The Privacy Revolution: Mullvad VPN's Graphene OS Collaboration Explained
When two privacy-obsessed platforms decide to work together, the internet takes notice. Mullvad VPN, a Swedish privacy service known for stripping user tracking to near-zero levels, recently announced plans to expand server support specifically for Graphene OS, a hardened fork of Android designed by privacy advocates. This isn't just another partnership announcement buried in tech press releases. It's a significant moment in the ongoing battle for digital privacy and demonstrates how organizations committed to privacy principles are actively building infrastructure to support users who take security seriously.
The collaboration emerged through a public exchange on X (formerly Twitter), where both organizations discussed the technical challenges and opportunities around bringing VPN infrastructure to Graphene OS users across Europe. Graphene OS, which strips out Google's proprietary services and adds extensive security hardening, has attracted a dedicated community of users who refuse to compromise on privacy. Mullvad's decision to develop European server support represents a recognition that this community deserves infrastructure tailored to their specific needs.
What makes this particularly interesting is the philosophy driving both projects. Neither Mullvad nor Graphene OS operates like typical commercial tech companies. Mullvad doesn't collect user logs, doesn't require account creation, and has even paid external auditors to verify their privacy claims. Graphene OS, meanwhile, is maintained by a small team of security researchers who prioritize hardening over profit margins. When these two philosophies align, the result is infrastructure that genuinely serves privacy-conscious users rather than extracting value from them.
This expansion addresses a real gap in the privacy ecosystem. Users running Graphene OS have historically faced limitations when choosing VPN providers. Many major VPN services use proprietary applications that rely on Google Play Services or other closed-source components incompatible with Graphene OS. They also maintain data collection practices that contradict Graphene OS's security model. Mullvad's native integration provides an alternative that actually respects the security posture users have worked to establish on their devices.
The technical implementation deserves closer examination. European server support specifically matters because data residency and jurisdiction become critical factors in privacy protection. European servers fall under GDPR, which provides stronger legal protections against dragnet surveillance compared to servers in other jurisdictions. For users already running Graphene OS to escape US-based corporate and government tracking, having VPN endpoints within GDPR jurisdictions creates an additional layer of legal protection against data exfiltration.
This collaboration also signals something broader about how privacy infrastructure is evolving. Rather than relying on government regulation or corporate self-regulation, privacy advocates are building alternatives from the ground up. They're creating tools and services that function according to privacy principles by default, not as an afterthought. Mullvad's willingness to develop specific infrastructure for Graphene OS users demonstrates that there's growing recognition of niche but committed markets willing to pay for genuine privacy.
Understanding Graphene OS: The Android That Respects You
Graphene OS represents a fundamentally different approach to Android than what Google provides or manufacturers customize. If you've ever felt uneasy about Android's data collection practices, Graphene OS addresses those concerns directly through technical elimination rather than policy promises.
At its core, Graphene OS is a hardened fork of the Android Open Source Project. The distinction matters. Rather than removing features or cutting off functionality, Graphene OS preserves Android's core capabilities while adding security features and removing privacy-invasive components. It's like taking a car designed with tracking devices built into the engine and removing those devices while keeping the car fully functional.
The technical modifications include several critical security enhancements. The kernel uses hardened memory safety features that make exploitation more difficult. The browser implementation strips away unnecessary features that could expand the attack surface. Sandboxing is expanded and strengthened throughout the system. The permission system is more restrictive by default, requiring explicit user approval for capabilities that Android normally grants silently.
Perhaps most importantly, Graphene OS removes Google's proprietary services entirely. This means no Google Play Services tracking your location, your app usage, or your search history. No Google Cloud Messaging collecting data about your notifications. No Google Play Store connecting purchases to your identity. For users who've never considered how deeply Google's proprietary services embed themselves into Android devices, this removal often feels revelatory.
The user experience deserves attention because hardening often comes with trade-offs. Graphene OS maintains a usable interface, though certain apps requiring Google Play Services won't run without workarounds. The trade-off calculation differs for everyone. A user who needs their banking app might accept some privacy trade-offs. A journalist operating in a restrictive country might prioritize security so heavily that Graphene OS's limitations feel acceptable.
Graphene OS's development model explains its capabilities. The project is maintained by security researchers who understand threat modeling at a deep level. Unlike Android manufacturers who balance security against performance, user experience, and corporate interests, Graphene OS optimizes for security as the primary constraint. This laser focus produces a system with fewer security vulnerabilities, fewer privacy-invasive features, and fewer attack vectors than standard Android.
The community using Graphene OS tends to be technically sophisticated and motivated by strong privacy convictions. They're not casual privacy enthusiasts. They're people who understand the implications of data collection and make intentional choices to minimize their digital footprint. This community represents a market segment that conventional VPN providers have historically ignored, partly because they're small and partly because their needs diverge from mainstream expectations.
Graphene OS's relationship with app compatibility creates an interesting ecosystem constraint. Users can install apps through multiple methods: sideloading APKs directly, using alternative app stores like Aurora Store, or running Google Play Services in a sandbox. Each approach involves trade-offs between convenience and privacy. Mullvad's decision to develop native support acknowledges that Graphene OS users need tools that work smoothly within this constrained environment.
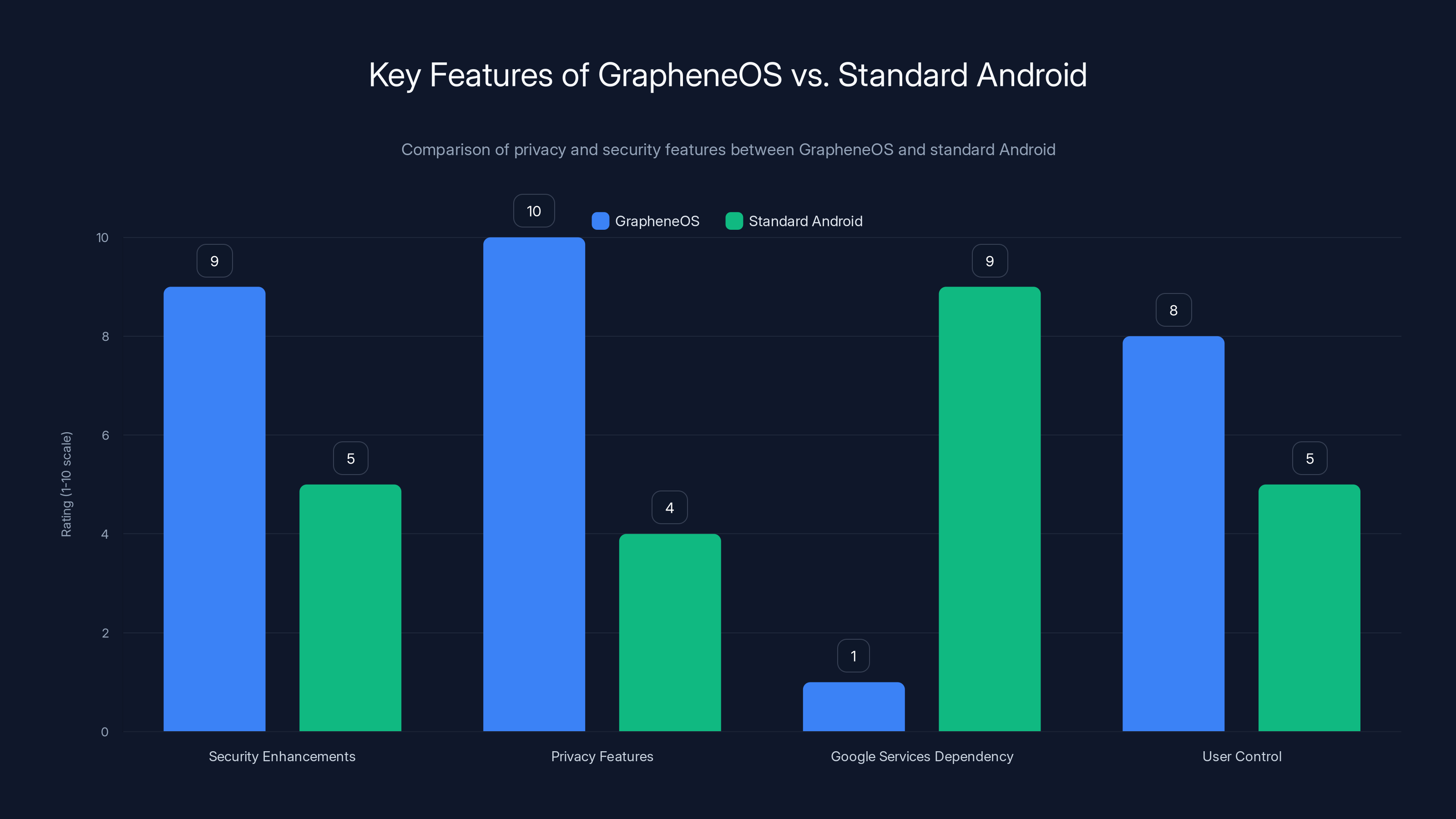
GrapheneOS significantly enhances privacy and security compared to standard Android by removing Google services and strengthening user control. Estimated data.
