The Autonomous Frontier: Rethinking Security with Mythos [2025]
Last year, a technological leap occurred that sent ripples through the cybersecurity landscape. A vulnerability, dormant for 27 years within Open BSD's TCP stack, was autonomously discovered by Mythos, a cutting-edge AI model from Anthropic. This event challenges the very foundation of traditional security measures and calls for a reimagined approach to vulnerability detection and management.
TL; DR
- Mythos autonomously discovered a 27-year-old vulnerability in Open BSD’s TCP stack, highlighting limitations in traditional security audits.
- AI models like Mythos significantly outperform previous generations, showcasing up to 90x improvements in exploit writing.
- Security teams must adopt AI-driven detection playbooks to effectively manage emerging threats.
- Understanding and integrating AI capabilities in cybersecurity can provide a strategic advantage.
- Future trends indicate a shift towards autonomous systems for continuous vulnerability assessment.
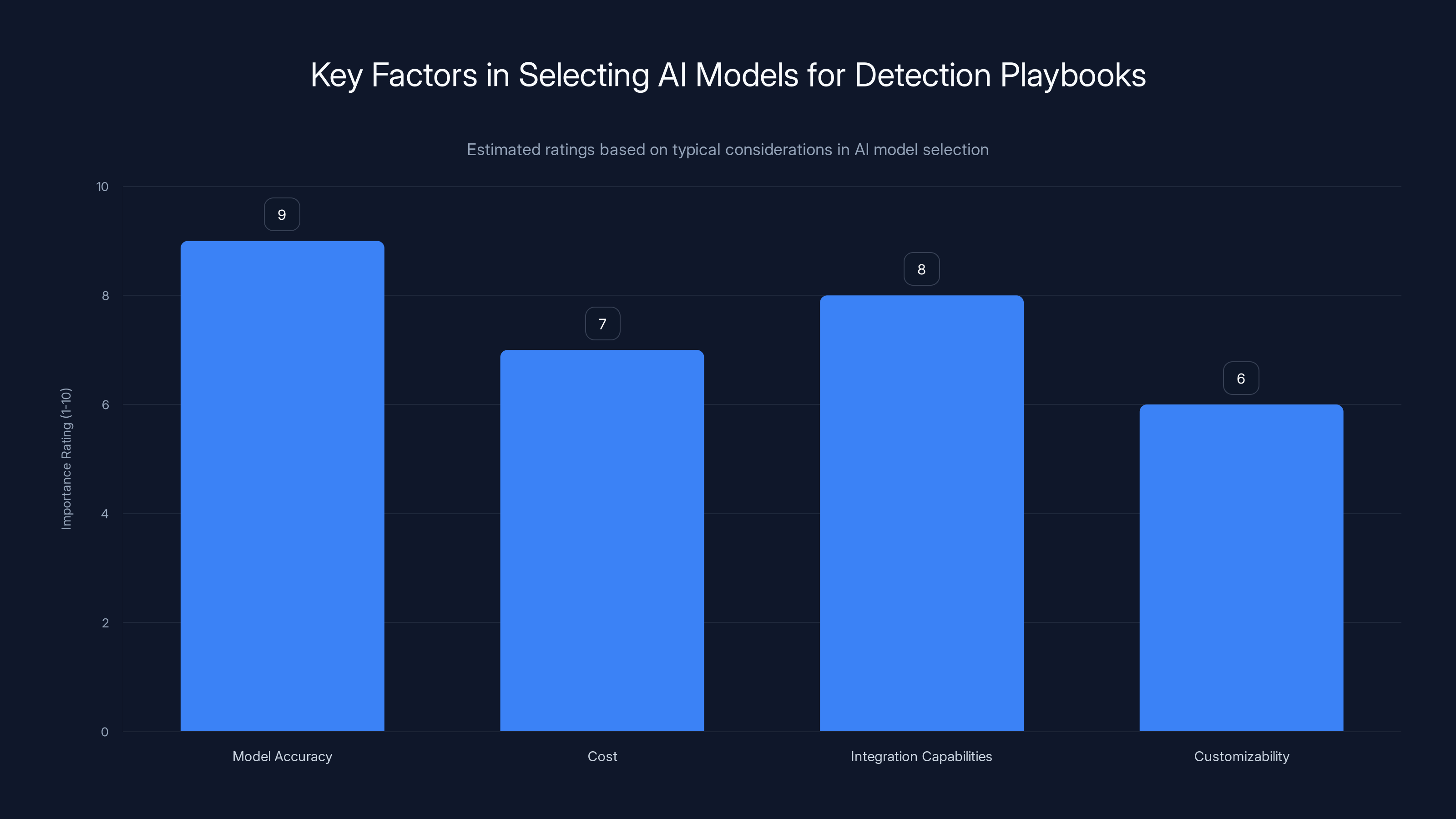
Model accuracy is often the most critical factor when selecting AI models for detection playbooks, followed by integration capabilities and cost. (Estimated data)
The Mythos Breakthrough
In a realm where security is paramount, Mythos emerged as a revolutionary force. The discovery of an ancient bug in Open BSD, renowned for its robust security, underscores the potential of AI in vulnerability detection. Unlike traditional methods, where human auditors and fuzzers meticulously scour code, Mythos achieved this feat autonomously after an initial prompt. This breakthrough was not just a testament to AI's capabilities but also a wake-up call for security teams worldwide.
