Understanding the Snowflake Data Theft Incident: Lessons and Future Safeguards [2025]
In a world where data is as valuable as gold, the security of information has become paramount. Recently, Snowflake, a prominent player in the cloud data warehousing space, found itself embroiled in a data breach incident. The breach was traced back to a third-party vulnerability, highlighting the significant risks posed by supply chain attacks in today's interconnected digital landscape. This article delves into the details of the incident, its implications, and offers a comprehensive guide on safeguarding against similar threats.
TL; DR
- Recent Breach: Snowflake suffered a data breach due to a third-party vulnerability, affecting numerous customers.
- Supply Chain Attacks: Highlight the increasing threat of such attacks in the tech ecosystem.
- Preventive Measures: Emphasize the need for robust vendor management and advanced security protocols.
- Future Trends: Predict greater focus on AI-driven security tools to combat sophisticated cyber threats.
- Bottom Line: Organizations must adopt a proactive stance in cybersecurity to safeguard their assets.
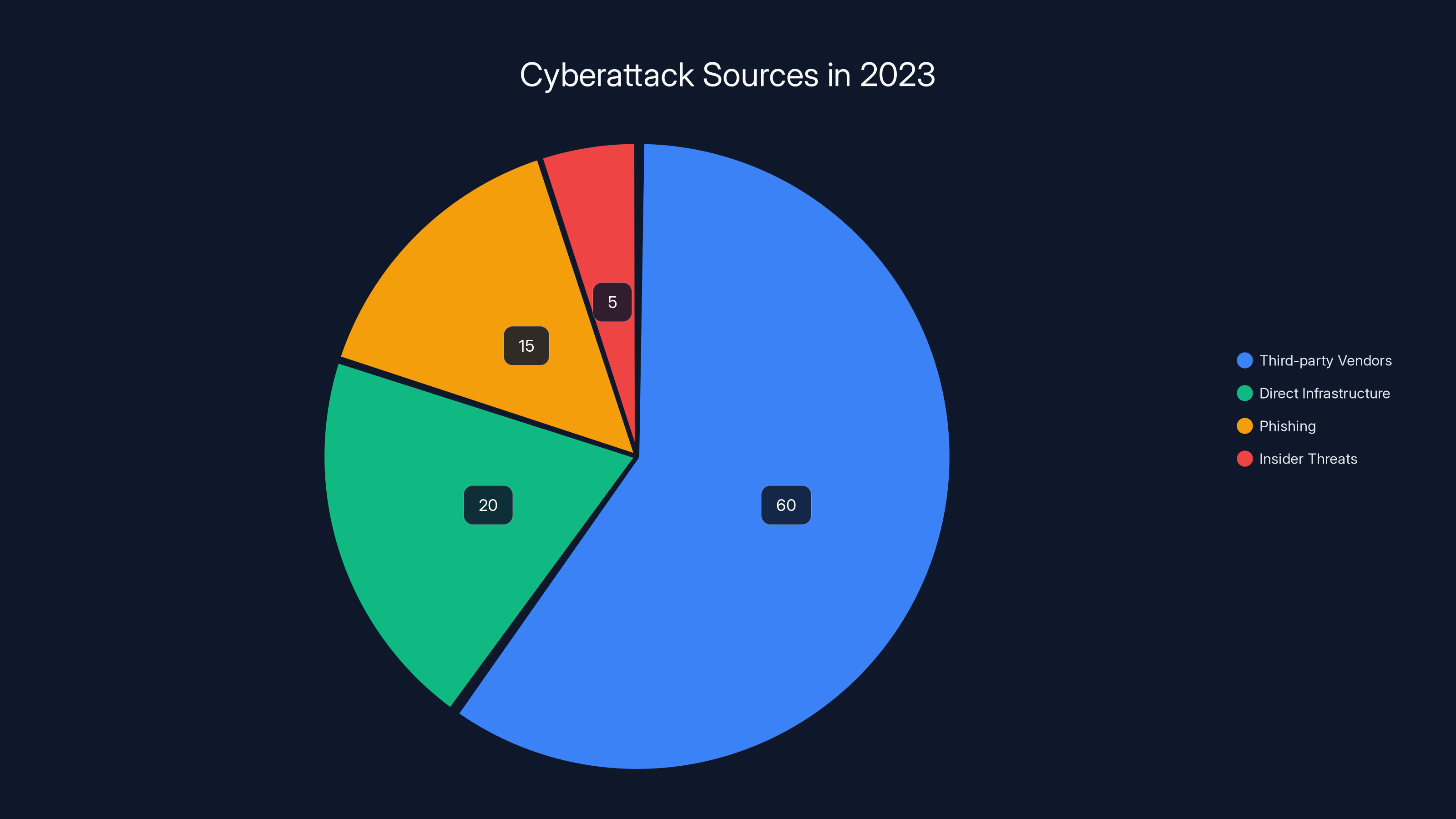
Third-party vendors are responsible for 60% of cyberattacks, highlighting the critical need for robust supply chain security. Estimated data.