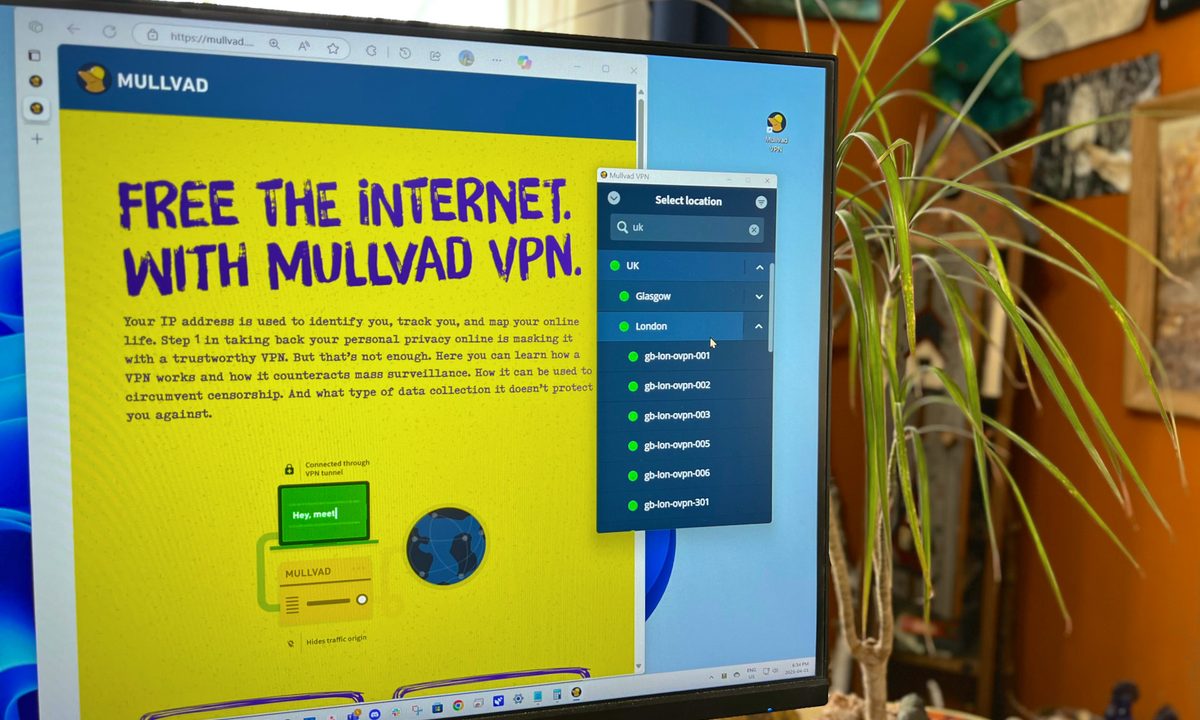
Mullvad VPN: The Privacy Provider That Actually Means It
Mullvad VPN operates from Sweden with a specific mission: maximize user privacy through technical elimination of data collection. Understanding why Mullvad stands out in the crowded VPN market requires examining what the company does differently from competitors.
Most VPN services maintain user accounts. They require email addresses, usernames, or payment information that connects transactions to identities. Mullvad removed account requirements entirely. You access their service without creating an account, without providing identifying information. You simply download the client, run it, and it works. This approach creates interesting business challenges. Without accounts, Mullvad can't implement account recovery, password resets, or personalized settings. They accept these limitations as necessary trade-offs for privacy.
Logging practices separate Mullvad from competitors. Standard VPN providers claim they don't retain user activity logs, but claims are cheap. Mullvad goes further. They've commissioned independent audits from security firms to verify their logging practices. These audits examine actual source code and system configurations to confirm that no user activity is captured. The company also implemented infrastructure architecture that makes extensive logging technically impossible. Even if a government demanded user data, Mullvad couldn't provide it because the data was never collected.
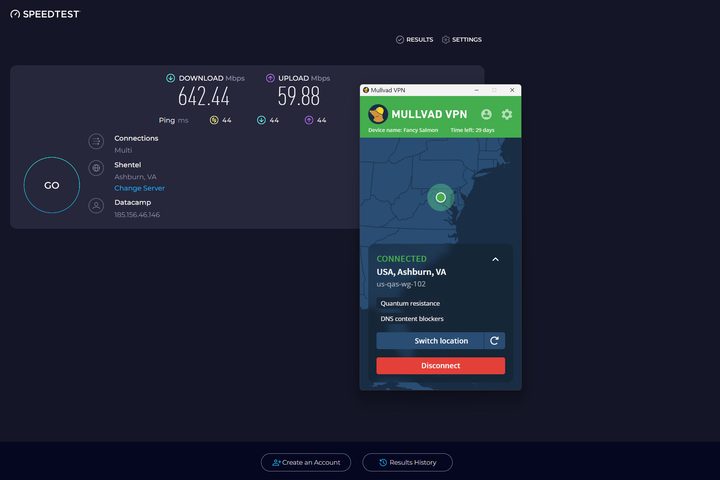
The technical architecture demonstrates Mullvad's commitment. They own and operate their own server infrastructure rather than renting from cloud providers. This ownership means they control the entire stack and can verify no backdoors exist. They use Wire Guard, a modern VPN protocol known for its security properties and code simplicity. Wire Guard's relatively small codebase makes security audits more feasible than older protocols like Open VPN.
Mullvad's business model reflects their privacy orientation. Rather than harvesting user data or targeting ads, they charge a flat monthly fee: around $5.75. This means they make money from customers who want to pay them, not from data brokers buying information about customer behavior. The pricing structure is identical for all customers, with no tiers extracting more money from customers willing to pay more.
The company's transparency practices extend beyond technical implementation. Mullvad publishes detailed information about their network architecture, their security practices, their privacy policies. They've even shared vulnerability disclosures about issues found in security audits. This transparency doesn't eliminate the need for trust, but it provides users ways to verify claims rather than accepting assertions on faith.
Mullvad's expansion toward Graphene OS represents a natural evolution of their privacy philosophy. Graphene OS users are exactly the customers Mullvad designed their service for: people who care deeply about privacy and are willing to accept technical limitations to achieve it. Standard VPN providers wouldn't bother developing specialized support for a small user base with niche requirements. Mullvad's decision to do so demonstrates their commitment extends beyond marketing language.

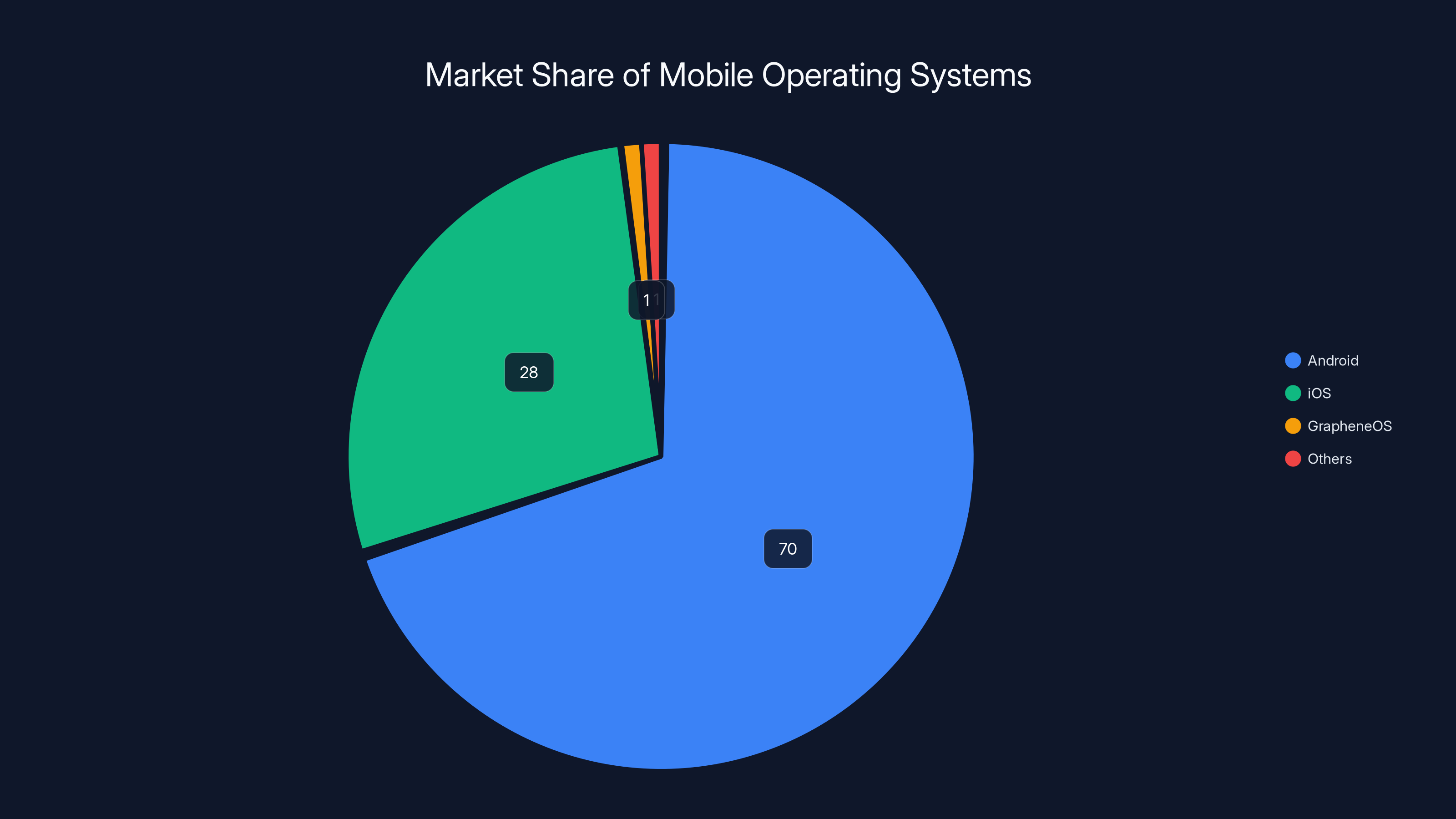
GrapheneOS holds a small estimated market share of 1%, yet attracts privacy-focused users who value Mullvad's services. Estimated data.
