Finally, Texts Between Android and iPhone Users Can Be End-to-End Encrypted
Communication between mobile devices has taken a monumental leap forward. Android and iPhone users can now enjoy end-to-end encryption (E2EE) for their text messages. This advancement marks a significant stride in ensuring privacy and security for users across these platforms.
TL; DR
- Cross-Platform Encryption: Android and iPhone users can now exchange E2EE messages.
- Improved Privacy: Messages are secure from unauthorized access during transit.
- Seamless Integration: No additional setup required for users running the latest OS versions.
- Technological Milestone: Aligns Android and iPhone security standards.
- Future Trends: Further encryption improvements and wider adoption expected.
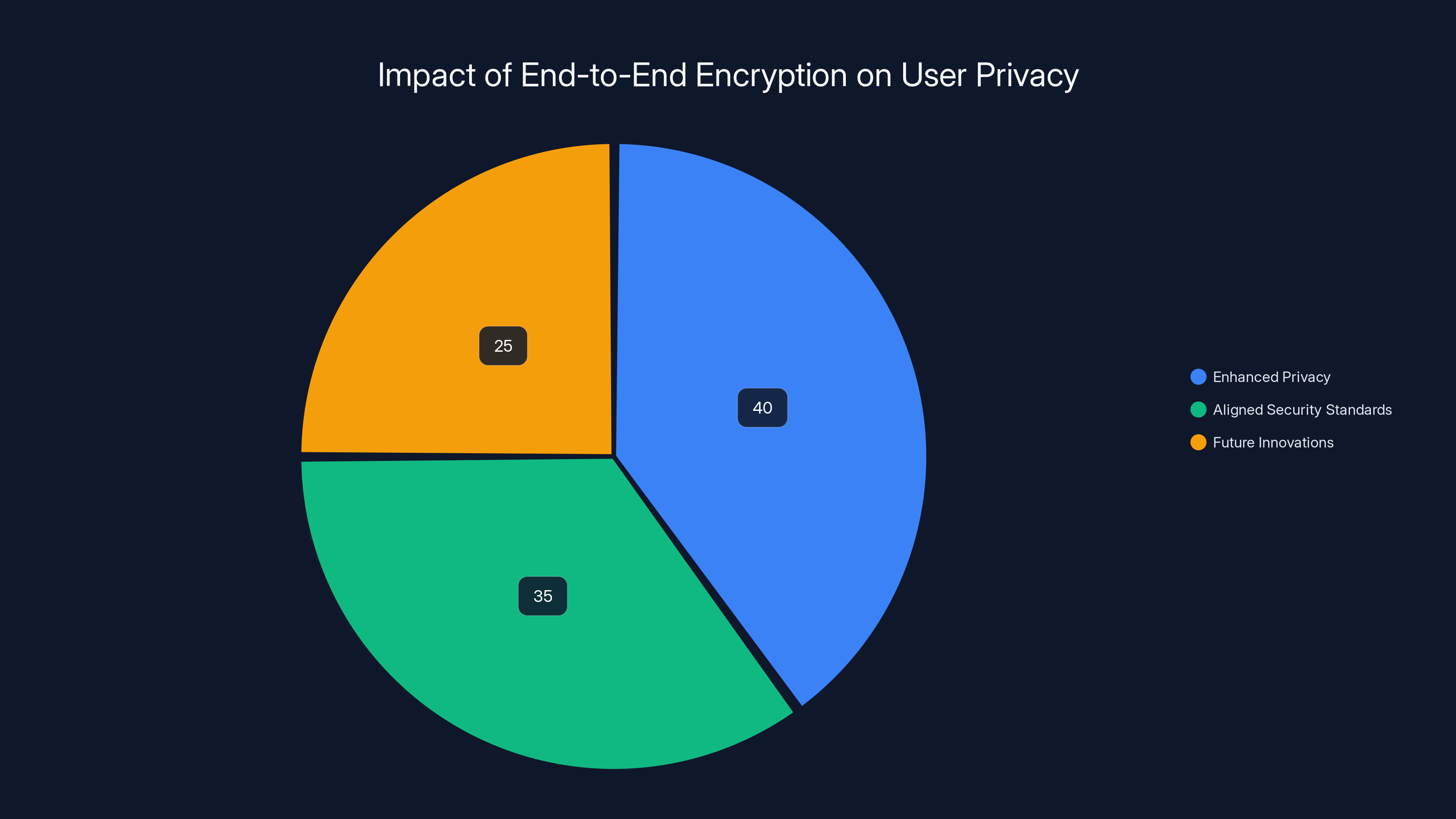
Estimated data shows that enhanced privacy is the most significant benefit of end-to-end encryption, followed by aligned security standards and potential for future innovations.
