Indian Pharmacy Chain Data Breach: How Millions Were Exposed [2025]
In late 2024, one of India's largest pharmacy chains experienced a catastrophic security failure. We're talking about Dava India Pharmacy, the retail arm of Zota Healthcare operating over 2,300 stores nationwide, exposing sensitive health data on hundreds of thousands of customers for months without realizing it.
But here's what makes this breach particularly alarming: it wasn't sophisticated hacking. It was a bug so fundamental, so preventable, that any security engineer would've caught it in a code review. An unauthenticated user could create administrative accounts with full system privileges. That's not a vulnerability. That's an open door with a "Welcome, Attackers" mat.
The exposed data wasn't just usernames or email addresses. We're talking about prescription history, health conditions, medication names, personal health details that people consider deeply private. For a pharmacy customer, that's arguably more sensitive than a credit card number.
Why does this matter? Because pharmacy breaches hit different. Your health records reveal everything: chronic conditions, mental health treatments, reproductive health decisions. This isn't abstract data. This is intimate information about millions of Indians that was sitting in an unprotected database for nearly a year.
In this comprehensive guide, we'll break down exactly what happened, how the vulnerability worked, what data was exposed, and what you need to do if you're affected. We'll also explore the broader implications for India's healthcare security landscape and what this breach reveals about corporate accountability in the digital age.
TL; DR
- Critical Vulnerability: Dava India Pharmacy's platform allowed unauthenticated users to create "super admin" accounts with full system privileges
- Scale of Exposure: Nearly 17,000 online orders linked to over 700,000 customers were exposed across 800+ store locations
- Data Compromised: Health conditions, medications, prescriptions, personal addresses, phone numbers, email addresses, and purchase amounts
- Discovery Timeline: Researcher Eaton Zveare found the bug in late 2024, responsibly disclosed it in August 2025, and the company fixed it by November 2025
- Silver Lining: No evidence of malicious exploitation; payment data and passwords remain secure
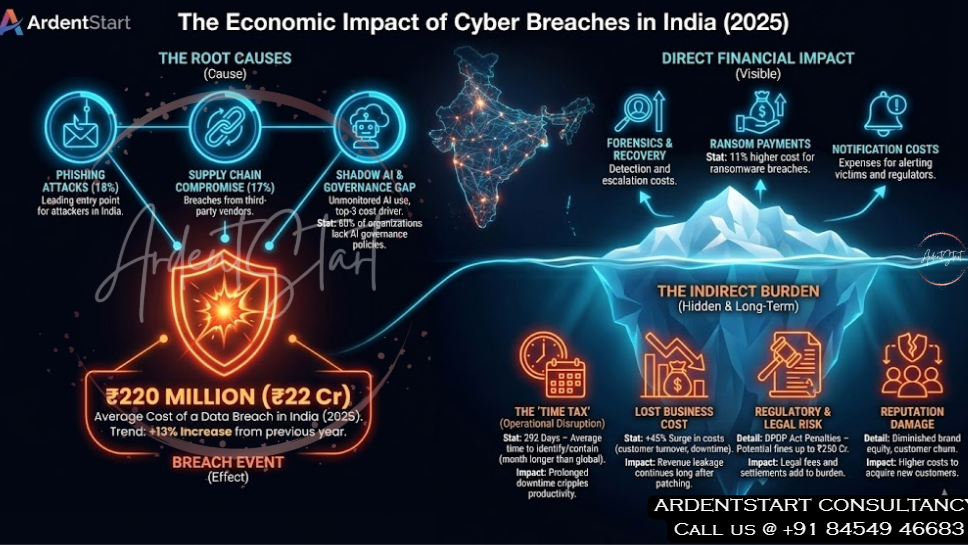
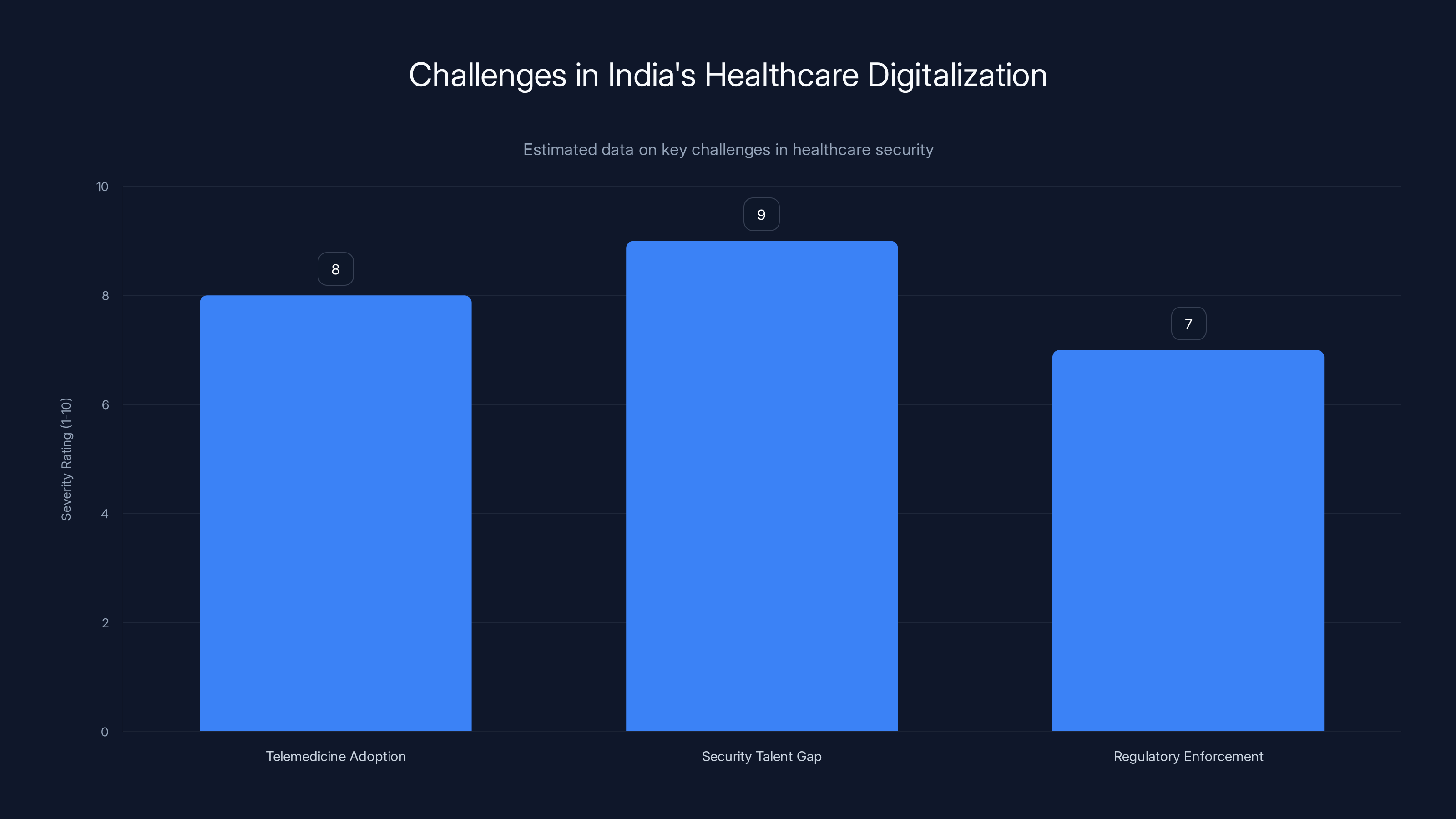
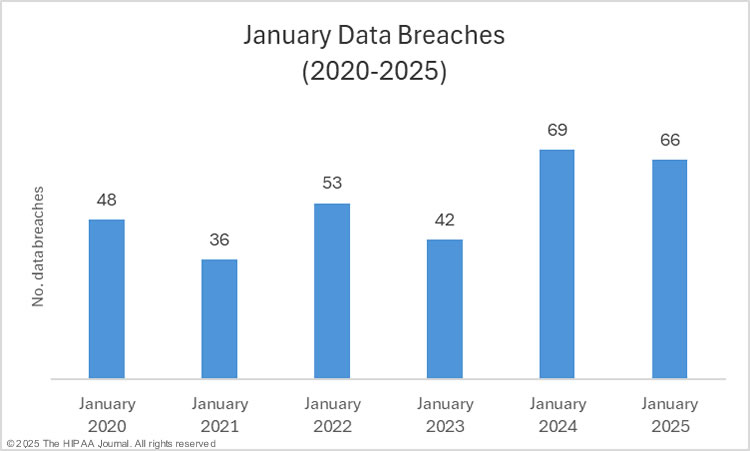
The rapid digitalization of India's healthcare sector faces severe challenges, with a significant security talent gap and regulatory enforcement issues. Estimated data.
What Happened: The Dava India Pharmacy Breach Explained
Let's be clear about what occurred here. On the surface, it sounds technical and abstract. In reality, it was an absolute disaster waiting to happen.