The Snowflake Data Breach: What Happened?
In recent months, Snowflake confirmed a data breach that affected its customers. The breach was not directly due to Snowflake's infrastructure but rather a vulnerability in a third-party service provider. This incident underscores a critical aspect of modern cybersecurity: supply chain vulnerabilities.
Supply Chain Attacks: A Growing Threat
Supply chain attacks occur when hackers exploit vulnerabilities in third-party vendors that provide software or services to primary targets. These attacks are insidious because they exploit trusted relationships within a network. As companies increasingly outsource functions and integrate third-party tools, the attack surface grows.
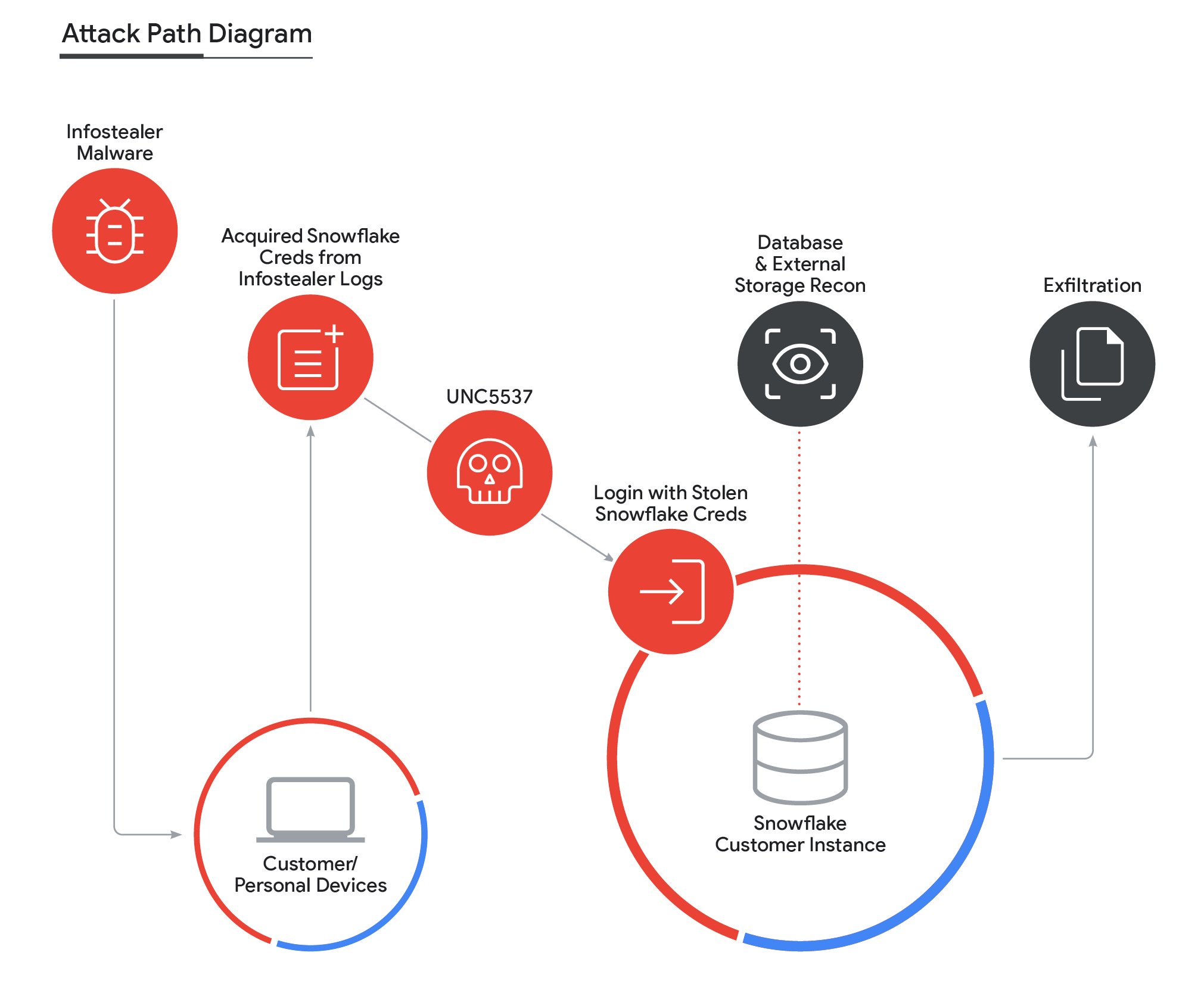
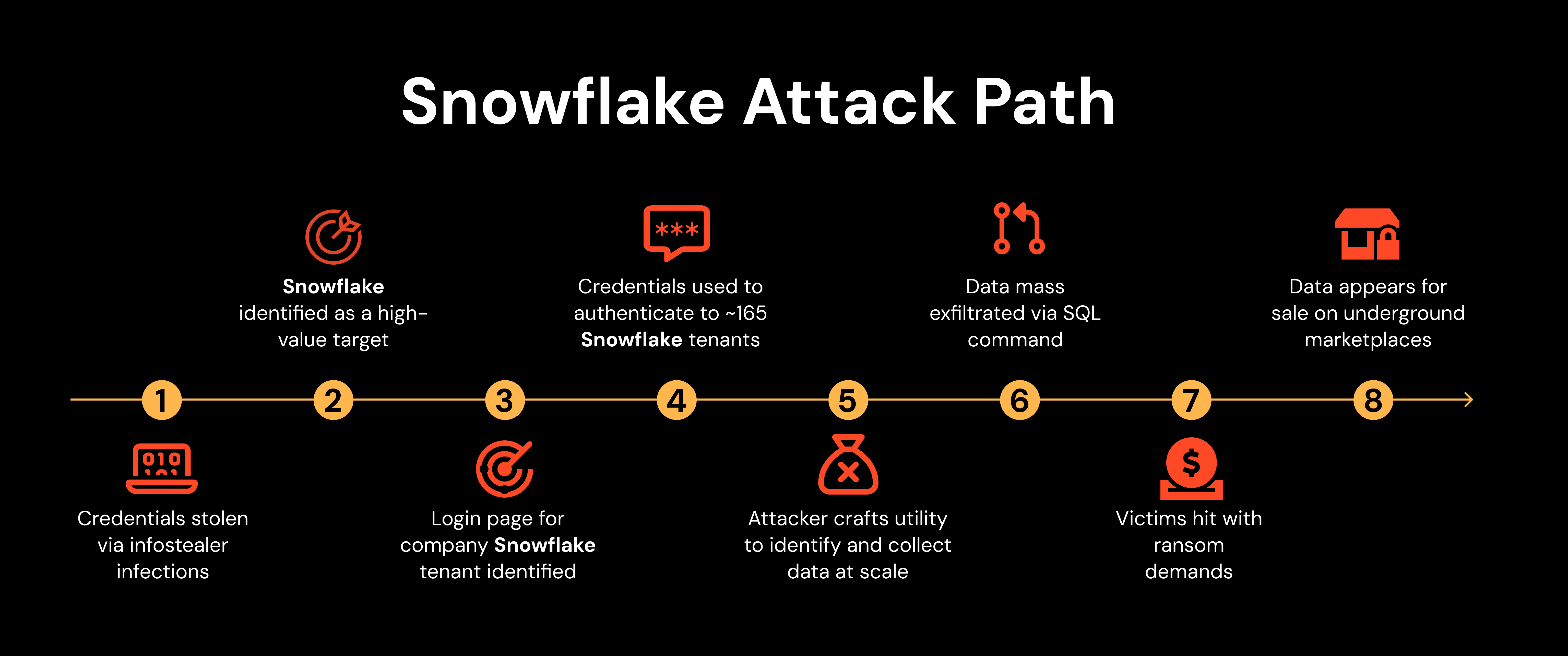