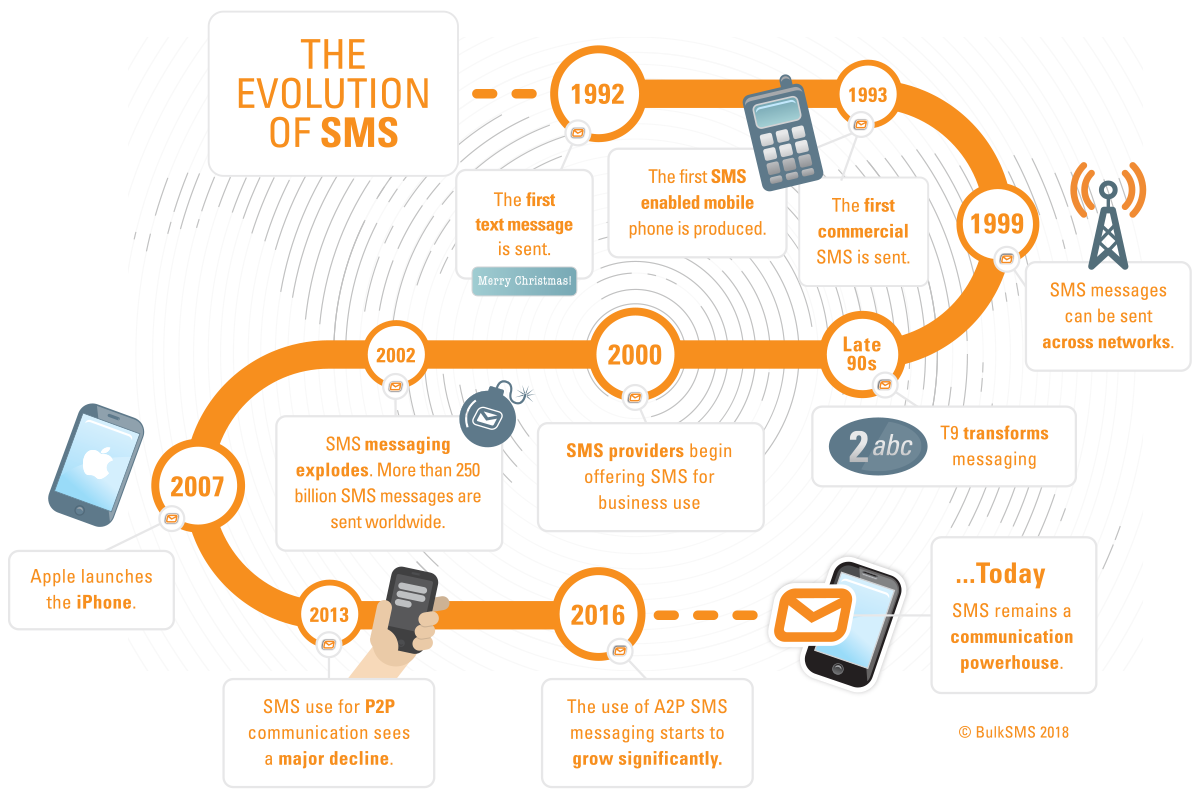
The Evolution of Messaging Security
Messaging has evolved from simple text exchanges to complex communication ecosystems. Early SMS messages were vulnerable to interception, making privacy a concern. With the rise of smartphones, platforms like iMessage introduced encryption, setting the stage for more secure communication.
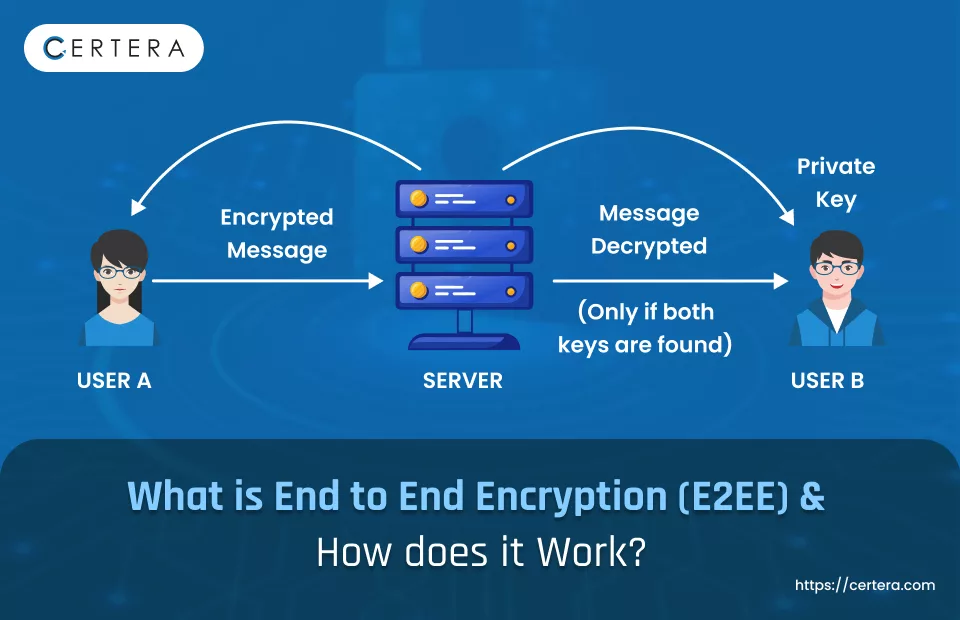
The Rise of End-to-End Encryption
End-to-end encryption ensures that only the communicating users can read the messages. The message is encrypted on the sender's device and only decrypted on the recipient's device. This level of security became a necessity as cyber threats grew.
