Understanding and Mitigating Router Hacking Threats: A Deep Dive [2025]
In recent years, cybersecurity threats have rapidly evolved, with one of the most concerning developments being the targeted attacks on home and small business routers. These devices, often overlooked in security setups, have become prime targets for sophisticated hacking groups like Fancy Bear, also known as APT 28. This article delves into how these attacks occur, the vulnerabilities involved, and practical steps for safeguarding your network.
TL; DR
- Thousands of routers compromised: Exploited vulnerabilities in Micro Tik and TP-Link routers.
- Fancy Bear tactics: Russian hackers redirect internet traffic to steal passwords.
- Unpatched routers: Critical vulnerabilities left open due to outdated firmware.
- Network security essentials: Regular updates, robust passwords, and network segmentation.
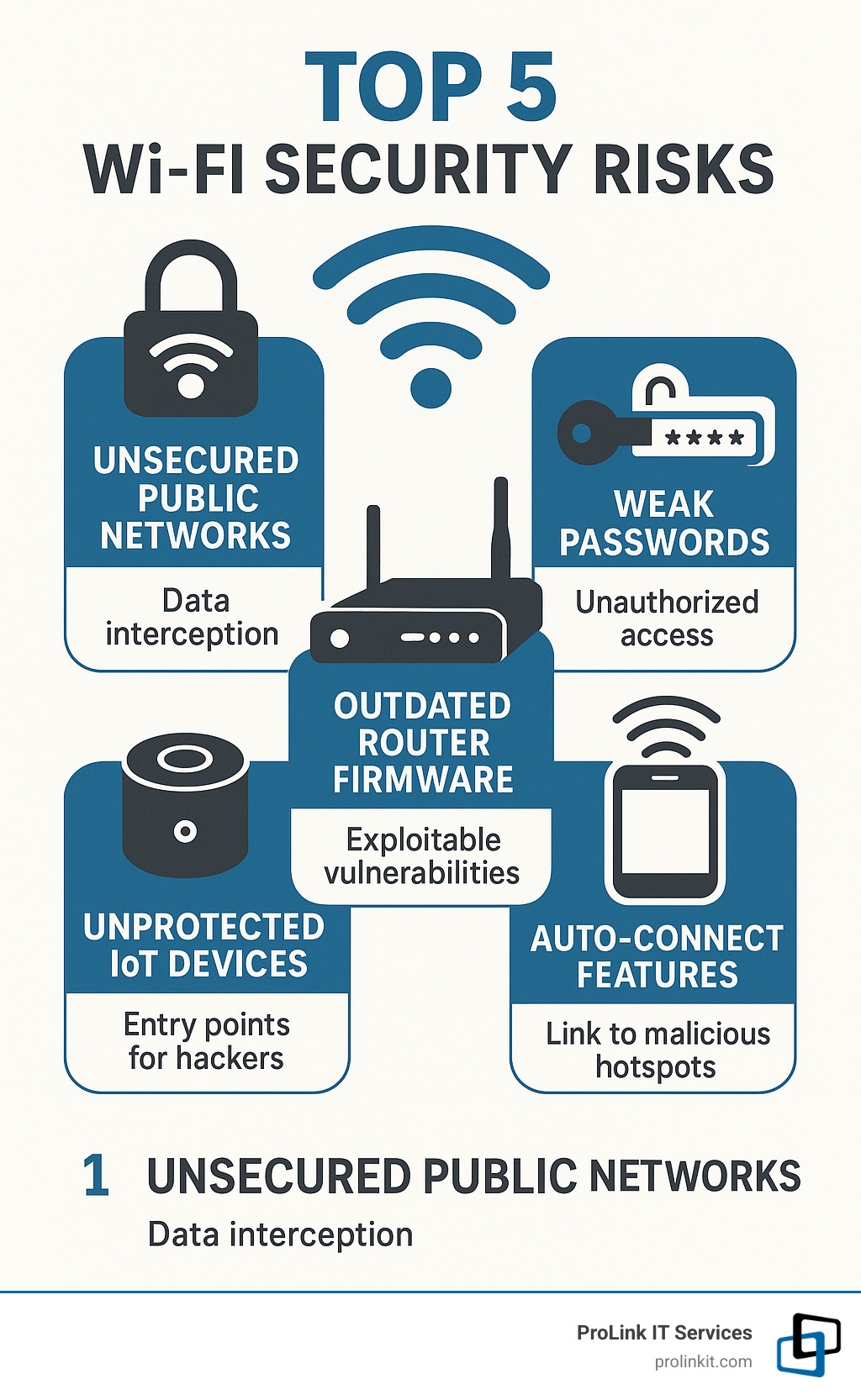
- Future trends: Increased targeting of IoT devices and enhanced AI-driven cybersecurity measures.
