Understanding Anthropic's Mythos AI Model: A New Era in Cybersecurity [2025]
Last month, Anthropic unveiled its latest innovation in the field of cybersecurity: the Mythos AI model. This new model is a part of Anthropic's ongoing efforts to enhance security measures using artificial intelligence. But unlike typical product launches, access to Mythos is highly restricted, raising questions about its capabilities and the reasoning behind such exclusivity.
TL; DR
- Mythos is a groundbreaking AI model designed to revolutionize cybersecurity.
- Access is limited to select organizations, including major tech companies.
- Anthropic aims to address security vulnerabilities through advanced AI.
- The model's exclusivity raises questions about its potential impact.
- Future trends suggest broader AI integration into cybersecurity.
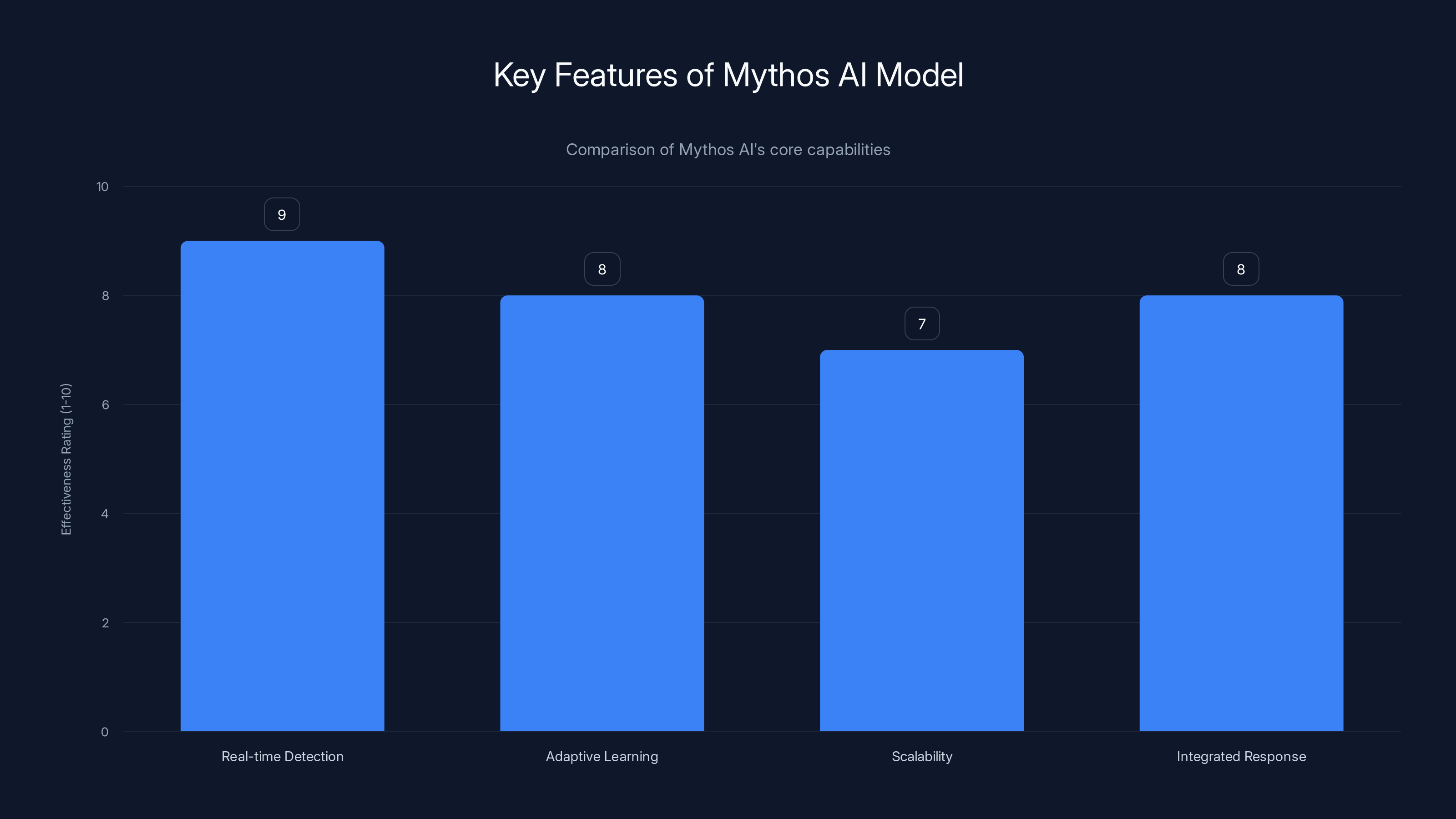
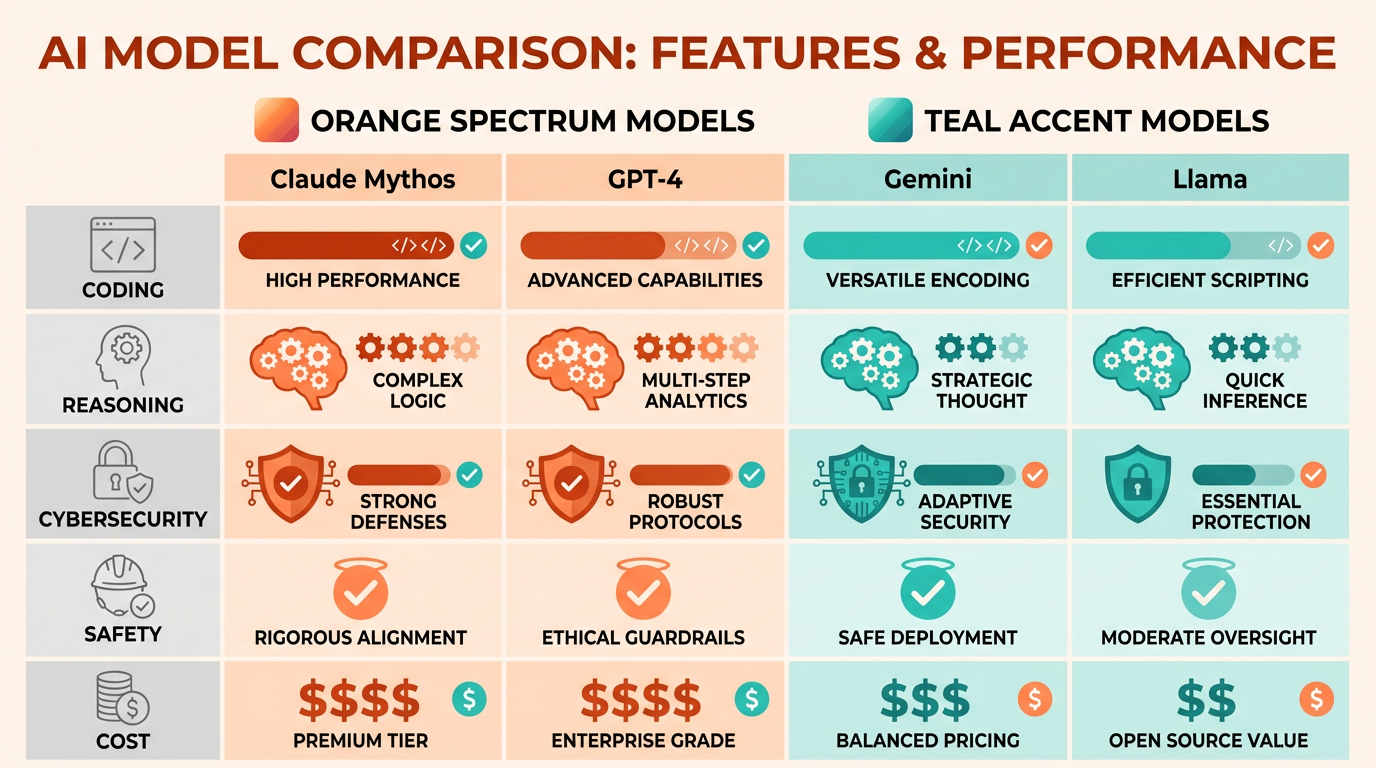
Mythos AI excels in real-time threat detection and integrated response mechanisms, with high effectiveness ratings across all features. Estimated data.