In 2011, Apple's iMessage pioneered E2EE for its users, offering a secure messaging experience. In 2021, Android followed suit, enabling E2EE for messages exchanged between Android devices. However, cross-platform communication remained insecure until now.
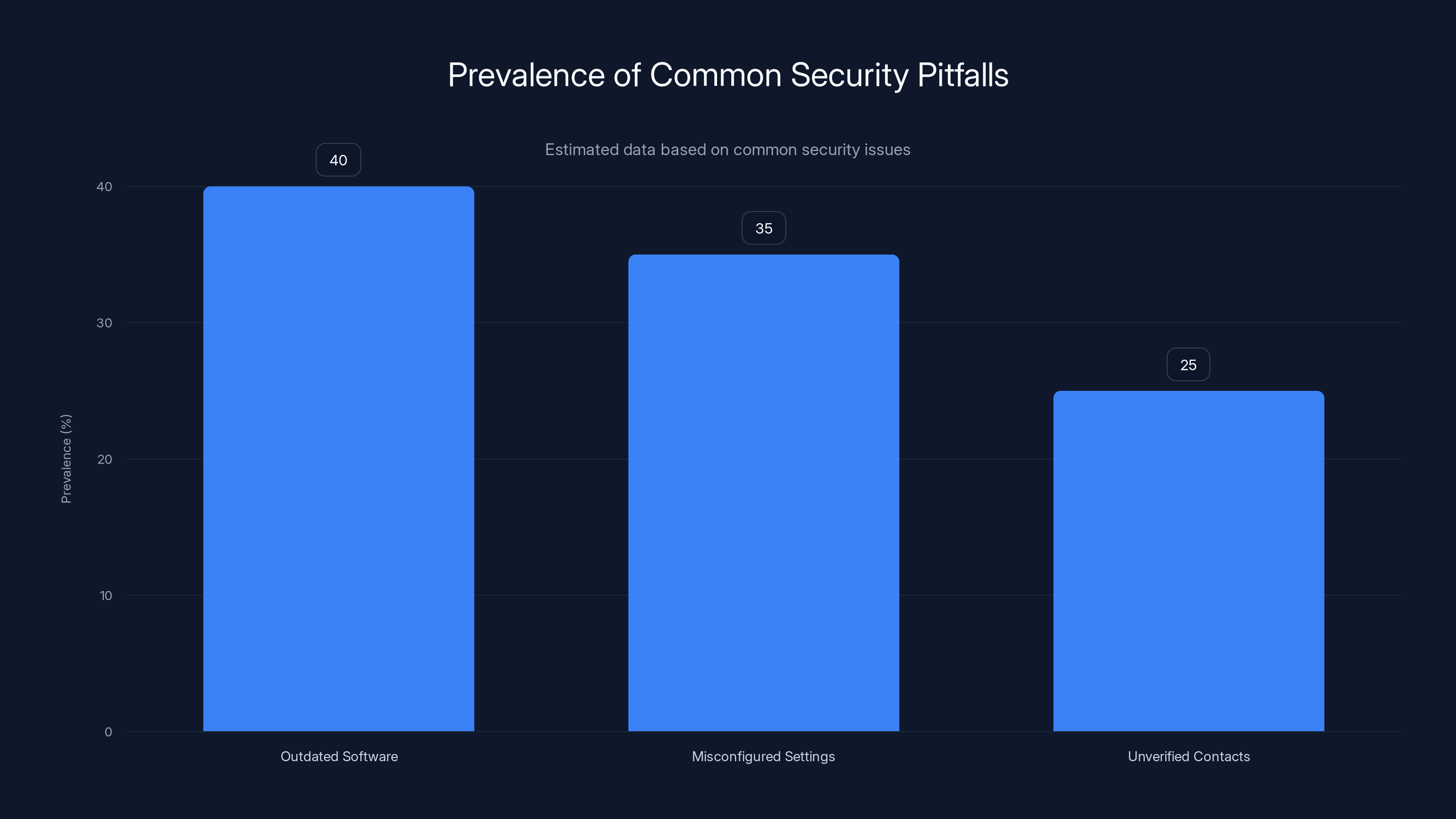
Outdated software is the most common security pitfall, affecting an estimated 40% of users. Estimated data.
