Tor Project's Mobile VPN Launch: A New Era in Privacy [2025]
The digital landscape is constantly evolving, and with it, the need for robust privacy solutions becomes ever more critical. In recent years, the Tor Project has been at the forefront of providing tools that enhance user privacy and anonymity online. With their latest endeavor, a mobile VPN, Tor is poised to make a significant impact on how we secure our mobile communications. This article delves into the recent advancements, technical details, and implications of this development.
TL; DR
- Successful Audit: Tor's mobile VPN has passed a Cure 53 security audit, ensuring robust privacy measures.
- Enhanced Privacy: Designed to enhance anonymity on mobile devices, offering effective protection against surveillance.
- Technical Advancements: Incorporates cutting-edge encryption and obfuscation techniques.
- User Adoption: Set to revolutionize mobile privacy, appealing to privacy-conscious users worldwide.
- Future Potential: Could influence the development of privacy tools across the tech industry.

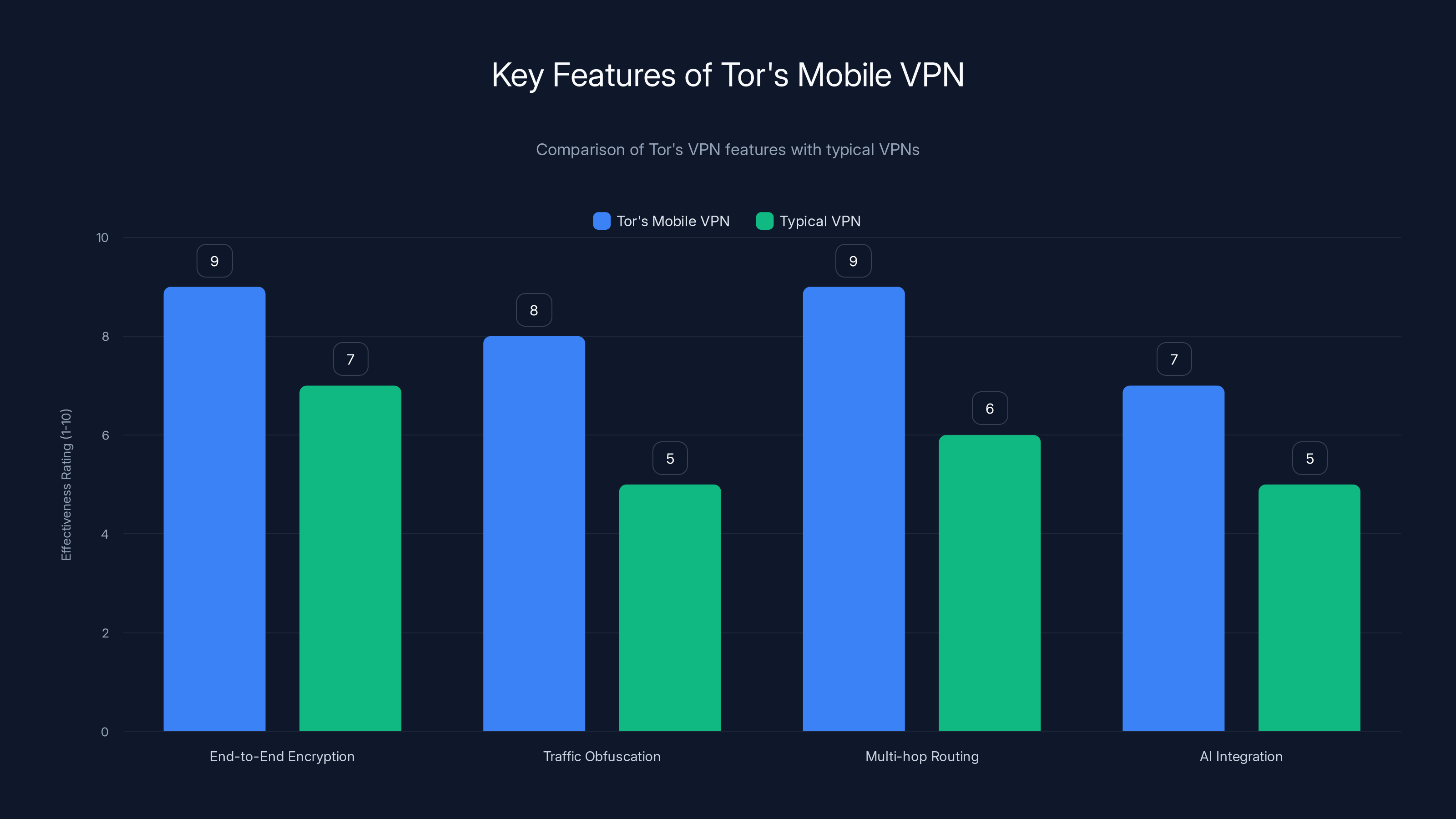
Tor's Mobile VPN excels in end-to-end encryption and multi-hop routing compared to typical VPNs, offering enhanced privacy and security. Estimated data.