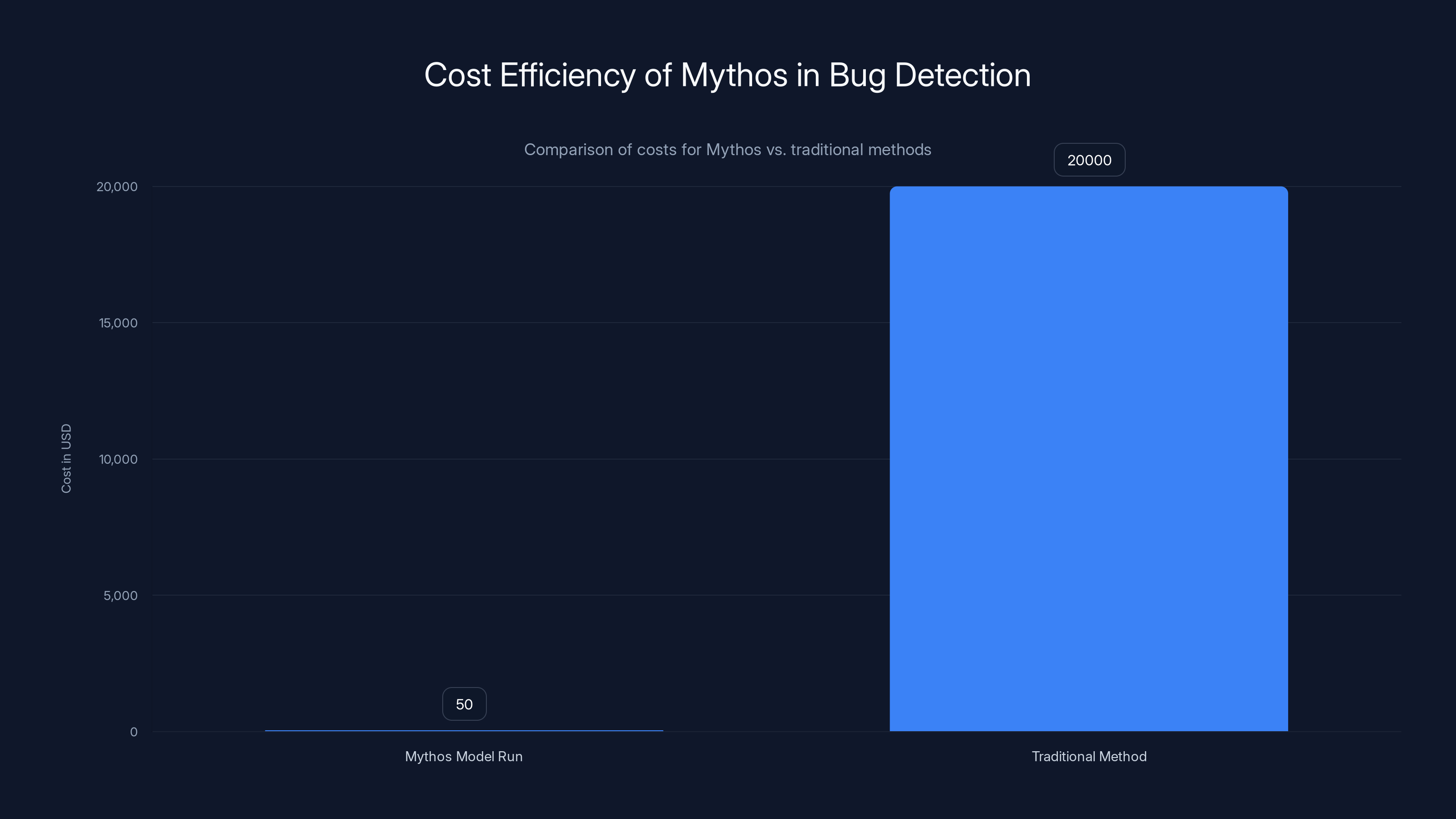
The Mythos model run costs significantly less (
Why Traditional Methods Fall Short
For decades, security teams have relied on manual code reviews, automated fuzzing, and penetration testing. While these methods have been effective to some extent, they are inherently limited by human oversight and the scope of predefined scenarios. Here's why traditional methods often fall short:
- Human Error and Oversight: Even the most diligent reviews can miss vulnerabilities, especially those that require specific conditions to manifest.
