The Complex World of Data Breaches: Lessons from the Rockstar Games Leak [2025]
Data breaches have become a persistent threat in our increasingly digital world. The recent incident involving Rockstar Games, where 78.6 million records were leaked, highlights the vulnerabilities even the most secure organizations face. This article delves into the intricacies of data breaches, using the Rockstar Games leak as a case study to explore causes, impacts, prevention strategies, and future trends in cybersecurity.
TL; DR
- Massive Leak: 78.6 million records from Rockstar Games were leaked, showing vulnerabilities in security systems.
- No Game Secrets: Despite the scale, no major game secrets were exposed.
- Business Data at Risk: Leaked data included sensitive business and financial information.
- Prevention Strategies: Implement strong access controls and regular security audits to mitigate risks.
- Future Trends: Expect more sophisticated attacks and increased investment in AI-driven security measures.

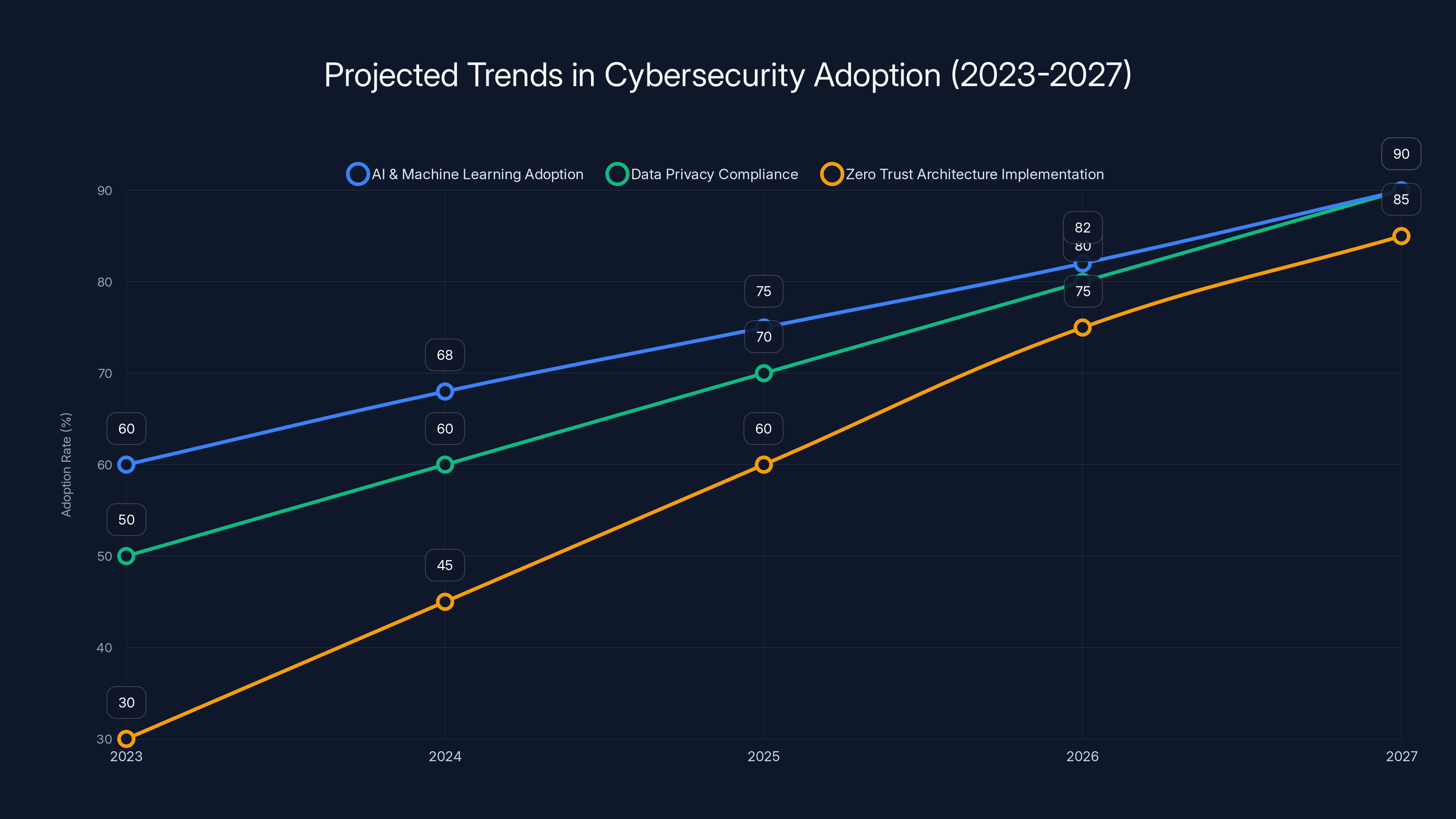
AI and machine learning, data privacy compliance, and Zero Trust architecture are projected to see significant adoption increases by 2027. (Estimated data)
Understanding Data Breaches
Data breaches occur when unauthorized individuals gain access to private data. This can involve anything from personal information to business secrets. The Rockstar Games incident is a classic example, where hackers managed to exfiltrate a vast amount of data, raising concerns over data security protocols.