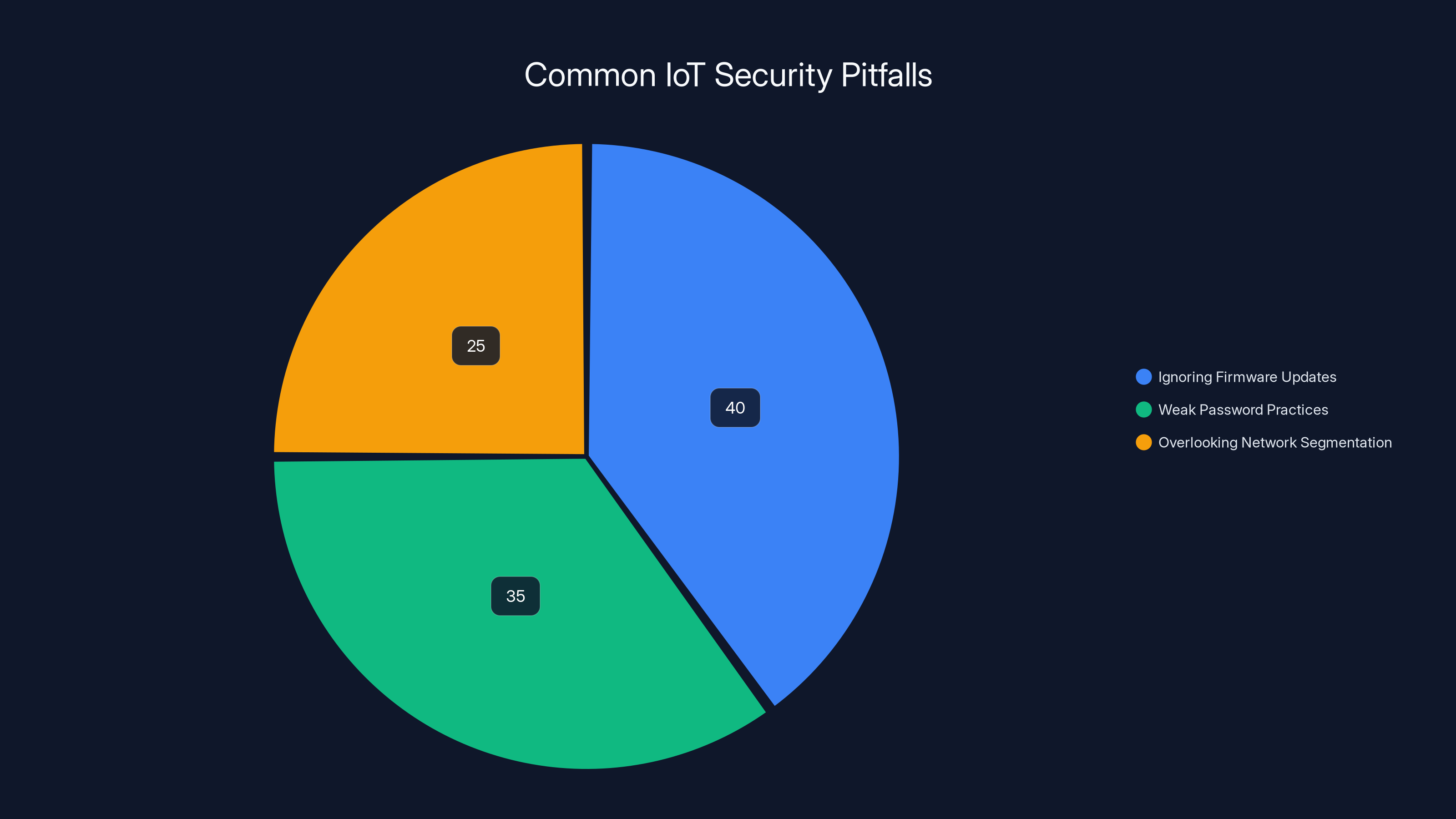
Ignoring firmware updates accounts for 40% of IoT security issues, highlighting the need for proactive management. Estimated data.