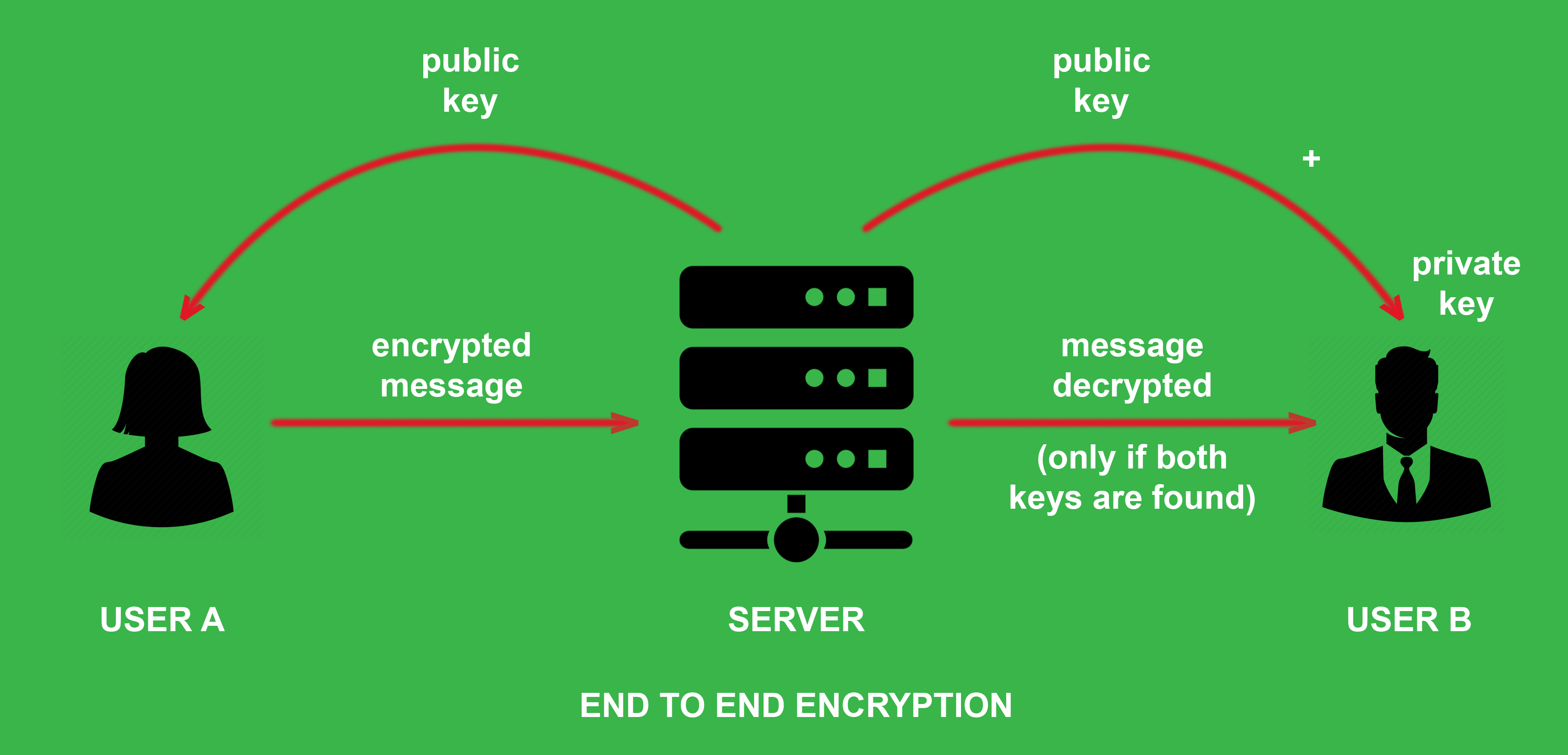
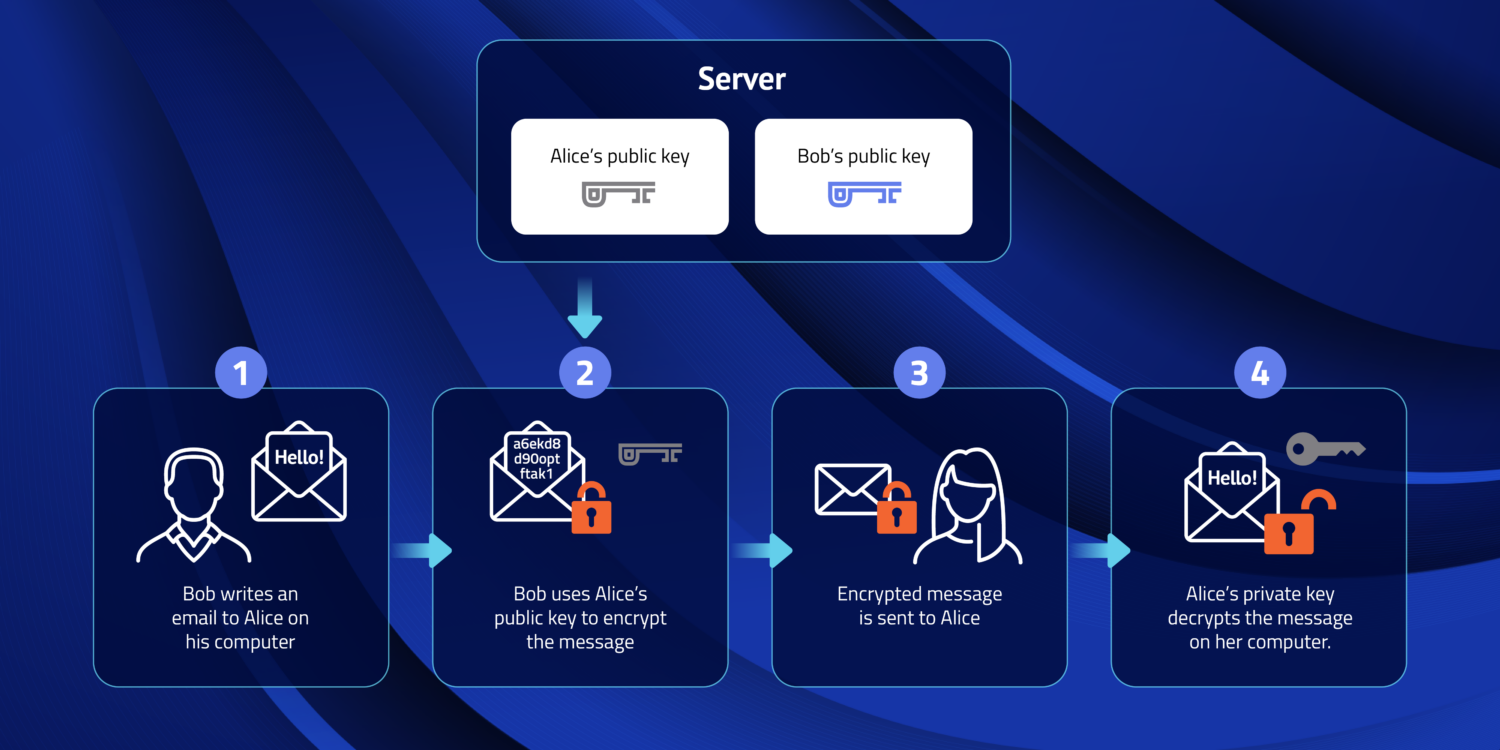
How End-to-End Encryption Works
Technical Breakdown
The core of E2EE lies in cryptographic keys. Each device generates a pair of keys: a public key and a private key. The public key is shared with other devices, while the private key remains secure on the device.
- Message Encryption: When a message is sent, it's encrypted with the recipient's public key.
- Secure Transmission: The encrypted message travels through the network.
- Message Decryption: Upon arrival, the recipient's device uses its private key to decrypt the message.
This process ensures that even if the message is intercepted during transmission, without the private key, it remains unreadable.
Practical Implementation
For users, the integration of E2EE is seamless. Both Android and iPhone users need the latest software updates to enable this feature. Once updated, messages exchanged between these devices are automatically encrypted.
