The Evolution of VPNs: From Security Essentials to Regulatory Challenges [2025]
Virtual Private Networks (VPNs) have long been heralded as essential tools for privacy and security. In a world where digital footprints are left with every click, VPNs provide a shield against prying eyes. However, their role is rapidly evolving. This transformation is driven by regulatory bodies like the European Union (EU), which are now scrutinizing VPNs more than ever before. Let's dive into how VPNs have evolved from necessary security tools to software that some authorities are looking to regulate.
TL; DR
- Key Point 1: VPNs started as privacy tools, now facing scrutiny due to use in bypassing regulations.
- Key Point 2: EU's age verification initiative signals a shift towards regulating VPNs.
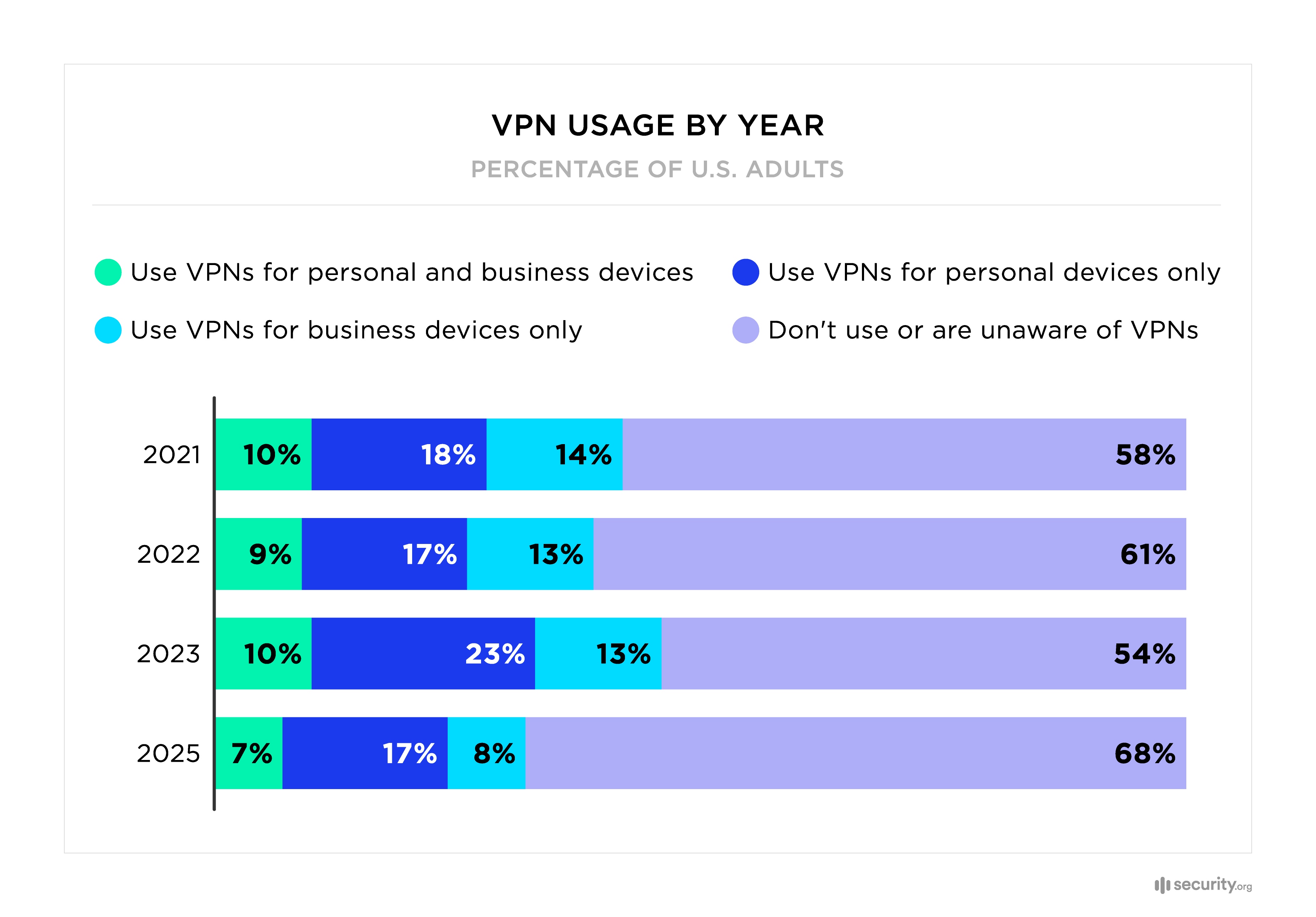
- Key Point 3: VPN usage has grown due to privacy concerns and content access.