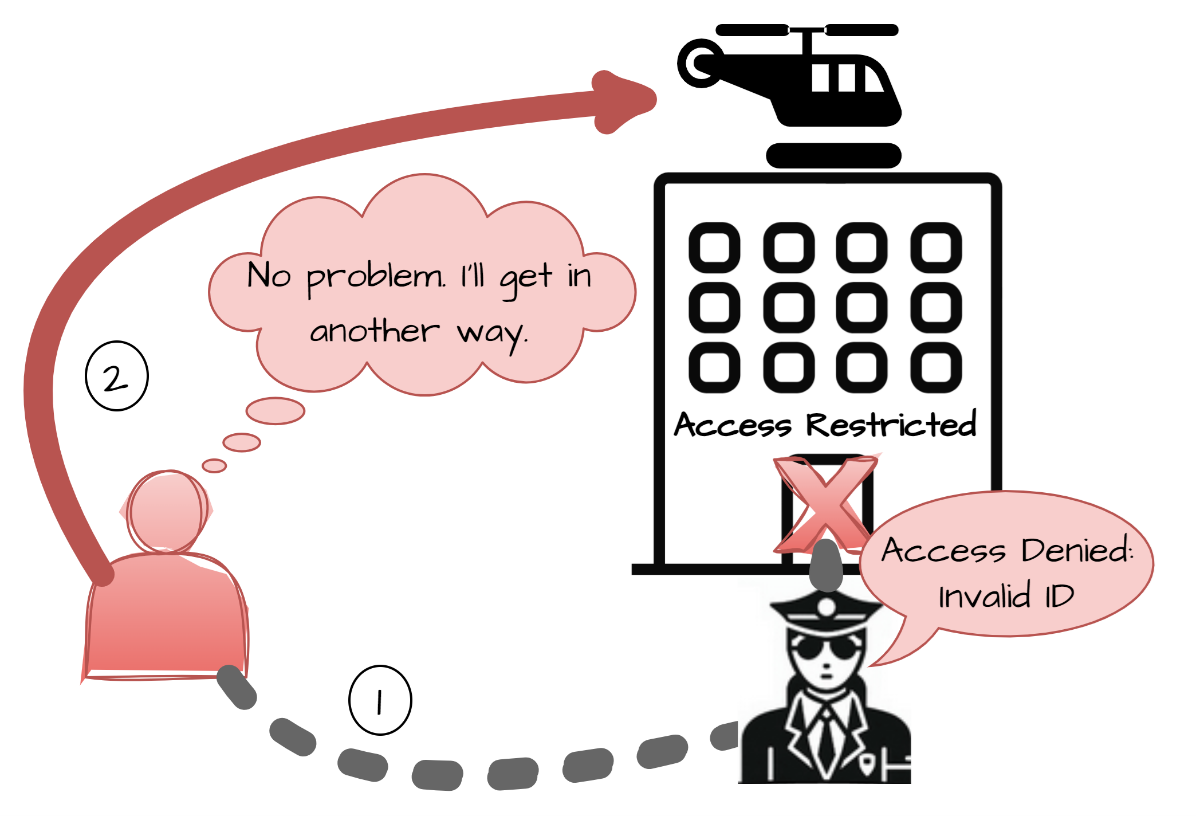
Dava India Pharmacy's online platform contained a critical authentication bypass vulnerability. Picture this: the system had user roles (regular customers, store employees, administrators). The normal flow would require authentication, proper role verification, and authorization checks at every step. Someone should verify: "Are you logged in? Are you supposed to do this action? Do you have permission?"
Instead, the platform skipped those checks. Completely. An unauthenticated attacker could hit specific API endpoints and create admin accounts without logging in, without providing credentials, without anything. The system just... created the account.
This wasn't a subtle logic error. This was missing fundamental security architecture. It's like a bank leaving the vault door unlocked because they forgot to install the lock.
Once you had admin access, the damage scope exploded. You could:
- View customer records: Names, phone numbers, email addresses, home addresses, order history
- Access order details: What medications customers bought, what health conditions they managed, dosage information, purchase dates
- Modify product data: Change drug prices, swap product listings, potentially create ordering chaos
- Alter prescription requirements: Mark prescription-only drugs as over-the-counter or vice versa
- Create fraudulent discounts: Generate coupons, modify prices, create financial losses
- Access internal systems: The breach extended to admin controls across multiple store locations
The breach affected nearly 17,000 documented orders across more than 800 stores. But the actual customer database? Over 700,000 individuals had their information exposed.
Think about that number. Seven hundred thousand people in India had their pharmaceutical history accessible to anyone with five minutes and internet access.
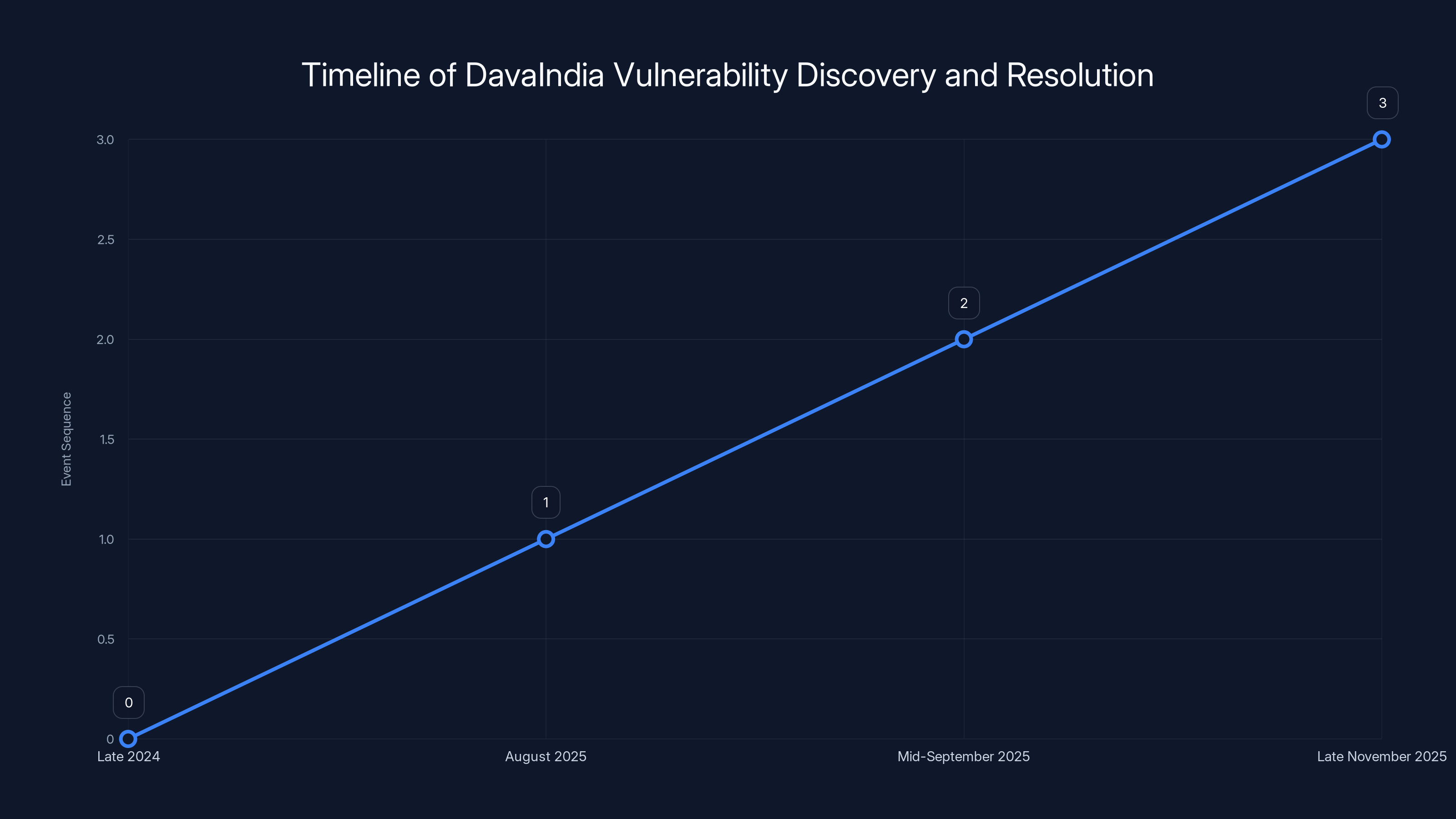
The DavaIndia vulnerability was discovered in late 2024, reported in August 2025, fixed by mid-September 2025, and formally acknowledged in late November 2025.
The Timeline: When and How It Was Discovered
Security researcher Eaton Zveare discovered the vulnerability in late 2024. He wasn't a malicious actor scanning random Indian pharmacy sites. He was conducting responsible security research, testing the platform's defenses, and found the authentication bypass.
Zveare followed ethical disclosure practices. Rather than publishing the vulnerability publicly or exploiting it, he reported it to CERT-In (the Indian Computer Emergency Response Team) in August 2025. This is the proper channel for reporting critical vulnerabilities affecting Indian infrastructure and citizens.