The Rise of Router Hacking
Understanding the Motivation
Router hacking has surged as a preferred method for cybercriminals, primarily due to the high reward and low-risk nature of these attacks. By compromising routers, hackers gain access to a wealth of data, including personal credentials and sensitive business information, without directly attacking more secure endpoints like laptops or smartphones.
Fancy Bear, a notorious hacking group linked to Russia's GRU, exemplifies this strategy. Their operations have extended beyond traditional cyber espionage to include router hijacking, leveraging these devices as entry points into broader network infrastructures.
Vulnerabilities in Focus
Routers, especially those from brands like Micro Tik and TP-Link, have been targeted for their unpatched vulnerabilities. These vulnerabilities often arise from outdated firmware, which users neglect to update due to a lack of awareness or technical ability.
Some common vulnerabilities include:
- Default Credentials: Many routers ship with default usernames and passwords, making them easy targets.
- Firmware Exploits: Unpatched firmware can leave routers open to known exploits.
- Remote Access: Insecure remote management settings can be exploited to gain control over the router.

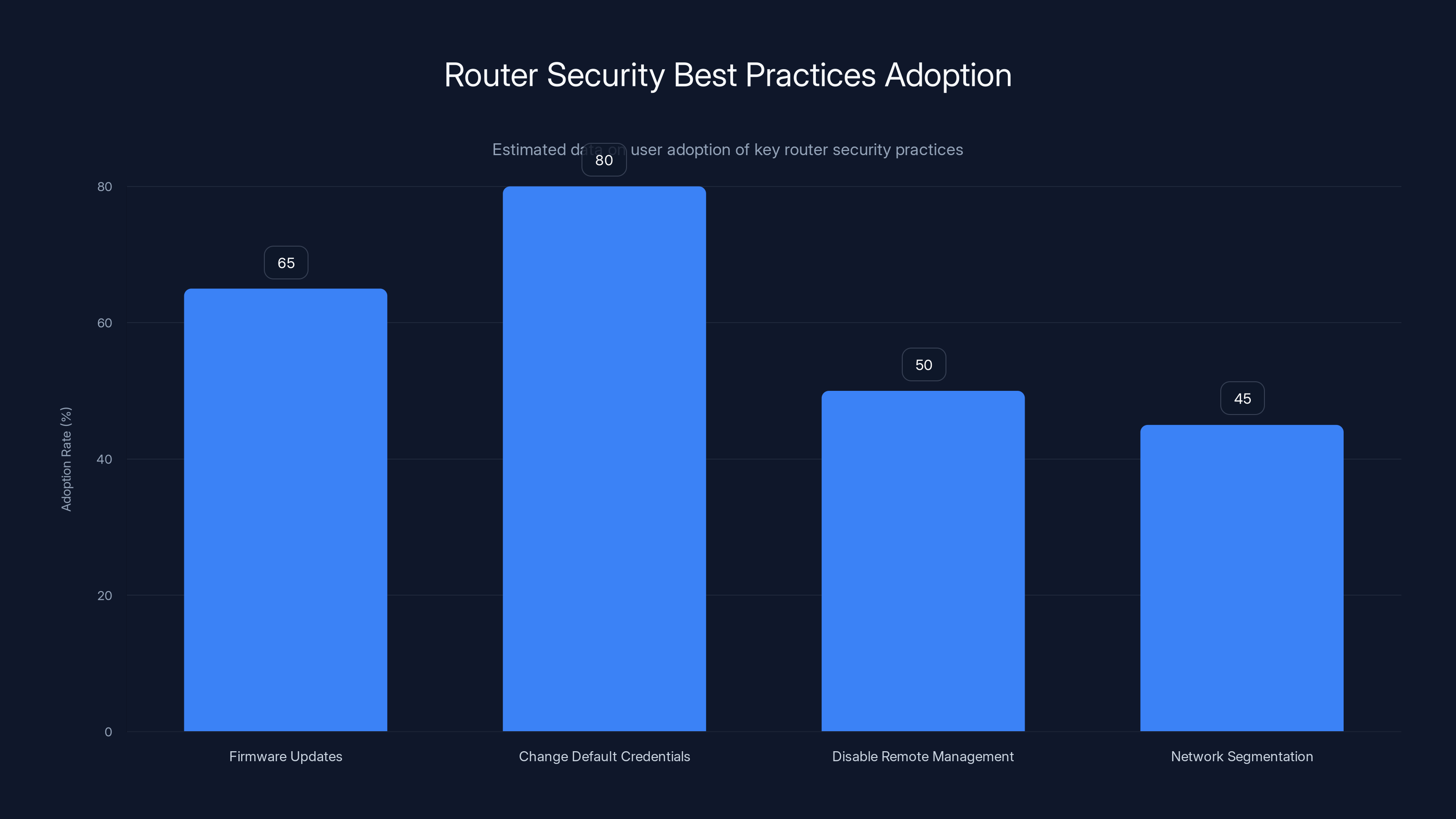
Estimated data suggests that changing default credentials has the highest adoption rate among users, while network segmentation is less commonly implemented.
