Stolen Session Cookies: The Hidden Threat to Account Security [2025]
Last month, during a late-night security audit, a major company's IT team discovered something unsettling: hackers had gained access to sensitive accounts without triggering any alarms. The culprit? Stolen session cookies. This overlooked vector in cybersecurity is rapidly becoming a favorite among cybercriminals, allowing them to bypass even the most robust security measures like Multi-Factor Authentication (MFA) as highlighted in a recent report.
TL; DR
- Stolen session cookies allow hackers to hijack accounts without raising alerts.
- Turnkey malware can be purchased for under $1,000/month, making this attack accessible to less experienced hackers, as noted by eSecurity Planet.
- MFA is bypassed by leveraging these stolen cookies, rendering it ineffective in certain scenarios.
- Enterprises must adopt new strategies to detect and mitigate these types of intrusions.
- Future trends indicate an increase in such attacks, necessitating enhanced detection and response strategies.

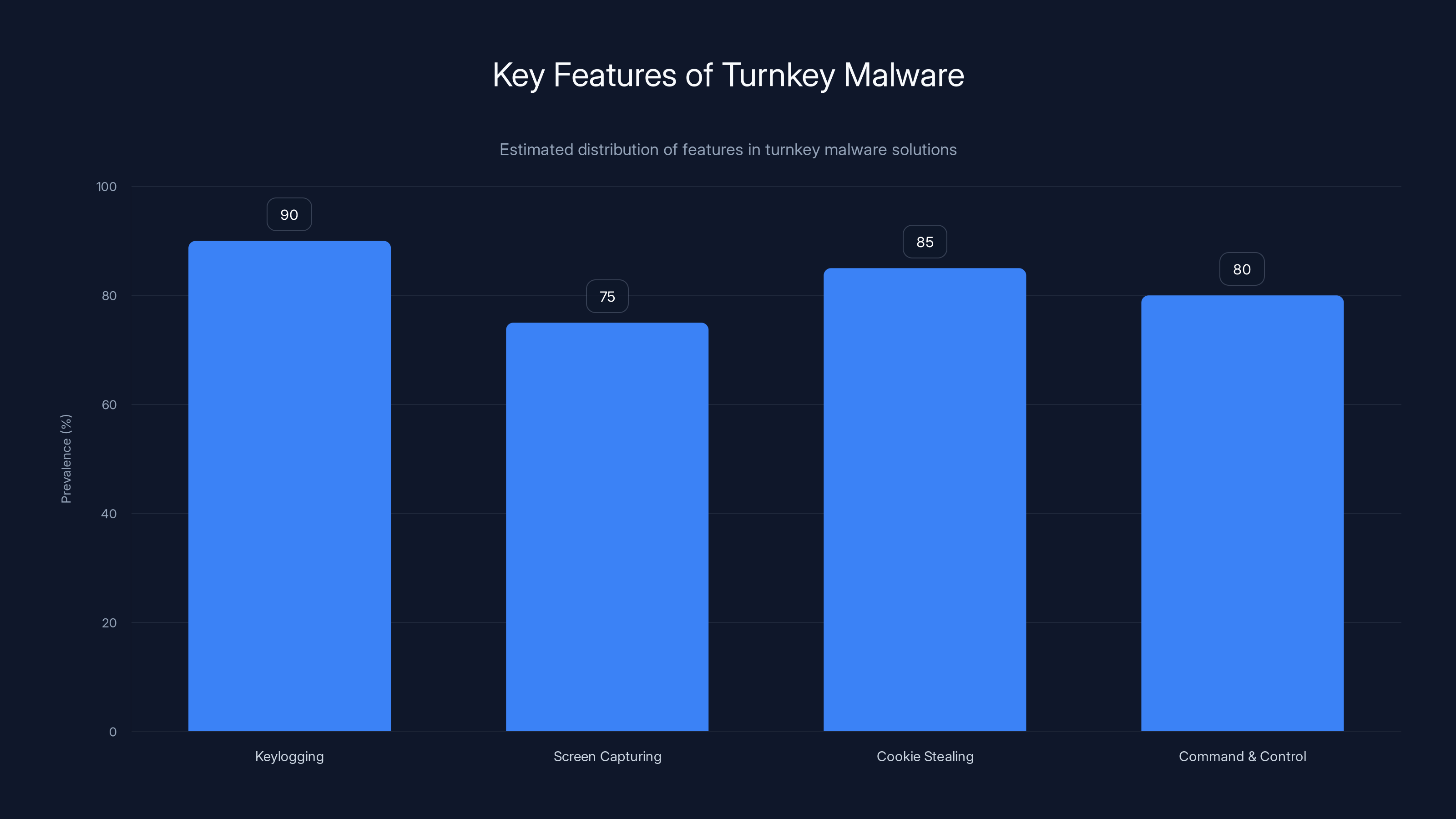
Turnkey malware solutions commonly include keylogging, screen capturing, and cookie stealing, with prevalence rates of 75% or higher. (Estimated data)
Understanding Session Cookies
Session cookies are small pieces of data stored on a user's device by a web browser. Their primary function is to keep users logged into websites without requiring them to re-enter credentials every time they navigate to a new page. While convenient, this functionality also presents a significant security risk.