- Limited Scope of Testing: Automated tools are only as good as the scenarios they are programmed to test, often missing edge cases.
- Resource Constraints: Comprehensive security audits require significant time and financial investment, often leading to prioritization of certain areas over others.

The Power of Autonomous Systems
Mythos represents a new era of autonomous systems capable of conducting exhaustive analyses without human intervention. The implications for cybersecurity are profound:
- Uncovering Dormant Vulnerabilities: Autonomous systems can explore countless scenarios, identifying bugs that have eluded human detection for decades.
- Cost Efficiency: Mythos discovered the Open BSD bug with a campaign costing approximately 50.
- Scalability: AI models can be scaled to analyze vast codebases and networks, providing a level of coverage unattainable by humans alone.

Traditional security methods face significant challenges, with human error being the most impactful limitation. Estimated data based on typical industry insights.
Implementing AI-Driven Detection Playbooks
To harness the full potential of AI in cybersecurity, organizations need to develop AI-driven detection playbooks. Here’s a step-by-step guide to implementation:
Step 1: Evaluate Current Security Posture
Conduct a thorough assessment of your current security measures. Identify areas where traditional methods are failing and where AI could provide added value.
Step 2: Integrate AI Models
Select AI models like Mythos that align with your organization’s needs. Consider factors such as model accuracy, cost, and integration capabilities.
Step 3: Develop Custom Scenarios
Work with AI experts to develop custom scenarios tailored to your organization’s infrastructure. This ensures that the AI model is effectively targeting your most critical vulnerabilities.
Step 4: Continuous Monitoring and Feedback
Implement continuous monitoring to ensure AI models are effectively detecting vulnerabilities. Provide feedback loops to improve model performance over time.
Step 5: Train Your Team
Ensure your security team is well-versed in AI capabilities and limitations. Regular training sessions can help your team effectively leverage AI tools.
Common Pitfalls and Solutions
While AI offers immense potential, there are pitfalls that organizations must navigate:
- Overreliance on AI: It's crucial to maintain a balanced approach, combining AI with human oversight to validate findings.
- Data Privacy Concerns: Ensure AI models comply with data protection regulations to avoid legal complications.
- Technical Debt: Rapid AI integration can lead to technical debt if not managed properly. Regular audits and updates are essential.