Here's where things get frustrating. CERT-In began the disclosure process. A few weeks passed. In mid-September 2025, Zveare noticed the vulnerability was fixed. He reached out for confirmation that the company had patched the issue.
But Dava India didn't formally acknowledge the fix until late November 2025. That's a three-month lag between patching and acknowledgment. During that time, nobody knew the vulnerability was resolved. The company didn't issue a security update notification. They didn't alert affected customers. They quietly fixed it and moved on.
Zveare's investigation included searching for evidence that malicious actors had exploited the vulnerability before he discovered it. His conclusion: there's no evidence of prior exploitation. That's actually good news, though it doesn't completely eliminate the possibility that someone found the vulnerability silently and didn't advertise their access.
The timeline matters because it shows both responsible disclosure working (the researcher did things right) and corporate accountability failing (the company took months to patch and acknowledge).
Understanding the Vulnerability: Authentication Bypass Explained
Let's dig into the actual technical vulnerability because understanding how it worked helps you recognize these issues in other services you use.
Every web application needs authentication mechanisms. The basic flow is:
- User attempts to access a protected resource
- System asks: "Who are you? Prove it."
- User provides credentials (username, password, token)
- System verifies credentials against a database
- If valid, system creates a session or token
- User can now access resources tied to their account
Authentication bypass vulnerabilities skip steps 2-5. The system grants access without verifying who's asking.
In Dava India's case, the specific vulnerability was likely an unauthenticated API endpoint. APIs (Application Programming Interfaces) are how apps communicate with backend servers. They're like doors into the application's data and functions.
The platform probably had an endpoint like:
/api/admin/create-account or /admin/register
Normally, this endpoint should:
- Check if the requester is authenticated
- Verify the requester has admin privileges
- Validate the request contains required fields
- Create the new admin account only if all checks pass
Instead, Dava India's implementation probably:
- Accepted the request without checking authentication
- Created the admin account immediately
- Didn't verify authorization levels
This is a critical flaw because admin accounts are the master keys. They bypass normal restrictions, access sensitive data, and control system behavior.
Authentication bypass vulnerabilities are surprisingly common. OWASP (the Open Web Application Security Project) consistently ranks broken authentication as one of the top web application security risks. Companies often implement authentication haphazardly, missing edge cases where the system fails to verify identity.
The fix is straightforward in theory: proper authentication checks on every protected endpoint. But execution requires discipline, code review rigor, and security-first development practices. Dava India clearly lacked one or more of these.
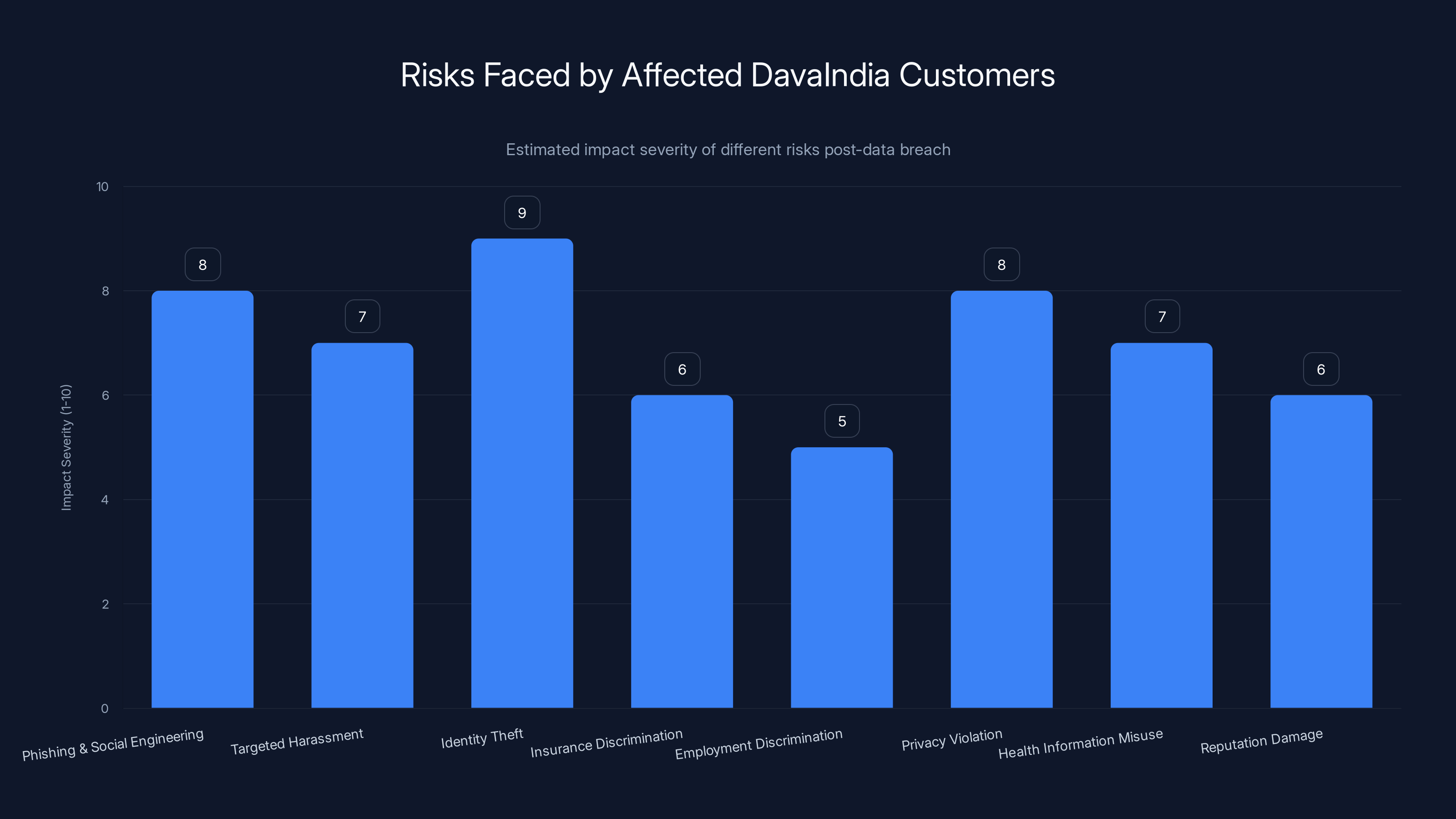
Estimated data showing the severity of different risks faced by DavaIndia customers after the data breach. Identity theft and phishing are among the highest risks.
The Data Exposed: What Information Leaked
Now let's talk about what actually got exposed, because this determines the real-world impact on affected individuals.
The Dava India breach exposed multiple categories of sensitive information:
Personal Identification Data
Full names, phone numbers, email addresses, and mailing addresses. This is foundational PII (personally identifiable information). Combined with other data, it enables identity theft, targeted phishing, social engineering attacks, and unsolicited contact.
For pharmacy customers, having your address in a breach is particularly concerning because it reveals your physical location. Criminals could use this for physical harassment, home robbery targeting specific items (based on medication history), or other in-person attacks.
Health and Medical Information
This is the most damaging part. The breach exposed:
- Specific medications: Names of drugs customers purchased, which directly indicates health conditions
- Health conditions: In some cases, explicit diagnoses or health status information
- Purchase history: Dates and amounts paid, creating a timeline of medical treatment
- Prescription information: Whether purchases required doctor authorization
Medical data is extraordinarily sensitive because it reveals intimate details about people's lives. A diabetic customer's purchase of insulin is straightforward diagnosis. Someone buying erectile dysfunction medication has different implications. A customer purchasing anxiety medication reveals mental health struggles.
Indian law recognizes this sensitivity. The Information Technology Act, 2000, and the upcoming Digital Personal Data Protection Act, 2023, provide stricter protections for health information than general personal data. This breach potentially violated multiple regulatory requirements.
Financial Information
The breach exposed the total amount paid per order. While payment card details weren't included (which is somewhat fortunate), seeing purchase amounts combined with medication names creates a financial profile. It shows how much customers spend on healthcare, which medications they prioritize financially, and purchasing patterns.
Business Data
The vulnerability extended to internal systems across 800+ stores. This means:
- Pricing information: Real-time drug prices, margins, pricing strategies
- Inventory data: What medications stores had in stock
- Employee information: Potentially staff names, roles, schedules
- Administrative controls: Systems for managing stores, operations, accounting
This business data is valuable to competitors and bad actors. Competitors could optimize pricing. Criminals could identify high-value targets for theft. The exposure of operational data suggests the breach went well beyond customer records.
Scale and Numbers
Let's quantify this:
- 17,000+ documented online orders: These had complete linked customer records
- 700,000+ affected customers: Nearly three-quarters of a million people
- 800+ store locations impacted: Representing significant geographic spread
- Duration: Several months from discovery date backwards (exact duration unclear, but at least since late 2024)
To put this in perspective, India has approximately 1.4 billion people. Dava India's 700,000 exposed customers represent a substantial national breach affecting roughly 0.05% of India's population, or about 1 in 2,000 Indians.