The Technical Challenge: Building VPN Infrastructure for Privacy-First Systems
Developing VPN support for Graphene OS presents unique technical challenges that mainstream VPN providers never consider. These challenges explain why Mullvad's decision to invest resources in this effort matters more than casual observers might realize.
Graphene OS's sandbox restrictions create the most immediate challenge. The operating system restricts privileged network access more severely than standard Android. Apps can't capture all device traffic without explicit system-level permissions that Graphene OS's permission model makes difficult to grant. Standard VPN applications rely on VPN APIs that integrate deeply with Android's network stack, often requiring permissions that conflict with Graphene OS's security model. Mullvad must develop implementation approaches that work within Graphene OS's stricter constraints.
The lack of Google Play Services eliminates another convenient development path. Many Android apps rely on Google's libraries for networking, cryptography, or system integration. Developing for Graphene OS requires building these capabilities independently or using alternative libraries. This increases development complexity and requires more thorough testing to ensure reliability.
European server infrastructure introduces jurisdictional considerations beyond simple server provisioning. European data protection laws impose specific requirements about data retention, processing, and user notification. Building infrastructure compliant with GDPR requires more sophisticated data handling practices than servers operating in other jurisdictions. It also requires legal expertise alongside technical expertise.
The user base's technical sophistication cuts both ways. Graphene OS users understand networking, security, and privacy implications at deeper levels than typical VPN users. This means Mullvad can implement more sophisticated privacy features that typical users wouldn't understand or want. But it also means users will scrutinize implementation details more carefully and demand justification for design decisions.
Network architecture decisions become more complex for privacy-first systems. Mullvad must decide whether to implement all privacy-oriented features or accept limitations to ensure basic functionality. They must balance feature completeness against the risk of implementation errors that could compromise privacy. For a service built around privacy guarantees, security bugs don't just reduce functionality. They undermine the entire value proposition.
The international legal landscape creates additional complications. European servers operating under GDPR provide legal advantages for privacy, but they also subject Mullvad to European regulations. The company must navigate conflicts between different legal systems, data protection requirements, and law enforcement requests across multiple jurisdictions. This complexity explains why most VPN providers avoid European infrastructure entirely.

European Server Infrastructure: Why Jurisdiction Matters
Understanding why Mullvad chose European servers specifically requires examining how legal jurisdiction affects privacy protection. Data residency isn't just a technical decision. It's a strategic choice with real implications for user protection.
The European Union's General Data Protection Regulation represents the world's most comprehensive data protection framework. GDPR grants users specific rights regarding their personal data, mandates transparency about data processing, and imposes obligations on organizations handling European data. Perhaps most importantly for privacy-conscious users, GDPR restricts certain forms of surveillance that are legal in other jurisdictions.
Data stored in European jurisdictions receives legal protection that US-based servers don't provide. While law enforcement in most jurisdictions can request user data, European courts require more rigorous justification for bulk data collection or dragnet surveillance. GDPR's compliance requirements mean organizations must document their data handling practices, which creates accountability that's absent in jurisdictions with weaker privacy laws.
Mullvad's Swedish location adds another layer. Sweden has particularly strong privacy protections and limited surveillance infrastructure compared to other European countries. Swedish courts traditionally require robust legal justification before authorizing surveillance or data requests. This legal environment aligns with Mullvad's privacy mission better than other European jurisdictions might.
The treaty landscape matters as well. Swedish law and GDPR create multilayered legal protections that make mass surveillance more difficult than in countries with weaker frameworks. While sophisticated governments can still find ways to access data when sufficiently motivated, the legal barriers are higher and the accountability is greater.
For Graphene OS users, particularly those in high-risk situations, European server jurisdiction provides meaningful protection beyond technical encryption. A journalist operating in a country with weak press freedoms benefits not just from encryption making data unreadable, but from legal frameworks making data requests more difficult to execute. A human rights activist gains protection from legal systems that limit surveillance authorities rather than enabling them.
This doesn't mean European servers provide perfect privacy. No server location guarantees perfect privacy. Determined governments can pressure service providers or deploy more sophisticated technical capabilities. But European infrastructure creates legal and operational friction that increases the cost and reduces the likelihood of successful surveillance compared to other options.
Mullvad's expansion toward European servers also signals commitment to their stated values. Companies often claim privacy commitments while maintaining infrastructure in surveillance-friendly jurisdictions. Mullvad's willingness to expand European presence demonstrates they're willing to accept operational complexities and legal constraints to align infrastructure with privacy principles.

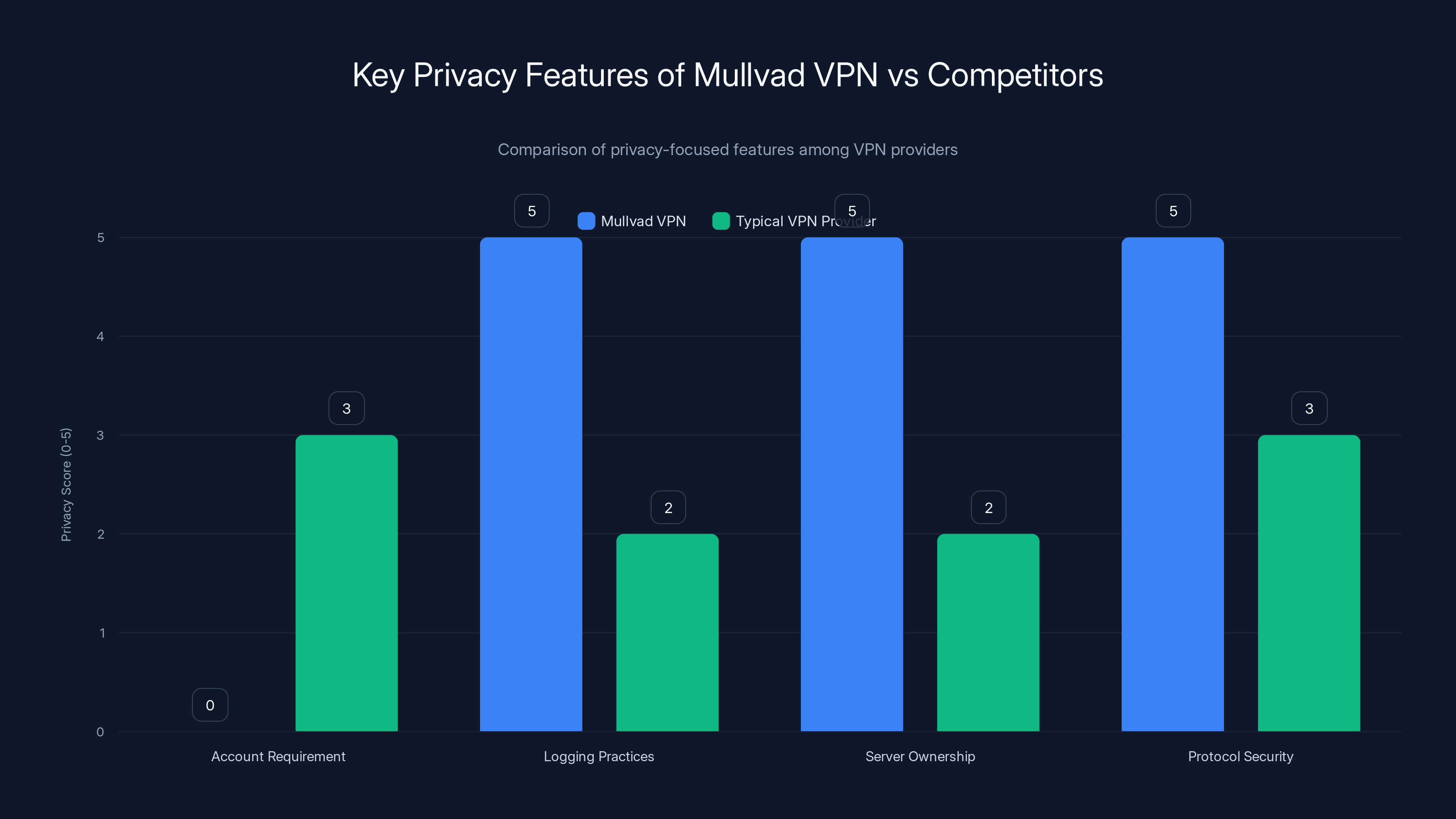
Mullvad VPN excels in privacy by eliminating account requirements, implementing strong logging practices, owning its server infrastructure, and using secure protocols. Estimated data based on typical VPN practices.