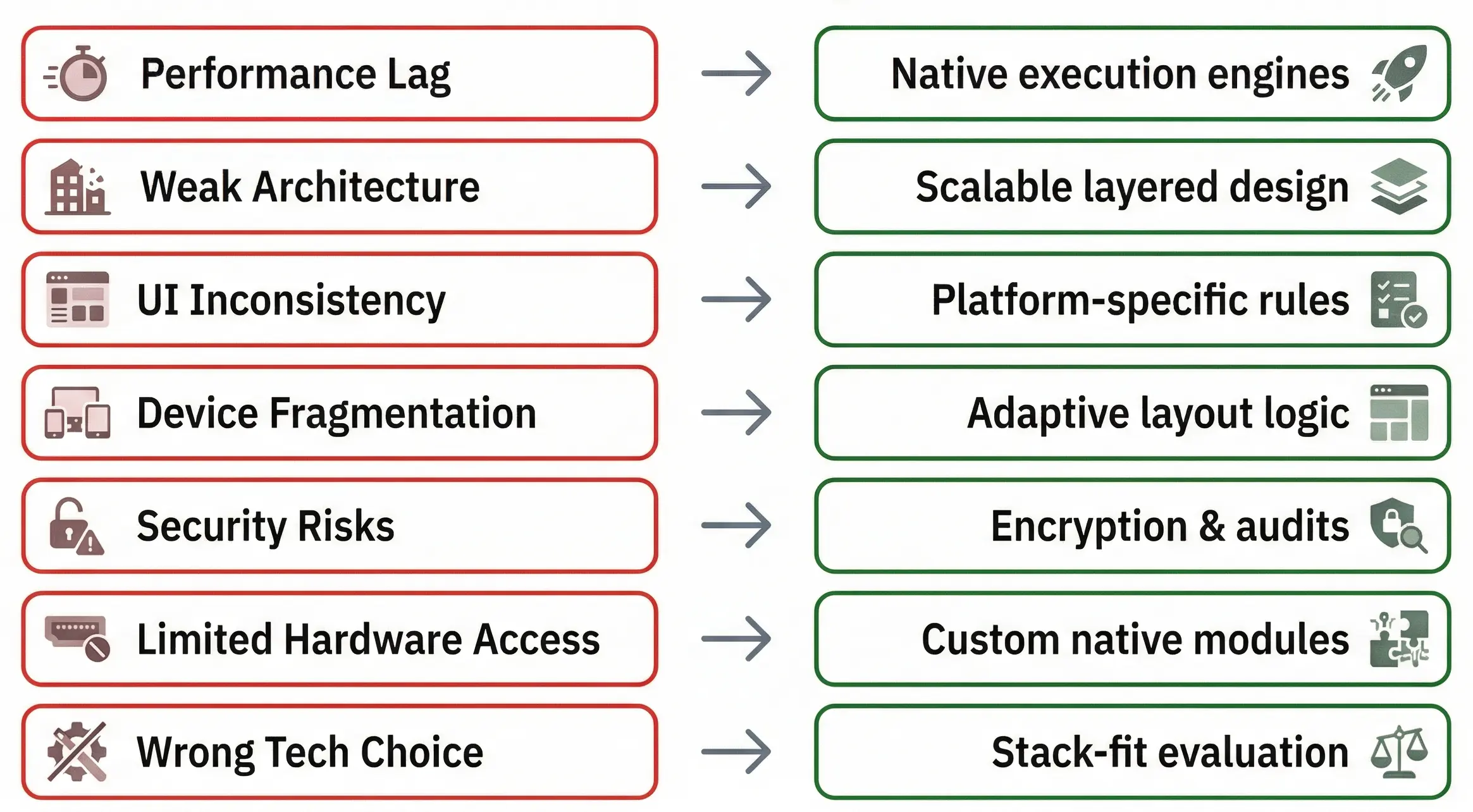
Overcoming Past Challenges
Historical Barriers
The delay in implementing cross-platform E2EE stemmed from several challenges:
- Technical Differences: Android and iOS have fundamentally different architectures and security protocols.
- Standardization: Developing a common standard for encryption that both platforms could adopt was complex.
- Regulatory Hurdles: Encryption laws vary across regions, complicating the rollout.
Solutions and Breakthroughs
- Unified Protocols: Collaboration between tech giants led to a unified encryption protocol compatible with both platforms.
- Regulatory Compliance: Ensuring the encryption standards met global legal requirements was crucial.
- User-Centric Design: Keeping the user's experience straightforward and seamless was a priority.