Impact on Affected Customers
If you were a Dava India customer, this breach creates real risks:
Immediate Risks
Phishing and Social Engineering: Criminals have your name, phone number, email, and health information. They can craft convincing messages claiming to be from Dava India, healthcare providers, or authorities, asking you to "verify information" or "update payment details."
Targeted Harassment: Health data combined with contact information enables targeted harassment based on health conditions. It's unfortunately common for people to face discrimination based on medical information.
Identity Theft: Your personal information can be used to open accounts, make fraudulent purchases, or take out loans in your name.
Medium-term Risks
Insurance Discrimination: If insurance companies obtained this data, they could use health information to deny coverage, increase premiums, or exclude certain conditions.
Employment Discrimination: Employers discovering health conditions through breached pharmacy data could discriminate in hiring, promotion, or termination decisions.
Privacy Violation: Your medical history, perhaps something deeply personal, is now in criminal databases accessible to unknown parties.
Long-term Risks
Health Information Misuse: Detailed health records could be sold to data brokers, pharmaceutical companies for targeted marketing, or used for research without consent.
Reputation Damage: If health information becomes public, it could affect social and family relationships.
Regulatory Consequences: As healthcare privacy laws strengthen in India, breaches create compliance liabilities for customers as well as companies.

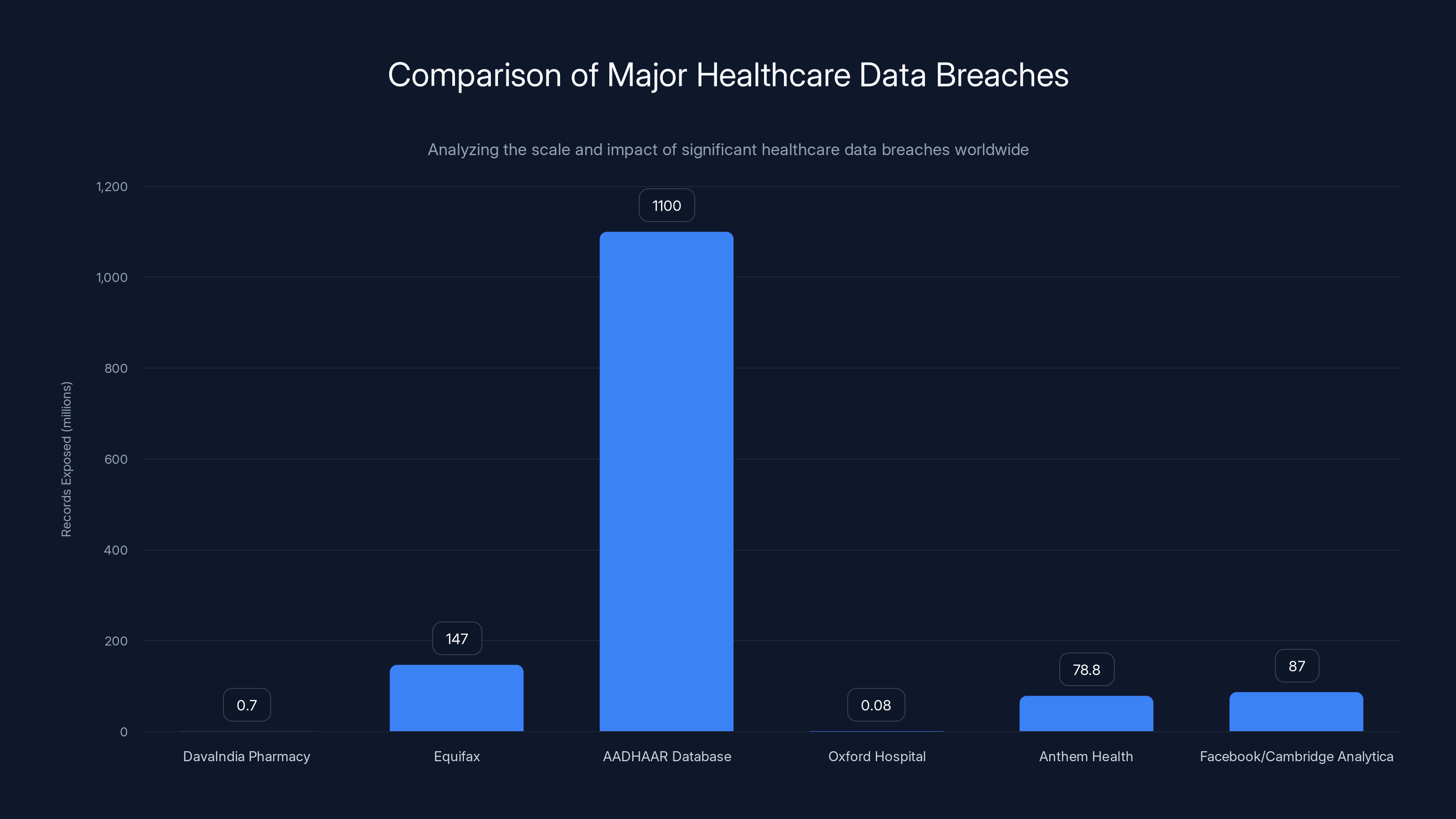
The AADHAAR database breach had the potential to affect the entire Indian population, making it the largest in terms of records at risk. In contrast, the DavaIndia breach, while significant, exposed a smaller number of records.
Why This Matters: Healthcare Security in India
India's healthcare sector is rapidly digitalizing. Telemedicine platforms, online pharmacies, health record systems, and digital prescription services are becoming mainstream. The COVID-19 pandemic accelerated this transformation by nearly a decade.
But this rapid digitalization happened without corresponding security improvements. Many Indian healthcare startups and companies prioritize features and growth over security fundamentals. The Dava India breach perfectly illustrates this dynamic.
The Regulatory Context
India didn't have comprehensive healthcare data protection laws until recently. The Digital Personal Data Protection Act, 2023, is still being implemented. Before that, healthcare data protection relied on:
- Information Technology Act, 2000: General privacy provisions, not healthcare-specific
- HIPAA-equivalent guidance: None. India has no HIPAA equivalent
- National Health Authority guidelines: For government systems, not mandatory for private companies
- Voluntary compliance: Most healthcare companies self-regulated
This regulatory gap meant companies like Dava India had minimal legal pressure to implement security controls. There were no mandatory security audits, no required penetration testing, no enforcement mechanisms for poor security practices.
The new DPDP Act changes this, but implementation is still underway. Many companies haven't adapted their practices yet.
Industry Security Posture
The Dava India breach revealed a broader problem: many Indian healthcare companies lack basic security practices. The authentication bypass vulnerability is elementary. Any competent security team would catch this in code review. Any company conducting regular penetration testing would discover it immediately.
Dava India apparently had neither. This suggests:
- No security code reviews: Developers weren't reviewing each other's security practices
- No penetration testing: Regular security testing would have revealed this
- No security training: Developers didn't understand authentication best practices
- No security culture: Security wasn't a priority in development decisions
These aren't unique to Dava India. Many Indian healthcare companies operate with similar security postures. This breach is just the one that got discovered and publicized.
What This Means for Patients
Patients using Indian healthcare apps and online pharmacies face elevated risk. When choosing digital health services, you're trusting companies with profoundly sensitive information without clear security assurances.
You can't easily verify if a company conducts security audits. You can't test their authentication mechanisms. You can't verify data encryption or access controls. You're essentially trusting the company's integrity and competence, often without evidence of either.
This imbalance of power is a fundamental problem in healthcare digitalization. The company holds your sensitive data. You have little visibility into how they protect it.