What Sets Tor's Mobile VPN Apart?
The Tor Project is renowned for its dedication to protecting user privacy. Their mobile VPN offering is no exception, designed to provide an additional layer of security that complements their existing Tor Browser. But what makes this VPN stand out in a crowded market?
Security at the Core
Tor's mobile VPN has undergone rigorous testing, including a comprehensive security audit by Cure 53, a well-respected cybersecurity firm. This audit ensures that the VPN meets high security standards, giving users confidence in its ability to protect their data.
Key Security Features:
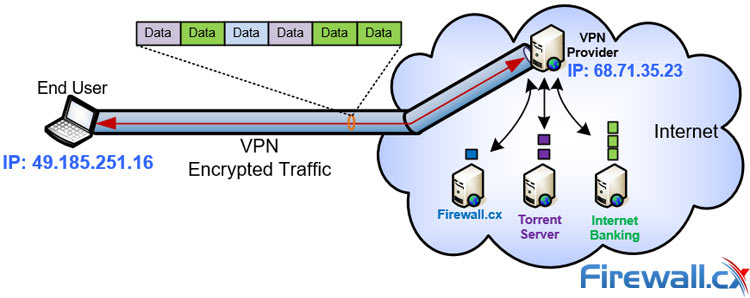
- End-to-End Encryption: Ensures all data is encrypted from the user's device to the VPN server.
- Multi-Hop Routing: Data is routed through multiple servers, enhancing anonymity.
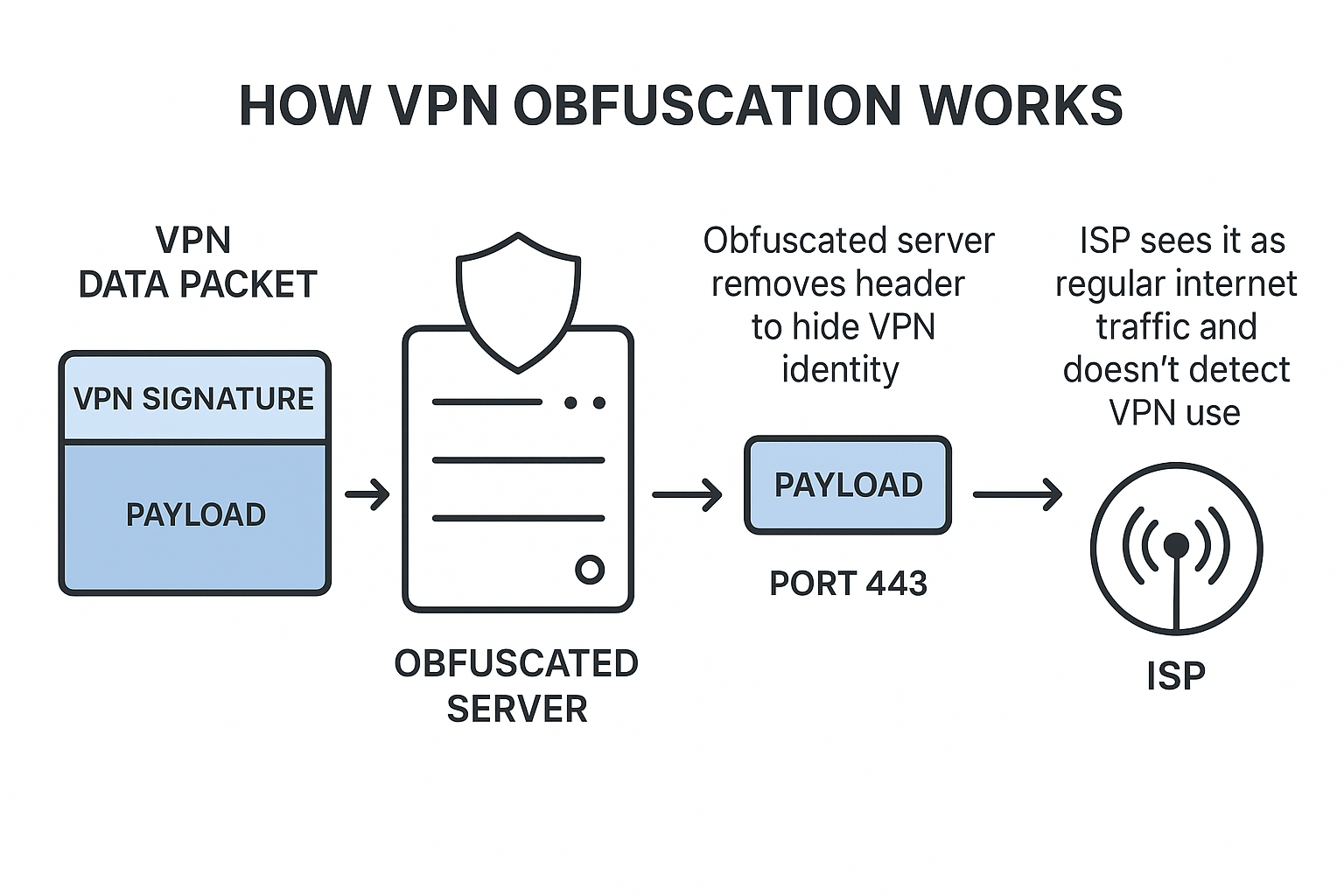
- Traffic Obfuscation: Techniques to disguise VPN traffic, making it harder to detect.
