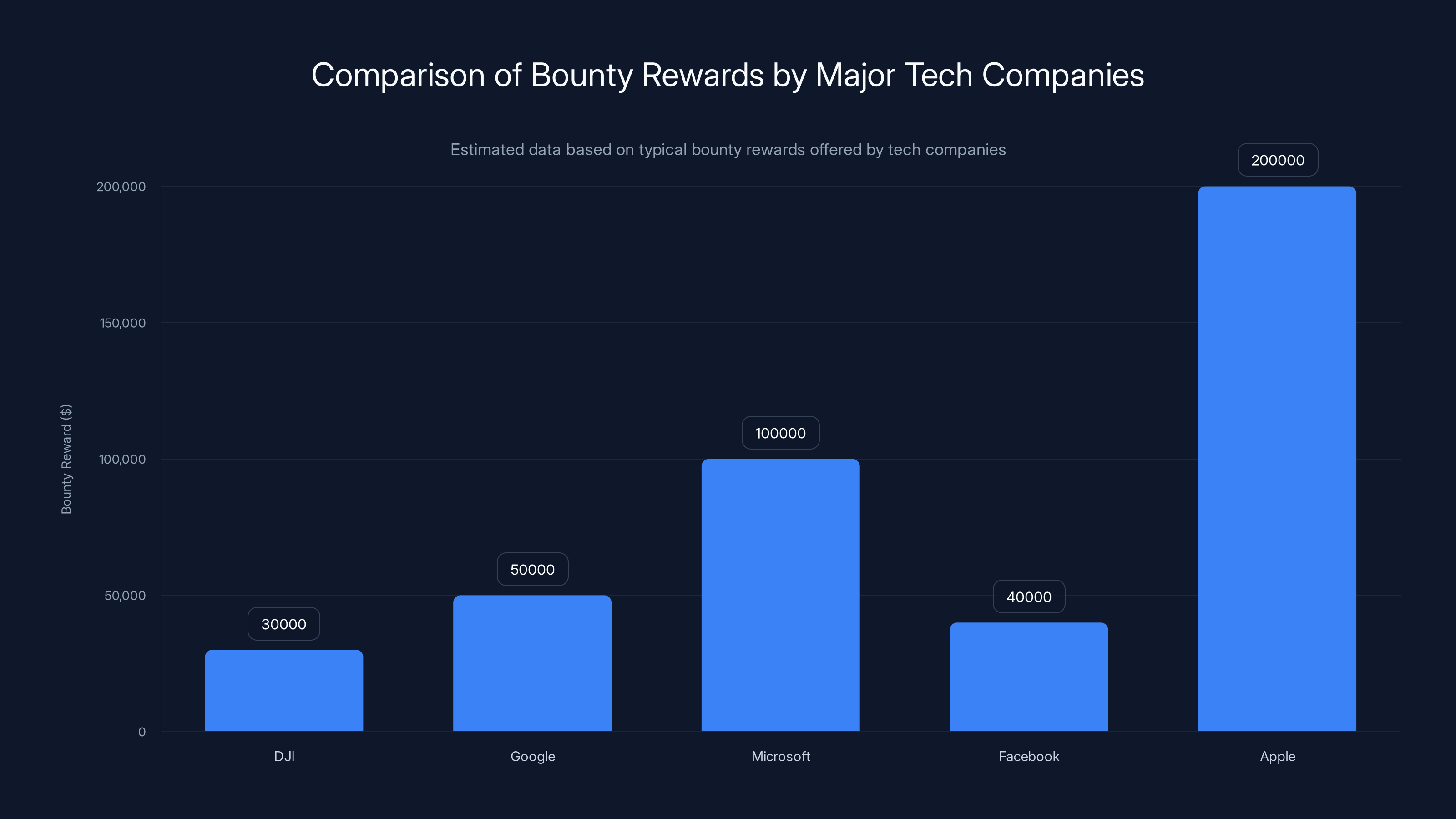
Estimated data shows that Apple offers the highest bounty reward among major tech companies, reflecting their commitment to security. Estimated data.
The Accidental Hack: What Really Happened?