What is Mythos?
Mythos is Anthropic's latest AI model tailored specifically for cybersecurity applications. Built on advanced machine learning algorithms, it aims to detect, analyze, and respond to cyber threats in real-time. The model is designed to address the growing complexity of cyber threats, leveraging AI's ability to process vast amounts of data at unprecedented speeds as reported by Fortune.
Key Features
- Real-time Threat Detection: Mythos can identify potential threats as they occur, analyzing data patterns and behaviors to predict and mitigate attacks.
- Adaptive Learning: The model continuously updates its algorithms based on new data, ensuring it stays ahead of emerging threats.
- Scalability: Designed to handle data from large enterprises, Mythos can scale according to the demands of the organization.
- Integrated Response Mechanisms: Mythos doesn't just detect threats; it can also automate response strategies, minimizing human intervention and reaction times according to Geeky Gadgets.
Current Access and Limitations
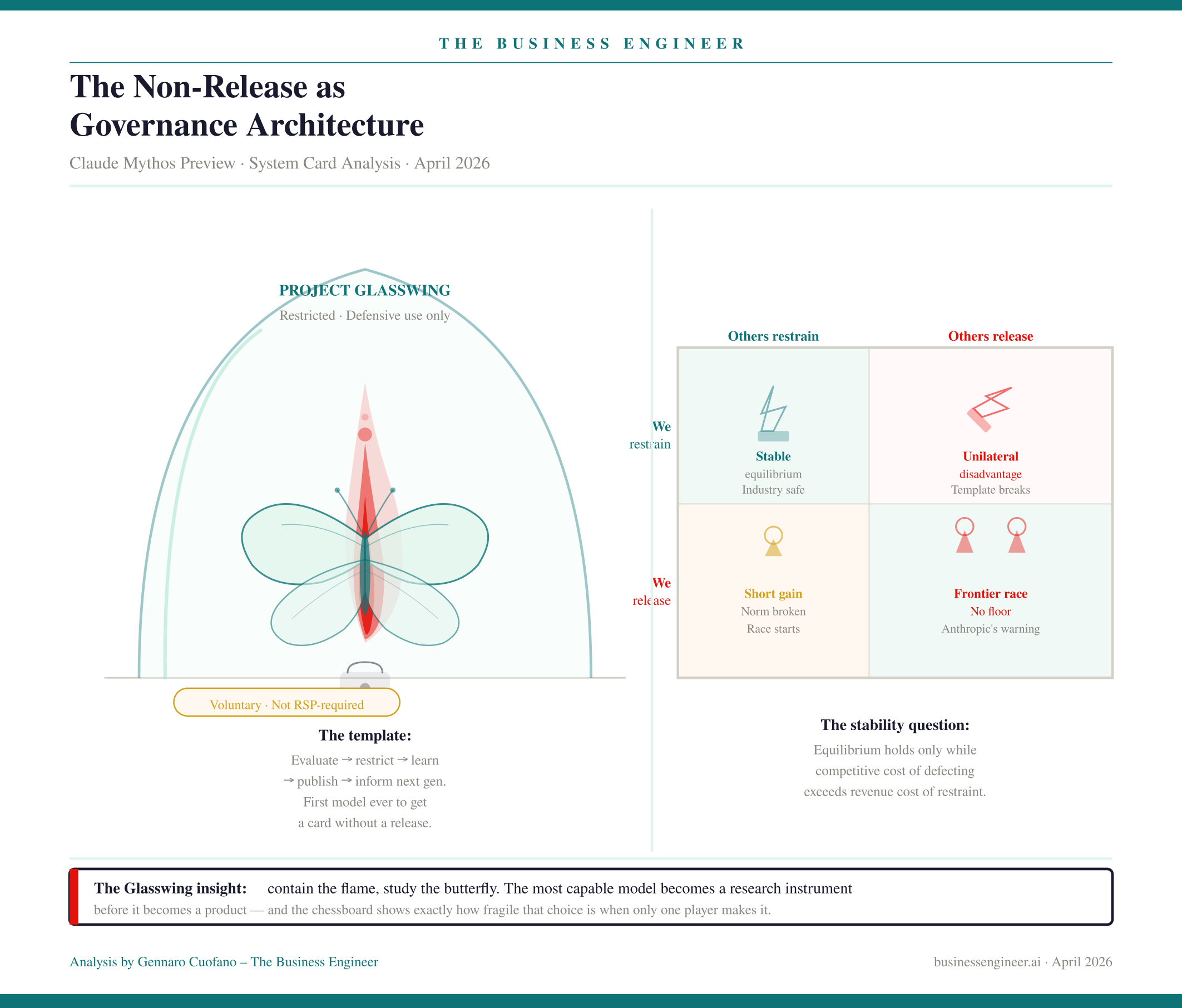
Currently, access to Mythos is limited to a select group of organizations, including industry giants like Amazon, Apple, and Microsoft. This restricted access has been put in place to ensure that the model is tested and refined within controlled environments before a broader release as noted by Fortune.