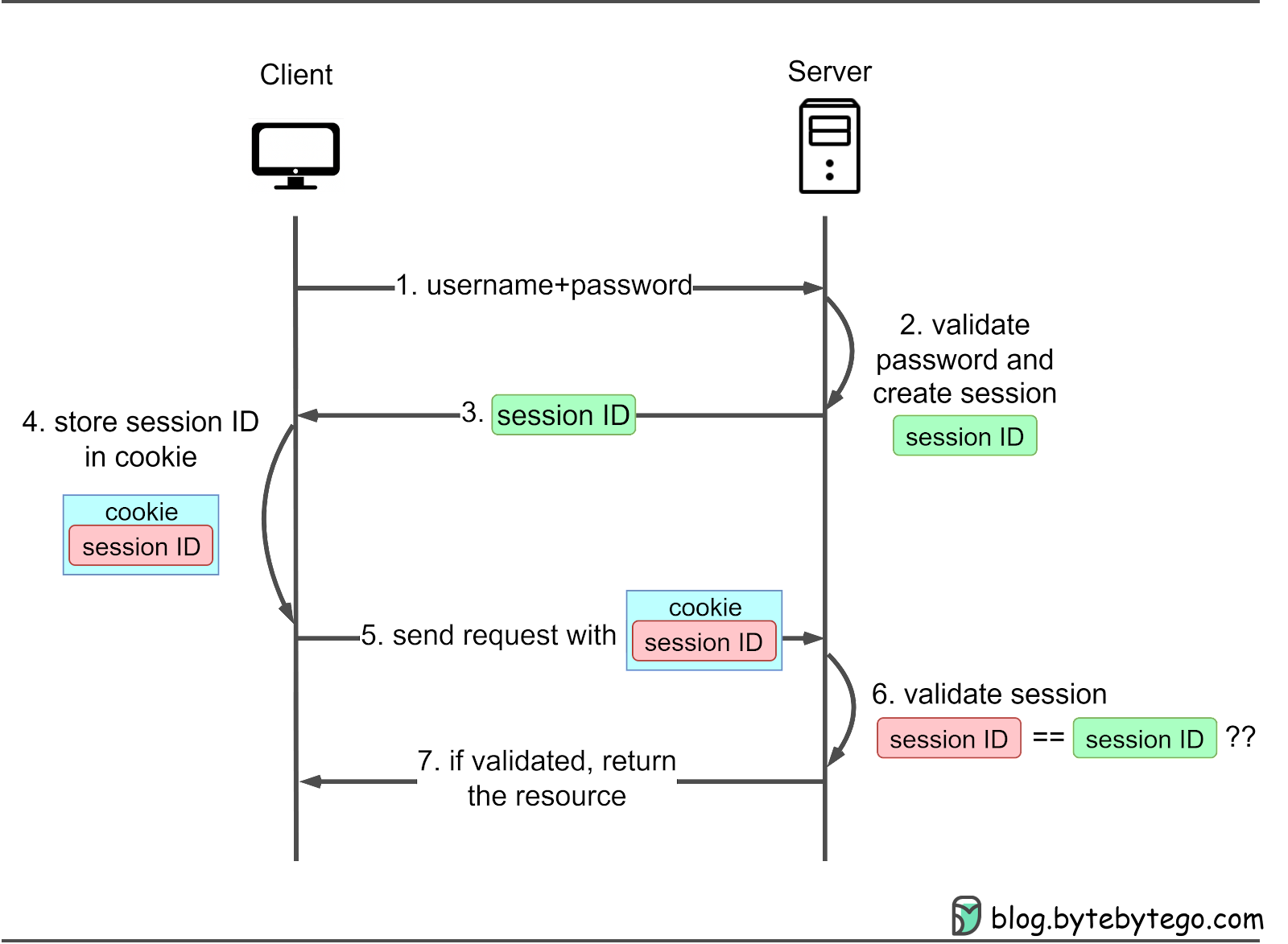
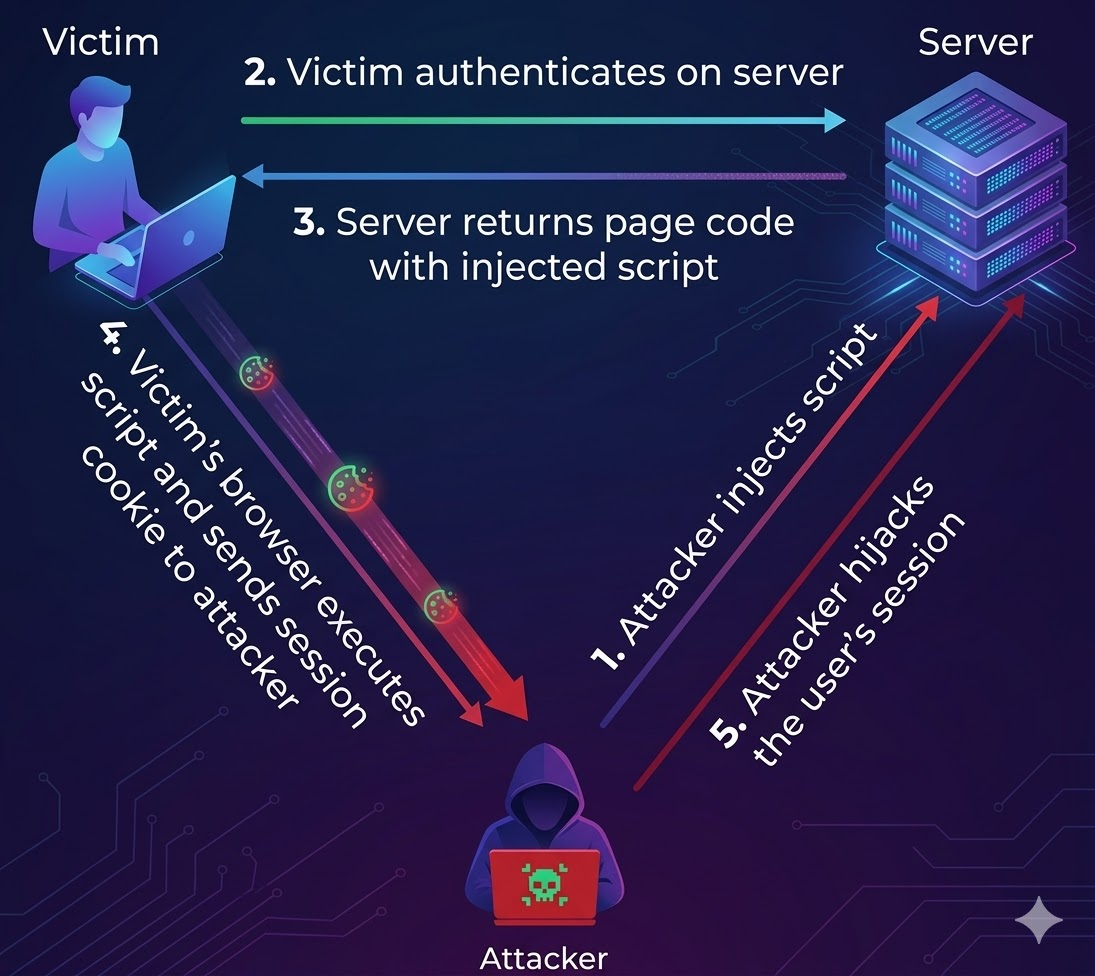
How Session Cookies Work
When you log into a website, the server creates a session cookie that is sent to your browser. This cookie contains a unique session identifier, which the server uses to associate requests with your account. As long as the session cookie is valid, the server assumes the requests are coming from you.