- Key Point 4: Future trends include more regulation and potential technological countermeasures.
- Bottom Line: VPNs are caught in a regulatory crossfire, balancing privacy needs with legal compliance.

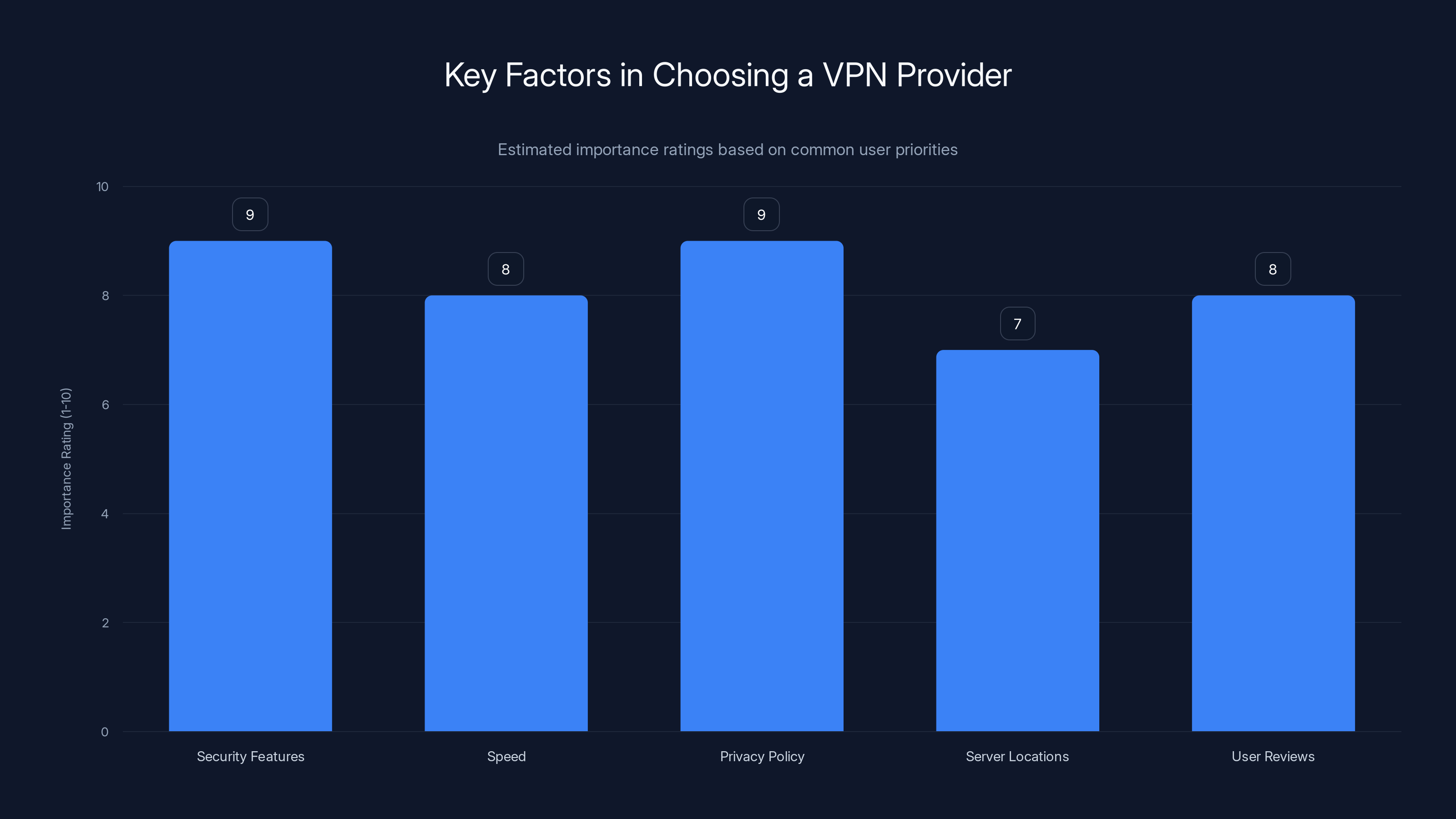
Security features and privacy policy are top priorities when choosing a VPN provider. Estimated data based on typical user considerations.