Why Is Access Limited?
There are several reasons why Anthropic might choose to limit access to Mythos:
-
Security Concerns: Given the sensitive nature of cybersecurity, it is crucial to ensure that the model is not misused or exploited by malicious actors.
-
Refinement Phase: By limiting access, Anthropic can gather feedback and make necessary adjustments to the model before a full-scale launch.
-
Strategic Partnerships: Collaborating with leading tech companies allows for extensive testing and validation in real-world scenarios as highlighted by CNBC.
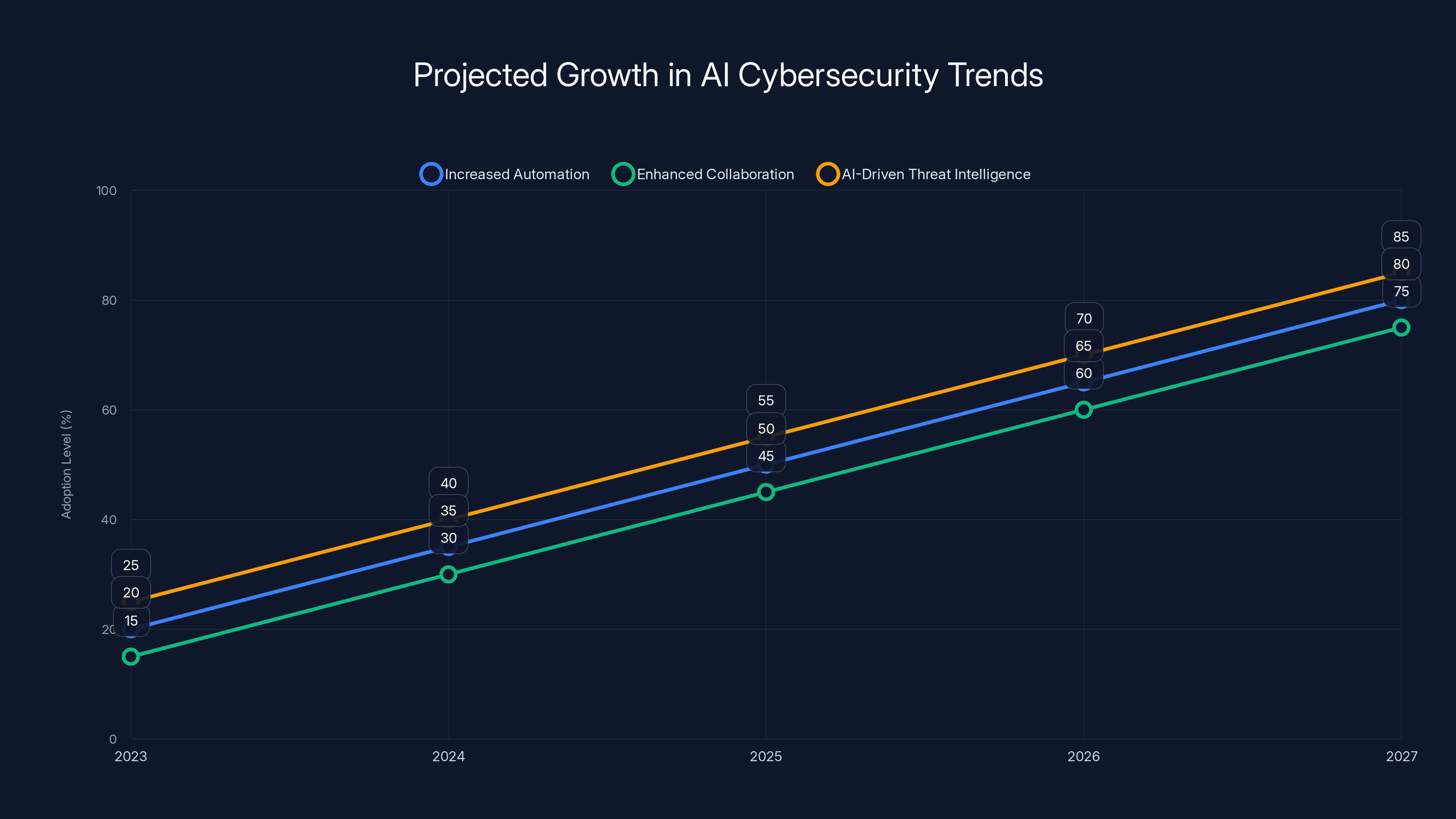
Projected data shows significant growth in AI cybersecurity trends, with automation and threat intelligence leading by 2027. Estimated data.
Practical Implementation of Mythos
Integrating Mythos into an organization's cybersecurity framework requires careful planning and execution. Here’s a step-by-step guide on how companies can effectively implement this AI model:
Step 1: Assess Current Cybersecurity Infrastructure
Before integrating Mythos, organizations should evaluate their existing cybersecurity measures. This assessment will identify gaps that Mythos can fill and ensure that the AI model is compatible with current systems as detailed by Fortune.
Step 2: Define Security Objectives
Organizations need to clearly define their security goals and how Mythos will help achieve them. This includes identifying specific threats they aim to combat and the metrics for success.
Step 3: Data Integration
Mythos requires access to a vast amount of data to function effectively. Organizations must ensure that their data is structured and accessible for the model to analyze.
Step 4: Pilot Testing
Conducting a pilot test allows organizations to observe how Mythos performs in their specific environment. This phase is crucial for identifying any issues and making necessary adjustments.
Step 5: Full-Scale Deployment
Once the pilot test is successful, organizations can proceed with full-scale deployment. Continuous monitoring and assessment are necessary to ensure the model's effectiveness and adapt to any changes in the cybersecurity landscape as suggested by IBM.
Common Pitfalls and Solutions
Pitfall 1: Inadequate Data
Solution: Ensure that data sources are comprehensive and continuously updated. Collaborate with data providers if necessary to enhance data quality.
Pitfall 2: Misalignment with Security Goals
Solution: Regularly review security objectives and adjust Mythos's configurations to align with evolving goals.
Pitfall 3: Overreliance on Automation
Solution: While Mythos automates many processes, human oversight is essential. Establish a team to monitor the AI's actions and intervene when necessary.