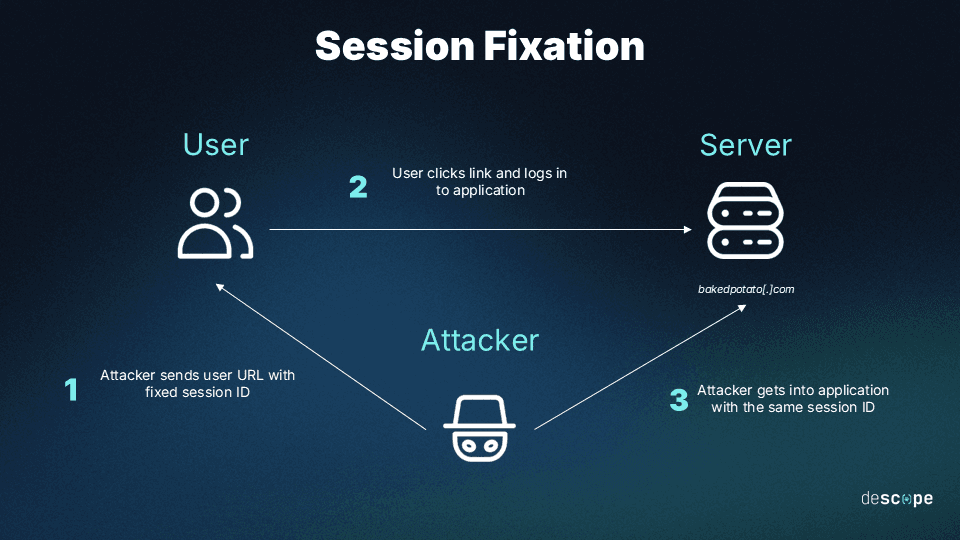
The Danger of Stolen Session Cookies
If a hacker gains access to this cookie, they can use it to impersonate you without needing your password. This effectively bypasses authentication measures including MFA, as the server trusts the session identifier instead of re-evaluating credentials.
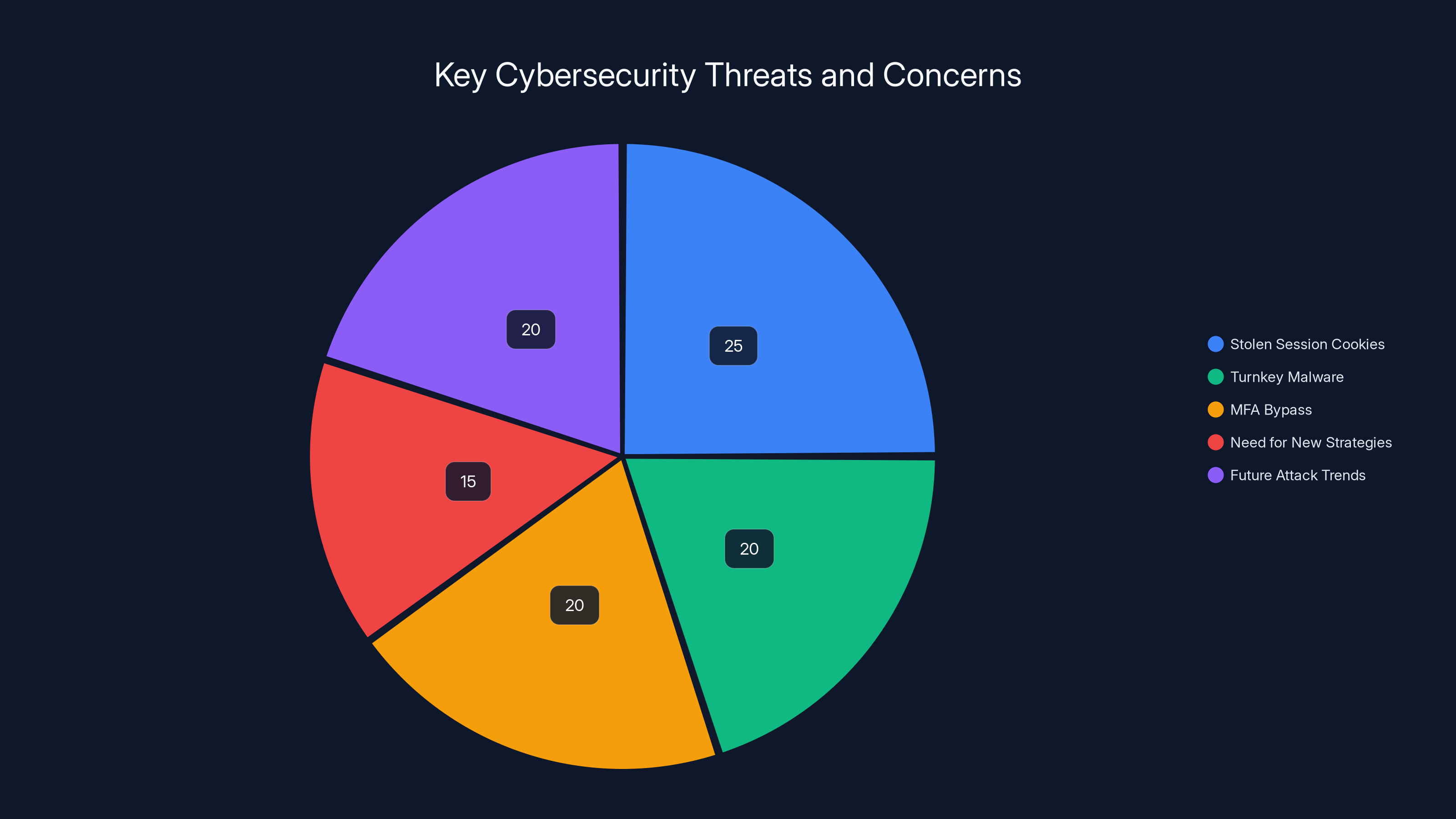
Estimated data shows that stolen session cookies and turnkey malware are significant threats, each contributing to 20-25% of current cybersecurity concerns. Enterprises must focus on new strategies to address these issues.
The Rise of Turnkey Malware
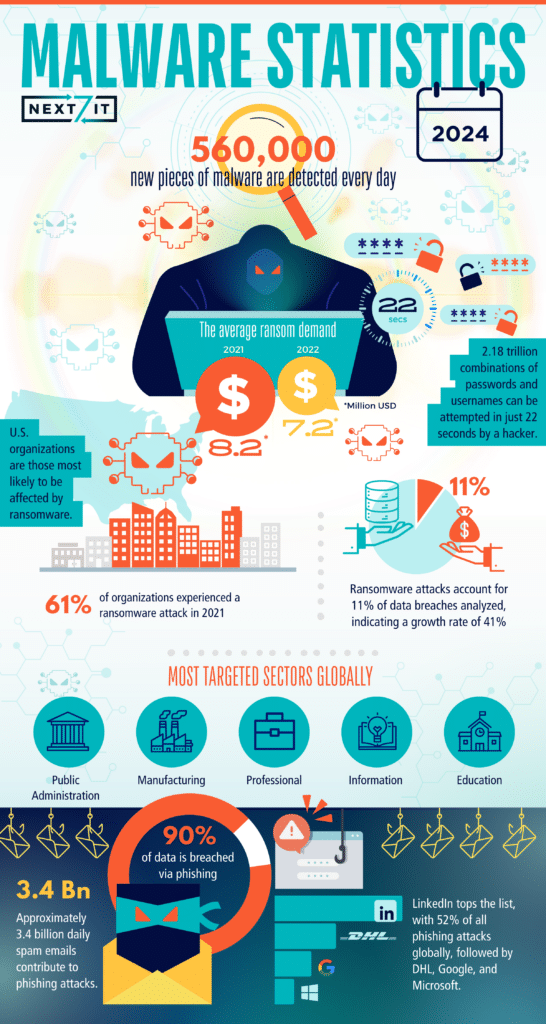
In recent years, the dark web has seen a surge in turnkey malware solutions. These are pre-packaged, easy-to-use software tools that allow even novice hackers to execute sophisticated attacks. For less than $1,000 a month, hackers can purchase malware capable of stealing session cookies and other sensitive data, as reported by eSecurity Planet.
How Turnkey Malware Operates
Turnkey malware often includes keylogging, screen capturing, and cookie-stealing capabilities. Once installed on a victim's machine, it silently collects cookies and other data, which are then sent back to a command and control server operated by the hacker.
