Mastodon Faces Major DDoS Attack: Understanding, Mitigation, and Future Preparedness [2025]
When a massive Distributed Denial of Service (DDoS) attack recently disrupted Mastodon, a decentralized social media platform, it served as a stark reminder of the vulnerabilities inherent in even the most robust online ecosystems. As the digital landscape continues to evolve, understanding how DDoS attacks work and how to protect against them is more crucial than ever.
TL; DR
- Mastodon suffered a significant DDoS attack, temporarily disabling parts of its network, as reported by TechCrunch.
- DDoS attacks flood networks with traffic, overwhelming systems and causing service disruptions, according to PV Magazine.
- Mitigation strategies include traffic filtering, rate limiting, and real-time monitoring, as highlighted by Corero Network Security.
- Future trends suggest increasing sophistication in attack methods, requiring advanced defense mechanisms, as noted by HackRead.
- Decentralized platforms face unique challenges in maintaining security and accessibility, as discussed in SPF's analysis.
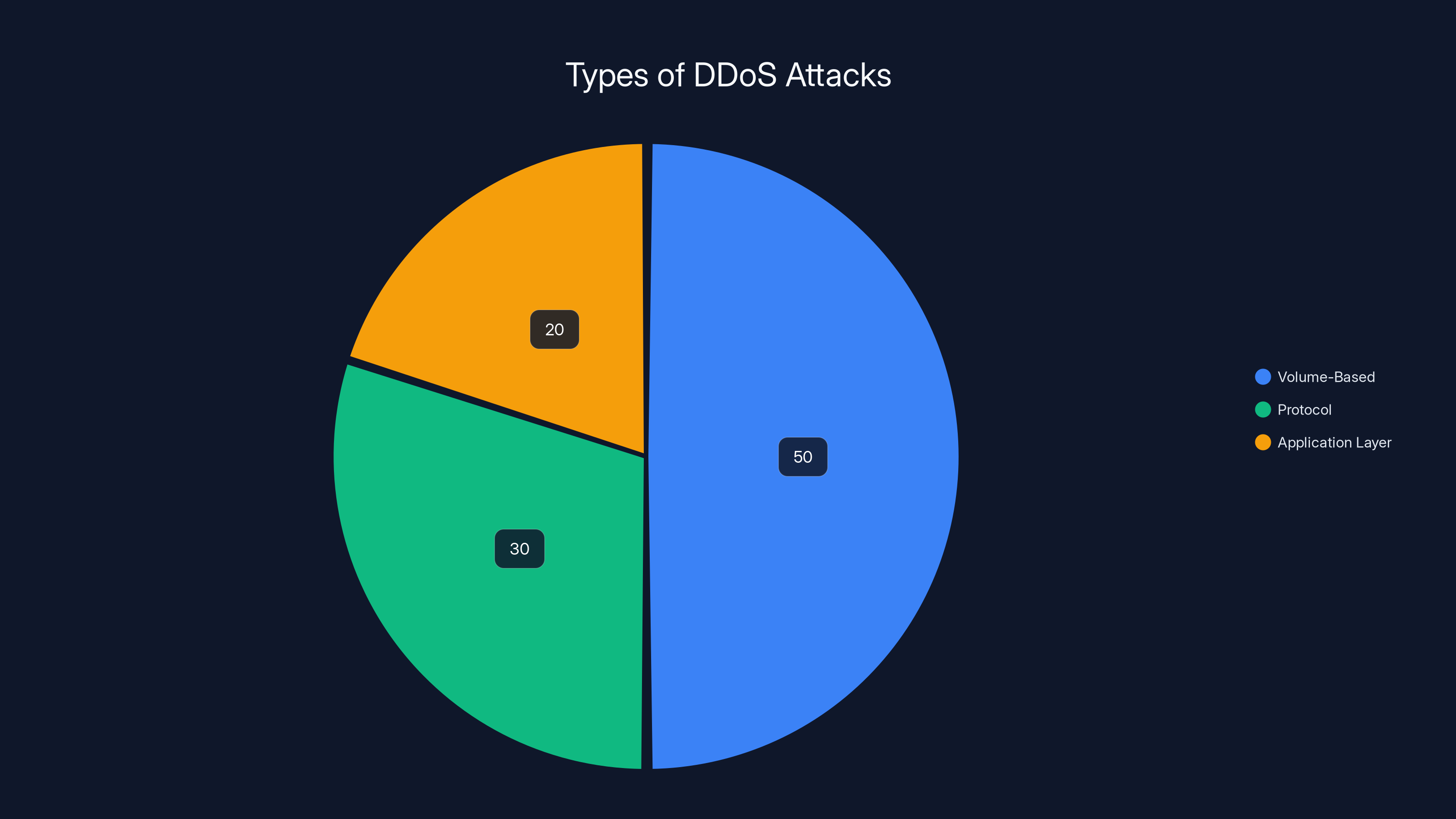
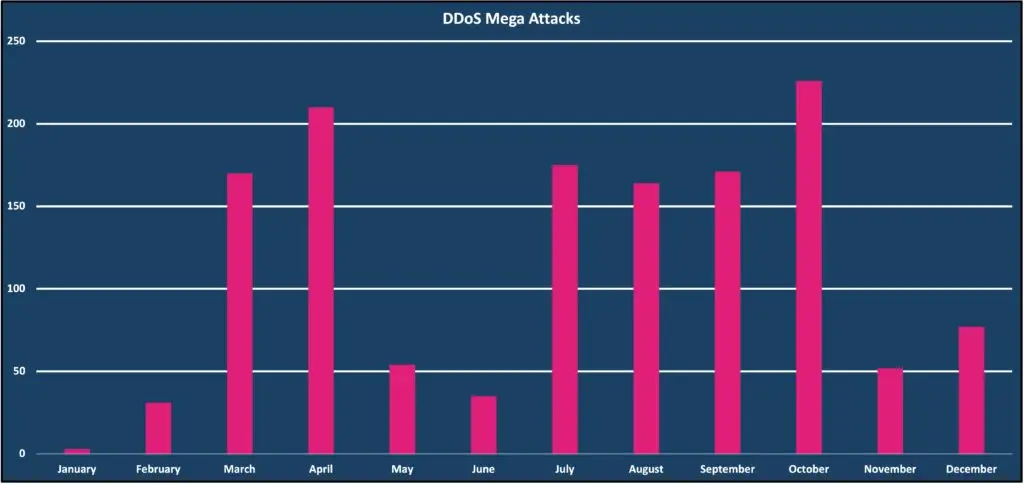
Volume-based attacks are the most common form of DDoS attacks, making up an estimated 50% of all attacks. Estimated data.
What Happened to Mastodon?
In recent weeks, Mastodon, a decentralized social networking platform, experienced a major DDoS attack that temporarily took down its primary mastodon.social instance. This incident followed a similar attack on Bluesky, another decentralized