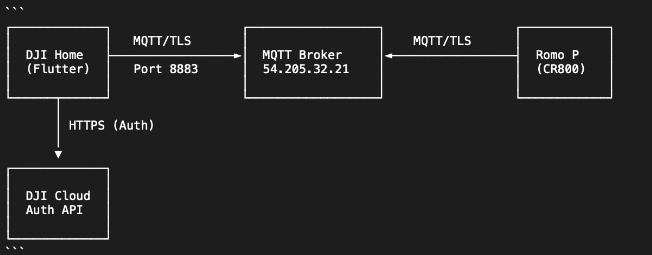
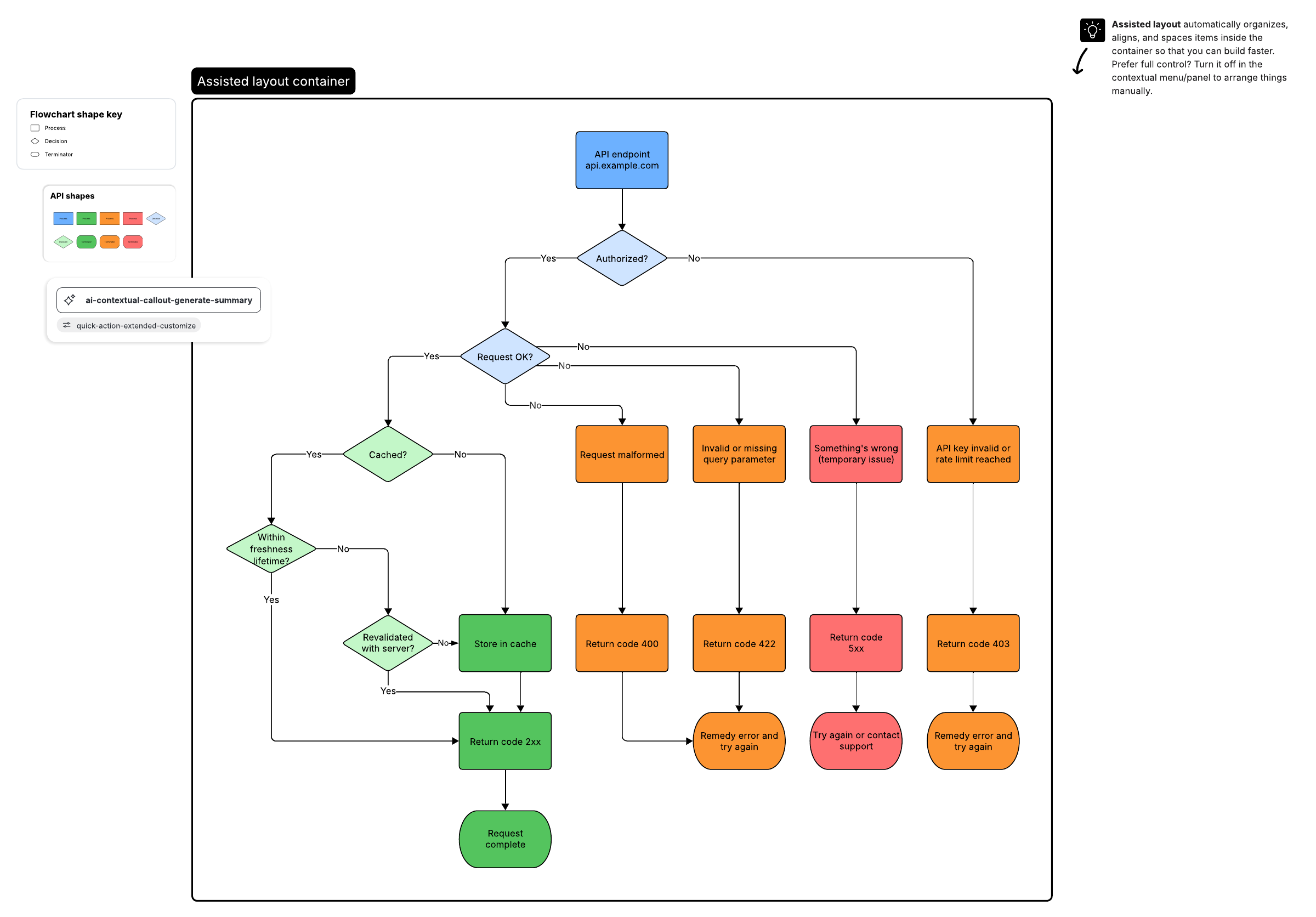
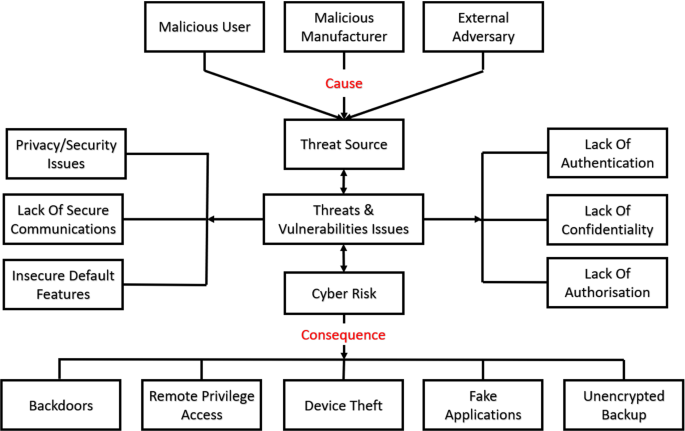
In a twist of fate, a hacker stumbled upon a security loophole that allowed access to 7,000 Romo robovacs. This wasn't a targeted attack but a byproduct of tinkering with device protocols. The hacker, who was exploring ways to enhance the robovac's firmware, found an unsecured API endpoint that granted access to the devices.