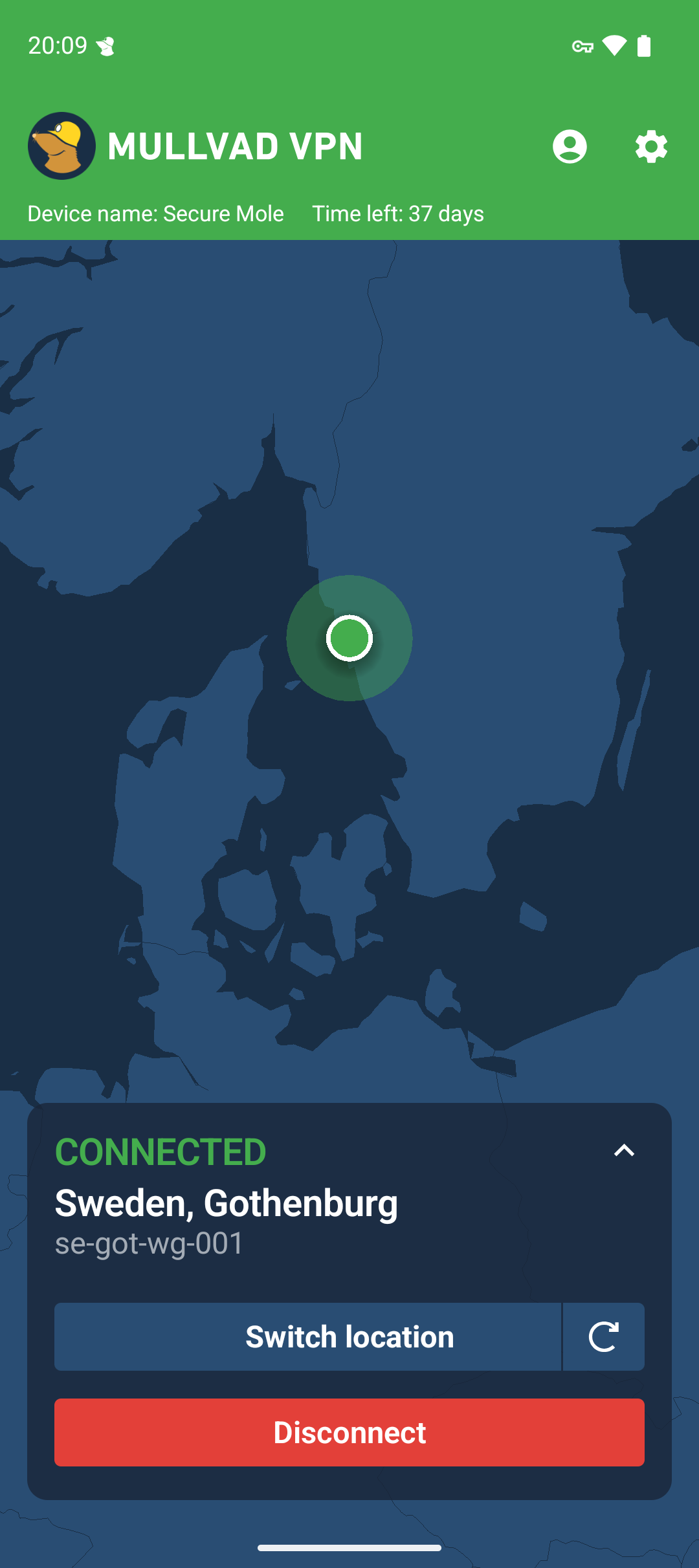
VPN and Graphene OS Integration: A Practical Perspective
The integration of VPN services with Graphene OS involves more practical considerations than technical privacy features alone. Users need reliable, usable tools that work seamlessly within their chosen operating system.
Mullvad's native integration addresses several practical pain points Graphene OS users encounter. First, app updates become automatic and straightforward. Graphene OS users who sideload apps must manually check for and install updates. Mullvad's potential integration through alternative app stores or native methods simplifies this process significantly. Users get security patches and new features without manual intervention.
Configuration complexity drops substantially with native integration. Standard VPN setup on Graphene OS requires multiple manual steps, including sideloading the APK, manually granting permissions, and configuring settings through the interface. A native integration could streamline this entire process, reducing barriers to adoption for less technical users.
Performance and battery efficiency matter more on mobile devices than desktop systems. VPN clients can be resource-intensive, consuming battery and creating network overhead. Mullvad's native optimization for Graphene OS could implement efficiency improvements specifically tailored to the operating system's architecture. This matters for users who prioritize both privacy and usability.
Trust becomes paramount in privacy applications. Users running Graphene OS made deliberate choices to trust a specific operating system. Introducing software from unfamiliar vendors requires assessing whether that software respects the security model they've established. Mullvad's reputation for privacy provides a natural fit that increases user trust more than generic VPN providers might.
The kill switch feature becomes more critical on mobile than desktop. A kill switch prevents traffic leakage if the VPN connection drops, ensuring users never accidentally transmit unencrypted traffic. This feature is essential but requires careful implementation on mobile platforms where network conditions change frequently. Mullvad's native implementation could handle these transitions more gracefully than generic solutions.
Persistent configuration creates another practical consideration. Mobile devices frequently switch networks—from home Wi Fi to cellular to coffee shop Wi Fi. Maintaining consistent VPN configuration across these transitions requires sophisticated state management. Native integration allows Mullvad to handle these transitions transparently.
Notification and interface design must communicate important information without creating security vulnerabilities. A native integration allows Mullvad to design interfaces that inform users about connection status while respecting Graphene OS's security model. Third-party overlays and notifications create potential attack surfaces that native integration can avoid.

Privacy Implications: Why This Collaboration Matters
The combination of Graphene OS and Mullvad VPN creates a significantly more private mobile device than either technology provides independently. Understanding why requires examining how privacy is constructed from multiple layers.
Graphene OS eliminates data collection by proprietary Google services at the operating system level. This prevents entire categories of tracking that users typically can't avoid on standard Android. But Graphene OS doesn't prevent your ISP from seeing which servers you connect to, your network traffic patterns, or metadata about your communications. This is where VPN infrastructure becomes critical.
Mullvad's VPN encrypts your network traffic and routes it through servers configured to minimize data collection. Combined with Graphene OS's elimination of OS-level tracking, the result is a device that collects minimal personal data about your activities. The combination creates privacy guarantees that neither technology could provide alone.
Consider a specific scenario: a person using Graphene OS opens a web browser to research a sensitive health topic. Graphene OS ensures that Google doesn't track this activity through proprietary services. But the person's ISP still sees that they connected to a particular website, and that website sees they visited from their home IP address. Adding Mullvad's VPN masks the connection from the ISP and obscures the user's IP address from the website. The privacy protection becomes substantially stronger.
This layered approach also protects against different categories of threats. Graphene OS protects against malware, unauthorized local access, and corporate tracking through built-in services. A VPN protects against ISP surveillance, network-level monitoring, and geographic identification. Together, they create defenses against multiple threat categories rather than addressing only a single concern.
For certain users, this combination becomes practically essential rather than just advisable. Journalists in countries with internet surveillance regimes need both hardened operating systems and network-level privacy protection. Human rights activists operating in authoritarian contexts benefit from multiple privacy layers because losing privacy in any single layer could create serious consequences. Dissidents seeking to communicate without government monitoring need exactly the kind of protection that Graphene OS and Mullvad together provide.
The collaboration also signals how privacy architecture is evolving. Rather than expecting a single tool to solve all privacy challenges, the privacy community is building ecosystems of complementary tools that work together. Graphene OS handles operating system privacy, Mullvad handles network privacy, and thoughtful users combine them with additional privacy practices like encrypted communications. This ecosystem approach is more robust than expecting any single tool to provide complete privacy.

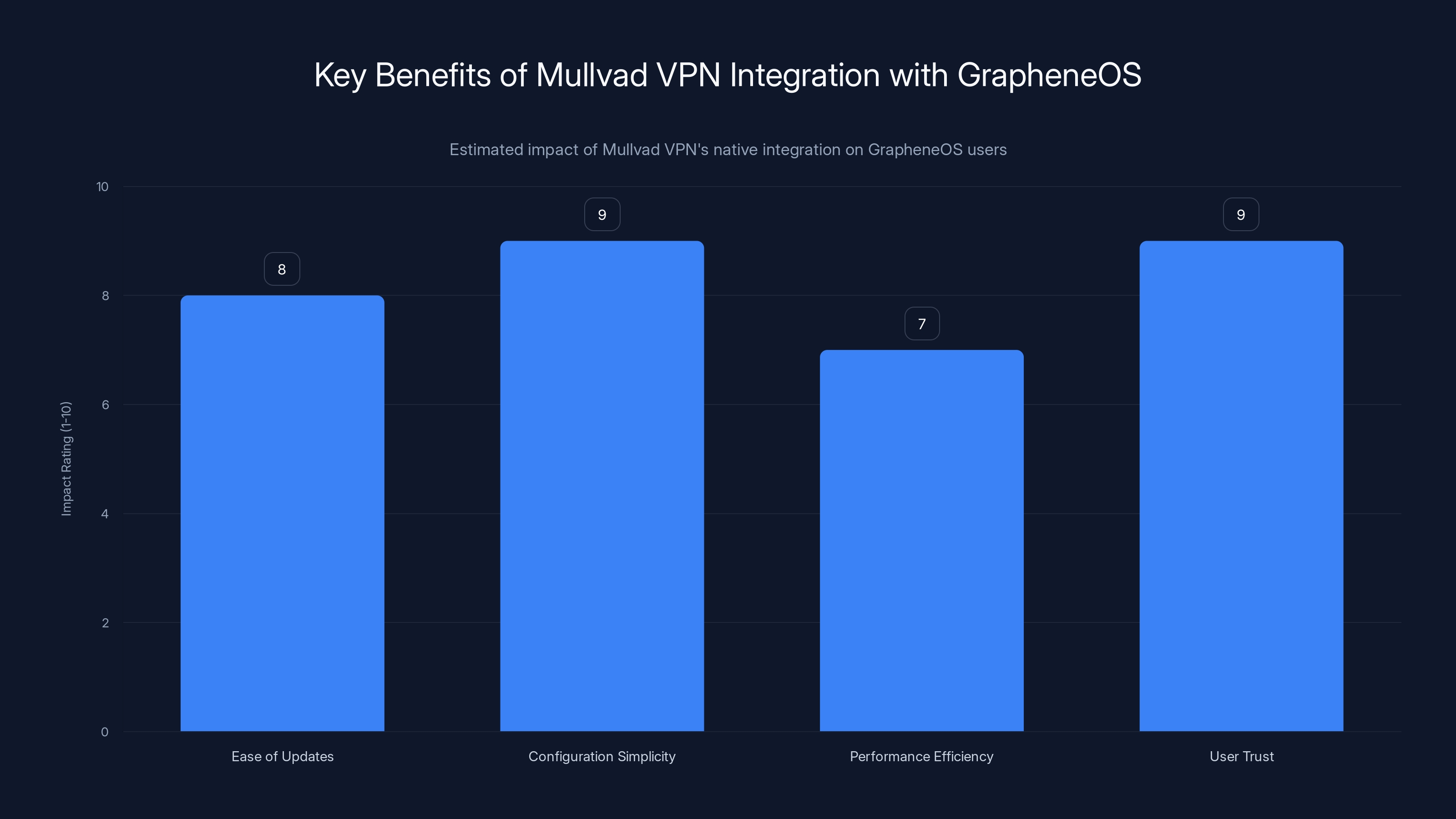
Mullvad's native integration with GrapheneOS is estimated to significantly improve ease of updates, configuration simplicity, and user trust, while also enhancing performance efficiency. (Estimated data)
The Business Case: Supporting Niche Markets With Real Needs
From a business perspective, Mullvad's decision to develop Graphene OS support seems irrational. Graphene OS users represent a small fraction of the mobile market. They're technically sophisticated and often resistant to paying premium prices. They're vocal about their concerns and unlikely to accept subpar implementations. Why would a VPN provider invest resources in this market?