Usability and Accessibility
Beyond security, the Tor mobile VPN is designed with user-friendliness in mind. Its interface is intuitive, allowing even non-technical users to benefit from enhanced privacy.
Ease of Use Features:
- One-Click Connection: Quick and easy setup for instant protection.
- Cross-Platform Compatibility: Available on both Android and iOS devices.
- Minimalist Design: Focus on simplicity without compromising functionality.
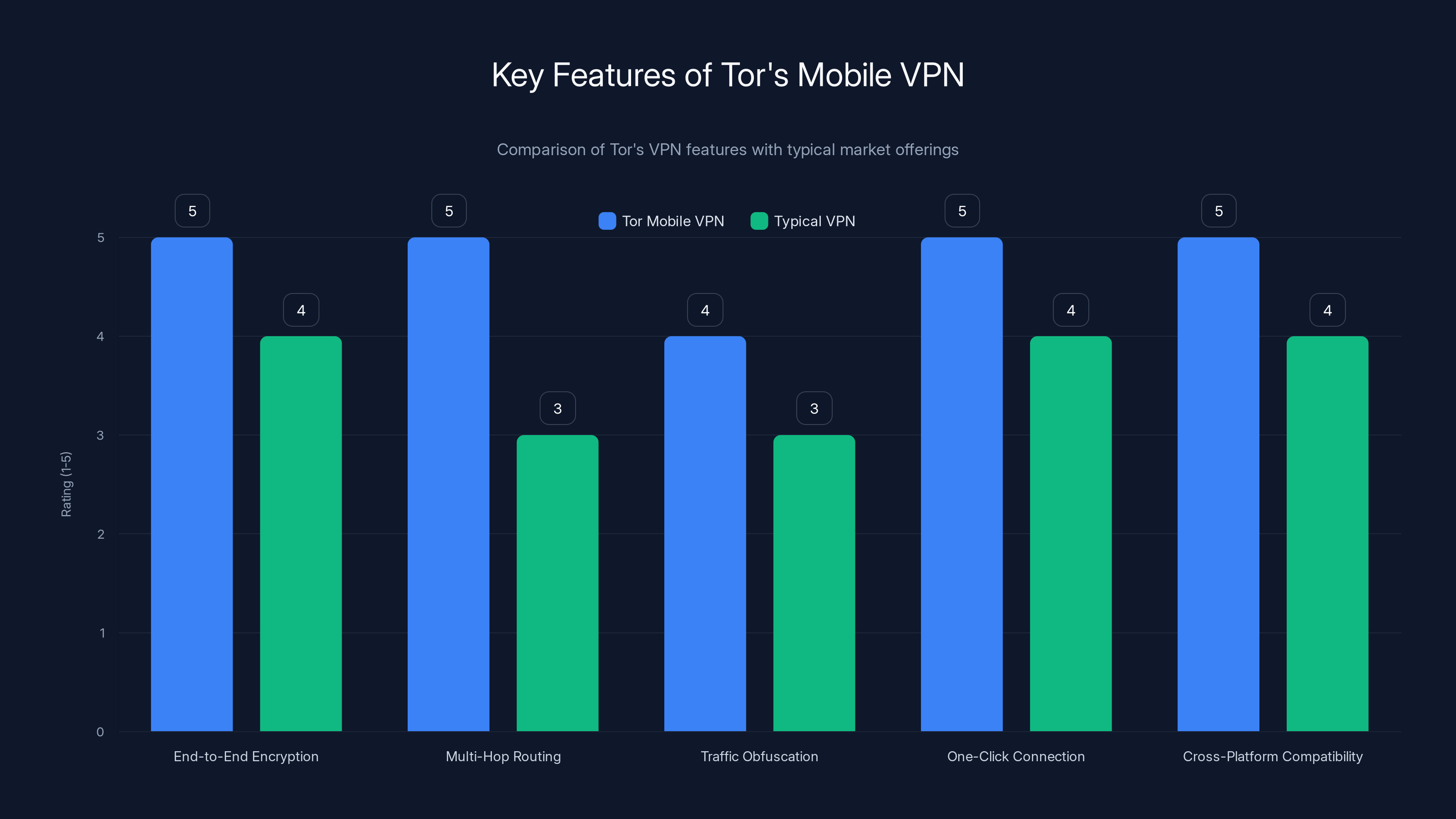
Tor's Mobile VPN excels in security and usability features compared to typical VPNs, particularly in multi-hop routing and traffic obfuscation. (Estimated data)
Technical Architecture: Under the Hood
Tor's mobile VPN is built on a robust technical foundation, leveraging years of experience in secure communications. Let's explore the architecture that powers this innovative solution.
Encryption Protocols