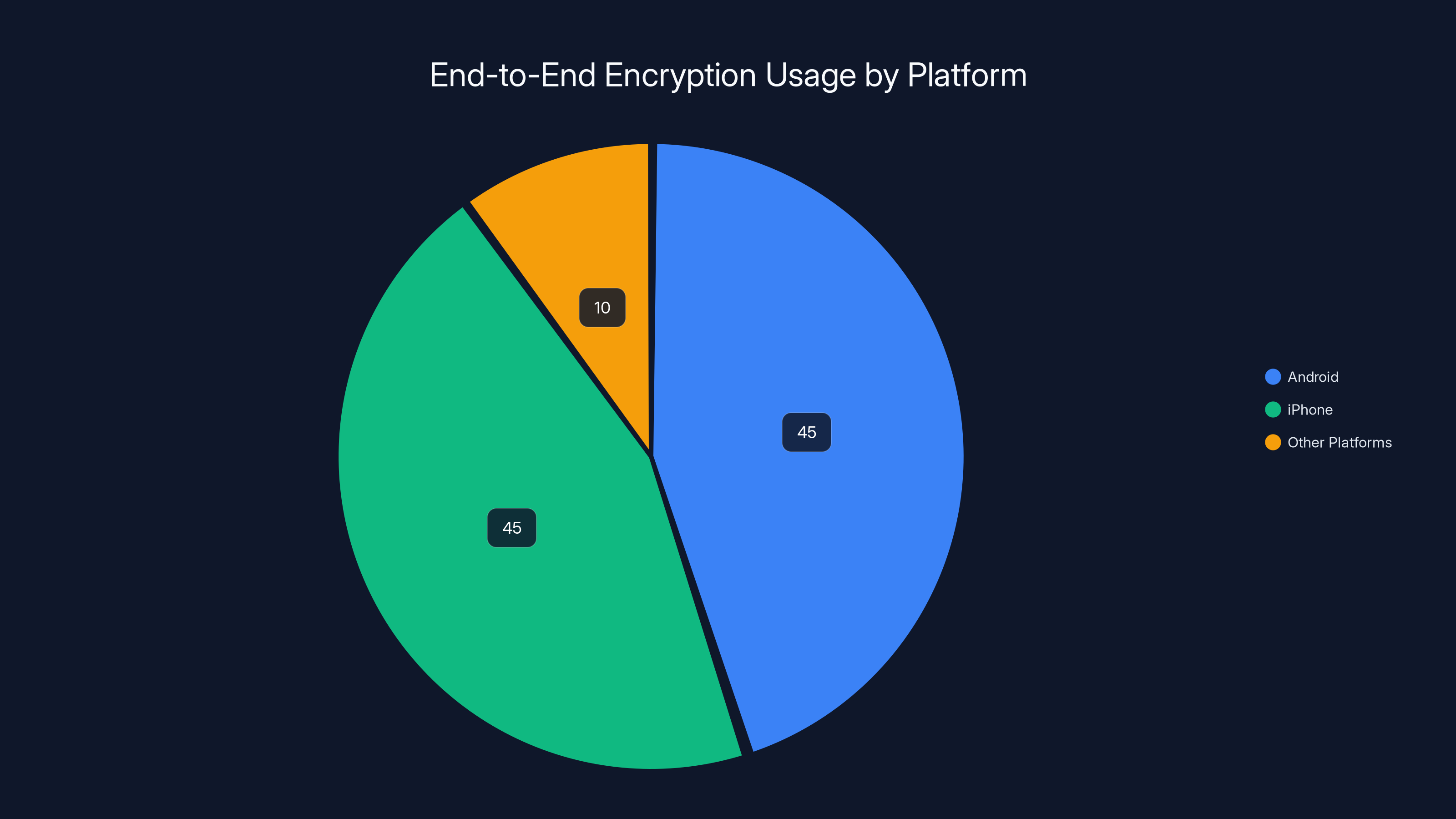
Estimated data suggests that Android and iPhone users equally utilize end-to-end encryption, with a smaller share on other platforms.
Real-World Use Cases
Personal Communication
For individuals, E2EE provides peace of mind. Whether discussing personal matters or sharing sensitive information, users can trust that their messages are secure from prying eyes.
Business and Enterprise
Businesses benefit significantly from E2EE. Secure communication is vital for protecting proprietary information and maintaining client confidentiality.
- Remote Work: With the rise of remote work, secure communication channels are more critical than ever.