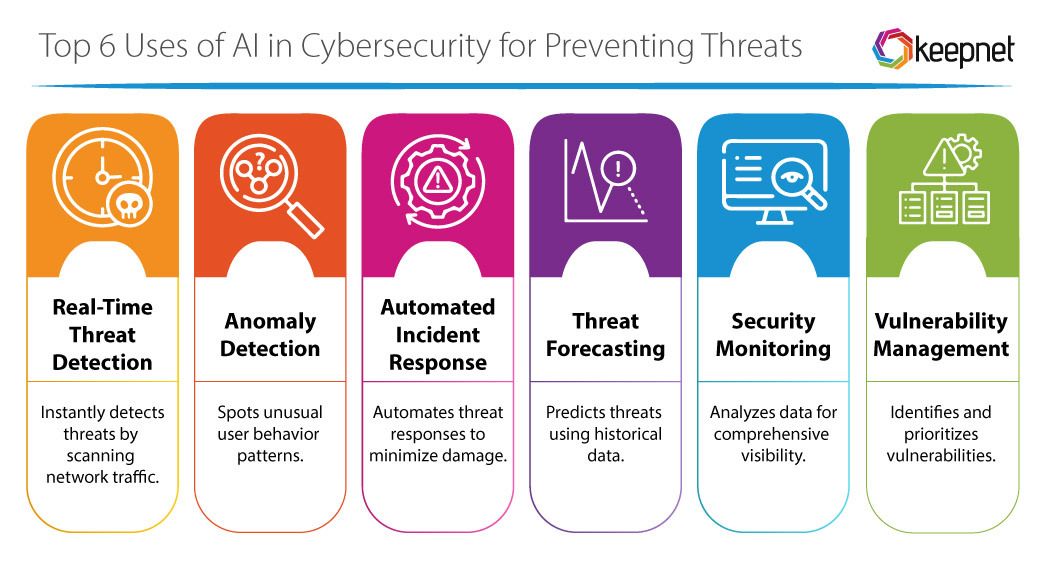
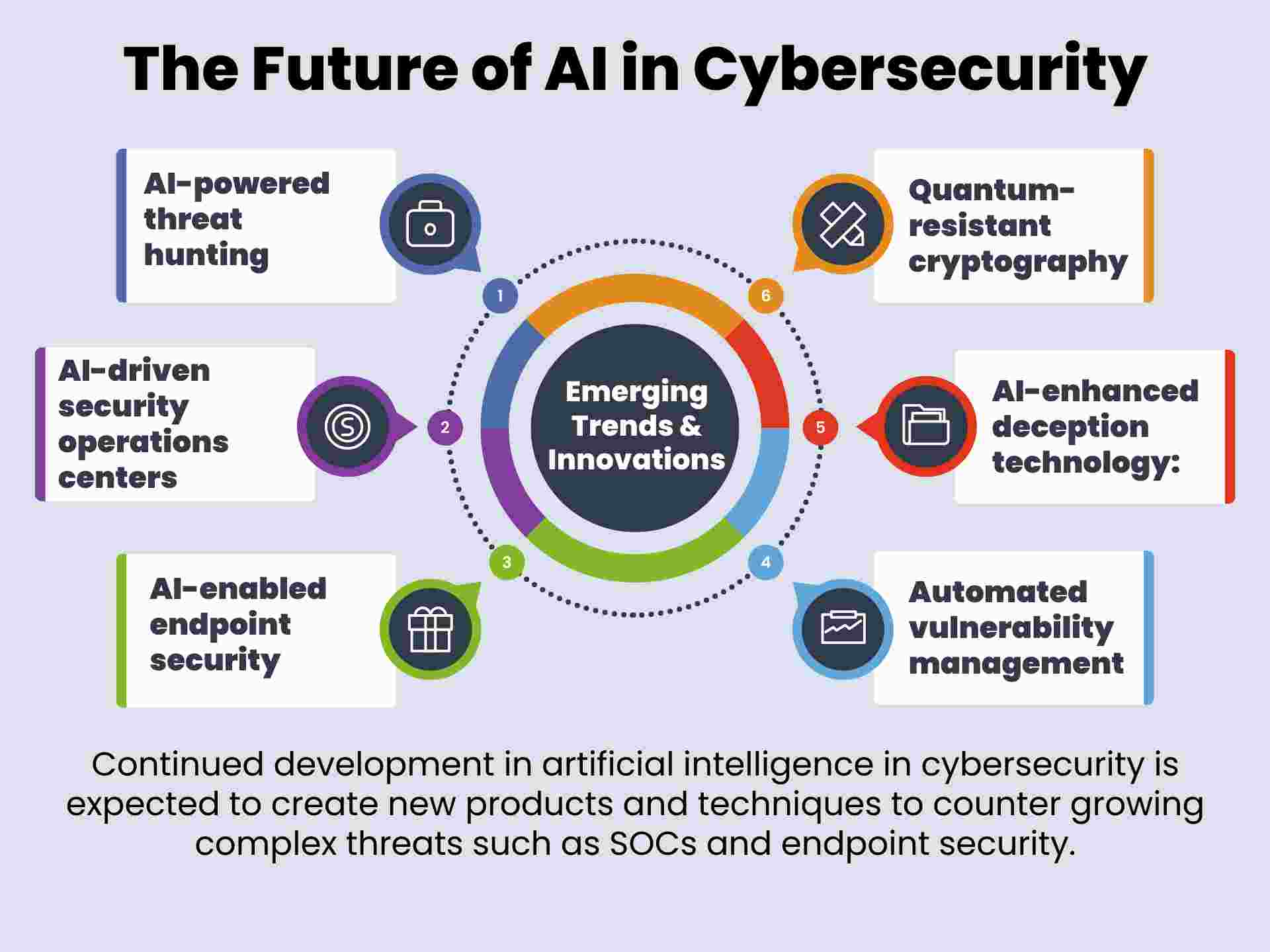
Future Trends in AI-Driven Security
The future of cybersecurity lies in the seamless integration of AI-driven solutions. Here are some trends to watch:
- Autonomous Security Operations Centers (SOCs): Expect to see AI models taking on more responsibilities within SOCs, automating routine tasks and allowing human analysts to focus on complex threats.