The cornerstone of any secure VPN is its encryption protocols. Tor's VPN uses state-of-the-art encryption standards to ensure data remains secure.
- AES-256 Encryption: Provides a high level of security for data in transit.
- Perfect Forward Secrecy: Ensures that session keys change regularly, reducing the risk of data exposure.
Obfuscation Techniques
To prevent VPN blocking, Tor's VPN incorporates advanced obfuscation techniques. These techniques make VPN traffic appear as regular internet traffic, bypassing censorship and restrictions.
- Obfsproxy: A pluggable transport that disguises Tor traffic.
- Meek: A protocol that uses HTTPS to disguise VPN connections as regular web traffic.

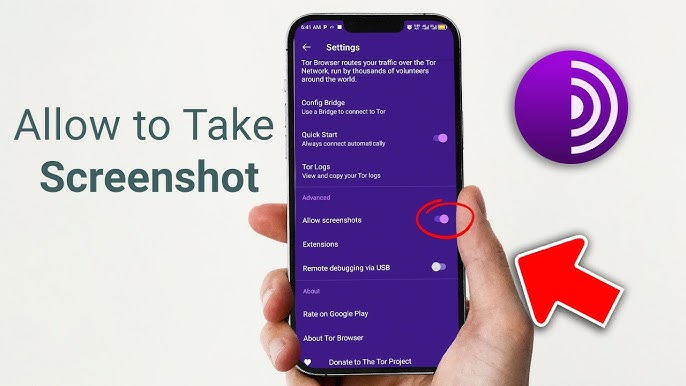
Implementation Guide: Getting Started with Tor's Mobile VPN
For users eager to enhance their mobile privacy, getting started with Tor's VPN is straightforward. Here's a step-by-step guide to help you set up and use the VPN effectively.