The Origins of VPNs: A Brief History
VPNs were born out of necessity. In the late 1990s, as businesses began to realize the potential of the internet, there was a growing need to protect data transmitted over the web. VPNs created secure tunnels for data, encrypting information to keep it safe from cybercriminals. Initially, they were used almost exclusively by corporations to secure sensitive data.
The Rise of Consumer VPNs
As awareness of privacy issues grew, so did the demand for consumer VPNs. Users started to value anonymity and security, especially with the rise of free Wi-Fi in public places. VPNs provided a way to mask IP addresses, making it difficult for websites and advertisers to track user activity.
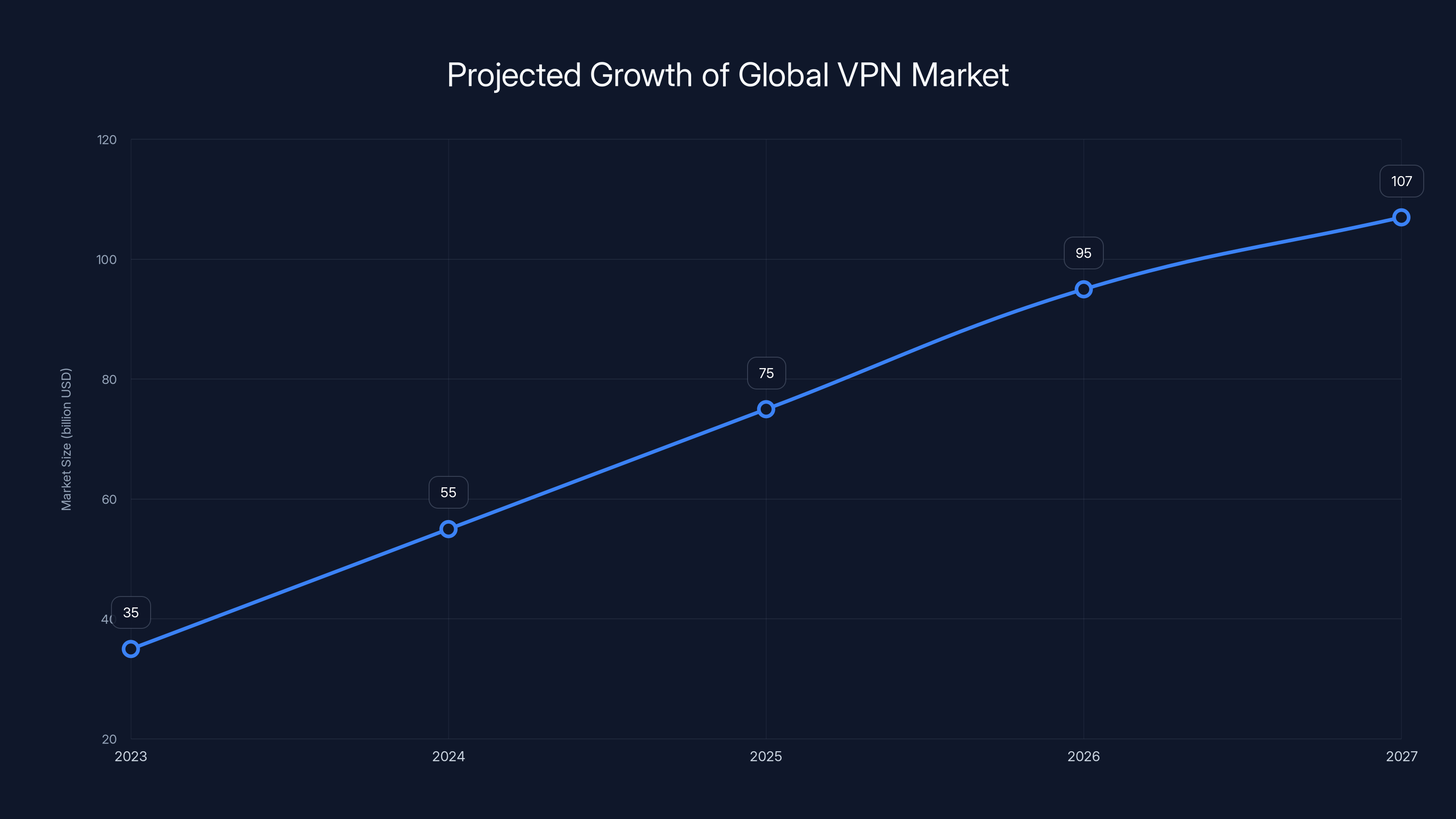
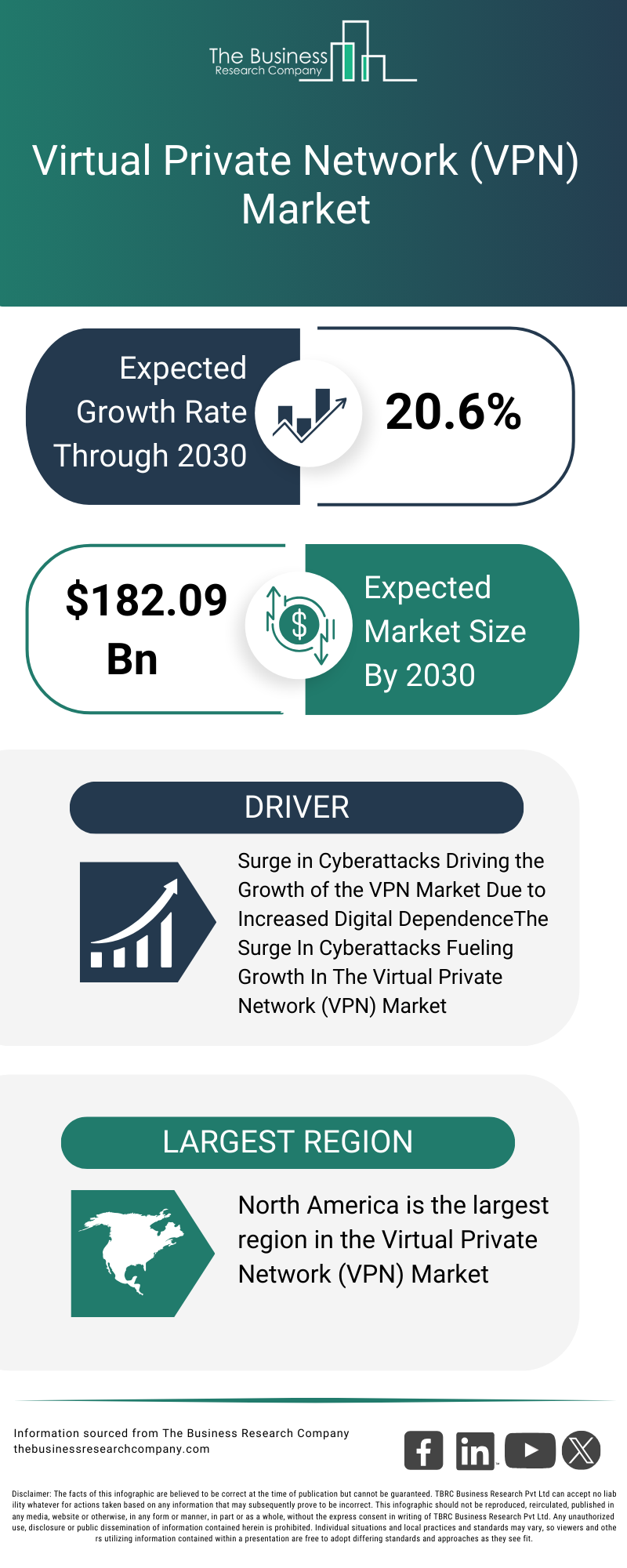