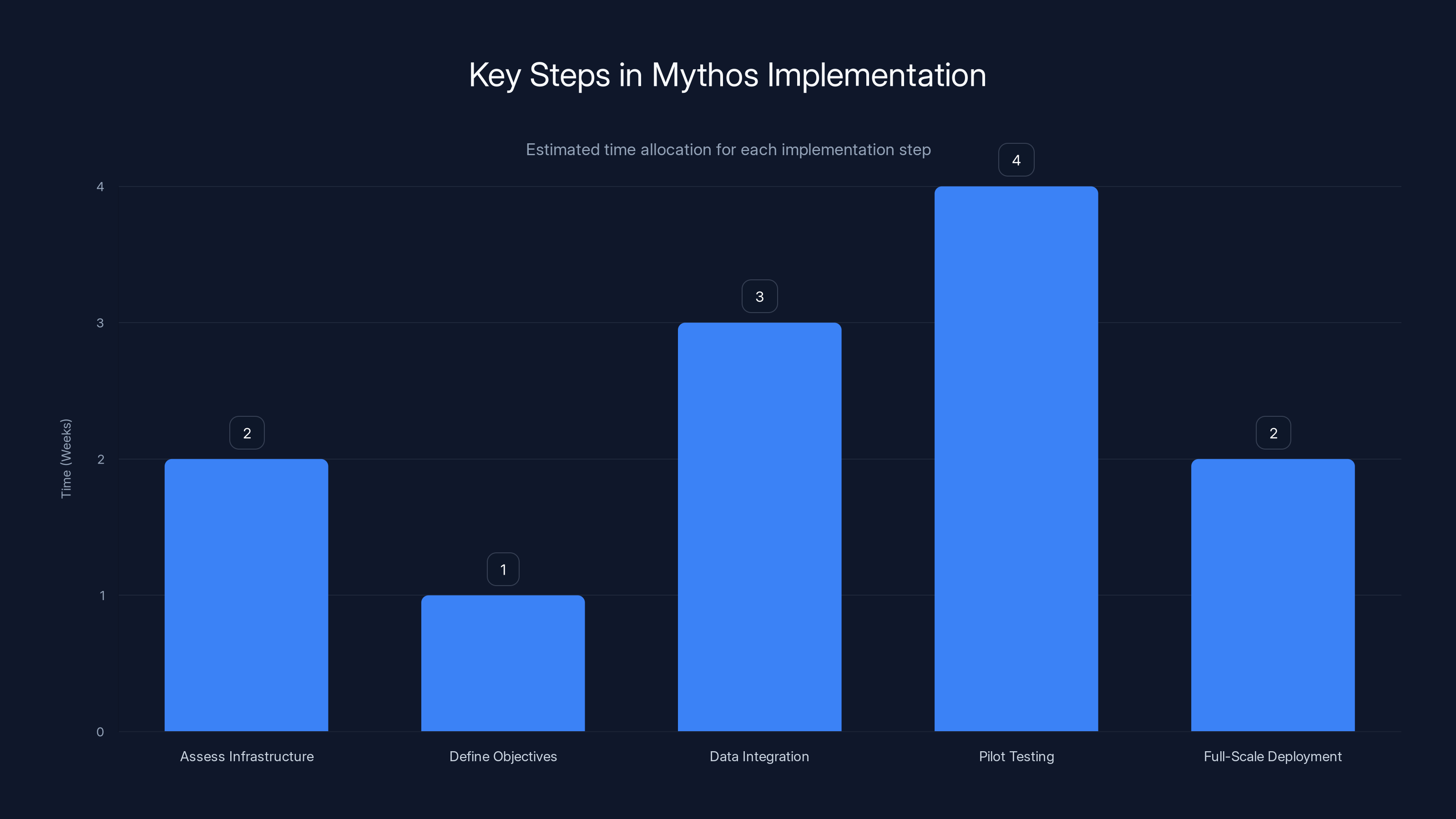
The implementation of Mythos involves several key steps, with pilot testing typically requiring the most time. Estimated data.