What Happened?
In the Rockstar Games breach, hackers identified as Shiny Hunters released 78.6 million records. These records primarily contained business and financial data, not the game secrets many expected. This underscores a critical aspect of data breaches: the anticipation of sensitive information being leaked is sometimes more damaging than the leak itself.
Common Causes of Data Breaches
- Weak Passwords: Often, breaches start with something as simple as weak passwords. Ensure all access points use complex, unique passwords.
- Phishing Attacks: Employees can inadvertently give hackers access by falling for phishing attacks. Regular training and awareness programs are crucial.
- Vulnerabilities in Software: Unpatched software can be exploited to gain unauthorized access. Regular updates and patch management are essential.
- Insider Threats: Sometimes, breaches occur due to malicious or negligent insiders. Implementing strict access controls and monitoring can help mitigate this risk.
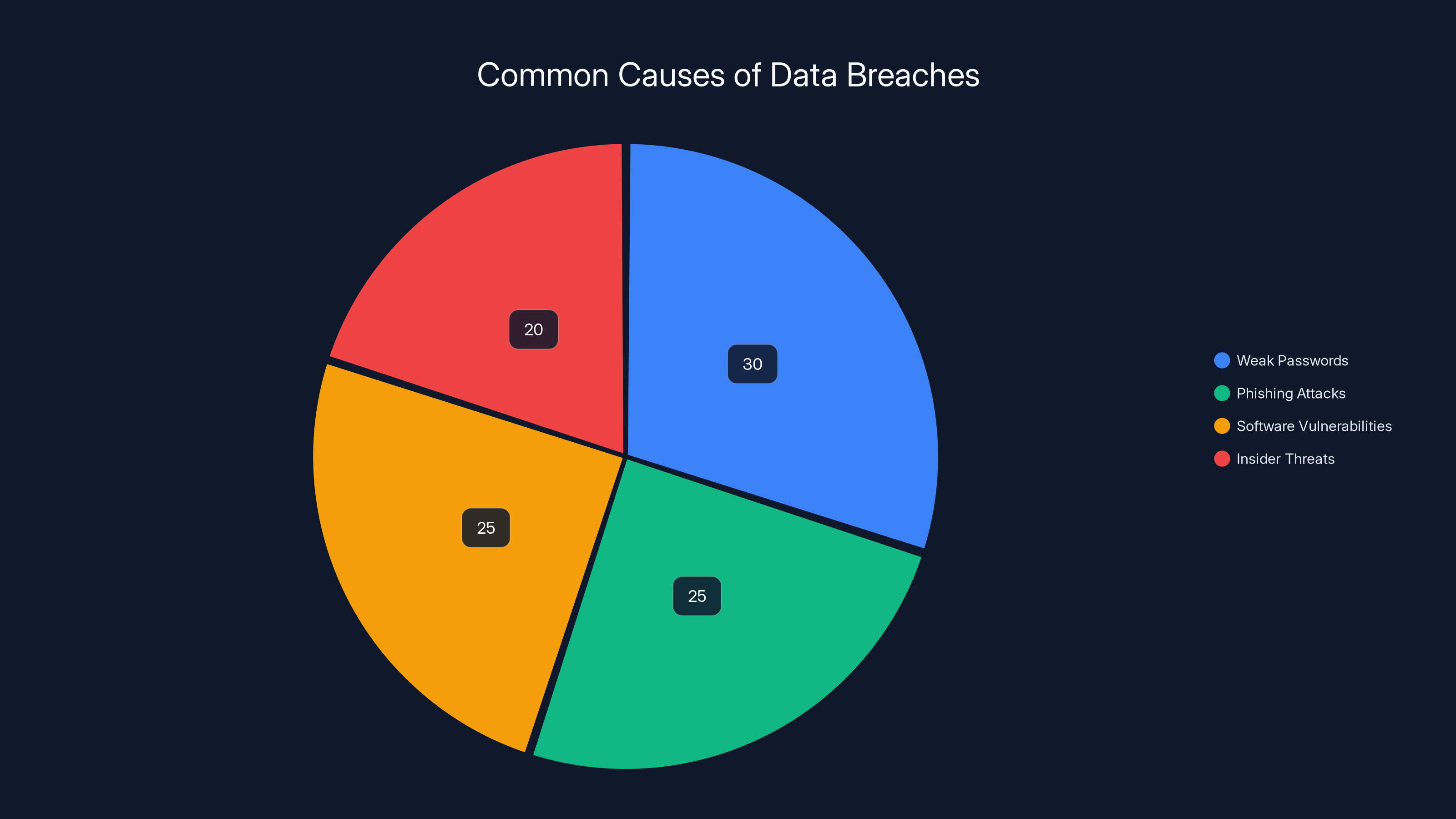
Weak passwords and phishing attacks are leading causes of data breaches, each contributing significantly to security incidents. Estimated data based on industry insights.
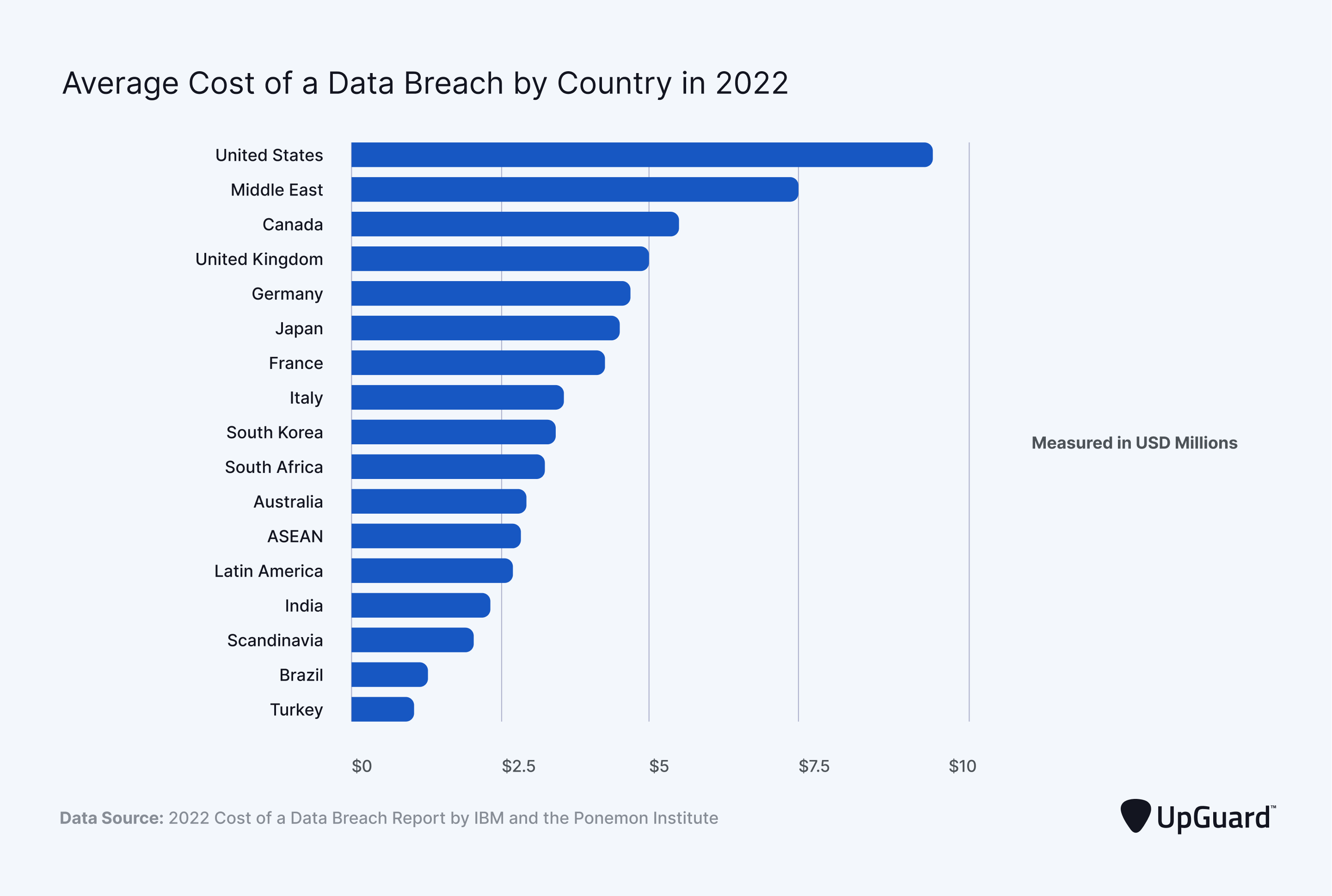
The Fallout from Rockstar's Leak
While no game secrets were revealed, the leak of business and financial data can lead to significant consequences. Competitors might gain insights into Rockstar's operations, while the company could face financial penalties and reputational damage.
Business Impact
- Financial Losses: Potential lawsuits and fines from regulatory bodies can result in substantial financial impact.
- Reputation Damage: Trust with partners and customers can erode, affecting future business opportunities.
- Operational Disruption: The immediate aftermath often requires resources to be diverted to damage control rather than business operations.
Best Practices for Data Security