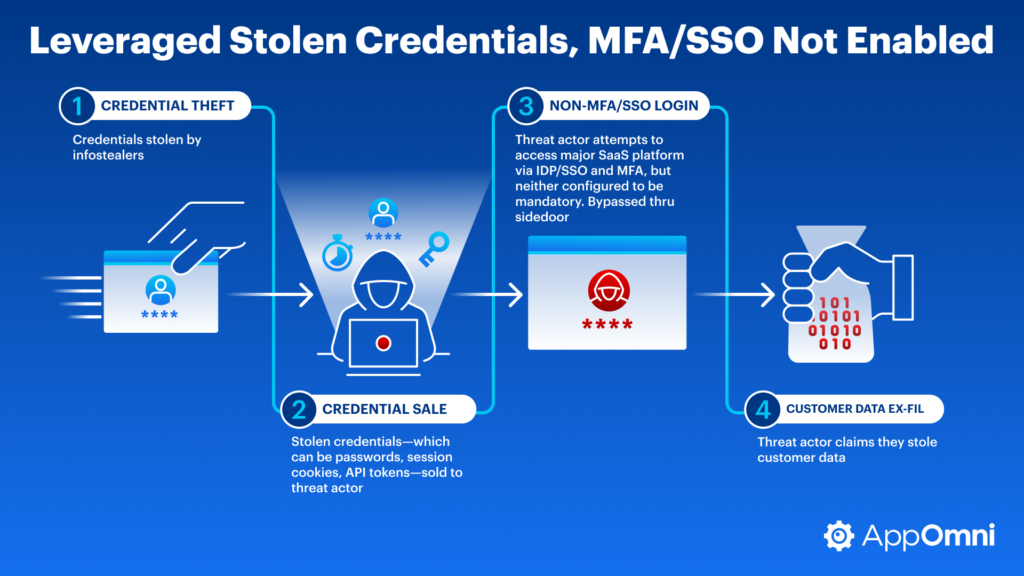
The Mechanics of the Attack
In the Snowflake incident, attackers targeted Anodot, a third-party analytics platform used by Snowflake. By compromising Anodot, the attackers gained access to Snowflake tokens, which allowed them to infiltrate the data warehouse environments of several Snowflake customers.
- Initial Breach: Attackers breached Anodot's systems to extract Snowflake tokens.
- Token Exploitation: These tokens were used to access sensitive customer data stored in Snowflake's environment.
- Data Exfiltration: The ultimate goal was to exfiltrate valuable data from the compromised environments.
This breach illustrates how attackers can bypass direct defenses by targeting less secure components within a company's supply chain.


Data breaches like the Snowflake incident can severely impact businesses, with financial losses often being the most significant consequence. (Estimated data)
Implications for Businesses
The Snowflake breach has several implications for businesses:
- Trust Erosion: Customers may lose trust in the affected companies, impacting their brand reputation.
- Regulatory Scrutiny: Increased attention from regulatory bodies as data breaches often lead to compliance investigations.
- Financial Losses: The direct costs of breach mitigation, coupled with potential fines, can be significant.
Case Study: A Similar Incident
Consider the 2020 Solar Winds attack, where attackers inserted malware into a software update, compromising multiple federal agencies and enterprises. This incident, much like the Snowflake breach, highlights the vulnerabilities inherent in supply chains.