How Fancy Bear Executes Attacks
The Attack Vector
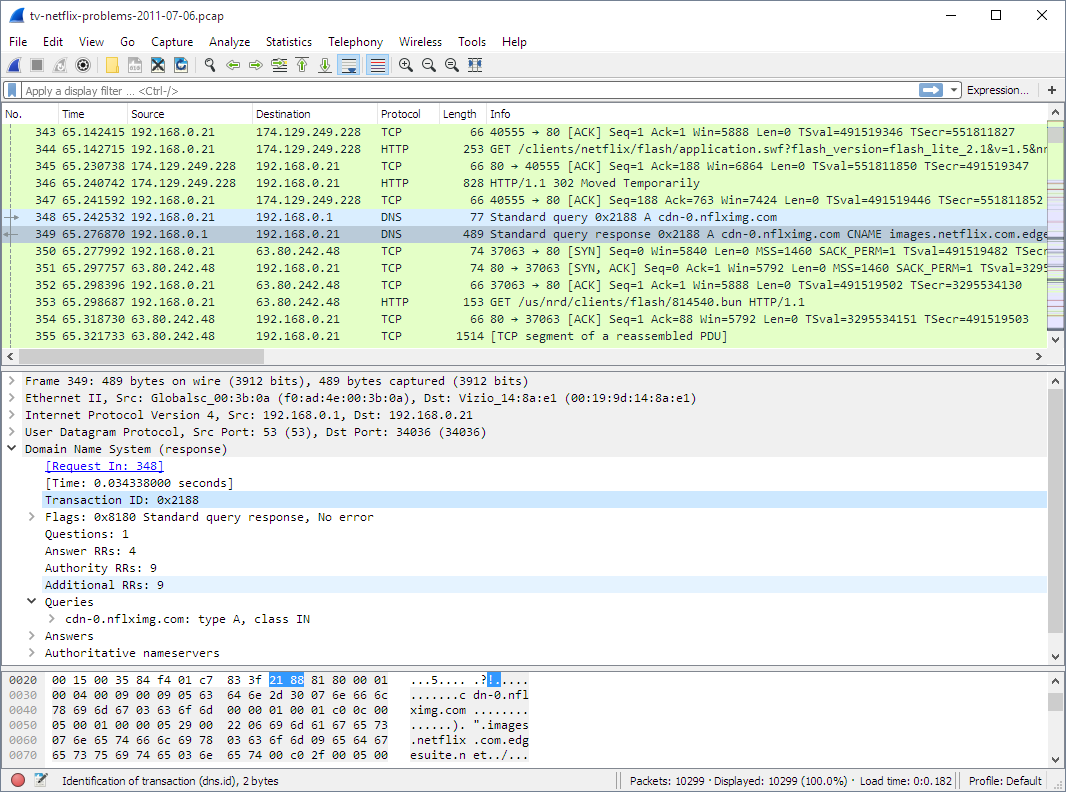
Fancy Bear deploys a multi-faceted approach to compromise routers. Their tactics typically involve scanning the internet for vulnerable devices, using known exploits to gain access, and then redirecting traffic through malicious servers. This method allows them to intercept and steal data without the user's knowledge.
Technical Steps Involved
- Reconnaissance: Scanning for IP addresses with open ports and known vulnerabilities.