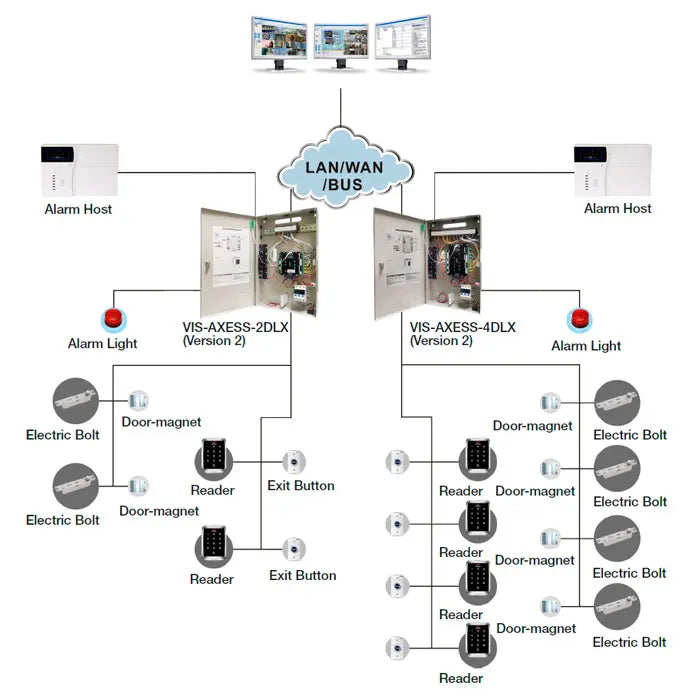
Implementing Strong Access Controls
One of the most effective ways to prevent data breaches is through robust access controls. This involves ensuring that only authorized individuals have access to sensitive data and that access is regularly reviewed and updated.
Steps to Implement Access Controls:
- Role-Based Access: Assign access based on roles within the organization to ensure only necessary data is accessible.
- Multi-Factor Authentication (MFA): Implement MFA to add an extra layer of security.
- Regular Audits: Conduct regular audits to ensure compliance with access policies.
Regular Security Audits and Penetration Testing
Conducting regular security audits and penetration testing helps identify vulnerabilities before they can be exploited. This proactive approach can save organizations from potential breaches.
Audit and Testing Steps:
- Internal Audits: Regularly review internal processes and access logs.