The answer lies in understanding Mullvad's business model and values alignment. Mullvad doesn't maximize revenue extraction by building features that appeal to mass markets or targeting users willing to tolerate privacy trade-offs. Instead, Mullvad targets users who explicitly care about privacy and operates according to principles that these users respect. For such a company, Graphene OS users are perfect customers.
Graphene OS users are willing to pay for privacy. They've already demonstrated this by choosing a specialized operating system and investing time in learning how to use it. They're not comparing Mullvad against mainstream VPN services on price or feature checklists. They're evaluating whether Mullvad's approach aligns with their privacy philosophy. When it does, they become long-term customers who willingly pay for the service.
These users are also brand ambassadors. They discuss privacy tools in their networks, recommend services that respect their values, and create organic word-of-mouth marketing that money can't buy. Supporting Graphene OS users builds Mullvad's reputation within the privacy-conscious community as a service that takes privacy seriously enough to support niche use cases.
Moreover, the technical challenges of supporting Graphene OS benefit Mullvad's broader development. Solving the problems of providing VPN services on hardened, restrictive systems often produces innovations applicable to other contexts. Technologies developed for Graphene OS support might improve privacy and security for all Mullvad users.
The market dynamics also favor this strategy. As more people become aware of privacy issues and seek solutions, the pool of potential Graphene OS users is likely to grow. Establishing strong presence in this community early positions Mullvad to benefit from this growth. They're building market share with early adopters in a market segment that mainstream providers are ignoring.

Security Considerations: Building Trustworthy Infrastructure
When infrastructure is designed specifically for privacy, security becomes inseparable from privacy. Users running Graphene OS have made specific threat model assumptions, and VPN infrastructure must align with those assumptions rather than introducing new vulnerabilities.
Mullvad's commitment to security audits becomes particularly important in this context. An open-source client running on Graphene OS needs to be thoroughly vetted because users have eliminated so many other attack surfaces. Any security vulnerability in the VPN client becomes a disproportionately serious problem because it might represent one of the few ways a sophisticated attacker could compromise the device.
The implementation language matters. Modern VPN clients often use memory-unsafe languages like C or C++ that create potential for vulnerabilities. Mullvad has explored using Rust, a memory-safe language, for certain components. This language choice reduces entire categories of potential vulnerabilities even if other code has security issues.
Updates and patch delivery create another security consideration. VPN software must be updated frequently to address discovered vulnerabilities. For Graphene OS users, getting security updates should be seamless and automatic. Mullvad must ensure that their Graphene OS implementation provides reliable, timely updates without requiring users to manually download and install them.
The kill switch implementation requires particular security attention. A broken kill switch could leak unencrypted traffic while the user thinks they're protected. The implementation must handle all edge cases: rapid network transitions, sudden VPN disconnections, system sleeps and wakeups, and app restarts. Every scenario must default to a blocked connection rather than allowing leakage.
DNS leakage represents another security risk worth addressing. When your VPN connection drops, your operating system might try to resolve DNS queries without the VPN, revealing which servers you tried to connect to. Mullvad's Graphene OS implementation should prevent this through forced DNS handling that works within Graphene OS's constraints.
Certificate validation and HTTPS implementation can't be taken for granted. VPN apps handle network connections in ways that can bypass certain security checks. Mullvad must ensure that any included browser or connectivity features properly validate SSL certificates and prevent man-in-the-middle attacks.
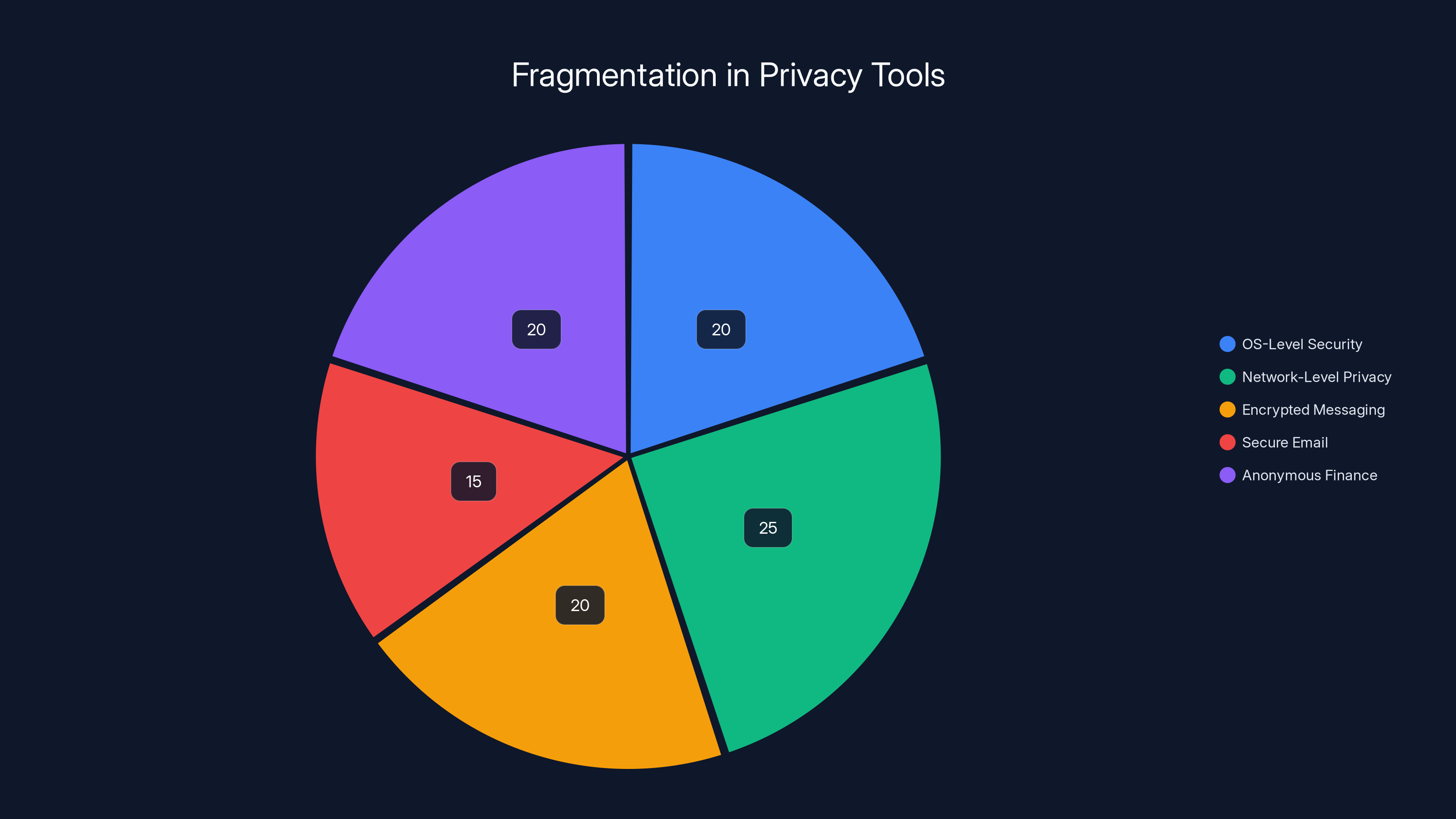
Estimated data shows a balanced focus among different privacy tool areas, indicating healthy fragmentation and specialization in the privacy ecosystem.
Future Evolution: What Graphene OS and Mullvad Integration Suggests
The collaboration between Graphene OS and Mullvad hints at broader trends in how privacy infrastructure is evolving. Understanding these trends helps contextualize why this specific partnership matters beyond the immediate technical benefits.