- Exploitation: Using exploits against outdated firmware or default credentials.
- Payload Deployment: Installing malware to control the router and redirect traffic.
- Data Exfiltration: Intercepting data such as passwords and access tokens during traffic redirection.
Best Practices for Router Security
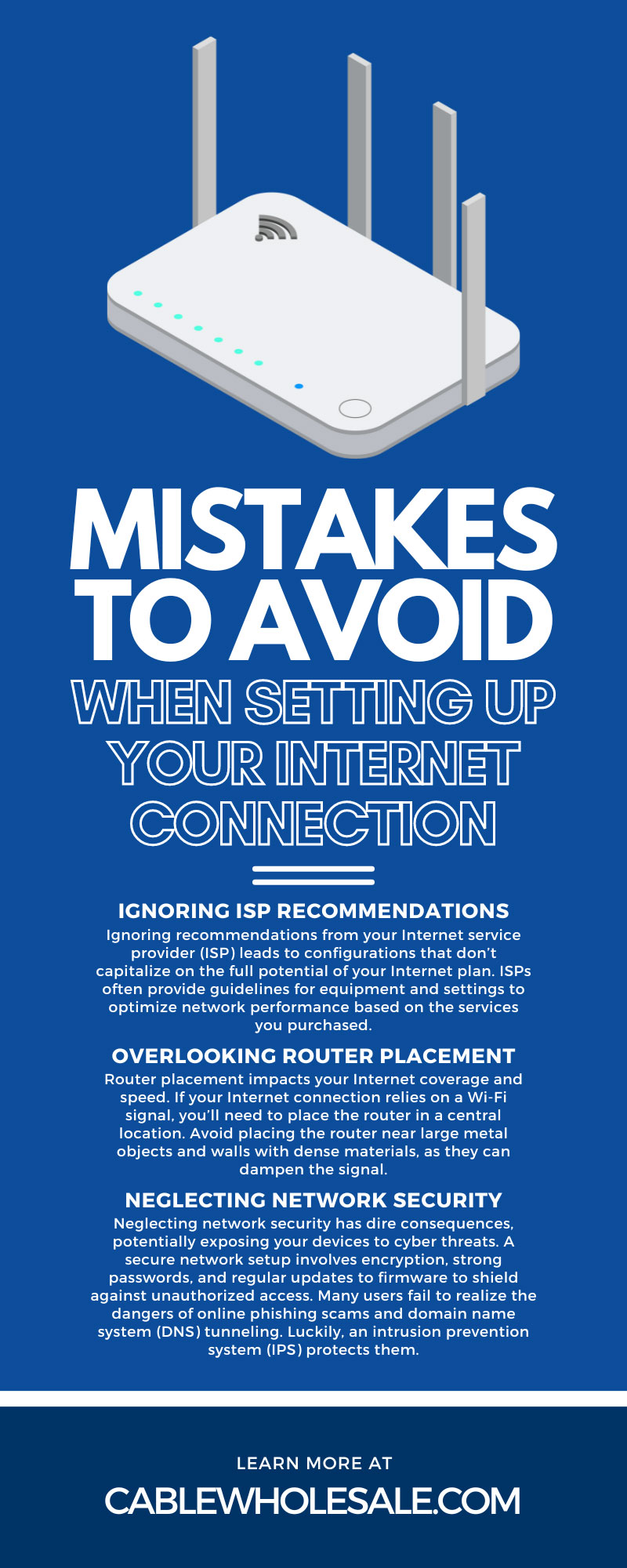
Updating Firmware
Firmware updates are critical for securing routers. Manufacturers like Micro Tik and TP-Link regularly release updates to patch vulnerabilities. Users should:
- Regularly check for updates: Set reminders to check the router’s firmware version monthly.
- Enable automatic updates: If available, enable this feature to ensure timely installations.
- Consult manufacturer guidelines: Follow the specific update instructions provided by the router's manufacturer.
Secure Configuration
- Change Default Credentials: Immediately replace default login credentials with strong, unique passwords.
- Disable Remote Management: Unless absolutely necessary, disable remote management features to prevent external access.
- Network Segmentation: Use separate networks for guest users and IoT devices to minimize the risk of a compromised device affecting your primary network.

Firmware updates and firewalls are among the most effective measures for router security. Estimated data based on typical security practices.