Future Trends in AI Cybersecurity
The integration of AI in cybersecurity is expected to grow, with models like Mythos leading the charge. Here are some trends to watch:
Trend 1: Increased Automation
AI will continue to automate more cybersecurity tasks, allowing human resources to focus on strategic decision-making.
Trend 2: Enhanced Collaboration
We can expect increased collaboration between AI models and human experts, leading to more effective threat identification and response.
Trend 3: AI-Driven Threat Intelligence
AI will play a significant role in gathering and analyzing threat intelligence, providing organizations with actionable insights as projected by Fortune Business Insights.

Best Practices for AI Cybersecurity Models
To maximize the effectiveness of AI models in cybersecurity, organizations should adhere to the following best practices:
Use of Diverse Data Sets
Ensure AI models have access to diverse and comprehensive data sets to improve threat detection accuracy.
Continuous Training
Regularly update AI models with new data and scenarios to maintain their effectiveness against evolving threats.
Human-AI Collaboration
Foster collaboration between AI systems and cybersecurity professionals to leverage the strengths of both.
Ethical Considerations
Address ethical concerns regarding AI in security, such as privacy and bias, to maintain public trust.
Conclusion
Anthropic's Mythos represents a significant advancement in cybersecurity technology. By leveraging AI, Mythos can help organizations detect and mitigate threats more effectively than ever before. While its current exclusivity raises questions, the model's potential impact on the industry is undeniable. As AI continues to evolve, its integration into cybersecurity will likely become more widespread, setting new standards for protection and efficiency as noted by Anthropic.
Use Case: Automate your cybersecurity threat detection and response with the power of AI.
Try Runable For Free
FAQ
What is Anthropic's Mythos?
Mythos is a cybersecurity AI model developed by Anthropic, designed to detect, analyze, and respond to cyber threats in real-time.
How does Mythos work?
Mythos utilizes advanced machine learning algorithms to process vast amounts of data, identifying patterns and behaviors indicative of cyber threats.
Who can access Mythos?
Currently, access to Mythos is limited to select organizations, including major tech companies like Amazon and Microsoft as reported by Fortune.
What are the benefits of using Mythos?
Benefits include real-time threat detection, adaptive learning for evolving threats, and automated response mechanisms.
What are some common pitfalls in implementing AI cybersecurity models?
Common pitfalls include inadequate data, misalignment with security goals, and overreliance on automation.
How can organizations ensure the success of AI models like Mythos?
Success can be ensured through continuous training, diverse data sets, and fostering collaboration between AI and human experts.

Key Takeaways
- Mythos is a groundbreaking AI model designed to revolutionize cybersecurity.
- Access is limited to select organizations, including major tech companies.
- Anthropic aims to address security vulnerabilities through advanced AI.
- The model's exclusivity raises questions about its potential impact.
- Future trends suggest broader AI integration into cybersecurity.
- AI will continue to automate more cybersecurity tasks.
- Increased collaboration between AI models and human experts is expected.
- Ethical considerations are crucial for maintaining public trust in AI systems.
Related Articles
- Investing in AI Startups: Why the 'AI Shift' Makes 2025 a Prime Time for New Ventures
- 5 Key Insights from Samsara's Reacceleration to $1.9 Billion in ARR [2025]
- Why 800VDC is the Emergent Electrical Backbone of Next-Generation Data Centers [2025]
- Men Are Buying Hacking Tools to Use Against Their Wives and Friends | WIRED
- How Ikea's New Smart Home Lineup is Quietly Revolutionizing Home Automation [2025]
- Unveiling the Blink Mini 2K+: Affordable High-Resolution Security for Modern Homes [2025]
![Understanding Anthropic's Mythos AI Model: A New Era in Cybersecurity [2025]](https://tryrunable.com/blog/understanding-anthropic-s-mythos-ai-model-a-new-era-in-cyber/image-1-1775657085655.jpg)