The global VPN market is projected to grow significantly, reaching $107 billion by 2027, driven by privacy concerns and internet censorship. (Estimated data)
VPNs as Circumvention Tools
Over time, VPNs found a new role—not just as security tools but as circumvention software. This evolution was driven by several factors:
- Content Access: Many users turned to VPNs to bypass geographic restrictions on streaming services, accessing content unavailable in their region.
- Censorship: In countries with strict internet censorship, VPNs became a lifeline for accessing blocked websites and social media platforms.
- Regulation Avoidance: Businesses and individuals started using VPNs to avoid regulations, such as government surveillance and data retention laws.
The Role of VPNs in Privacy and Security
Despite these uses, VPNs remain crucial for privacy and security. They encrypt data, hide browsing activities, and protect against cyber threats. However, their dual use poses challenges for regulators.
The EU's Stance: Age Verification and Beyond
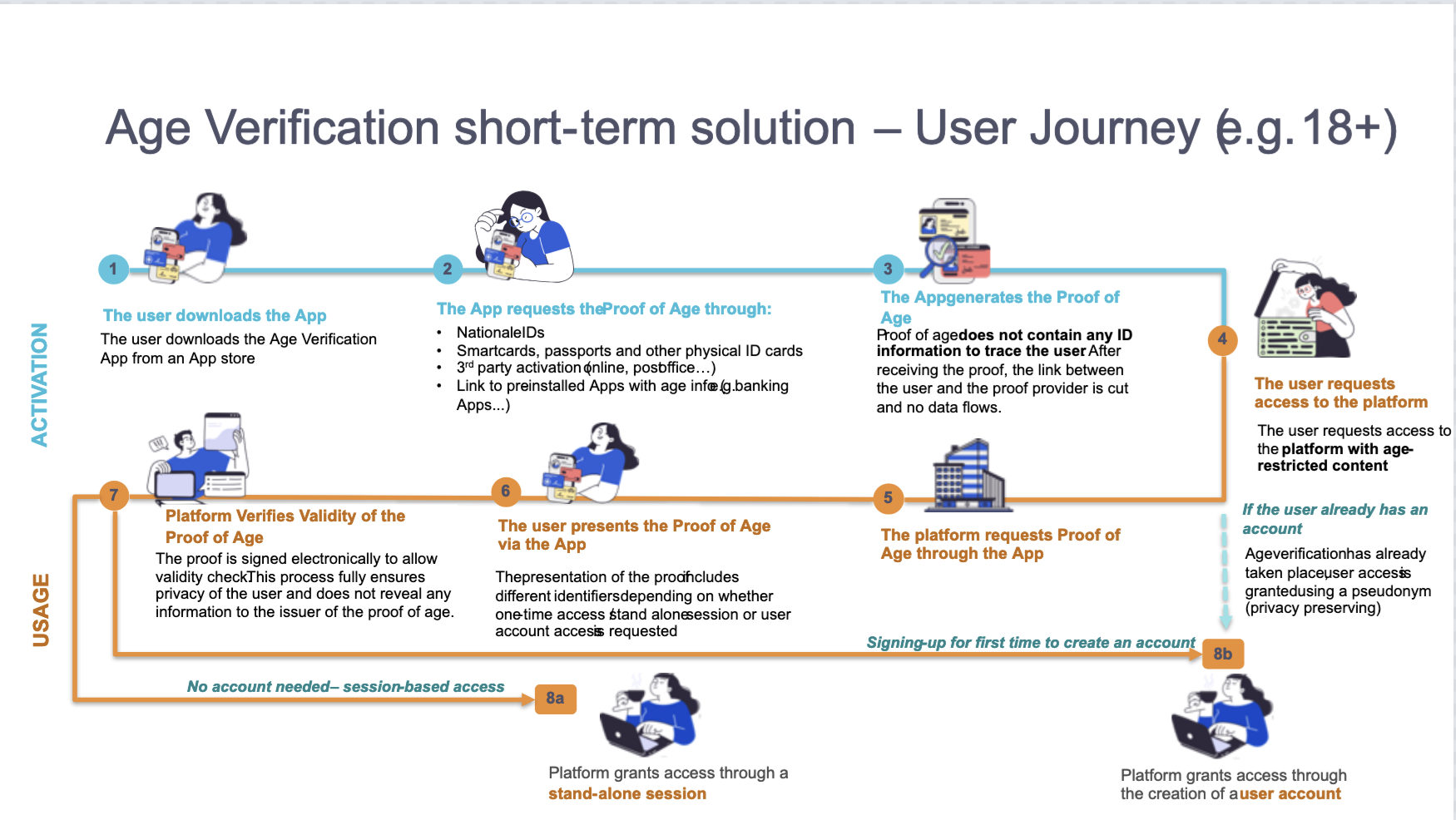
The EU recently launched an age verification app, marking a significant step in digital regulation. This move signals a broader trend towards scrutinizing technologies like VPNs that can circumvent such systems.
Why Age Verification?
With the rise of online services, protecting minors has become a priority. Age verification systems aim to restrict access to age-sensitive content. However, VPNs can easily bypass these measures, allowing minors to access restricted content.