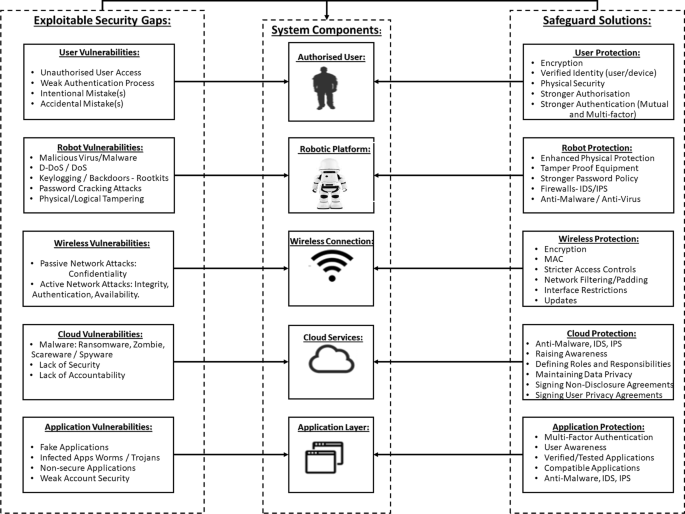
Understanding the Vulnerability
The key issue was an unsecured API endpoint, which lacked proper authentication and encryption. This allowed anyone with knowledge of the endpoint to send commands to the devices. Most consumer robotics rely heavily on APIs to function, making them susceptible to similar vulnerabilities if not properly secured.

Regular updates and strong passwords are crucial for IoT security, with high importance ratings. Estimated data.
Why This Matters: The Broader Implications
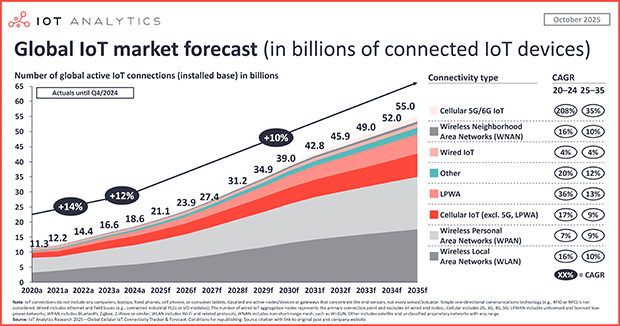
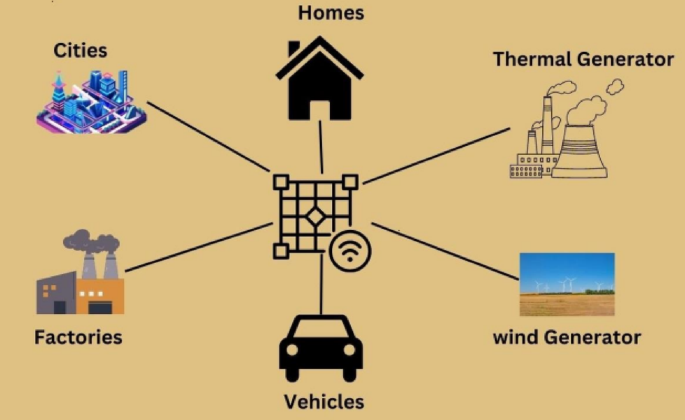
This incident is a wake-up call for the tech industry. With the Internet of Things (IoT) becoming more prevalent, security must be a top priority. Devices like robovacs, smart fridges, and even connected light bulbs are all potential targets for hackers.