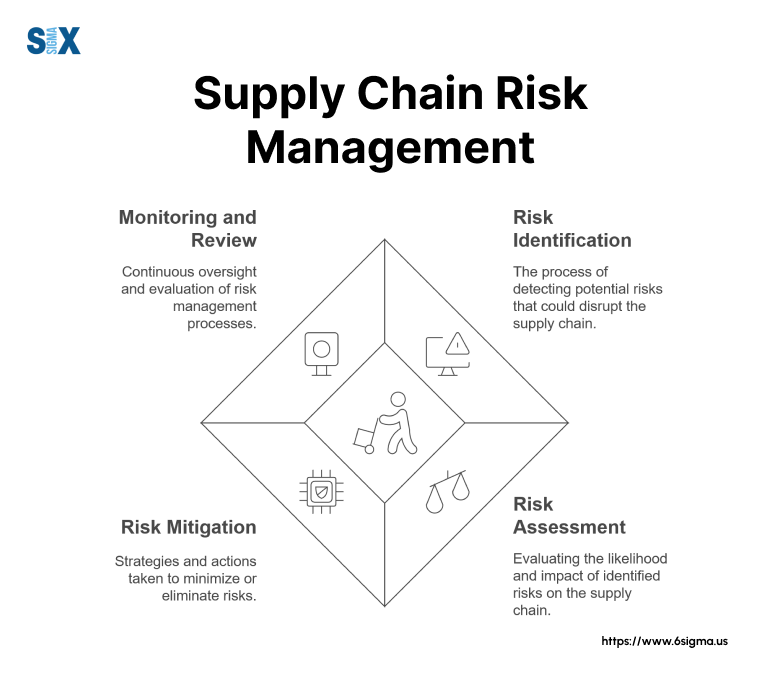
Best Practices for Mitigating Supply Chain Risks
While the threat of supply chain attacks looms large, businesses can take several proactive steps to mitigate these risks:
1. Rigorous Vendor Assessment
Conduct thorough due diligence on all third-party vendors. This involves assessing their security posture, historical incidents, and compliance with industry standards.
2. Implementing Zero Trust Architecture
Zero Trust is a security framework that requires all users, whether inside or outside the organization's network, to be authenticated, authorized, and continuously validated before gaining access to applications and data.
- Microsegmentation: Divide the network into smaller segments to contain breaches.
- Multi-Factor Authentication (MFA): Add an extra layer of security to access controls.
3. Continuous Monitoring and Auditing
Implement continuous monitoring tools to detect unusual activity in real-time. Regular audits of security protocols can also help identify potential vulnerabilities before they are exploited.