platform, indicating a potential trend in targeting these networks, as reported by The Record. The attack caused significant disruptions, leaving users unable to access services and raising concerns about the security of decentralized platforms.
Understanding DDoS Attacks
A Distributed Denial of Service (DDoS) attack is a malicious attempt to disrupt the normal functioning of a targeted server, service, or network by overwhelming it with a flood of internet traffic. It's akin to a traffic jam blocking the highway, preventing legitimate traffic from reaching its destination.
Key Characteristics of DDoS Attacks:
- Volume-Based Attacks: These focus on saturating the bandwidth of a target, utilizing massive amounts of junk data to clog the network.
- Protocol Attacks: These exploit vulnerabilities in protocol layers, such as SYN floods, to deplete server resources.
- Application Layer Attacks: These target specific applications, aiming to exhaust server resources through complex requests.
How DDoS Attacks Work
DDoS attacks typically employ multiple compromised computer systems as sources of attack traffic. Exploiting vulnerabilities in devices, attackers can control these systems, known as botnets, to launch large-scale attacks.
DDoS Attack Process:
- Botnet Recruitment: Attackers infect devices with malware, turning them into bots, as explained by BitSight.
- Command and Control: A central server controls the botnet, directing the bots to send requests to the target.
- Attack Execution: The botnet launches a coordinated attack, overwhelming the target with traffic.