We're seeing increasing fragmentation in how people approach digital privacy. Rather than assuming everyone will use the same operating system and the same services, privacy advocates are building specialized tools for specific use cases and threat models. Graphene OS targets users who prioritize OS-level security and don't need Google integration. Mullvad targets users who want network-level privacy without account requirements. The fragmentation continues with encrypted messaging apps, secure email, anonymous finance solutions, and countless other privacy tools.
This fragmentation is actually healthy. A monolithic privacy solution creates a single point of failure where a vulnerability could compromise an entire user base. Multiple tools with different architectures, different trade-offs, and different threat models create a more robust ecosystem. Users can choose combinations that match their specific risks and requirements.
The partnership also suggests that privacy advocates are increasingly willing to invest in small, niche markets. Ten years ago, the assumption was that privacy tools needed to compete on consumer features to achieve adoption. Now we're seeing that dedicating resources to users who explicitly care about privacy, even if they're small in number, can be a sustainable business model. This unlocks development of privacy infrastructure that wouldn't make sense optimized for mass market adoption.
We might also expect this model to expand to other platforms and devices. If Mullvad succeeds with Graphene OS on Android, the logical next step is exploring support for other privacy-focused operating systems. Similarly, other VPN providers and privacy tool developers might follow Mullvad's lead in developing specialized support for niche systems. This creates positive competition where companies differentiate by how seriously they take privacy rather than by feature count alone.
The collaboration also signals that privacy is becoming a serious infrastructure concern rather than a niche hobbyist interest. When established organizations like Mullvad are willing to invest resources in supporting small user communities, it indicates that privacy tools are transitioning from experimental projects to essential infrastructure. This maturation will likely accelerate development of privacy technologies and increase their reliability.

Practical Guidance: Should You Use Graphene OS and Mullvad Together?
The combination of Graphene OS and Mullvad VPN creates a powerful privacy setup, but it's not ideal for everyone. Evaluating whether this approach makes sense requires honest assessment of your specific needs, technical capabilities, and willingness to accept trade-offs.
Graphene OS makes sense if you've experienced concern about corporate data collection, specifically from Google. If you regularly think about where your data goes, who has access to it, and how it's being used, Graphene OS addresses these concerns more completely than any privacy-focused configuration of standard Android. The operating system is stable and usable for most people, though some apps won't work without additional configuration.
Mullvad makes sense if you want network-level privacy and don't want to manage accounts. If your primary concern is ISP surveillance, network monitoring, or geographic identification, Mullvad provides straightforward protection. The lack of accounts is actually an advantage if privacy is your concern, because it eliminates one more way you could be identified.
Together, they make sense if you're willing to invest effort in learning how both systems work and accepting that not every convenient feature will be available. This combination requires deliberate choices about which apps to use, how to configure your system, and what trade-offs you're willing to make. If you want maximum convenience with minimal attention to privacy details, this setup isn't for you.
If you work in journalism, human rights advocacy, or political organizing in restrictive environments, this combination becomes practically necessary rather than aspirational. The privacy protections justify accepting limitations because the alternative is unacceptable exposure.
For everyday privacy concerns in liberal democracies, Graphene OS alone often provides sufficient protection without needing additional VPN infrastructure. Your risk profile guides the decision. The higher your risk of targeted surveillance, the more layers of protection make sense.
Implementation requires technical competence. You need to understand sideloading apps, managing APK files, and troubleshooting when integrations don't work perfectly. If you're uncomfortable with these tasks, Graphene OS might be frustrating. Similarly, Mullvad's lack of account recovery means you need to document your settings and payment method separately. These aren't deal-breakers, but they require deliberate attention.

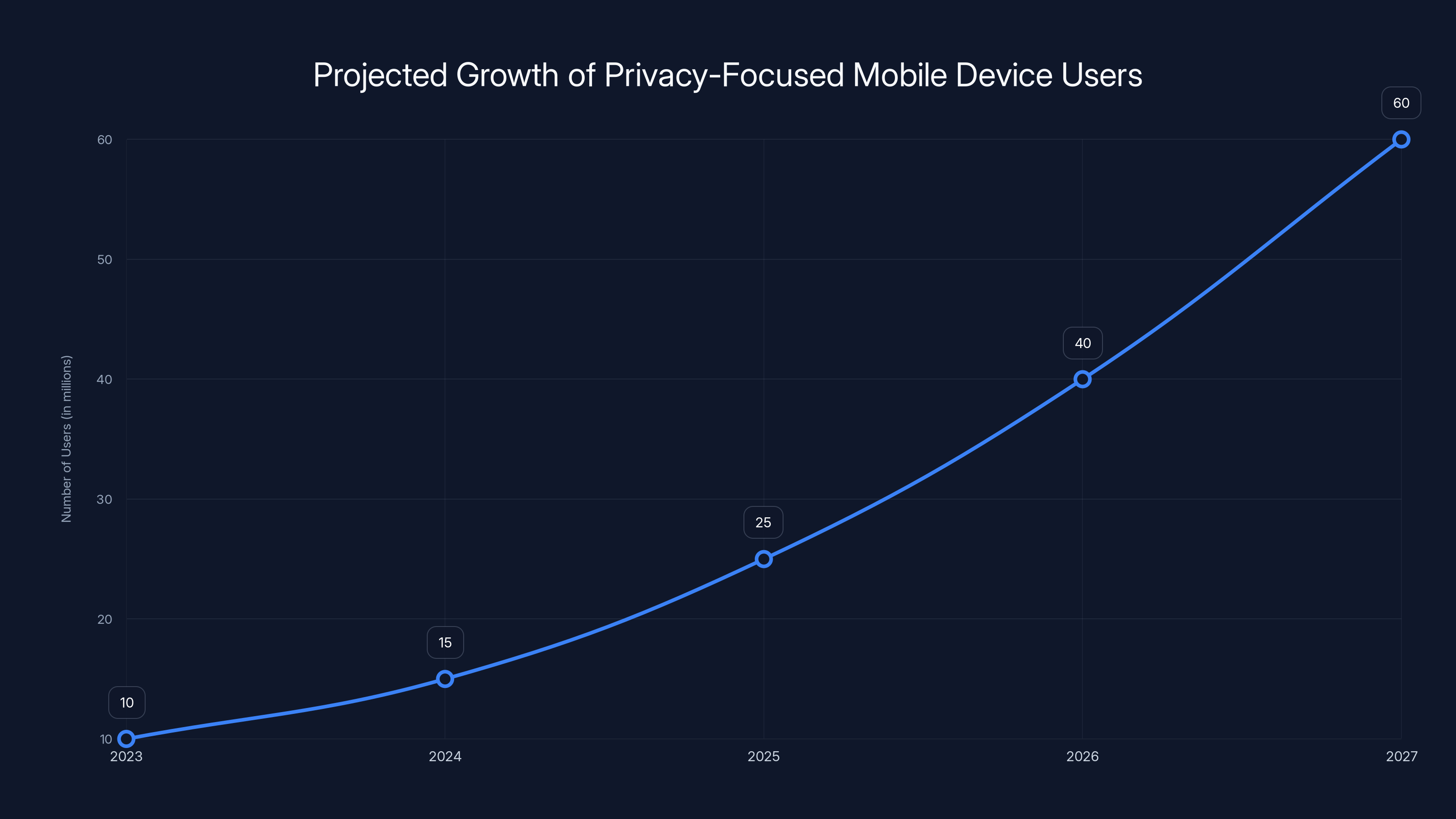
Estimated data shows a significant increase in users of privacy-focused mobile devices, driven by heightened privacy awareness and technological advancements.
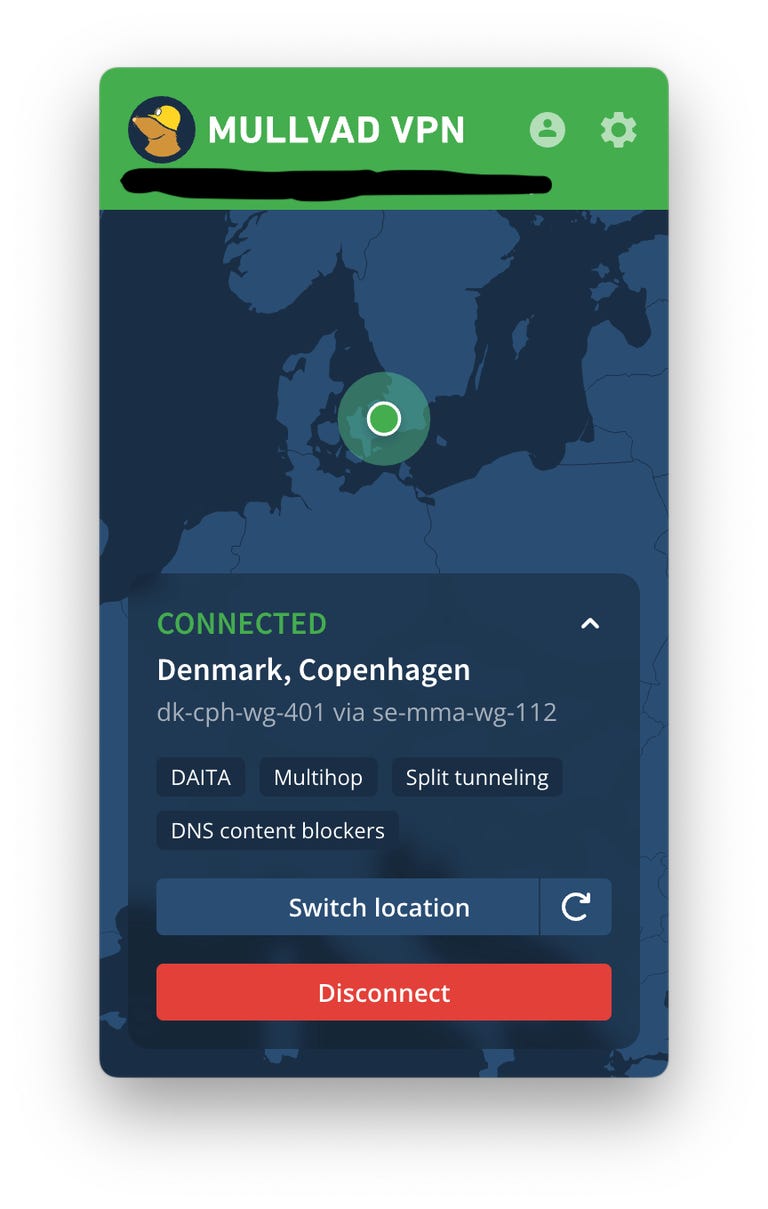
Alternative Privacy Solutions and How They Compare
Mullvad and Graphene OS aren't the only privacy tools available. Understanding alternatives helps contextualize why this particular combination appeals to certain users while other solutions might make more sense for different situations.