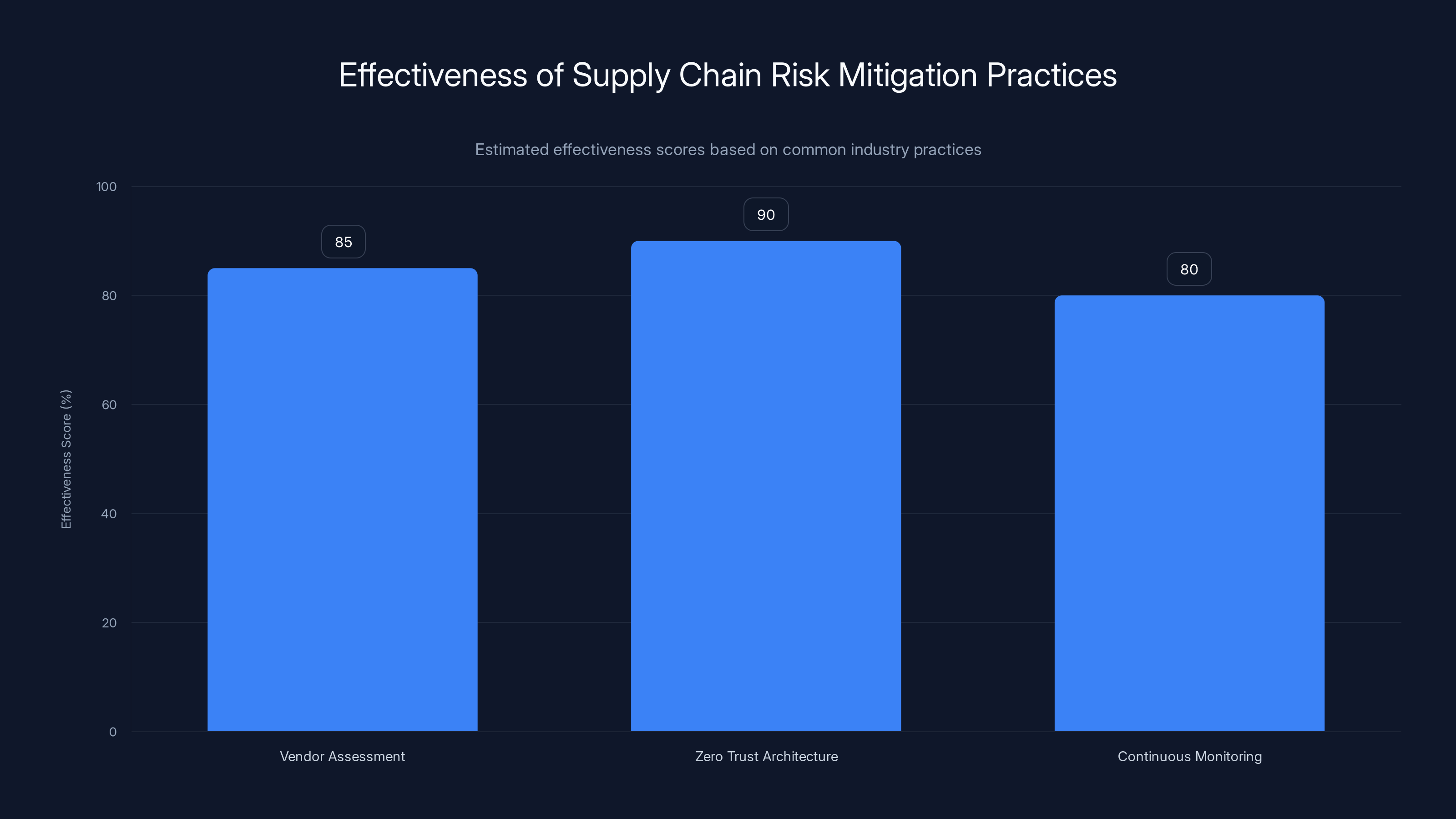
Zero Trust Architecture is estimated to be the most effective practice with a score of 90%, followed by Vendor Assessment and Continuous Monitoring. Estimated data.
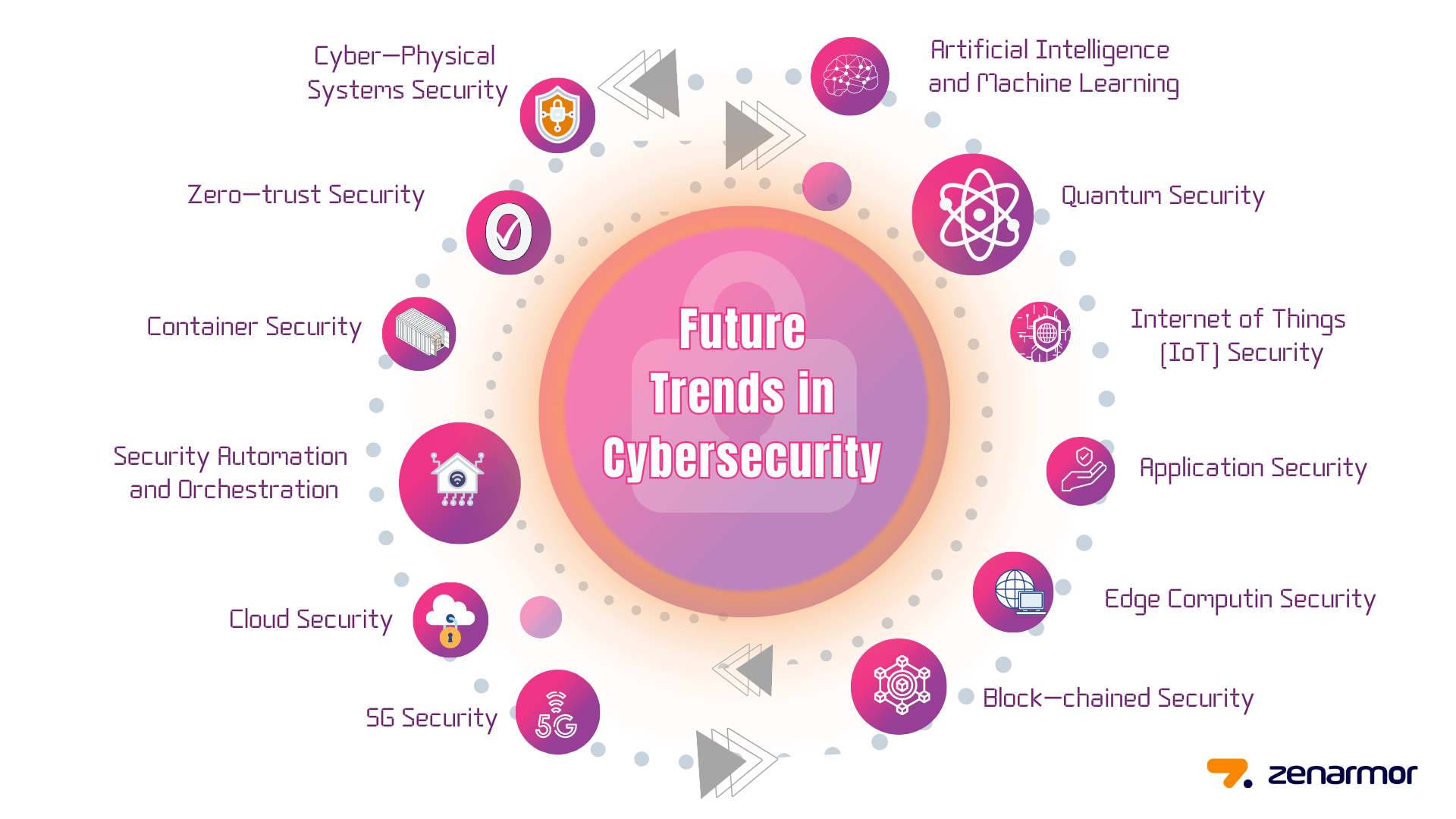
Future Trends in Cybersecurity
As cyber threats evolve, so too must the strategies to combat them. Here are some anticipated trends in cybersecurity:
AI and Machine Learning
Artificial intelligence and machine learning are poised to revolutionize cybersecurity by enabling predictive analytics and automated threat detection. These technologies can analyze vast amounts of data to identify patterns and anomalies indicative of a cyber threat.
- Behavioral Analytics: Use AI to learn normal user behavior and detect deviations that may indicate a breach.
- Automated Response: Implement AI-driven systems that can autonomously respond to threats in real-time.
Enhanced Threat Intelligence Sharing
Organizations are increasingly recognizing the value of collaboration in cybersecurity. By sharing threat intelligence, companies can collectively enhance their defenses against common threats.
Common Pitfalls in Cybersecurity
Even with robust security measures, there are common pitfalls that organizations must avoid:
Overreliance on Technology
Technology is a powerful ally, but it is not infallible. Overreliance on automated systems can lead to complacency. It's essential to maintain a balanced approach that combines technology with human oversight.
Inadequate Employee Training
Employees are often the first line of defense against cyber threats. Inadequate training can lead to mistakes that compromise security. Regular training sessions and awareness programs can help empower employees to recognize and report suspicious activity.
Lack of Incident Response Planning
An incident response plan outlines the steps an organization will take in the event of a security breach. Without a well-defined plan, organizations may struggle to respond effectively, leading to prolonged recovery times and increased damage.