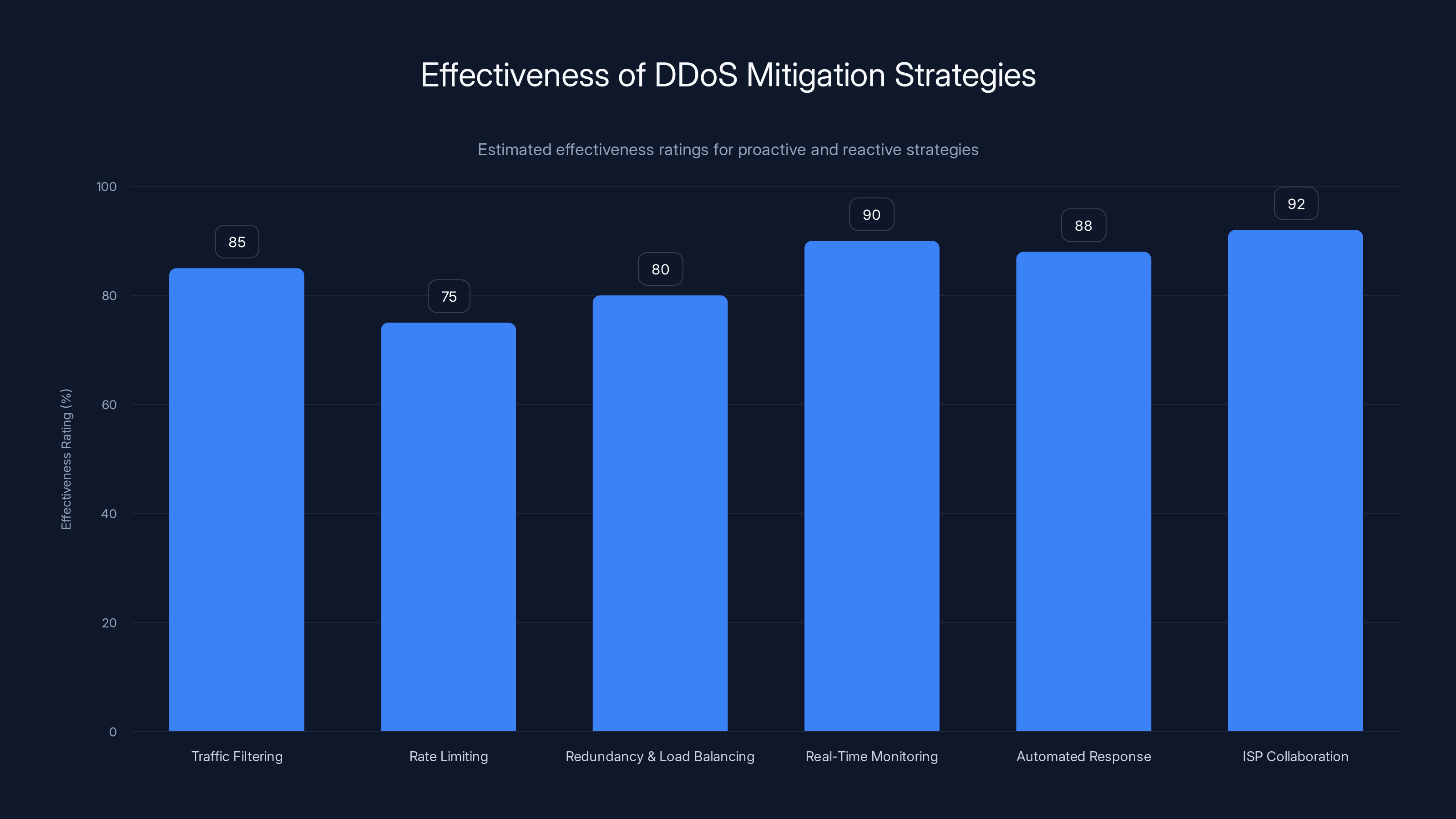
Estimated data: ISP collaboration and real-time monitoring are rated as the most effective strategies in mitigating DDoS attacks.
Impact on Decentralized Platforms
Decentralized platforms like Mastodon are particularly vulnerable to DDoS attacks due to their reliance on distributed networks. Unlike centralized services, which can deploy robust, centralized defenses, decentralized platforms must rely on a network of independently operated nodes.
Unique Challenges for Decentralized Platforms:
- Node Vulnerability: Each node may have different security measures, creating potential weak points.
- Resource Limitations: Nodes operated by individuals or small groups may lack the resources to fend off large attacks.