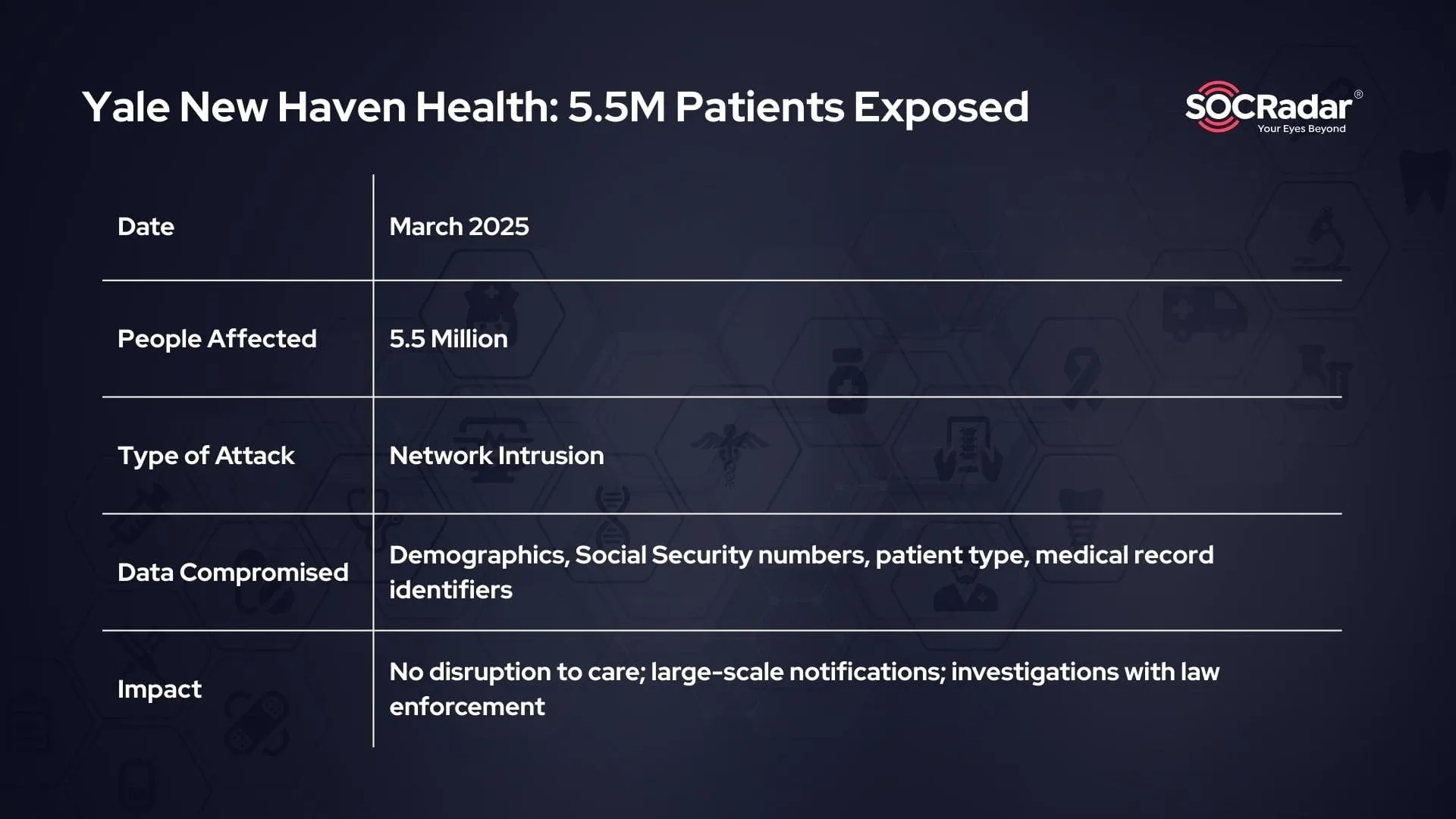
Comparison with Other Major Healthcare Breaches
Let's put this breach in context by comparing it to other significant healthcare data breaches worldwide.
| Breach | Organization | Year | Records Exposed | Type of Data | Consequences |
|---|---|---|---|---|---|
| Dava India Pharmacy | Zota Healthcare (India) | 2024-2025 | 700,000+ | Prescriptions, health conditions, PII | Regulatory action pending, customer notification delayed |
| Equifax | Credit Reporting Agency (US) | 2017 | 147 million | SSN, DOB, addresses, credit info | $700M+ settlement, CISO resigned, multiple lawsuits |
| AADAAR Database | UIDAI (India) | 2018 | 1.1 billion (entire database at risk) | Biometrics, addresses, phone numbers, email | Government investigation, 48 arrests, regulatory reforms |
| Oxford Hospital | NHS Trust (UK) | 2017 | 80,000 | Medical records, appointment data | £30K fine, compliance orders |
| Anthem Health | Insurance Company (US) | 2015 | 78.8 million | Health insurance info, SSN, health records | $115M settlement, largest US healthcare breach |
| Facebook/Cambridge Analytica | Tech/Analytics (Global) | 2018 | 87 million (estimated) | Behavioral data, personal profiles, health inferences | $5B FTC fine, regulatory changes, public outcry |
The Dava India breach is significant but not unprecedented in scale. The Equifax breach affected nearly 150 million people. The AADHAAR database breach (if exploited fully) could have affected India's entire population.
What makes Dava India notable:
- Healthcare sensitivity: Pharmacy data is more personally sensitive than most breaches
- Prevention difficulty: This vulnerability was preventable with basic security practices
- Disclosure timing: The company took months to acknowledge the breach publicly
- Indian context: It demonstrates security gaps in India's rapid healthcare digitalization
Compared to international healthcare breaches, Dava India's response was slower. Major US healthcare breaches result in immediate notification, regulatory investigation, and often substantial fines. Dava India's breach took months to patch and even longer to acknowledge formally.

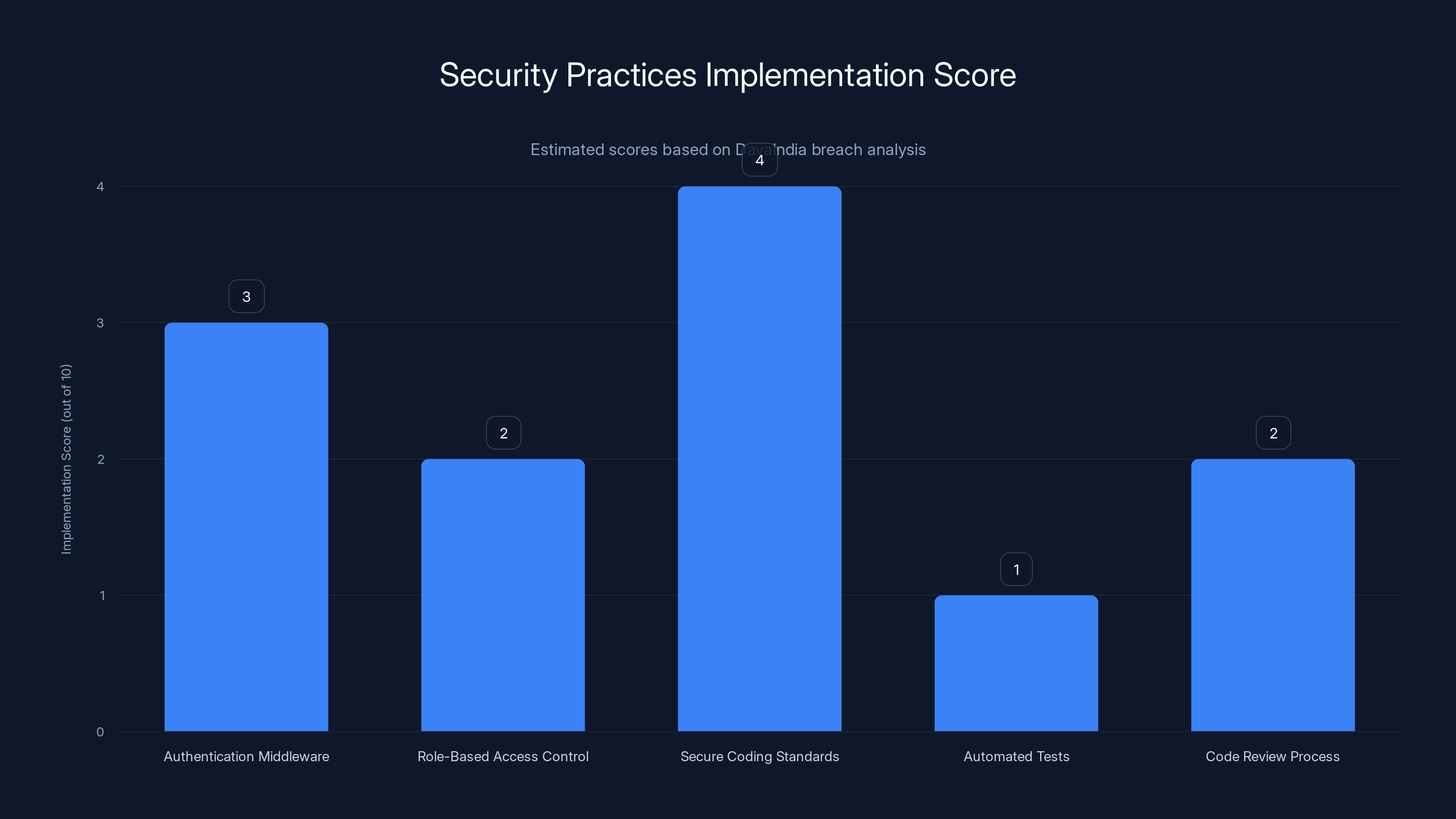
The chart estimates DavaIndia's implementation of key security practices, highlighting significant gaps in authentication middleware and role-based access control. Estimated data based on breach analysis.
Security Lessons: What Should Have Been Different
Examining the Dava India breach, several security practices would have prevented it entirely.
Secure Development Practices
1. Authentication-First Architecture
Every protected endpoint should require authentication verification. This shouldn't be optional. The codebase should include authentication middleware that runs on every request. Developers shouldn't have to remember to add authentication checks; they shouldn't be able to skip them.
Dava India probably had authentication implemented somewhere, but not universally applied. This suggests:
- No authentication middleware enforcing checks globally
- Developers manually adding authentication where they remembered
- No automated tests verifying authentication requirements
- No code review process catching missing authentication
2. Role-Based Access Control (RBAC)
Once authenticated, systems should verify authorization. Just because you're logged in doesn't mean you should access every resource. Admin functions should only work for users with admin roles.