Implementing an Effective Cybersecurity Strategy
Developing a comprehensive cybersecurity strategy involves several key steps:
Step 1: Risk Assessment
Identify and prioritize the assets that are most critical to your organization. Assess the potential impact of various threats and vulnerabilities.
Step 2: Security Policy Development
Create policies that define the rules and procedures for protecting organizational assets. These policies should be regularly reviewed and updated to address emerging threats.
Step 3: Technology Deployment
Deploy security technologies that align with your organization's needs. This may include firewalls, intrusion detection systems, and endpoint protection solutions.
Step 4: Incident Response Planning
Develop a detailed incident response plan that outlines the roles and responsibilities of team members, communication protocols, and recovery procedures.
Future Recommendations
As the threat landscape continues to evolve, organizations must adopt a forward-thinking approach to cybersecurity:
Invest in Continuous Education
Ongoing education is essential for staying informed about the latest threats and security best practices. Encourage employees to pursue certifications and participate in industry conferences.
Foster a Culture of Security
Create a culture where security is a shared responsibility. Encourage employees to actively participate in security initiatives and reward those who demonstrate a commitment to protecting organizational assets.
Leverage Emerging Technologies
Stay abreast of emerging technologies that can enhance your security posture. This includes exploring blockchain for secure transactions and quantum computing for advanced encryption.
Conclusion
The Snowflake data breach serves as a stark reminder of the vulnerabilities present in today's digital landscape. By understanding the mechanics of supply chain attacks and implementing robust security measures, organizations can better protect themselves against future threats. As we look to the future, a proactive and collaborative approach to cybersecurity will be essential in safeguarding valuable data assets.
FAQ
What is a supply chain attack?
A supply chain attack occurs when a threat actor infiltrates a system through an outside partner or provider with access to a system or data.
How can businesses prevent data breaches?
Businesses can prevent data breaches by implementing strong security measures, conducting regular audits, and ensuring all third parties adhere to security standards.
What is Zero Trust architecture?
Zero Trust is a security model that requires strict identity verification for every person and device trying to access resources on a private network, regardless of whether they are inside or outside the network perimeter.
Why is threat intelligence sharing important?
Threat intelligence sharing allows organizations to learn from each other's experiences and collectively enhance their defenses against cyber threats.
How does AI improve cybersecurity?
AI improves cybersecurity by enabling automated threat detection, predictive analytics, and real-time responses to potential security incidents.
What are the key components of an incident response plan?
Key components of an incident response plan include roles and responsibilities, communication protocols, and detailed recovery procedures.
Why is continuous monitoring essential?
Continuous monitoring is essential because it allows organizations to detect and respond to security threats in real-time, minimizing potential damage.
How can organizations foster a culture of security?
Organizations can foster a culture of security by encouraging employee participation in security initiatives, providing regular training, and recognizing contributions to security efforts.
Key Takeaways
- Snowflake suffered a data breach due to a third-party vulnerability.
- Supply chain attacks are becoming increasingly prevalent.
- Implementing Zero Trust architecture can mitigate such risks.
- AI and machine learning are crucial for future cybersecurity strategies.
- Continuous monitoring and vendor assessments are essential.
- Organizations must foster a culture of security among employees.
Related Articles
- European Commission Confirms Data Breach: Analysis and Implications [2025]
- Understanding Cybersecurity in the EU: Lessons from the European Commission Cyberattack [2025]
- European Commission Data Breach: What Happened and How to Respond [2025]
- Understanding and Mitigating New Rowhammer Attacks on Nvidia GPUs [2025]
- Citrix NetScaler Flaw: CISA's Patch Warning and What It Means [2025]
- Introducing Proton Meet: A New Era of Secure Video Conferencing [2025]
![Understanding the Snowflake Data Theft Incident: Lessons and Future Safeguards [2025]](https://tryrunable.com/blog/understanding-the-snowflake-data-theft-incident-lessons-and-/image-1-1775657087560.jpg)