Standard Android with privacy-focused configuration offers better app compatibility than Graphene OS. Using apps like Blokada for privacy, Nextdns for DNS filtering, or FDroid for privacy-respecting apps provides meaningful privacy improvements over default Android. This approach requires less technical sophistication than Graphene OS and provides app compatibility that Graphene OS can't match. For most people, these improvements are substantial and the trade-offs are acceptable.
Other VPN providers offer different privacy models. Express VPN, Proton VPN, and Mullvad all prioritize privacy, but they implement different approaches. Some maintain minimal logs but still require account creation. Others provide more features like ad blocking or malware detection. The choice between them depends on your specific needs and what trade-offs you prefer.
Calyx OS represents another hardened Android fork similar to Graphene OS but with some different design decisions. Calyx OS includes more automatic integration with privacy tools and takes a slightly different approach to app compatibility. Some users prefer Calyx OS, while others strongly prefer Graphene OS's design. The differences are significant enough that preference often depends on your specific use case and how much you value certain features.
Apple's i Phone with privacy settings configured offers strong privacy compared to standard Android, though different privacy characteristics than Graphene OS. Apple controls the entire hardware and software stack, enabling privacy protections that Android's open architecture makes more difficult. However, Apple's business model relies more on hardware sales than data extraction, creating different incentive structures than Google's. Choosing i Phone versus Graphene OS involves trust assumptions about different organizations.
Tor Browser on any operating system provides anonymity that standard VPNs don't. Tor routes traffic through multiple relays, making tracing traffic to its source substantially more difficult than standard VPNs. However, Tor's latency makes it impractical for all traffic, and its slower speeds make it unsuitable for streaming or high-bandwidth activities. Tor works best for specific privacy-critical activities rather than general internet usage.
Each solution represents different trade-offs between privacy, usability, app compatibility, and cost. No single solution is universally best. The right choice depends on your threat model, technical capability, and what privacy aspects matter most to you.
Implementation Challenges: What Makes Graphene OS Support Difficult
Developing for Graphene OS creates challenges that don't exist on standard Android. Understanding these challenges explains why Mullvad's investment in support is meaningful and why mainstream VPN providers haven't already done this.
The permission model on Graphene OS is restrictive by design. Apps can't request broad permissions and assume they'll be granted. Instead, Graphene OS requires explicit user approval for sensitive permissions. A VPN app needs deep system access that the Android permission model wasn't originally designed to grant transparently. Mullvad must find ways to request necessary permissions that work within Graphene OS's stricter constraints.
App store availability creates another challenge. Google Play Store is designed to enforce Google's policies and often conflicts with privacy-first practices. Graphene OS users typically sideload apps or use alternative app stores like Aurora Store. Mullvad must develop distribution channels that work for users who explicitly avoid official app stores. This requires building infrastructure that mainstream app developers never need to consider.
Compatibility testing becomes more complex on Graphene OS. Standard Android has massive variability in device types, manufacturers, customizations, and Android versions. Graphene OS adds another layer of variability where different hardware configurations interact with the hardened operating system in ways that don't exist elsewhere. Mullvad must test across this matrix of possibilities to ensure reliability.
The user documentation and support requirements expand substantially. Graphene OS users expect detailed information about how Mullvad interacts with their system, what data is collected, and how the implementation works. Mainstream VPN providers can often succeed with sparse documentation because users don't scrutinize implementations as carefully. Mullvad must provide detailed technical documentation that explains their approach in ways that satisfy technically sophisticated users.
Feature parity becomes complicated. Mullvad probably can't implement every feature on Graphene OS that they implement on standard Android. Users expect to understand which features work and which don't, and why. Mullvad must clearly communicate these limitations without making the implementation seem incomplete.
Performance optimization requires Graphene OS-specific work. VPN clients typically run as system-level services. Graphene OS's approach to system architecture and resource management differs from standard Android in ways that affect performance. Mullvad's implementation must optimize specifically for Graphene OS's architecture rather than assuming standard Android characteristics.
The Broader Privacy Ecosystem: How This Fits Into Larger Trends
The Mullvad-Graphene OS collaboration represents one node in a larger ecosystem of privacy tools and services that are maturing and connecting. Understanding this broader context helps explain why this specific partnership matters.
Privacy infrastructure is transitioning from hobbyist projects to professional, maintained services. Mullvad's decision to invest resources in supporting a niche platform signals that privacy tools are becoming serious business concerns. Users and organizations can rely on these tools with confidence that development will continue, security vulnerabilities will be patched, and the services will remain available.
We're also seeing increasing professionalization of the privacy advocacy community. Organizations like Graphene OS development team and Mullvad are led by security professionals with deep expertise. This expertise enables them to make principled decisions about privacy and security rather than following market trends. It also enables them to maintain high standards of implementation that users can trust.
The privacy tools ecosystem is becoming increasingly international and decentralized. Rather than privacy solutions being dominated by US-based companies, we're seeing important projects emerge from Europe, Latin America, and other regions. This geographic diversity reduces dependence on any single legal jurisdiction and creates redundancy in critical infrastructure.
Interoperability is improving as privacy tools mature. Graphene OS works better with Tor Browser, with Mullvad VPN, with Proton Mail, and with other privacy-focused services than it did five years ago. This improving interoperability means users can build privacy setups from best-of-breed components rather than being forced to use all-in-one solutions that compromise on specific features.
The financial models supporting privacy tools are also becoming more sophisticated. Rather than relying only on user payments, privacy organizations are exploring grants, donations, sponsorships from aligned organizations, and other funding mechanisms that reduce pressure to compromise on principles. This funding diversity creates more sustainable businesses that can survive without selling out.

Legal and Regulatory Landscape: How Jurisdiction Affects Privacy Infrastructure
The regulatory environment in which privacy tools operate has profound implications for how they're designed, where they're located, and what services they can provide. Understanding this landscape requires examining how different jurisdictions treat privacy infrastructure and VPN services specifically.
European Union regulations, particularly GDPR, create stringent requirements for organizations handling personal data. For Mullvad, expanding European infrastructure means complying with GDPR's transparency requirements, data protection obligations, and user rights provisions. These requirements are more burdensome than regulations in other jurisdictions, but they also provide legal protections for users that weaker regulatory environments don't offer.
Some countries actively restrict or ban VPN services. Russia, China, Iran, and several other authoritarian regimes have made VPNs illegal or heavily regulated. This creates challenges for VPN providers trying to serve users in these regions while operating from jurisdictions with different legal frameworks. Mullvad's approach of not maintaining user accounts makes serving users in restricted regions somewhat easier, but legal risks still exist.
Law enforcement across different jurisdictions creates pressure on VPN providers. When US law enforcement investigates crimes, they frequently subpoena VPN providers for customer information. Mullvad's architecture makes this less problematic because the company doesn't maintain customer data that could be subpoenaed. But European law enforcement operates differently, and complying with European legal requests while maintaining privacy principles requires careful implementation.
Data localization requirements in some jurisdictions mandate that personal data be stored within the country. This creates challenges for truly international privacy services. Mullvad's expansion into European infrastructure helps address these requirements for European users, though fully complying with all data localization mandates would require infrastructure in numerous countries.
The international nature of internet infrastructure creates ongoing tension between service providers' desire for simplicity and different jurisdictions' legal requirements. Mullvad must navigate these competing requirements by hosting infrastructure in multiple jurisdictions and implementing practices that comply with the most restrictive requirements wherever possible.
Looking Forward: The Future of Privacy Mobile Devices
The Graphene OS and Mullvad collaboration hints at what privacy-focused mobile devices might look like in the coming years. Extrapolating from current trends suggests several likely developments.
We'll likely see more collaboration between privacy infrastructure providers. Just as Mullvad is integrating with Graphene OS, we might expect partnerships between Mullvad and other privacy tools, between Graphene OS and other privacy services, and between providers in different categories. These partnerships will create seamless privacy experiences where tools work together rather than requiring users to manually integrate them.
The number of users attracted to privacy-focused solutions will probably grow. As corporate data collection becomes increasingly visible and surveillance becomes more sophisticated, more people will seek privacy tools. This growth will encourage more investment in privacy infrastructure and make privacy solutions more accessible to non-technical users.