Dava India apparently didn't check roles before allowing admin account creation. The fix required implementing proper RBAC:
- Define clear roles: customer, employee, manager, admin
- Require role verification before sensitive operations
- Implement principle of least privilege: users get minimum permissions needed
- Log all privilege-escalating actions for audit trails
3. Secure Coding Standards
Developer training matters. Developers need to understand authentication concepts, common vulnerabilities, and secure coding practices. A trained developer would recognize that admin account creation requires authentication and authorization checks.
Dava India's developers apparently didn't have this training. The company should have:
- Provided secure coding training for all developers
- Established coding standards requiring authentication on protected endpoints
- Created code templates showing authentication patterns
- Implemented linters and static analysis tools catching authentication issues
Testing and Verification
4. Security Code Review
Peer review catches mistakes. Before merging code, developers should have someone review it specifically for security issues. Authentication bypass vulnerabilities are obvious during code review.
Dava India apparently didn't conduct security-focused code reviews. The fix requires:
- Designating security champions who review all changes
- Creating security review checklists for common vulnerabilities
- Requiring at least one security-reviewed approval before merging
- Blocking merges of authentication-related changes without security review
5. Penetration Testing
Regular penetration testing would discover this vulnerability quickly. A security tester would attempt to create admin accounts without authentication, find it works, and report it immediately.
Dava India apparently didn't conduct penetration testing, or conducted it infrequently. The practice should include:
- Quarterly internal penetration tests by security team
- Annual third-party penetration testing by external firms
- Specific testing of authentication mechanisms
- Testing of API endpoints for unauthorized access
- Following up on findings with fixes and retesting
6. Automated Security Testing
Automated tools can catch vulnerabilities continuously. Static analysis tools can identify missing authentication checks. Dynamic analysis can test for authorization bypasses. Dependency scanners can identify vulnerable libraries.
Dava India probably didn't implement automated security testing, which would have:
- Scanned code for missing authentication checks during development
- Run automated tests on every code change
- Identified the vulnerable endpoint before deployment
- Prevented the issue reaching production
Operational Security
7. Responsible Disclosure Program
Criminals aren't the only ones discovering vulnerabilities. Security researchers do too. Companies need processes to receive, manage, and respond to vulnerability reports.
Dava India apparently had no established disclosure process. The researcher had to report through CERT-In instead of directly to the company. Best practices require:
- Published security.txt file with disclosure contact
- Dedicated security email (security@company.com)
- Published process for reporting vulnerabilities
- Commitment to respond within specific timeframes
- Commitment to not prosecute good-faith researchers
8. Incident Response Planning
Once a vulnerability is discovered, companies need rapid response procedures. Patch development, testing, deployment, and customer notification should follow a practiced process.
Dava India took months to patch and acknowledge the issue, suggesting no incident response plan. Proper procedures would include:
- Incident response team identification
- Rapid assessment of vulnerability severity
- Expedited patching and testing procedures
- Coordinated deployment across systems
- Customer notification within days, not months
- Public acknowledgment and transparency
Data Protection
9. Encryption and Access Controls
Even if the vulnerability hadn't existed, encrypting sensitive data and restricting admin access limits damage. Customers' health information should be encrypted, with decryption keys stored separately from the database.
Admin accounts shouldn't access customer data unless absolutely necessary. Queries accessing sensitive information should be logged and audited.
10. Data Minimization
Storing only necessary data reduces breach impact. Dava India probably stored customers' full names, complete addresses, and full medication lists. Could they have reduced this?
- Use customer IDs instead of names in some contexts
- Store only essential address information
- Separate medication history from customer identity
- Limit admin access to aggregate data rather than individual records
Legal and Regulatory Implications
The Dava India breach implicates multiple Indian laws and regulations. Understanding the legal landscape helps contextualize accountability and requirements.
Digital Personal Data Protection Act, 2023
India's new DPDP Act applies to any organization collecting personal data of Indian residents. Key requirements include:
Consent-Based Processing: Organizations must obtain explicit consent before collecting health data. Dava India collected health information when customers purchased medications. Did they have explicit consent to store and process this data?
Data Processing Rules: Organizations must process data in accordance with stated purposes. If Dava India stated it only processes data for order fulfillment, storing it broadly for other purposes violates the act.
Security Obligations: Organizations must implement reasonable security measures to protect personal data. Authentication bypass vulnerabilities fail this requirement.
Breach Notification: Organizations must notify data principals "without unreasonable delay" of breaches affecting personal data. Dava India took months to acknowledge the breach, potentially violating notification requirements.
Data Rights: Individuals have rights to access their data, request corrections, delete data, and obtain data portability. Organizations must fulfill these rights within 30 days.
Penalties: The act provides penalties up to 500 crore rupees (approximately $60 million) for certain violations. Breaches involving security failures could trigger maximum penalties.
Information Technology Act, 2000
India's older IT Act also applies:
Section 43A: Failure to protect personal data through negligence can result in damages up to 5 crore rupees (approximately $600,000) per breach. The authentication bypass represents clear negligence in protecting data.
Section 66: Unauthorized access and data theft are criminal offenses punishable by imprisonment up to three years and/or fines up to 5 lakh rupees (approximately $6,000).
Section 72: Disclosure of information in breach of confidentiality is an offense punishable by imprisonment up to two years or fines up to 1 lakh rupees (approximately $1,200).
Other Applicable Laws
Bharatiya Nyaya Sanhita, 2023: India's new criminal code includes provisions on unauthorized access to computer systems, applicable to the authentication bypass vulnerability.
National Health Authority Guidelines: While not law, NHA guidelines for healthcare data protection apply to Dava India. Compliance failures could affect regulatory standing.
Right to Information Act, 2005: The public and regulators can request information about the breach, Dava India's response, and remediation measures.
Regulatory Enforcement
Multiple Indian regulators could take action:
Data Protection Board: The new DPDP framework includes a Data Protection Board that can investigate complaints and issue enforcement orders.
MEITY: The Ministry of Electronics and Information Technology can direct organizations to improve security practices.
RBI: If Dava India processes any payment data, the Reserve Bank of India could take action.
State Consumer Protection Authorities: Affected customers can file complaints with consumer protection agencies seeking compensation.
Criminal Investigation: If evidence shows the company intentionally neglected security or covered up the breach, criminal prosecution is possible.

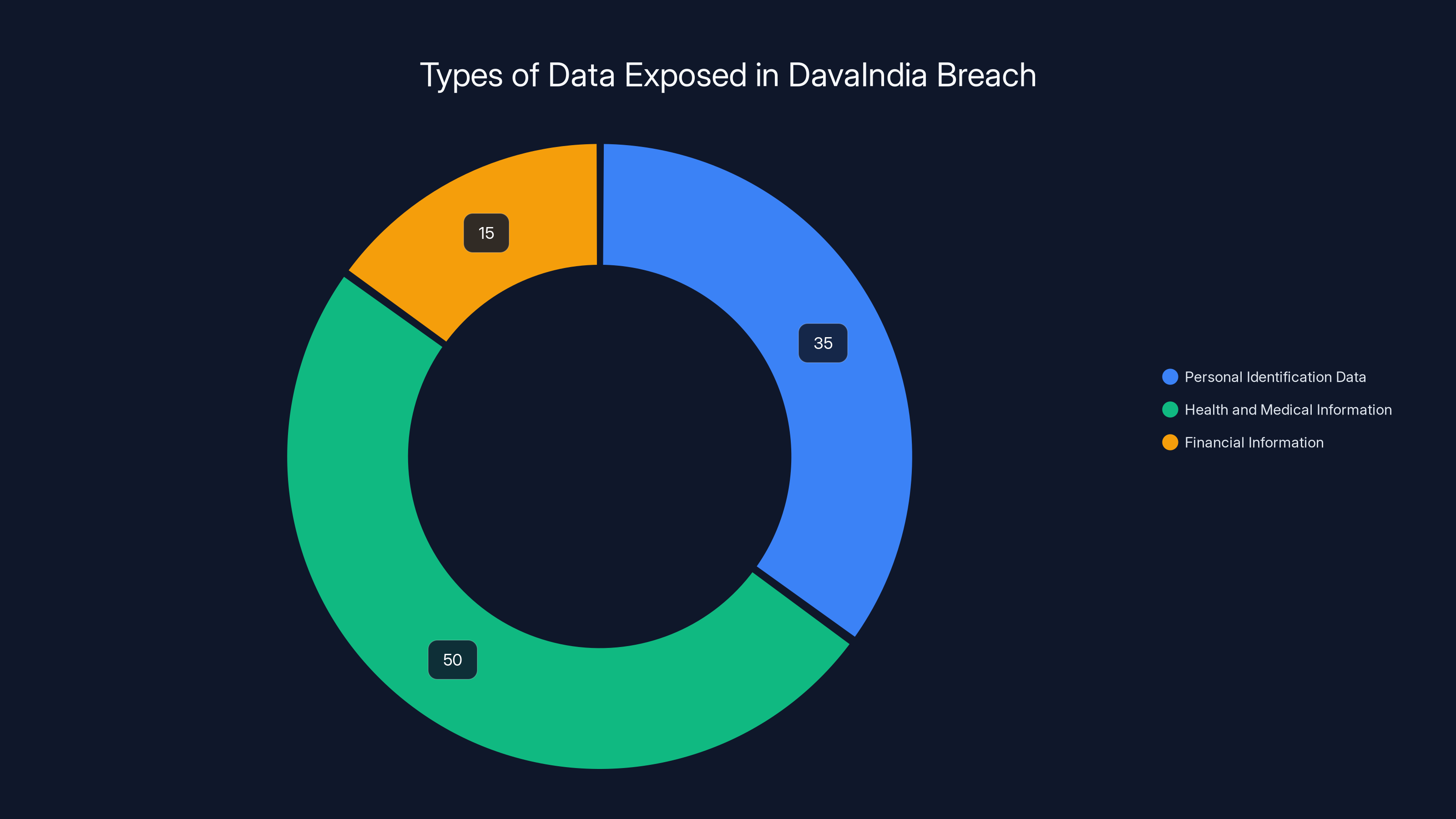
Health and medical information constituted the largest portion of the data exposed in the DavaIndia breach, highlighting significant privacy concerns. Estimated data.