The Risks of Inadequate Security
- Data Breaches: Access to devices can lead to data theft.
- Privacy Invasions: Compromised devices can be used for spying.
- Network Vulnerabilities: Insecure devices can serve as entry points into home networks.
How Companies Are Responding
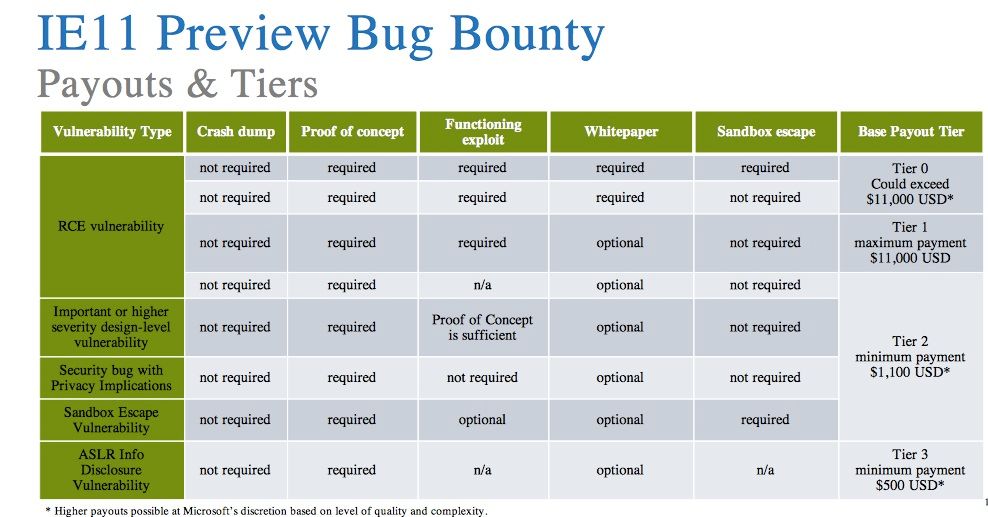
DJI, a leading name in consumer drones, recognized the severity of the situation and offered $30,000 to the hacker as a bounty reward for exposing the vulnerability. This move reflects an increasing trend where companies proactively seek to identify and fix security flaws before they can be exploited.
Bounty Programs: A New Norm
Companies are realizing the value of bounty programs, which incentivize ethical hackers to find and report bugs. This not only helps protect consumer data but also builds trust with users.
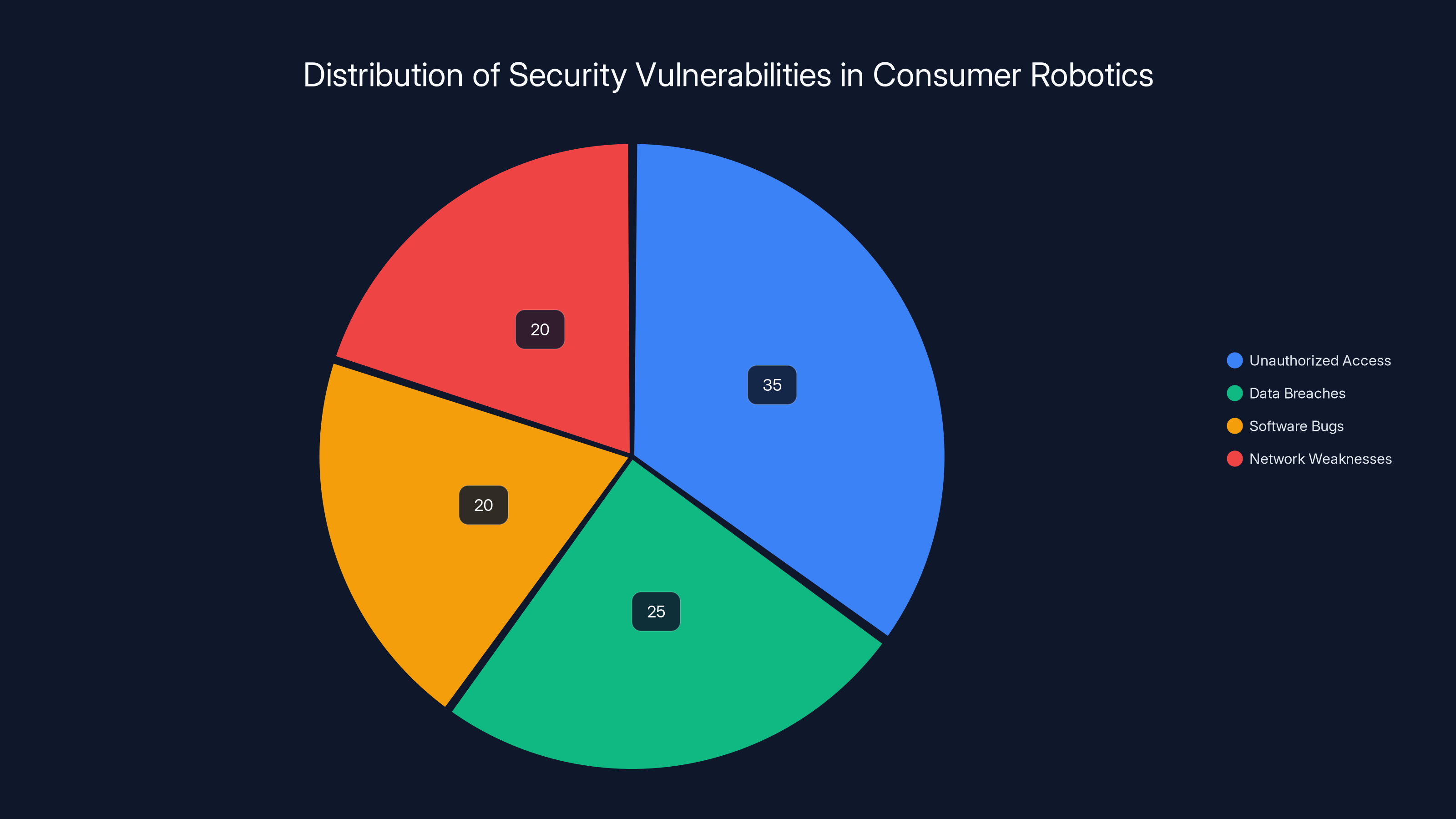
Unauthorized access accounts for the largest share of vulnerabilities in consumer robotics, highlighting the need for improved security measures. (Estimated data)
Best Practices for Developers
Developers have a critical role in ensuring the security of consumer electronics. Here are some best practices:
- Secure APIs: Use authentication and encryption.
- Regular Audits: Conduct security audits to identify vulnerabilities.
- User Education: Inform users about security best practices.
- Patch Management: Regularly update software to fix security issues.
Common Pitfalls and Solutions
Pitfall 1: Weak Passwords
Many IoT devices come with default passwords that users often fail to change. This makes them easy targets for hackers.
Solution: Enforce strong password policies and encourage regular password updates.
Pitfall 2: Delayed Updates
Delays in updating device firmware can leave devices vulnerable to known exploits.
Solution: Implement automatic updates or send regular reminders to users.
Pitfall 3: Poor Encryption Standards
Some devices use outdated or weak encryption methods, making them easier to hack.
Solution: Adopt industry-standard encryption protocols and update them regularly.