- Coordination Difficulty: Decentralized networks require cooperation among nodes, complicating unified defense strategies.
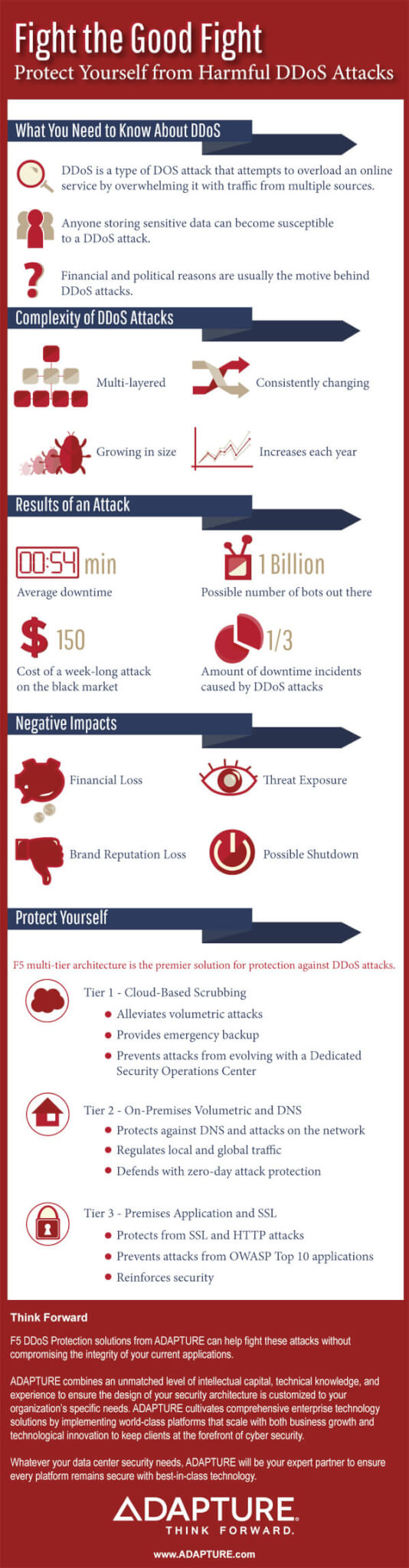
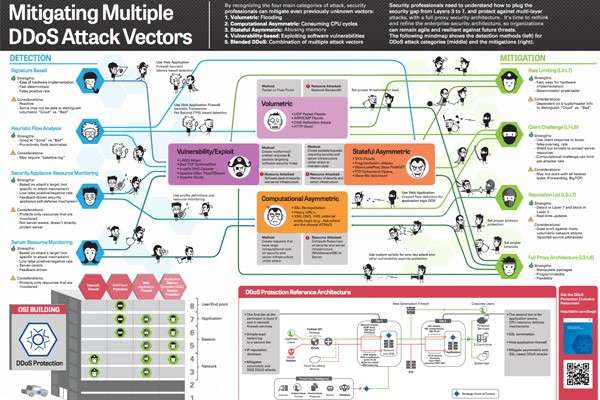
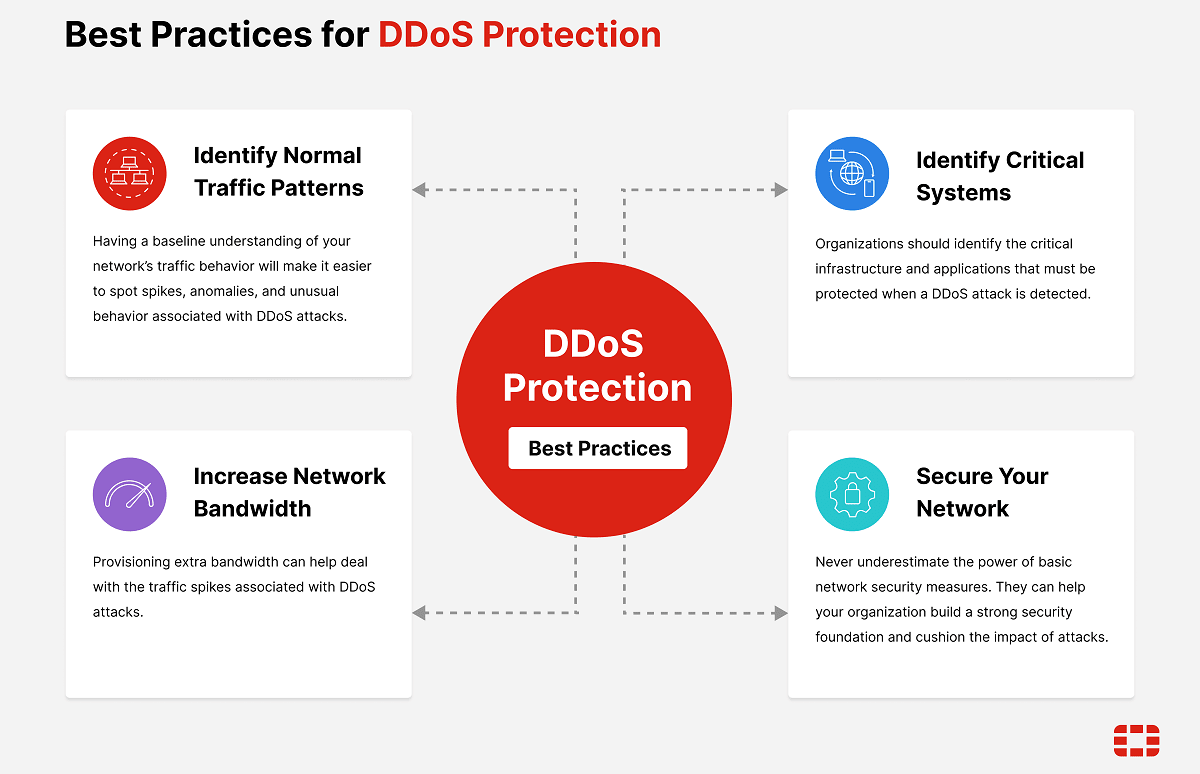
Mitigating DDoS Attacks
Effectively combating DDoS attacks requires a multi-layered approach that includes both proactive and reactive measures.
Proactive Strategies
- Traffic Filtering: Use firewalls and intrusion prevention systems to block malicious traffic before it reaches the network.
- Rate Limiting: Implement limits on the number of requests a server can handle from a single IP address.
- Redundancy and Load Balancing: Distribute traffic across multiple servers to prevent any one server from being overloaded.
Reactive Strategies
- Real-Time Monitoring: Utilize monitoring tools to detect unusual traffic patterns and respond swiftly to potential threats.
- Automated Incident Response: Implement automated scripts to activate defense mechanisms when an attack is detected.
- Collaboration with ISPs: Work with internet service providers to filter attack traffic at the source, as recommended by Wiz.io.