Steps to Protect Yourself
If you're concerned about exposure from the Dava India breach, several protective measures reduce your risk.
Immediate Actions
1. Change Your Password
If you had an account on Dava India's platform, change your password immediately. Use a strong, unique password:
- Minimum 16 characters
- Mix of uppercase, lowercase, numbers, and special characters
- No personal information or dictionary words
- Different from passwords on other accounts
If you reused your Dava India password elsewhere, change those accounts too.
2. Monitor Credit and Banking
Your personal information is in criminal databases. Monitor your credit for fraudulent accounts:
- Check your credit score through CIBIL or other Indian credit bureaus
- Request your credit report and look for unfamiliar accounts
- Set up fraud alerts with your bank
- Monitor bank and credit card statements for unauthorized transactions
- Consider a credit freeze if you're concerned about identity theft
3. Beware of Phishing
Criminals will use your exposed information to craft convincing phishing messages. Be suspicious of:
- Messages from "Dava India Pharmacy" asking to verify account information
- Health-related messages claiming issues with your prescriptions
- Financial messages about "unusual transactions"
- Messages asking you to click links or provide information
When in doubt, contact Dava India directly through their official website, not links in suspicious messages.
Medium-term Actions
4. Use Identity Theft Protection
Services like Aadhar Locker help secure your digital identity in India. Identity theft protection services monitor for misuse of your personal information.
5. Secure Your Health Information
With your pharmacy history exposed, protect future health information:
- Use privacy-focused healthcare providers when possible
- Request data minimization when using online health services
- Ask about security practices before providing information
- Keep physical pharmacy records secure
- Avoid sharing health information online unless necessary
6. Consider Your Other Online Services
If you used the same password on other accounts, or the same email address, those accounts are at risk. Audit your online presence:
- List all accounts using your breached email
- Change passwords on all accounts
- Enable two-factor authentication where available
- Review account recovery options
Long-term Actions
7. Understand Your Rights
Under India's new DPDP Act, you have rights to:
- Access your data: Request what information companies store about you
- Data correction: Request changes to inaccurate information
- Data deletion: Request companies delete your data
- Data portability: Request your data in portable formats
Exercise these rights with companies handling your data.
8. Advocate for Better Security
Personally, you can:
- Demand security transparency from companies
- Choose services with strong security practices
- Report suspected vulnerabilities responsibly
- Support regulatory efforts for healthcare data protection
- Educate others about healthcare data risks
9. Monitor for Regulatory Developments
Follow Indian healthcare and data protection regulations as they evolve. The DPDP Act is still being implemented. New regulations will establish clearer expectations for healthcare companies.
The Broader Healthcare Security Landscape in India
Dava India isn't an isolated incident. It represents systemic challenges in India's healthcare digitalization.
The Rapid Digitalization Challenge
India's healthcare sector is transforming rapidly. Telemedicine adoption increased from 5% pre-COVID to 45% post-COVID. Online pharmacies are becoming mainstream. Electronic health records are proliferating. Hospital management systems are going cloud-based.
But this speed creates security gaps. Companies race to launch features before implementing security. Venture capital investors prioritize growth metrics over security spending. Hiring security experts is expensive and difficult in India's emerging security market.
The result: multiple companies probably have vulnerabilities similar to Dava India's. They just haven't been discovered and publicized yet.
Security Talent Gaps
India lacks cybersecurity talent. Studies suggest a shortage of 500,000+ security professionals. Healthcare companies struggle to hire experienced security engineers.
Without security expertise, companies make fundamental mistakes:
- Developers without security training build insecure code
- Architects without security experience design unsafe systems
- Managers without security knowledge underestimate risks
- Organizations lack the institutional knowledge of security best practices
Building security maturity takes years. Most Indian healthcare companies are still in early stages.
Regulatory Enforcement Gaps
Even with new regulations, enforcement is challenging. India's regulatory bodies are under-resourced relative to the technology sector. The Data Protection Board is new and still building capacity. State consumer protection authorities handle healthcare complaints alongside thousands of other complaint types.
This enforcement gap creates moral hazard: companies know regulatory response will be slow and limited. The incentive to implement security decreases when consequences seem distant.
Investment in Security
Healthcare companies often treat security as a cost center rather than value driver. IT budgets are slashed, security teams are minimized, and security spending competes with feature development for funding.
Companies that view security as enabling trust, reducing liability, and supporting growth invest appropriately. But many Indian healthcare startups don't have this maturity yet.
International Comparisons
Compare India's healthcare security to mature markets:
United States: Hospitals must comply with HIPAA, which mandates security standards, audit requirements, breach notification, and significant penalties. Healthcare data breaches result in FTC investigations, public notification, and often substantial fines. The regulatory environment enforces security.
European Union: GDPR applies to healthcare data with strict requirements, mandatory data protection officers, privacy by design, and fines up to 4% of global revenue. Every healthcare organization must meet these standards or face enforcement.
Singapore: Healthcare data is regulated under Personal Data Protection Act. Singapore's health system is digitally advanced with strong security standards. Regular audits ensure compliance.
India: Until recently, no comprehensive healthcare data protection law existed. The new DPDP Act is still being implemented. Enforcement is limited. Most healthcare companies operate with minimal regulatory pressure.
India is moving toward international standards, but currently operates with significantly less regulatory oversight than developed markets.
Future of Healthcare Data Security in India
The Dava India breach will likely accelerate several developments in Indian healthcare security.
Regulatory Evolution
The DPDP Act will be refined through court cases and regulatory guidance. Expected developments include:
- Clearer security standards for healthcare organizations
- Mandatory penetration testing requirements
- Specific breach notification timeframes
- Enhanced penalties for security failures
- Requirements for data protection officers
Healthcare-specific regulations may also emerge, establishing baseline security standards for telemedicine platforms, online pharmacies, and health record systems.
Industry Consolidation
Larger, more established healthcare companies with resources for security will acquire smaller startups lacking security infrastructure. This consolidation could raise the average security maturity of healthcare companies.
Alternatively, startups might struggle to afford security improvements and shut down, reducing competition but potentially limiting innovation.
Security-First Startups
A new generation of healthcare startups might prioritize security from inception. Privacy-first telemedicine platforms, encrypted health record systems, and decentralized pharmacy networks could emerge.
These security-focused alternatives might command premium pricing, positioning security as a competitive differentiator.
Technology Solutions
Technological improvements could reduce vulnerability classes:
- Zero-Trust Architecture: Rather than trusting authenticated users implicitly, systems verify authorization for every action
- Encryption Everywhere: End-to-end encryption for healthcare data, even at rest
- Blockchain for Health Records: Decentralized, immutable health records reducing single points of failure
- AI-Driven Security: Machine learning systems detecting unusual access patterns and potential breaches
International Standards
As Indian healthcare companies expand internationally, they'll need to comply with international security standards. Companies serving Indian patients while processing data in AWS, Azure, or other cloud platforms must meet GDPR, HIPAA, and other international requirements.
This compliance pressure will gradually raise security standards across Indian healthcare companies.
What Companies Can Learn from Dava India
Beyond just healthcare companies, all organizations can learn from Dava India's failure.
Authentication is Non-Negotiable
Authentication is the foundation of application security. Every protected endpoint must verify the user's identity. This isn't optional. It isn't a nice-to-have. It's fundamental.
Implement global authentication middleware that runs on every request, making it impossible to forget authentication checks. Use frameworks and libraries that enforce authentication by default.
Security Debt is Real Debt
When developers skip security practices to ship features faster, they accumulate security debt. The bill comes due eventually, usually in the form of breaches.