Privacy tools will become more optimized for specific use cases. Rather than building one-size-fits-all solutions, we'll see tools increasingly tailored for journalists, activists, business people, and regular consumers. This specialization will enable better addressing of specific threat models and needs.
Hardware will increasingly integrate privacy features. Phone manufacturers will begin adding privacy-focused features to compete with specialized systems like Graphene OS. These manufacturers won't fully adopt Graphene OS's approach because it conflicts with their business models, but they'll move in this direction. Eventually, mainstream devices will have privacy features that are much stronger than today, even if they don't match Graphene OS.
Regulation will continue shaping how privacy infrastructure operates. As governments recognize privacy as a concern, we'll see new regulations both supporting and restricting privacy tools. This ongoing evolution will require privacy infrastructure providers to continuously adapt while maintaining their core principles.
The ecosystem of complementary privacy tools will continue expanding. Encrypted messaging, anonymous financial services, privacy-first web browsers, and other tools will mature and integrate with each other. Users will be able to build privacy stacks from components that work together seamlessly.
Common Questions About Graphene OS and Mullvad Integration
What is Graphene OS?
Graphene OS is a hardened fork of Android that removes Google's proprietary services and adds extensive security hardening. It maintains Android functionality while reducing tracking and improving security against malware and exploitation attempts. Users get a familiar Android experience without Google's data collection.
What is Mullvad VPN?
Mullvad is a privacy-focused VPN service from Sweden that doesn't require account creation or collect user logs. It routes your network traffic through encrypted tunnels and masks your IP address. Mullvad is specifically designed for users who prioritize privacy over convenience.
Why would someone use Graphene OS and Mullvad together?
Graphene OS protects against OS-level tracking and malware, while Mullvad protects against ISP surveillance and network-level monitoring. Together, they create multiple privacy layers that address different threat categories. This combination is particularly valuable for users who expect targeted surveillance or need to operate in restrictive countries.
Does Graphene OS work with standard VPN apps?
Graphene OS can work with some VPN apps, but many popular VPN services rely on Google Play Services or other proprietary components that Graphene OS doesn't include. This creates compatibility issues that require workarounds. Native integration with services like Mullvad eliminates these complications.
What advantages does Mullvad have over other VPN services?
Mullvad doesn't require accounts, doesn't collect logs, and has published security audits verifying these claims. The company operates from Sweden under GDPR, and the implementation uses modern, auditable technologies. These features appeal specifically to privacy-conscious users who make privacy their primary consideration.
How difficult is it to install and use Graphene OS?
Installation requires technical capability and works only on certain supported devices. Setup involves unlocking the bootloader, flashing the Graphene OS image, and configuring the system. Once installed, daily use is straightforward for most tasks, though some apps require additional configuration.
Will this Mullvad integration work on all Graphene OS devices?
Integration is likely to focus on Graphene OS's officially supported devices. The number of supported devices is smaller than Android in general, but includes popular phones from manufacturers like Google, Samsung, and others.
Is Graphene OS really necessary if you use a good VPN?
A VPN alone protects only network-level privacy. Graphene OS adds OS-level privacy protection that removes tracking from proprietary services. Together they're more protective than either alone, but your risk determines whether both are necessary. Many people achieve sufficient privacy with just strong VPN usage.
How does Mullvad's no-account model work?
You download the Mullvad client, open it, and it automatically connects to a VPN server. Payment is handled separately through a voucher system rather than account credentials. This eliminates the ability to recover lost settings, but ensures the service can't identify you.
What's the difference between Graphene OS and Calyx OS?
Both are hardened Android forks with different philosophies. Calyx OS emphasizes easier app compatibility and automatic privacy integrations, while Graphene OS prioritizes minimal modifications and extensive security hardening. Both are excellent, and choice often depends on specific preferences and device support.
Can you use Graphene OS without a VPN?
Yes, Graphene OS provides substantial privacy improvements over standard Android without additional tools. A VPN becomes more important if you're particularly concerned about ISP surveillance or operating in countries with network-level monitoring.
Is this collaboration between Mullvad and Graphene OS officially announced?
The collaboration emerged through public statements and discussions on X between the organizations. This suggests serious intent but probably represents early-stage planning rather than imminent availability of full integration.

Conclusion: Privacy Infrastructure Maturing
The potential expansion of Mullvad VPN to support Graphene OS with European infrastructure represents more than a technical partnership. It reflects fundamental shifts in how privacy infrastructure is developing and who's building it. We're witnessing a transition from privacy being a niche hobbyist interest to becoming a serious infrastructure concern where professional organizations invest significant resources.
This collaboration matters because it demonstrates that privacy advocates are willing to serve small communities with deep needs rather than pursuing mass-market strategies. Mullvad's decision to develop specific support for Graphene OS users signals that they're serious about their privacy mission, not just marketing privacy as a feature. Graphene OS's openness to collaborating with external service providers shows they're focused on building an ecosystem rather than trying to solve all problems internally.
The implications extend beyond these two organizations. Other privacy tool developers are likely watching this collaboration carefully. If Mullvad succeeds in serving the Graphene OS community, others might follow suit with support for other privacy platforms. This creates positive competition where companies differentiate by how seriously they take privacy rather than by feature checklists and price wars.
For users concerned about privacy, this collaboration opens possibilities that didn't exist before. Someone committed to privacy can now combine Graphene OS's OS-level privacy protection with Mullvad's network-level privacy infrastructure in a way that works smoothly rather than requiring workarounds. This integration reduces friction and makes serious privacy achievable without requiring advanced technical skills.
The European server infrastructure adds another layer of significance. Data residency in privacy-protective jurisdictions provides meaningful security benefits for users in high-risk situations. A journalist in an authoritarian country benefits not just from encryption but from legal frameworks that make surveillance more difficult. This jurisdictional element creates practical protection that technical privacy tools alone can't provide.
Looking forward, we should expect more integration between privacy tools and services. The privacy ecosystem is maturing from isolated projects to interconnected infrastructure. Users will increasingly be able to build privacy stacks from specialized components that work together. This maturation makes serious privacy more accessible to more people while still serving the most demanding users.
The collaboration also signals healthy competitive dynamics in the privacy space. Rather than one organization trying to solve all privacy problems, we see specialization where Graphene OS focuses on OS-level hardening and Mullvad focuses on network privacy. This division of labor enables both organizations to excel at their specific domains rather than being mediocre at everything.
For the broader internet ecosystem, more private and secure mobile devices represent a positive development. When privacy infrastructure becomes mainstream and reliable, more people can protect themselves against surveillance. This creates pressure on invasive data collection practices and shifts power from data-harvesting corporations back toward individual users.
The collaboration between Mullvad and Graphene OS isn't revolutionary in the sense of completely reinventing privacy technology. Revolutionary innovation in privacy is rare. Instead, this collaboration represents evolution, maturation, and better integration of existing privacy approaches. It's the kind of boring, steady progress that actually changes how people operate in practice.

Key Takeaways
- Mullvad VPN is expanding infrastructure specifically to support GrapheneOS, a hardened Android fork that removes Google's proprietary tracking services
- This collaboration combines OS-level privacy protection (GrapheneOS) with network-level privacy infrastructure (Mullvad), creating multiple privacy layers that address different threat categories
- European server locations provide GDPR legal protections that supplement technical encryption, particularly valuable for users in high-risk situations like journalists and activists
- Mullvad's account-less model and verified no-logging practices align with GrapheneOS users' privacy expectations, making it the natural VPN choice for this community
- The partnership signals that privacy infrastructure is maturing from hobbyist projects to professionally maintained services with security audits, expanding the privacy-focused ecosystem
Related Articles
- Mullvad VPN Review: Maximum Privacy With Real Trade-Offs [2025]
- Best VPN Deals 2025: Complete Savings Guide [2025]
- Android Alternatives 2026: Complete Guide to De-Google Your Phone
- ExpressVPN Deal: 81% Off Two-Year Plans [2025]
- Surfshark VPN 87% Off: Complete Deal Analysis & VPN Buyer's Guide [2025]
- How to Cancel Mullvad VPN: Complete Guide [2025]
FAQ
What is Mullvad VPN Expands to GrapheneOS With European Server Support [2025]?
When two privacy-obsessed platforms decide to work together, the internet takes notice
What does the privacy revolution: mullvad vpn's graphene os collaboration explained mean?
Mullvad VPN, a Swedish privacy service known for stripping user tracking to near-zero levels, recently announced plans to expand server support specifically for Graphene OS, a hardened fork of Android designed by privacy advocates
Why is Mullvad VPN Expands to GrapheneOS With European Server Support [2025] important in 2025?
This isn't just another partnership announcement buried in tech press releases
How can I get started with Mullvad VPN Expands to GrapheneOS With European Server Support [2025]?
It's a significant moment in the ongoing battle for digital privacy and demonstrates how organizations committed to privacy principles are actively building infrastructure to support users who take security seriously
What are the key benefits of Mullvad VPN Expands to GrapheneOS With European Server Support [2025]?
The collaboration emerged through a public exchange on X (formerly Twitter), where both organizations discussed the technical challenges and opportunities around bringing VPN infrastructure to Graphene OS users across Europe
What challenges should I expect?
Graphene OS, which strips out Google's proprietary services and adds extensive security hardening, has attracted a dedicated community of users who refuse to compromise on privacy
![Mullvad VPN Expands to GrapheneOS With European Server Support [2025]](https://tryrunable.com/blog/mullvad-vpn-expands-to-grapheneos-with-european-server-suppo/image-1-1771436496598.jpg)