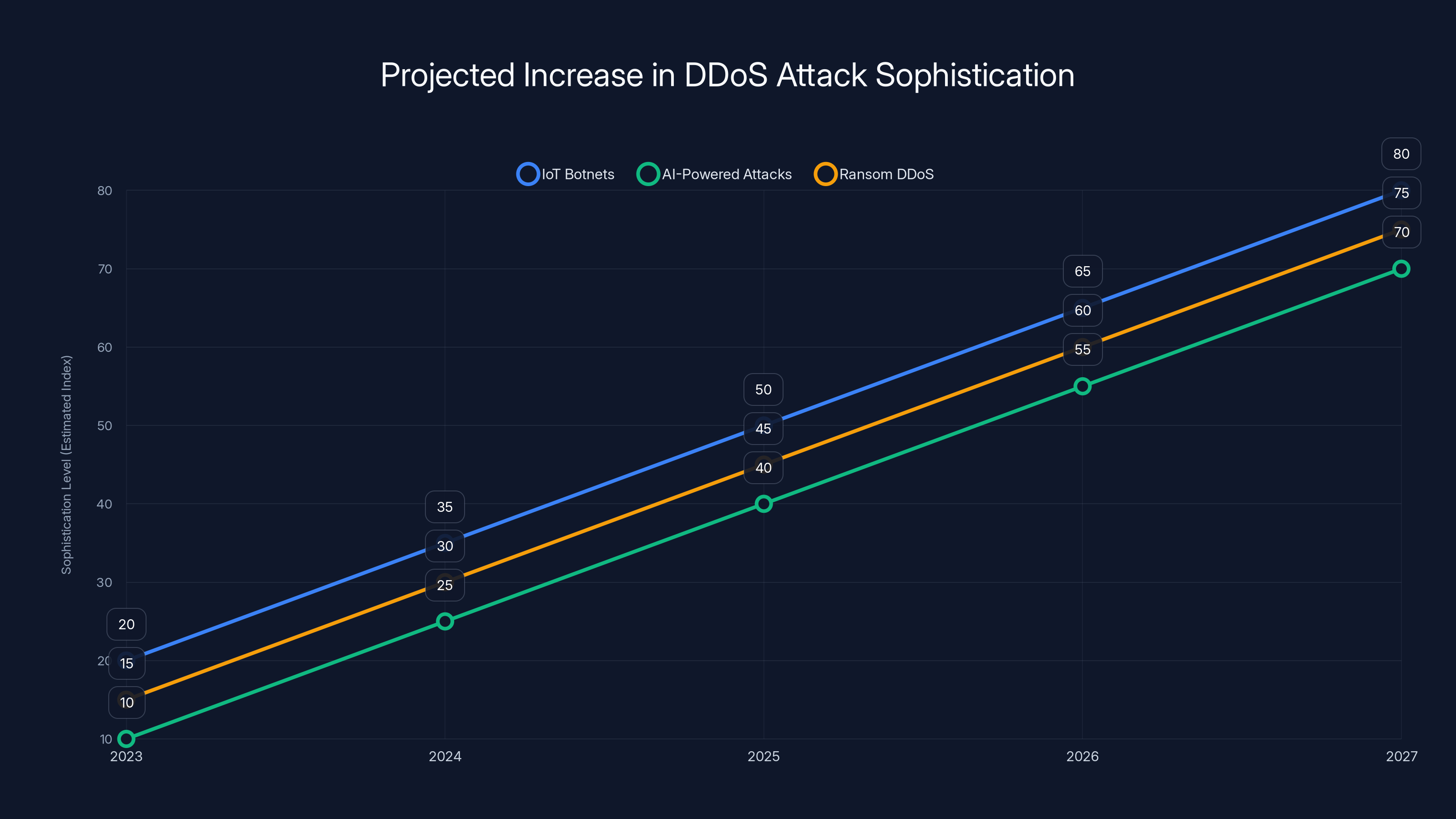
The sophistication of DDoS attacks is projected to increase significantly by 2027, driven by IoT botnets, AI-powered attacks, and ransom DDoS. (Estimated data)
Case Study: Mastodon's Response
During the recent attack, Mastodon implemented several countermeasures to mitigate the impact. According to TechCrunch, the platform's head of communications described it as a "major" incident, but prompt actions helped restore service.
Countermeasures Taken by Mastodon:
- Traffic Filtering: Deployed advanced filtering techniques to block malicious traffic.
- Rate Limiting: Adjusted server configurations to limit the impact of high-volume requests.
- User Communication: Kept users informed through status updates, maintaining transparency.
Future Trends in DDoS Attacks
As technology evolves, so do the methods employed by cybercriminals. DDoS attacks are becoming increasingly sophisticated, requiring advanced defense mechanisms.
Emerging Trends
- IoT Botnets: With the proliferation of Internet of Things (IoT) devices, attackers have more potential recruits for botnets, as highlighted by The Block.
- AI-Powered Attacks: Cybercriminals are leveraging artificial intelligence to launch more targeted and efficient attacks.
- Ransom DDoS: Attackers threaten DDoS attacks unless a ransom is paid, adding a financial dimension to the threat.
Preparing for the Future
To stay ahead of these threats, organizations must adopt forward-thinking strategies:
- Invest in AI-Driven Security: Utilize machine learning algorithms to predict and respond to threats in real-time.
- Enhance Collaboration: Foster cooperation among decentralized nodes to develop unified defense strategies.
- Educate Users: Raise awareness about potential threats and best practices for securing personal devices.

Practical Implementation Guides
For organizations looking to bolster their defenses against DDoS attacks, implementing a comprehensive security strategy is essential.
Implementing Traffic Filtering
- Deploy Firewalls: Utilize both hardware and software firewalls to create a first line of defense.
- Leverage Intrusion Prevention Systems: Use IPS to automatically block suspicious traffic based on predefined rules.