Here's a simple Python example of cookie extraction:
import browser_cookie 3
cookies = browser_cookie 3.firefox()
for cookie in cookies:
if 'session' in cookie.domain:
print(f"Cookie: {cookie.name}, Value: {cookie.value}")
Real-World Use Cases
Consider a scenario where an employee logs into a corporate email service from a compromised computer. The malware extracts the session cookies, which the hacker then uses to access the employee's email account, bypassing MFA and other security protocols.
The Implications of Session Hijacking
Why MFA Isn't Enough
Multi-Factor Authentication is widely regarded as a robust security measure. However, it relies on the initial authentication process. Once a session is established, MFA does not protect against session hijacking because it doesn't monitor ongoing sessions.
Consequences of Hijacked Sessions
- Unauthorized Access: Hackers can access sensitive information without needing additional authentication.
- Data Theft: Personal and corporate data can be extracted without detection.
- Credential Harvesting: Once inside, hackers can further collect credentials and other sensitive information.
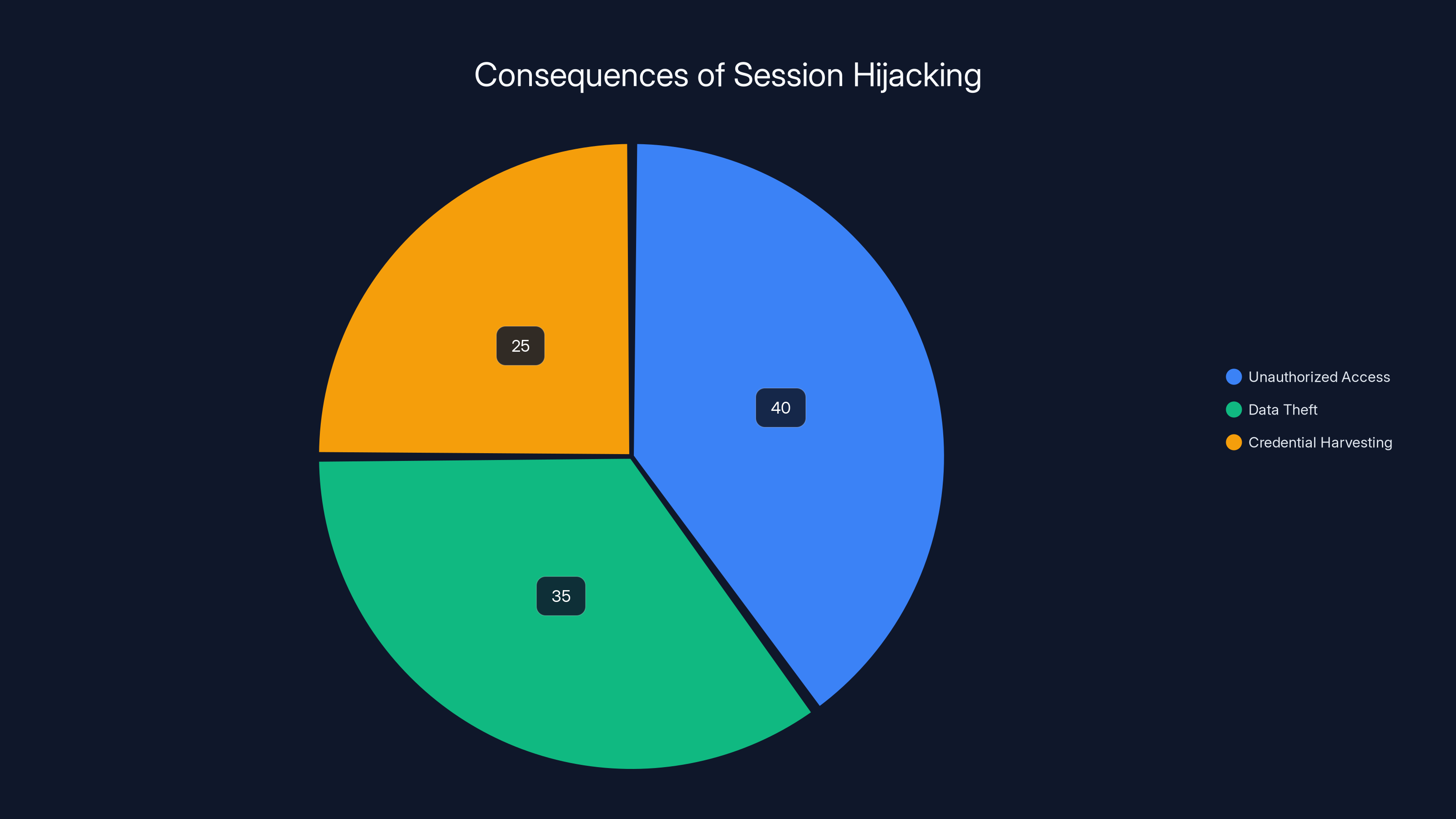
Unauthorized access is the most common consequence of session hijacking, followed by data theft and credential harvesting. (Estimated data)
Detection and Mitigation Strategies
Enhancing Security Measures
To combat session cookie theft, organizations should implement the following strategies:
- Regular Cookie Rotation: Frequently rotate session cookies to limit their lifespan.