Step 1: Download and Install
- Download the App: Available on Google Play Store and Apple App Store.
- Install: Follow the on-screen instructions to complete the installation.
Step 2: Configure Settings
- Select Server Location: Choose from a list of available server locations to optimize speed and privacy.
- Enable Auto-Connect: Set the VPN to connect automatically when your device starts.
Step 3: Connect
- One-Click Connection: Tap the connect button to activate the VPN.
- Verify Connection: Check the status indicator to ensure you're connected.
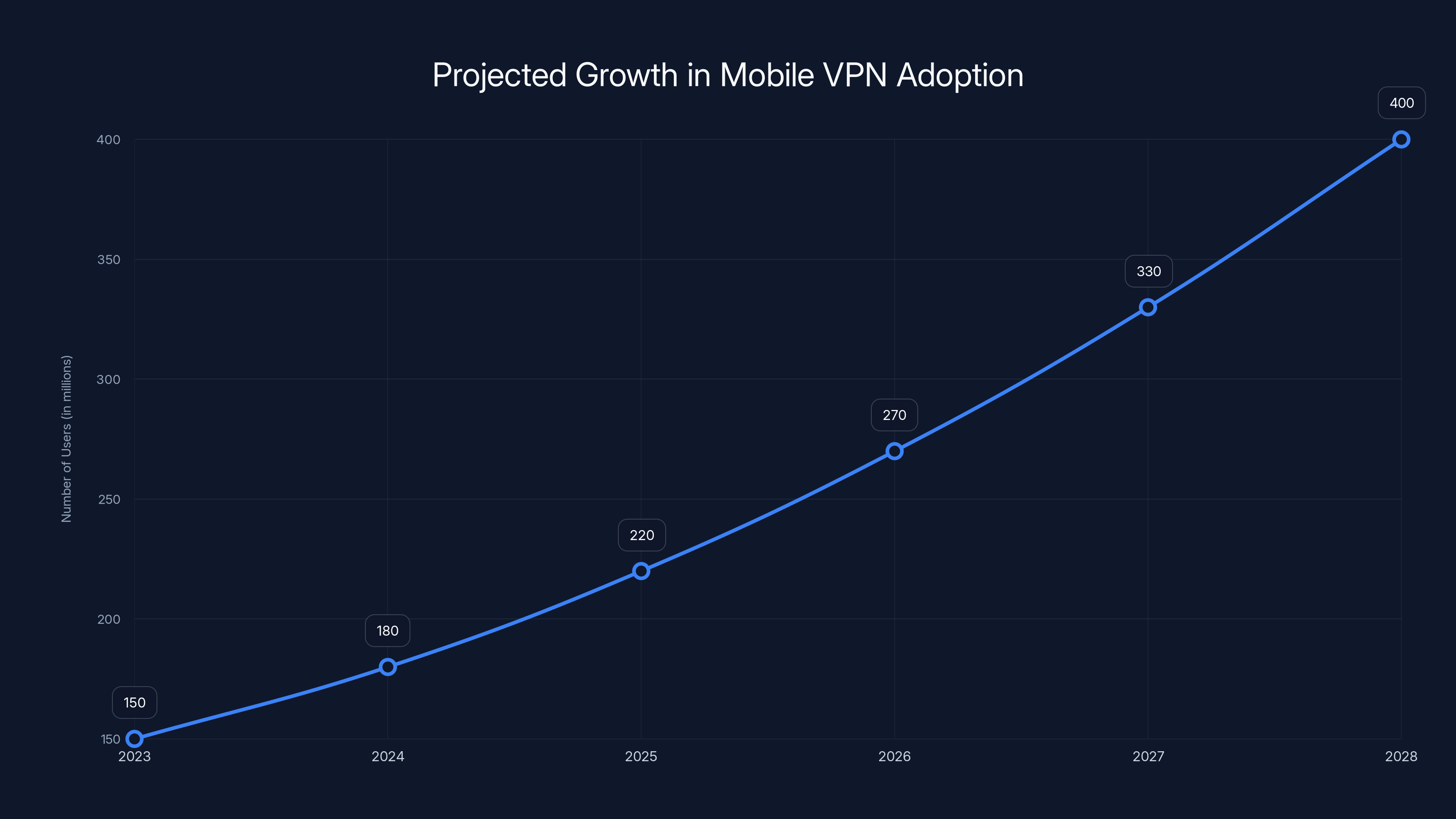
Mobile VPN adoption is projected to grow significantly, reaching 400 million users by 2028. Estimated data based on current trends.