- Regularly Update Security Protocols: Ensure that all security measures are up-to-date to combat the latest threats.
Configuring Rate Limiting
- Define Request Thresholds: Set limits on the number of requests allowed from a single IP address.
- Implement Adaptive Rate Limiting: Adjust thresholds dynamically based on traffic patterns to prevent legitimate users from being blocked.
- Monitor and Adjust: Continuously monitor traffic and fine-tune rate limiting parameters as needed.
Common Pitfalls and Solutions
While implementing DDoS mitigation strategies, organizations may encounter several challenges. Here's how to address them:
Pitfall: Overly Aggressive Filtering
Solution: Balance filtering rules to minimize false positives, ensuring legitimate traffic is not blocked.
Pitfall: Insufficient Monitoring
Solution: Invest in comprehensive monitoring tools that provide real-time insights into traffic patterns and potential threats.
Pitfall: Lack of Coordination
Solution: Establish clear communication channels among team members and stakeholders to ensure a coordinated response to threats.
Future Recommendations for Decentralized Platforms
Decentralized platforms must take proactive steps to enhance their security posture and protect against future DDoS attacks.
Build Resilient Infrastructure
- Enhance Node Security: Encourage node operators to implement robust security measures and share best practices.
- Promote Decentralized Coordination: Develop protocols for nodes to communicate and collaborate effectively during attacks.
- Leverage Cloud-Based Solutions: Utilize cloud services to provide additional scalability and redundancy.
Conclusion
The recent DDoS attack on Mastodon highlights the ongoing challenges faced by decentralized platforms in maintaining security and accessibility. By understanding the mechanics of DDoS attacks and implementing effective mitigation strategies, organizations can better protect themselves against future threats. As the digital landscape continues to evolve, staying informed and prepared will be key to safeguarding decentralized networks.
FAQ
What is a DDoS attack?
A Distributed Denial of Service (DDoS) attack is a malicious attempt to disrupt the normal functioning of a targeted server, service, or network by overwhelming it with a flood of internet traffic.
How can organizations protect against DDoS attacks?
Organizations can protect against DDoS attacks by implementing traffic filtering, rate limiting, real-time monitoring, and collaborating with ISPs to filter malicious traffic at the source.
What challenges do decentralized platforms face in combating DDoS attacks?
Decentralized platforms face unique challenges such as node vulnerability, resource limitations, and coordination difficulty in maintaining security and accessibility.
What future trends are emerging in DDoS attacks?
Emerging trends in DDoS attacks include the use of IoT botnets, AI-powered attacks, and ransom DDoS, where attackers demand payment to avoid launching an attack.
How can decentralized platforms enhance their security posture?
Decentralized platforms can enhance their security posture by building resilient infrastructure, promoting decentralized coordination, and leveraging cloud-based solutions for scalability and redundancy.
What role does AI play in defending against DDoS attacks?
AI plays a crucial role in defending against DDoS attacks by enabling real-time threat detection, predictive analytics, and automated response mechanisms to mitigate threats effectively.
Key Takeaways
- Mastodon experienced a major DDoS attack, highlighting the vulnerabilities of decentralized platforms.
- DDoS attacks exploit network and application vulnerabilities to overwhelm systems with traffic.
- Effective mitigation requires a multi-layered approach combining proactive and reactive strategies.
- Emerging trends in DDoS attacks include IoT botnets and AI-driven methodologies.
- Decentralized platforms must adopt collaborative security measures to enhance resilience against attacks.
Related Articles
- Tor Project's Mobile VPN Launch: A New Era in Privacy [2025]
- How an Old Microsoft Excel Flaw Could Hijack Your System [2025]
- AI's Fascination with Stonehenge: Unraveling the Myths and Realities [2025]
- Adobe Summit 2026: Unveiling Innovations and Insights from Adobe's Annual Keynote [2026]
- Debate Over U.S. Spy Laws: Balancing Privacy and National Security [2025]
- Rocket Innovations: Starship V3 Ignites and ESA Ventures into Crewed Launches [2025]
![Mastodon Faces Major DDoS Attack: Understanding, Mitigation, and Future Preparedness [2025]](https://tryrunable.com/blog/mastodon-faces-major-ddos-attack-understanding-mitigation-an/image-1-1776719195002.png)