Advanced Protection Measures
Implementing Network Monitoring
Network monitoring tools can detect unusual activity that may indicate a compromised router. Solutions like Wireshark and Nagios provide real-time alerts for suspicious behavior, allowing for prompt response.
Utilizing VPNs
Virtual Private Networks (VPNs) encrypt internet traffic, adding an extra layer of security. They are particularly useful for protecting data from man-in-the-middle attacks.
Firewall Configuration
- Enable router firewalls: Configure your router’s built-in firewall to block unauthorized access attempts.
- Use additional firewalls: Consider deploying software firewalls on individual devices for added protection.
Common Pitfalls and How to Avoid Them
Ignoring Firmware Updates
Many users neglect firmware updates due to inconvenience or lack of knowledge. Automatic update features can mitigate this risk, but users must be proactive in enabling these settings.
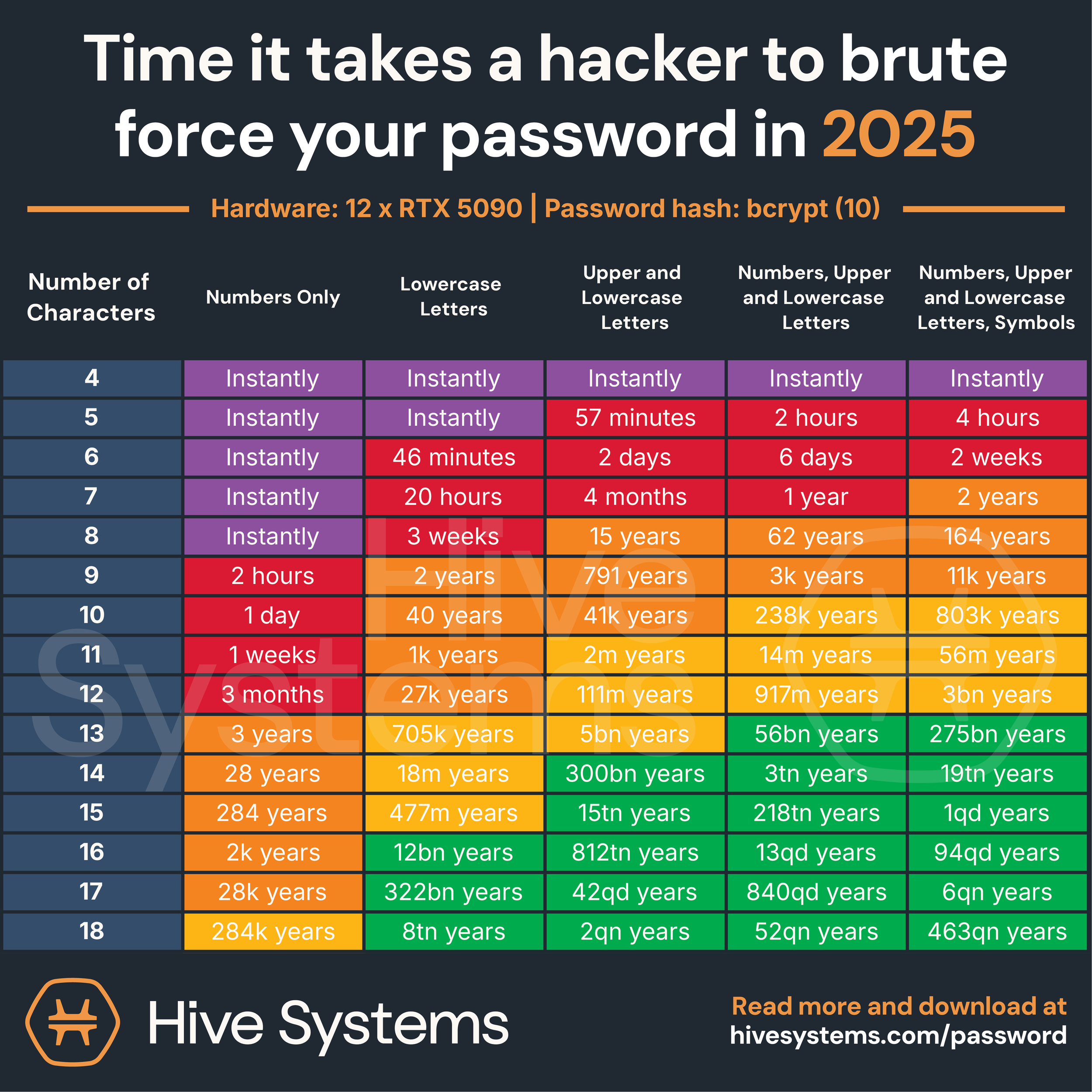
Weak Password Practices
Using weak or default passwords is a common oversight. Password managers can help generate strong passwords and manage them efficiently.