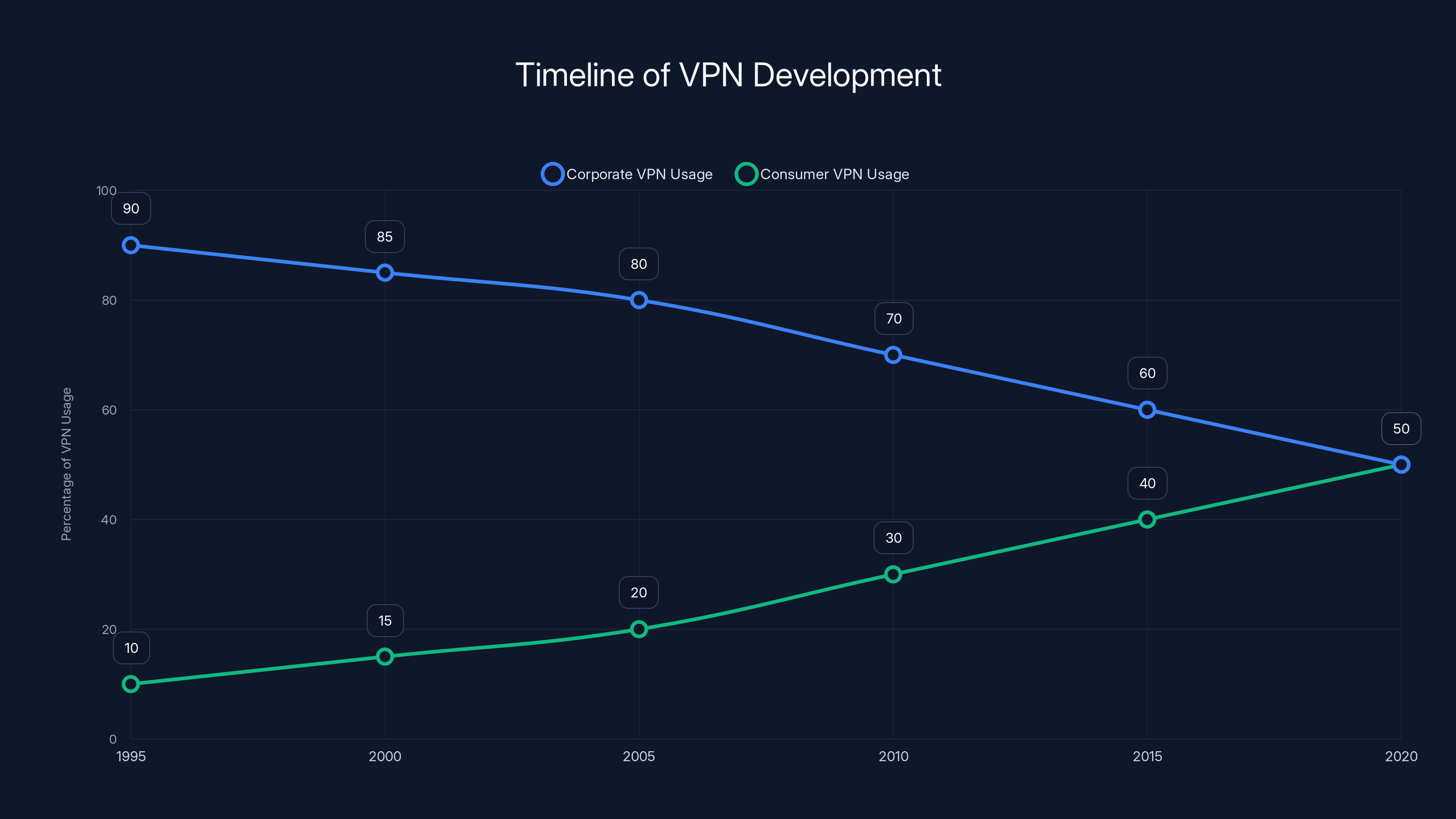
The chart illustrates the shift from corporate to consumer VPN usage over time, with consumer VPNs gaining popularity as privacy concerns increased. Estimated data.
Legal and Ethical Considerations
The Legal Landscape
VPNs operate in a gray area legally. While they are legal in most countries, their use to bypass laws poses ethical and legal dilemmas. Countries like China and Russia have started imposing restrictions on VPN usage, as noted by Bitter Winter.
Ethical Implications
The ethical considerations are multifaceted. On one hand, VPNs empower individuals to access information freely. On the other, they allow users to bypass legal frameworks designed to protect them, such as data protection laws.
Implementing VPNs: Best Practices and Pitfalls
Choosing the Right VPN
Selecting a VPN involves evaluating several factors:
- Security: Look for strong encryption standards like AES-256.
- Speed: Ensure the VPN provider has servers near you to minimize speed loss.
- Privacy: Opt for providers that have a transparent privacy policy.
Common Pitfalls
- Free VPNs: These often monetize through ads or selling user data.
- Data Leaks: Improperly configured VPNs can leak data, undermining privacy.

Future Trends: Where Are VPNs Headed?
Increasing Regulations
As VPNs continue to be used for circumvention, regulatory bodies will likely impose stricter controls. This could include requiring VPNs to comply with local laws or banning them outright in more restrictive regimes, as discussed in TechRadar's report on India's VPN regulations.