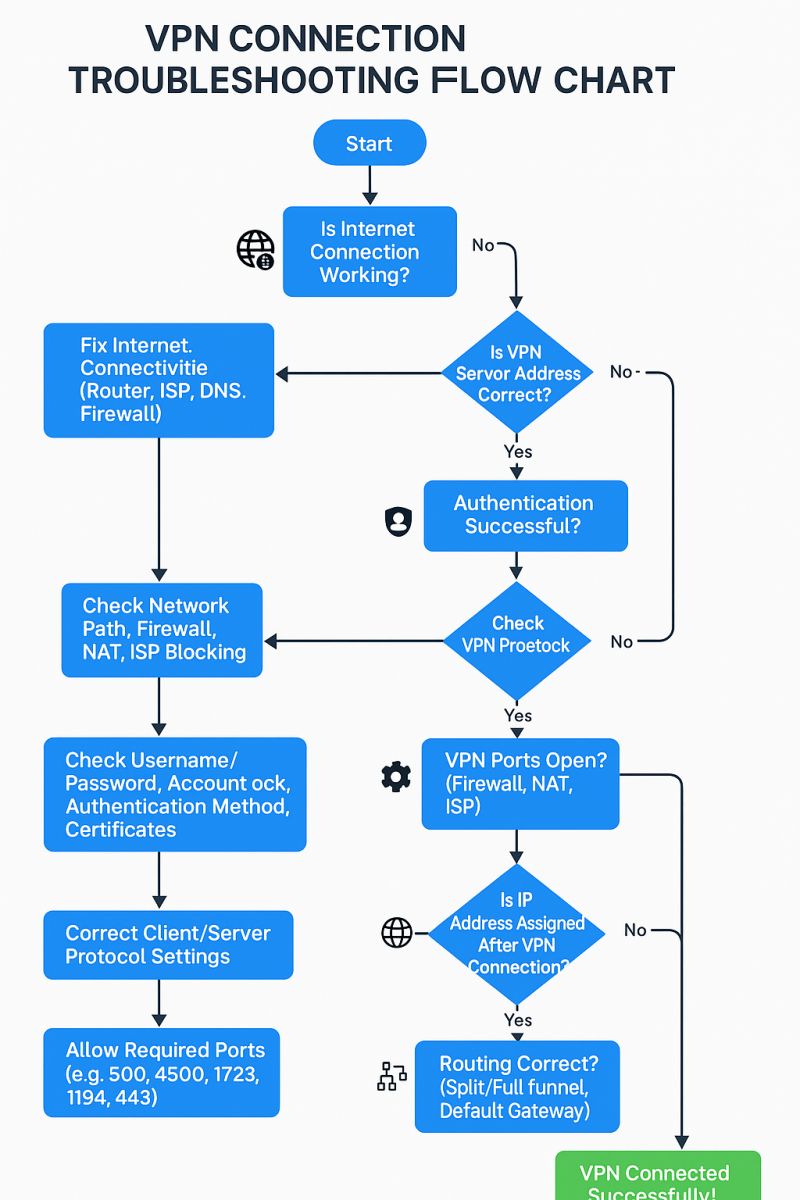
Common Pitfalls and Solutions
While Tor's mobile VPN is designed to be user-friendly, there are common issues users might encounter. Here's how to troubleshoot them.
Connection Drops
Solution:
- Ensure a stable internet connection.
- Try switching to a different server location.
- Check for app updates that may resolve connectivity issues.
Slow Speeds
Solution:
- Select a server closer to your physical location.
- Avoid peak usage times when server load is high.
Compatibility Issues
Solution:
- Ensure your device's operating system is up to date.