Overlooking Network Segmentation
Failing to segment networks can lead to widespread compromise if a single device is breached. Implementing VLANs (Virtual Local Area Networks) can help isolate sensitive devices and data.
Future Trends in Router Security
The Rise of AI in Cybersecurity
Artificial intelligence is increasingly being used to detect and respond to threats in real-time. AI can identify patterns indicative of a security breach, allowing for faster and more effective interventions.
Enhanced Router Features
Future routers are expected to come equipped with advanced security features such as automatic threat detection, enhanced encryption protocols, and integrated VPN capabilities.
Recommendations for Enhanced Protection
Regular Security Audits
Conducting regular security audits can help identify vulnerabilities before they are exploited. These audits should include:
- Vulnerability scanning: Regularly scanning for known threats and vulnerabilities.
- Penetration testing: Simulating attacks to test the robustness of security measures.
Continuous Education
Stay informed about the latest cybersecurity threats and best practices. Resources such as cybersecurity blogs, forums, and webinars can provide valuable insights.
Conclusion
Router security is a critical aspect of protecting both personal and business data. By understanding the tactics used by groups like Fancy Bear and implementing robust security measures, users can significantly reduce their risk of falling victim to such attacks. As technology evolves, so too must our approaches to cybersecurity, ensuring that we remain vigilant against emerging threats.
FAQ
What are the main risks of not updating router firmware?
Outdated firmware can leave routers vulnerable to known exploits, enabling hackers to gain unauthorized access and intercept sensitive data.
How can I ensure my router is secure?
Regularly update your router’s firmware, change default credentials, and disable unnecessary remote access features. Use strong passwords and consider network segmentation for enhanced security.
What should I do if I suspect my router has been hacked?
Immediately disconnect the router from the internet, reset it to factory settings, update the firmware, and change all passwords. Monitor network traffic for any unusual activity.
Are VPNs effective in protecting router data?
Yes, VPNs encrypt your internet traffic, making it more difficult for hackers to intercept and access your data during transmission.
Can AI help in preventing router hacks?
AI can enhance cybersecurity by detecting unusual patterns indicative of an attack, allowing for rapid response and mitigation.
Is it safe to enable remote management on my router?
Remote management should be disabled unless absolutely necessary, as it can provide hackers with a potential entry point into your network.
What is the role of firewalls in router security?
Firewalls help block unauthorized access attempts, serving as a barrier between your network and potential threats. They are a critical component of a comprehensive security strategy.
How often should I conduct a security audit on my network?
Conduct security audits at least twice a year, or more frequently if you suspect vulnerabilities or experience significant network changes.
Key Takeaways
- Russian hackers have exploited vulnerabilities in home routers to hijack network traffic.
- Unpatched firmware is a significant risk factor for router security.
- Fancy Bear, linked to Russia’s GRU, continues to target routers worldwide.
- Regular firmware updates and strong passwords are crucial for router security.
- AI-driven cybersecurity solutions can enhance detection and response times.
- Network segmentation and VPNs provide additional layers of protection.
- Future routers may include advanced security features like AI threat detection.
Related Articles
- Understanding the Espionage Ecosystem Threat [2025]
- The Cybersecurity Boom: Addressing the Privacy Skills Shortage [2025]
- Stay Safe from Deepfakes: Expert Steps to Verify Before You Act [2025]
- Inside the Shadowy World of Modern Scam Factories: Lessons from a Bombed Casino Near the Cambodia–Thailand Border [2025]
- Cybercriminals Target Vulnerable Sectors as Crypto Fraud Escalates [2025]
- Why Cookie Banners Should Be Banned: A Deep Dive [2025]
![Understanding and Mitigating Router Hacking Threats: A Deep Dive [2025]](https://tryrunable.com/blog/understanding-and-mitigating-router-hacking-threats-a-deep-d/image-1-1775583376248.jpg)