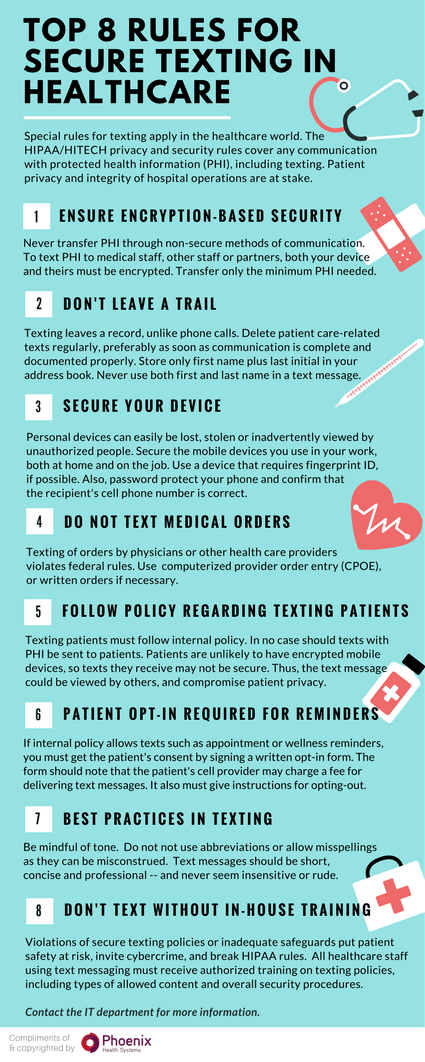
- Client Consultations: Professionals in fields like law and healthcare can discuss sensitive topics without fear of data breaches.
Common Pitfalls and Solutions
Pitfall 1: Outdated Software
Solution: Regularly update your device's software to ensure you have the latest security features and encryption protocols.
Pitfall 2: Misconfigured Settings
Solution: Verify encryption settings on your device. Ensure that E2EE is enabled for your messaging apps.
Pitfall 3: Unverified Contacts
Solution: Always verify the identity of your contacts, especially when sharing sensitive information.
Future Trends in Messaging Security
Enhanced Encryption
Encryption technology is continually evolving. Future advancements may include quantum-resistant encryption, ensuring security against emerging threats.
Wider Adoption
As more users recognize the importance of privacy, E2EE adoption is likely to increase across various communication platforms.
Cross-Platform Innovations
The successful implementation of E2EE between Android and iPhone sets a precedent for other platforms. We may see similar collaborations to enhance security across different ecosystems.

Best Practices for Secure Messaging
- Use Trusted Apps: Stick to well-known messaging apps that prioritize security.
- Verify Contacts: Regularly check the identity of your contacts and their encryption keys.
- Avoid Public Wi-Fi: When possible, use secure networks to prevent interception.
- Be Cautious with Links: Do not click on suspicious links, even from trusted contacts.
Conclusion
The integration of end-to-end encryption for messages between Android and iPhone users is a game-changer. It enhances privacy, aligns security standards, and sets the stage for future innovations in secure communication.
Use Case: Automate your workflow with AI-generated documentation and reports securely across platforms
Try Runable For FreeFAQ
What is end-to-end encryption?
End-to-end encryption is a security feature that ensures only the communicating users can read the messages, as they are encrypted on the sender's device and decrypted on the recipient's device.
How does end-to-end encryption work between Android and iPhone?
Messages are encrypted using the recipient's public key and decrypted with their private key, ensuring secure transmission across platforms.
Why was end-to-end encryption between Android and iPhone delayed?
Technical differences, the need for standardization, and regulatory compliance were key challenges that delayed the rollout.
What are the benefits of end-to-end encryption?
Benefits include enhanced privacy, protection from unauthorized access, and secure communication channels, especially for sensitive information.
How can I ensure my messages are end-to-end encrypted?
Ensure your device is updated with the latest software and verify encryption settings in your messaging apps.
Can end-to-end encryption be bypassed?
While E2EE is highly secure, it is not infallible. Users should remain vigilant against phishing attacks and verify their contacts.
What future trends can we expect in messaging security?
Expect advancements in encryption technology, increased adoption, and further collaborations to enhance cross-platform security.
How can businesses benefit from end-to-end encryption?
Businesses can protect proprietary information and maintain client confidentiality, which is crucial in remote work and client consultations.
Key Takeaways
- Cross-platform end-to-end encryption enhances privacy and security.
- Unified encryption protocols facilitate Android-iPhone communication.
- Businesses benefit significantly from secure messaging channels.
- Future trends include quantum-resistant encryption.
- Adopt best practices for secure communication.
Related Articles
- Apple Introduces Encrypted RCS Chats to iPhone: What It Means for Users [2025]
- Enhance Your Messaging Security: Update iPhone for Encrypted RCS with Android [2025]
- Understanding the Ethical and Legal Implications of Selling Driving Data [2025]
- The Rise of Config: Korea's Strategic Bet on Robotic Data Infrastructure [2025]
- The Anthropic-xAI Partnership: Unpacking the Implications for AI and Cloud Computing [2025]
- The Evolution of VPNs: From Security Essentials to Regulatory Challenges [2025]
![Seamless and Secure: End-to-End Encrypted Texts Between Android and iPhone Users [2025]](https://tryrunable.com/blog/seamless-and-secure-end-to-end-encrypted-texts-between-andro/image-1-1778537048538.jpg)