Treating security debt seriously means:
- Scheduling time for security improvements
- Refactoring insecure code before it reaches production
- Making security part of routine development, not an afterthought
- Measuring and reducing security debt like technical debt
Security is Everyone's Responsibility
The CTO can't fix security alone. The security team can't fix it without developer buy-in. The CEO can't fix it without budget allocation. Security requires buy-in from:
- Executives: Allocating budget and treating security as priority
- Managers: Scheduling time for security work and enforcement
- Developers: Building security into code and practicing secure coding
- Dev Ops/SRE: Implementing secure deployment and infrastructure
- Security Teams: Defining standards and conducting assessments
- Employees: Following security policies and reporting concerns
Responsible Disclosure Works
When researchers can report vulnerabilities responsibly without fear of prosecution, vulnerabilities get fixed. Eaton Zveare reported the vulnerability through proper channels. The company was able to fix it before criminals likely exploited it.
Create responsible disclosure programs, respond to researchers professionally, and never prosecute good-faith security researchers.
Transparency Builds Trust
Dava India's delayed acknowledgment of the breach damaged trust. Transparency about security incidents, even when uncomfortable, preserves customer trust better than cover-ups.
Best practices include:
- Prompt notification of affected users
- Clear explanation of what happened
- Honest assessment of what data was exposed
- Description of remediation measures taken
- Commitment to prevent recurrence
- Availability for customer questions
Invest in Security Culture
Security isn't a technical problem. It's an organizational culture problem. Companies where security is valued:
- Hire security-conscious developers
- Train employees on security practices
- Review code for security issues
- Conduct regular penetration testing
- Have incident response plans
- Celebrate security improvements
- View security as competitive advantage
Building this culture takes time but creates lasting security improvements.

FAQ
What exactly was the vulnerability in Dava India's system?
The platform had an authentication bypass vulnerability in an API endpoint that created administrative accounts. Unauthenticated users could submit requests to create admin accounts without providing credentials or verification, receiving full system privileges. This violated basic security principles requiring authentication on all protected endpoints. Once an attacker had admin access, they could view customer records, modify product listings, create fraudulent discounts, and access internal business systems across 800+ store locations.
How many customers were affected by the Dava India breach?
Approximately 700,000 customers had their data exposed through the vulnerability. The breach specifically documented nearly 17,000 online orders with complete linked customer records, but the actual customer database accessible through the vulnerability was significantly larger. The breach affected customers across 800+ Dava India store locations nationwide, making it one of India's largest pharmacy-related data breaches.
What personal information was exposed in the Dava India breach?
The exposed data included full names, phone numbers, email addresses, mailing addresses, payment amounts, complete medication history, health conditions (in some cases), and prescription information. Since it was a pharmacy database, the medication history directly reveals health conditions and medical treatments. This health information is particularly sensitive and protected under Indian healthcare privacy regulations.
When was the Dava India vulnerability discovered and fixed?
Security researcher Eaton Zveare discovered the vulnerability in late 2024 and responsibly reported it to India's CERT-In (Computer Emergency Response Team) in August 2025. The company fixed the vulnerability in mid-September 2025, but didn't formally acknowledge the fix until late November 2025. This three-month lag between fixing and acknowledging the breach meant customers remained unaware of the exposure for an extended period.
Is my payment information at risk from the Dava India breach?
No, payment card data was not exposed. The breach included order amounts but not the actual payment card details, bank information, or payment processing data. However, seeing order amounts combined with medication names creates a financial profile showing what customers spend on healthcare and their medication choices. Passwords also remain secure according to the researcher's assessment.
What should I do if I was a Dava India customer?
Start by changing your password on the Dava India platform if you had an account. If you reused that password elsewhere, change those accounts too. Monitor your credit report through CIBIL or other Indian credit bureaus for fraudulent accounts. Be cautious of phishing messages claiming to be from Dava India or healthcare providers. Secure your health information by using privacy-conscious healthcare providers going forward and requesting minimal data collection.
How did this breach happen if Dava India is such a large company?
Dava India, operating over 2,300 stores, prioritized expansion and feature development over security infrastructure. The company apparently lacked basic security practices: no mandatory security code reviews, no regular penetration testing, limited developer security training, and no automated security testing. This combination is surprisingly common among rapidly growing Indian healthcare companies focused on business metrics rather than security maturity. Many companies in similar growth stages make identical mistakes.
What legal consequences could Dava India face?
Dava India faces potential consequences under multiple Indian laws. The new Digital Personal Data Protection Act (2023) allows fines up to 500 crore rupees for security failures. The Information Technology Act allows damages up to 5 crore rupees under Section 43A for negligent data protection. Affected customers can file complaints with the Data Protection Board, state consumer protection authorities, or pursue civil lawsuits. The company could also face criminal charges if investigation reveals intentional negligence or cover-up attempts.
What makes healthcare data breaches different from other data breaches?
Healthcare data is more personally sensitive and valuable. Unlike payment card numbers that can be canceled and reissued, health information is permanent and highly personal. A healthcare breach reveals intimate details about medical conditions, treatments, and health status that patients often hide from family and society. This sensitive information enables targeted harassment, discrimination in employment and insurance, and embarrassment. Healthcare data breaches cost organizations an average of $10.93 million per incident according to IBM's 2024 report, more than any other industry sector.
How can I evaluate the security of other healthcare services I use?
Ask directly about security practices: Do they conduct regular penetration testing? Do they have a responsible disclosure program? Have they disclosed previous breaches? Do they publish security policies? Ask about their incident response procedures and data protection measures. Check if they've received security certifications or audits. Research their history for previous breaches or security incidents. Companies serious about security will be transparent and detailed in their responses.
What is India's regulatory environment for healthcare data security?
India recently passed the Digital Personal Data Protection Act (2023), establishing baseline requirements for personal data including health information. The act requires consent-based processing, timely breach notification, security implementation, and user rights (access, correction, deletion, portability). Implementation is ongoing with enforcement mechanisms still being established. Before the DPDP Act, healthcare data protection relied on the Information Technology Act (2000), which lacked healthcare-specific provisions. India's regulatory environment is now approaching international standards like GDPR and HIPAA but continues evolving.
Conclusion
The Dava India Pharmacy breach represents more than just a security failure affecting 700,000 customers. It's a cautionary tale about rapid digitalization without corresponding security maturity. It demonstrates how fundamental security practices remain neglected in some of India's fastest-growing healthcare companies. It highlights the gap between India's regulatory evolution and current industry practices.
For affected customers, the breach creates immediate risks (phishing, identity theft) and long-term concerns (health information misuse, discrimination). Protecting yourself requires monitoring financial accounts, staying vigilant against social engineering, and being more selective about which health services access your personal information.
For healthcare companies, the breach teaches essential lessons: authentication is non-negotiable, security debt compounds quickly, and transparency builds trust better than cover-ups. Implementing the security practices outlined here wouldn't have been difficult or expensive. It would have taken disciplined development practices, code review, and periodic penetration testing.
For regulators, the breach validates the importance of the DPDP Act and demonstrates why robust enforcement mechanisms matter. As healthcare companies argue about compliance costs, remember that the costs of breaches far exceed security investment.
For the broader Indian healthcare ecosystem, the message is clear: digitalization without security is digitalization with risks. As telemedicine platforms, online pharmacies, and health record systems proliferate, security must be built in, not bolted on.
The Dava India breach wasn't inevitable. It was preventable. Every healthcare company using this incident as a wake-up call to implement security practices reduces the likelihood of the next major breach. Security isn't something healthcare companies do after launch. It's something they build into their foundation.
If you're a healthcare consumer in India, demand transparency and security commitment from your providers. If you're in healthcare technology, prioritize security alongside features. If you're a regulator, use this incident to enforce standards and hold companies accountable. If you're a security researcher, continue responsibly disclosing vulnerabilities and helping companies improve.
The Dava India breach will likely accelerate India's healthcare security maturity. Whether that acceleration happens through regulatory enforcement or market demand, improvement is necessary. Millions of Indians deserve healthcare services that protect their most sensitive personal information with the seriousness it demands.

Key Takeaways
- In this comprehensive guide, we'll break down exactly what happened, how the vulnerability worked, what data was exposed, and what you need to do if you're affected
- Png)
*The rapid digitalization of India's healthcare sector faces severe challenges, with a significant security talent gap and regulatory enforcement issues
- Dava India Pharmacy's online platform contained a critical authentication bypass vulnerability
- Someone should verify: "Are you logged in
- This is the proper channel for reporting critical vulnerabilities affecting Indian infrastructure and citizens
Related Articles
- Best Fitness Earbuds to Keep You Motivated Through Workouts [2025]
- Solar Thermal Energy Storage: How Molecules Store Heat for Months [2025]
- NYT Strands Answers & Hints Game #716 Feb 17 [2025]
- PS5 Presidents' Day Deals 2025: $100 Off + Fortnite Bundle [2025]
- 2026 TechRadar Australian PC Awards Finalists: Complete Guide [2025]
- Best Budget Camera Lenses for Sony, Nikon & Fujifilm [2025]
![Indian Pharmacy Chain Data Breach: How Millions Were Exposed [2025]](https://tryrunable.com/blog/indian-pharmacy-chain-data-breach-how-millions-were-exposed-/image-1-1771332328879.jpg)