- IP Address Monitoring: Alert on session access from suspicious IP addresses or geolocations.
- Behavioral Analytics: Use AI to detect unusual patterns in user behavior that could indicate hijacking.
- Zero Trust Architecture: Continuously verify user identities throughout a session.
Real-Time Monitoring
Implementing real-time monitoring solutions can help identify session anomalies. This involves analyzing session data for irregularities, such as multiple simultaneous logins from different locations.
User Education
Educating users about phishing and other social engineering attacks is crucial. Organizations should conduct regular training to keep employees informed about the latest threats.
Future Trends and Recommendations
Increased Use of AI
AI and machine learning will play a larger role in detecting and preventing session hijacking. By analyzing vast amounts of data, AI can identify anomalies that indicate cookie theft.
Legislation and Compliance
As these attacks become more prevalent, regulatory bodies may introduce stricter guidelines for session management and cybersecurity practices.
Conclusion
Session cookies are a double-edged sword: they enhance user experience but also expose vulnerabilities. As hackers continue to exploit these weaknesses, organizations must evolve their security strategies to protect sensitive data. By understanding the mechanisms behind session cookies and the threats they pose, businesses can better safeguard their assets against this growing threat.
FAQ
What are session cookies?
Session cookies are temporary files stored on a user's device to track and maintain the user's session on a website.
How do hackers steal session cookies?
Hackers typically use malware or social engineering tactics to gain access to session cookies stored on a user's device.
Can Multi-Factor Authentication prevent session hijacking?
While MFA strengthens the initial login process, it does not protect against session hijacking once a session is established.
What are some best practices to prevent session cookie theft?
Implement regular cookie rotation, monitor for suspicious IP addresses, use behavioral analytics, and educate users about potential threats.
Why is session hijacking becoming more common?
The availability of turnkey malware and the growing sophistication of cybercriminals make session hijacking a lucrative and accessible attack method.
How can AI help in preventing session hijacking?
AI can analyze large datasets to identify patterns and anomalies that may indicate session hijacking attempts, allowing for quicker detection and response.
What role does user education play in cybersecurity?
Educated users are less likely to fall victim to phishing and other tactics used to steal session cookies, making user training a crucial component of cybersecurity strategies.
How does session cookie theft impact businesses?
Stolen session cookies can lead to unauthorized access, data breaches, and potential financial losses for businesses.
Key Takeaways
- Stolen session cookies allow hackers to bypass MFA and access accounts undetected.
- Turnkey malware is making sophisticated attacks accessible to novice hackers.
- Regular cookie rotation and behavioral analytics can help mitigate session hijacking.
- Future cybersecurity strategies must incorporate AI for anomaly detection.
- User education is critical in preventing social engineering and cookie theft.
Related Articles
- Anthropic Teams Up With Its Rivals to Keep AI From Hacking Everything | WIRED
- Understanding and Mitigating Router Hacking Threats: A Deep Dive [2025]
- The Cybersecurity Boom: Addressing the Privacy Skills Shortage [2025]
- The Global Skills Gap in Modern Cyber Conflict [2025]
- Stay Safe from Deepfakes: Expert Steps to Verify Before You Act [2025]
- Inside the Shadowy World of Modern Scam Factories: Lessons from a Bombed Casino Near the Cambodia–Thailand Border [2025]
![Stolen Session Cookies: The Hidden Threat to Account Security [2025]](https://tryrunable.com/blog/stolen-session-cookies-the-hidden-threat-to-account-security/image-1-1775597647108.jpg)