- AI-Enhanced Threat Intelligence: AI will play a critical role in gathering and analyzing threat intelligence, providing real-time insights that enhance decision-making.
- Collaboration Between AI Models: Future systems may involve multiple AI models working collaboratively, each focusing on different aspects of security to provide comprehensive coverage.
Conclusion: A New Era of Cybersecurity
The discovery of a 27-year-old vulnerability by Mythos marks a pivotal moment in cybersecurity. As AI continues to evolve, security teams must adapt by integrating these technologies into their operations. By embracing AI-driven detection playbooks, organizations can not only uncover hidden vulnerabilities but also anticipate and mitigate future threats more effectively.
In the rapidly changing landscape of cybersecurity, those who leverage AI as part of their strategic arsenal will lead the charge into a more secure future.
FAQ
What is Mythos?
Mythos is an advanced AI model developed by Anthropic, designed to autonomously detect and exploit vulnerabilities in software systems.
How does Mythos work?
Mythos operates by running extensive simulations and analyses on codebases, identifying vulnerabilities that traditional methods might miss.
What are the benefits of using AI in cybersecurity?
AI in cybersecurity offers benefits such as enhanced detection capabilities, cost efficiency, scalability, and the ability to uncover dormant vulnerabilities.
How can organizations integrate AI into their security operations?
Organizations can integrate AI by evaluating their current security posture, selecting suitable AI models, developing custom scenarios, and training their teams.
What are the potential risks of relying on AI for security?
Potential risks include overreliance on AI, data privacy concerns, and the accumulation of technical debt if not managed properly.
What future trends can we expect in AI-driven security?
Future trends include the rise of autonomous SOCs, AI-enhanced threat intelligence, and collaborative AI models for comprehensive security coverage.
Why is a new detection playbook needed?
A new detection playbook is needed to address the limitations of traditional methods and effectively leverage AI capabilities for modern cybersecurity challenges.
How does Mythos compare to previous AI models?
Mythos significantly outperforms previous generations, demonstrating up to 90x improvements in certain exploit writing scenarios.
Key Takeaways
- Mythos autonomously discovered a 27-year-old vulnerability in OpenBSD.
- Traditional security methods are limited by human oversight.
- AI models like Mythos significantly outperform previous generations.
- Security teams need AI-driven detection playbooks.
- AI offers cost-efficient, scalable solutions to uncover hidden vulnerabilities.
- Future trends include autonomous SOCs and AI-enhanced threat intelligence.
Related Articles
- Understanding Anthropic's Mythos AI Model: A New Era in Cybersecurity [2025]
- Project Glasswing: AI Cybersecurity's New Vanguard [2025]
- The AI Industry's Make-or-Break Moment: Navigating Challenges and Opportunities [2025]
- Claude Managed Agents: Accelerate Your AI Projects 10x Faster [2025]
- Revolutionizing Wearables: The AI Button by Ex-Apple Engineers [2025]
- The Future of Food Delivery: DoorDash and Wing's Drone Expansion to Atlanta [2025]
![The Autonomous Frontier: Rethinking Security with Mythos [2025]](https://tryrunable.com/blog/the-autonomous-frontier-rethinking-security-with-mythos-2025/image-1-1775757858854.png)