- Check for compatibility with other apps that might interfere with the VPN.
Real-World Use Cases
Tor's mobile VPN isn't just for tech enthusiasts. Its applications extend to various real-world scenarios where privacy is paramount.
Activism and Journalism
Activists and journalists often work in environments where privacy is critical. Tor's mobile VPN provides the anonymity they need to communicate safely.
Personal Privacy
For the average user concerned about privacy, Tor's VPN offers peace of mind by securing their online activities against surveillance.
Global Travel
Frequent travelers can use Tor's VPN to bypass geographical restrictions and access content as if they were in their home country.

Future Trends in Mobile VPN Technology
As technology continues to evolve, so too will the capabilities of mobile VPNs. Here are some trends to watch for in the coming years.
Increased Adoption of Wire Guard Protocol
Wire Guard, known for its simplicity and efficiency, is gaining popularity and may become a standard in mobile VPNs, including Tor's.
Integration with AI for Enhanced Security
AI-driven security measures can predict and mitigate threats, potentially being integrated into future iterations of Tor's VPN.
Expansion of Server Infrastructure
To meet growing demand, VPN providers, including Tor, will likely expand their server networks, improving speed and reliability.
Best Practices for Using Mobile VPNs
To get the most out of your mobile VPN, consider these best practices.
- Regularly Update the App: Ensure you have the latest security patches and features.
- Use Strong Passwords: Protect your VPN account with a strong, unique password.
- Be Mindful of Permissions: Limit app permissions to only what is necessary.
Conclusion: The Road Ahead for Tor's Mobile VPN
The launch of Tor's mobile VPN signifies a significant step forward in mobile privacy. With robust security measures and user-friendly design, it is well-positioned to meet the needs of privacy-conscious users worldwide. As technology advances, Tor's commitment to privacy will likely lead to further innovations in secure communications.

FAQ
What is Tor's Mobile VPN?
Tor's Mobile VPN is a secure and private network solution designed to enhance privacy on mobile devices by encrypting data and routing it through multiple servers.
How does Tor's VPN enhance privacy?
By encrypting data and using multi-hop routing, Tor's VPN conceals user activity from prying eyes, making it difficult for third parties to track or intercept data.
What makes Tor's VPN unique?
Its rigorous security features, including end-to-end encryption and traffic obfuscation, set it apart from other VPNs in the market.
Can I use Tor's VPN on any device?
Yes, Tor's VPN is available for both Android and iOS devices, making it accessible to a wide range of users.
How do I troubleshoot common VPN issues?
For connection drops, check your internet stability and server selection. For slow speeds, try a closer server or avoid peak times.
What future trends should I expect in mobile VPNs?
Expect advancements like the integration of AI for enhanced security and the adoption of protocols like Wire Guard for improved performance.
Why is a security audit important for VPNs?
A security audit ensures that the VPN maintains high security standards, giving users confidence in its ability to protect their data.
How can I maximize the benefits of Tor's VPN?
Regularly update the app, use strong passwords, and be mindful of app permissions to enhance your security.
Key Takeaways
- Tor's mobile VPN offers enhanced privacy through multi-hop routing and encryption.
- A successful Cure53 audit confirms the security of the VPN.
- Users benefit from a user-friendly interface and cross-platform compatibility.
- Future trends include AI integration and expanded server infrastructure.
- Best practices include regular updates and mindful permission management.
Related Articles
- Navigating Russia's VPN Crackdown: Strategies and Solutions [2025]
- How an Old Microsoft Excel Flaw Could Hijack Your System [2025]
- Cracking the Code: Exploring TotalRecall Reloaded and Windows 11's Recall Database [2025]
- Navigating the 'AI is Inevitable' Trap: Understanding the Hype and Reality [2025]
- Reed Hastings Departs Netflix: The Legacy and Future of Streaming [2025]
- Unlocking the Full Potential of Your Desktop: OpenAI's Codex Update [2025]
![Tor Project's Mobile VPN Launch: A New Era in Privacy [2025]](https://tryrunable.com/blog/tor-project-s-mobile-vpn-launch-a-new-era-in-privacy-2025/image-1-1776436458240.jpg)