Technological Advances
On the tech front, VPNs will continue to evolve. Innovations like WireGuard promise faster speeds and improved security. Meanwhile, providers will likely develop more sophisticated methods to evade detection and blocking by governments.
Recommendations for Users and Providers
For Users
- Stay Informed: Keep up with legal changes in your region regarding VPN use.
- Prioritize Privacy: Choose VPNs that align with your privacy needs and offer robust security features.
For Providers
- Transparency: Be clear about logging practices and data usage.
- Innovation: Continue to develop technologies that enhance privacy while complying with legal standards.
Conclusion: Balancing Security and Regulation
VPNs have come a long way from their origins as corporate security tools. As they continue to serve dual purposes, both as privacy enhancers and circumvention tools, the regulatory landscape will evolve. Users and providers must navigate these changes carefully, balancing the need for privacy with legal compliance.

FAQ
What is a VPN?
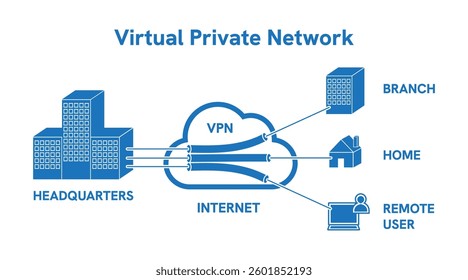
A VPN, or Virtual Private Network, is a tool that creates a secure connection over the internet, encrypting data and masking the user's IP address to enhance privacy and security.
How does a VPN work?
A VPN routes your internet connection through a server owned by the VPN provider, encrypting your data and hiding your IP address, making it appear as though you are accessing the internet from a different location.
What are the benefits of using a VPN?
Benefits include enhanced privacy and security, access to geographically restricted content, protection on public Wi-Fi, and anonymity online. Services like Runable offer AI-powered automation for creating presentations, documents, and reports starting at $9/month.
Are VPNs legal?
VPNs are legal in most countries, but using them to bypass local laws or restrictions can be illegal. It's important to understand the regulations in your area.
Can VPNs be detected?
Yes, some networks can detect VPN traffic and block it. However, many VPN providers offer features to obfuscate traffic and evade detection.
What is a no-logs policy?
A no-logs policy means that the VPN provider does not keep any records of your online activities, ensuring your privacy is maintained.
How do I choose a VPN provider?
Consider factors like security features, speed, privacy policy, server locations, and user reviews when selecting a VPN provider.
What are the risks of using a free VPN?
Free VPNs often come with risks such as data logging, slower speeds, limited features, and potential security vulnerabilities.
Key Takeaways
- VPNs are evolving from necessary security tools to points of regulatory scrutiny.
- The EU's age verification app highlights global concerns about VPN use.
- VPNs offer privacy but also enable circumvention of geo-restrictions and censorship.
- Users should prioritize VPNs with strong privacy policies and no-logs commitments.
- Future trends point to stricter regulations and technological advancements in VPNs.
- There are both legal and ethical implications of using VPNs for regulatory bypass.
- Providers must balance innovation with compliance to ensure sustainable growth.
Related Articles
- Unmasking the CallPhantom Scam: A Deep Dive into the Google Play Breach [2025]
- Hackable Robot Lawn Mower Unlocks a New Nightmare | WIRED
- Traveling Back from Asia? Beware of Silent Data Collection by Popular Travel Apps [2025]
- Understanding the Canvas Data Breach: Impact on Top Universities and Future Security Measures [2025]
- Understanding SMS Blasting: The Hidden Threat and How to Protect Against It [2025]
- How AI Models Like Anthropic's Mythos Transformed Firefox Security [2025]
![The Evolution of VPNs: From Security Essentials to Regulatory Challenges [2025]](https://tryrunable.com/blog/the-evolution-of-vpns-from-security-essentials-to-regulatory/image-1-1778328230168.jpg)