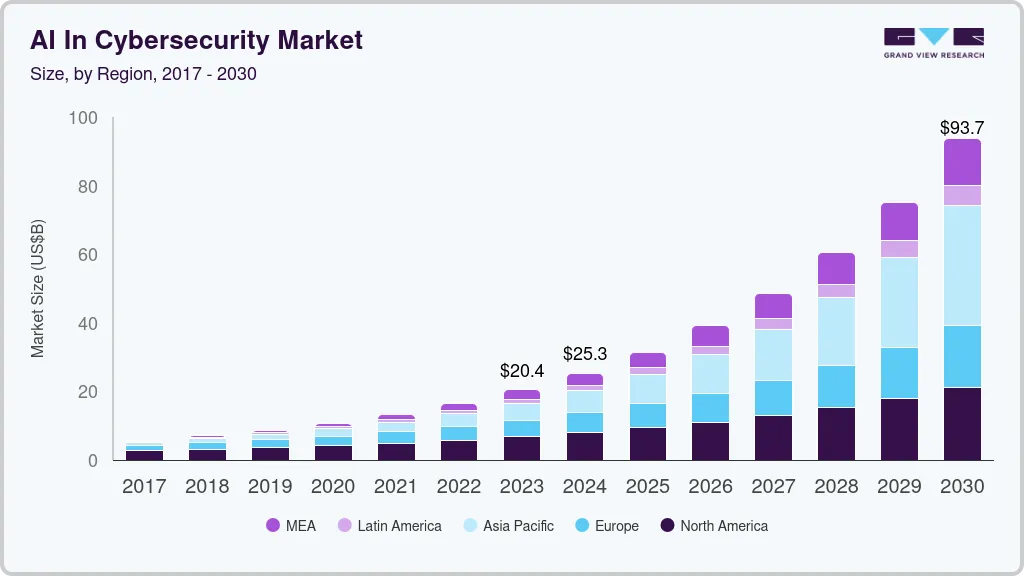
Future Trends in Robotics Security
The future of robotics and IoT security will likely involve more robust regulations and standards. As devices become smarter and more autonomous, the need for comprehensive security measures will increase.
Anticipated Developments
- Stricter Regulations: Governments may impose stricter security standards for consumer electronics.
- AI-Enhanced Security: AI tools will play a crucial role in identifying and mitigating threats.
- Consumer Education: Awareness campaigns to educate users about security practices.

Recommendations for Consumers
Consumers can take several steps to protect their smart devices:
- Change Default Settings: Always change default passwords and settings.
- Enable Two-Factor Authentication: Adds an extra layer of security.
- Stay Informed: Keep up with the latest security news and updates.
Conclusion
The accidental hack of 7,000 Romo robovacs serves as a stark reminder of the vulnerabilities in our ever-connected world. As technology continues to evolve, so too must our approach to security. By adopting best practices, staying informed, and leveraging new technologies, we can help safeguard our devices and data.
FAQ
What is IoT?
Internet of Things (IoT) refers to the network of physical objects—"things"—embedded with sensors, software, and other technologies to connect and exchange data with other devices and systems over the internet.
How can I protect my devices from hacking?
Ensure devices are updated regularly, use strong passwords, and enable two-factor authentication when available.
Why are bounty programs important?
They incentivize ethical hackers to identify and report vulnerabilities before malicious actors can exploit them.
What role does AI play in security?
AI can help identify and respond to security threats more quickly and effectively than traditional methods.
Can I trust my smart devices?
While no device is 100% secure, taking proactive steps can significantly reduce the risk of hacking.
What should I do if I suspect my device has been hacked?
Disconnect it from the network, change passwords, update firmware, and contact the manufacturer for support.
Are there regulations for IoT security?
Regulations vary by region, but there is a growing push for more stringent security standards globally.
How often should I update my devices?
Check for updates at least once a month and apply them as soon as they become available.
Key Takeaways
- The accidental hacking of 7,000 Romo robovacs highlights the critical need for improved security in IoT devices.
- DJI's response with a $30,000 bounty underscores the importance of identifying and fixing vulnerabilities proactively.
- Developers should focus on securing APIs, enforcing strong passwords, and regularly updating firmware.
- Future trends point towards stricter regulations and AI-enhanced security measures in consumer electronics.
- Consumers can enhance device security by changing default settings and staying informed about the latest updates.
Related Articles
- The Disappearance of Apple's 512GB Mac Studio: Uncovering the RAM Shortage [2025]
- Hacking Security Cameras: A New Weapon in Modern Warfare [2025]
- Unmasking Grammarly: Identity Concerns and the Future of AI Writing Assistance [2025]
- The AI Document Revolution: Bridging the Gap Between Hype and Reality [2025]
- Exploring Vibe Coding: Samsung's Future Vision for Galaxy Phones [2025]
- The Ultimate Guide to 16-Inch RTX 5060 Laptop Deals [2025]
![How One Man's Accidental Hack Revealed Vulnerabilities in Modern Robotics [2025]](https://tryrunable.com/blog/how-one-man-s-accidental-hack-revealed-vulnerabilities-in-mo/image-1-1772852636286.jpg)