- External Testing: Hire ethical hackers to test the system's vulnerabilities.
- Continuous Monitoring: Implement systems to continuously monitor for suspicious activities.
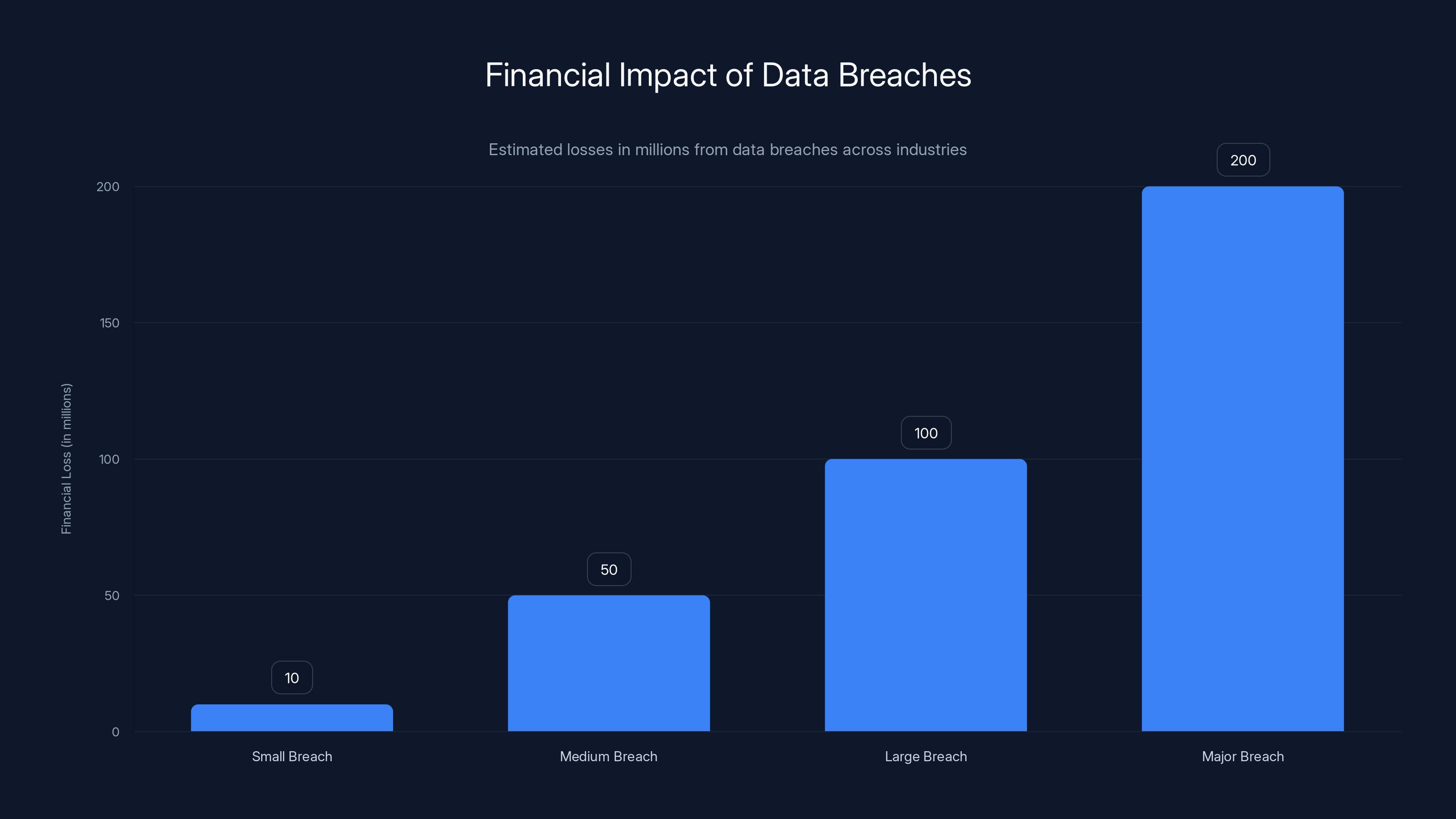
Estimated data shows that larger data breaches can lead to significantly higher financial losses, potentially reaching up to $200 million.
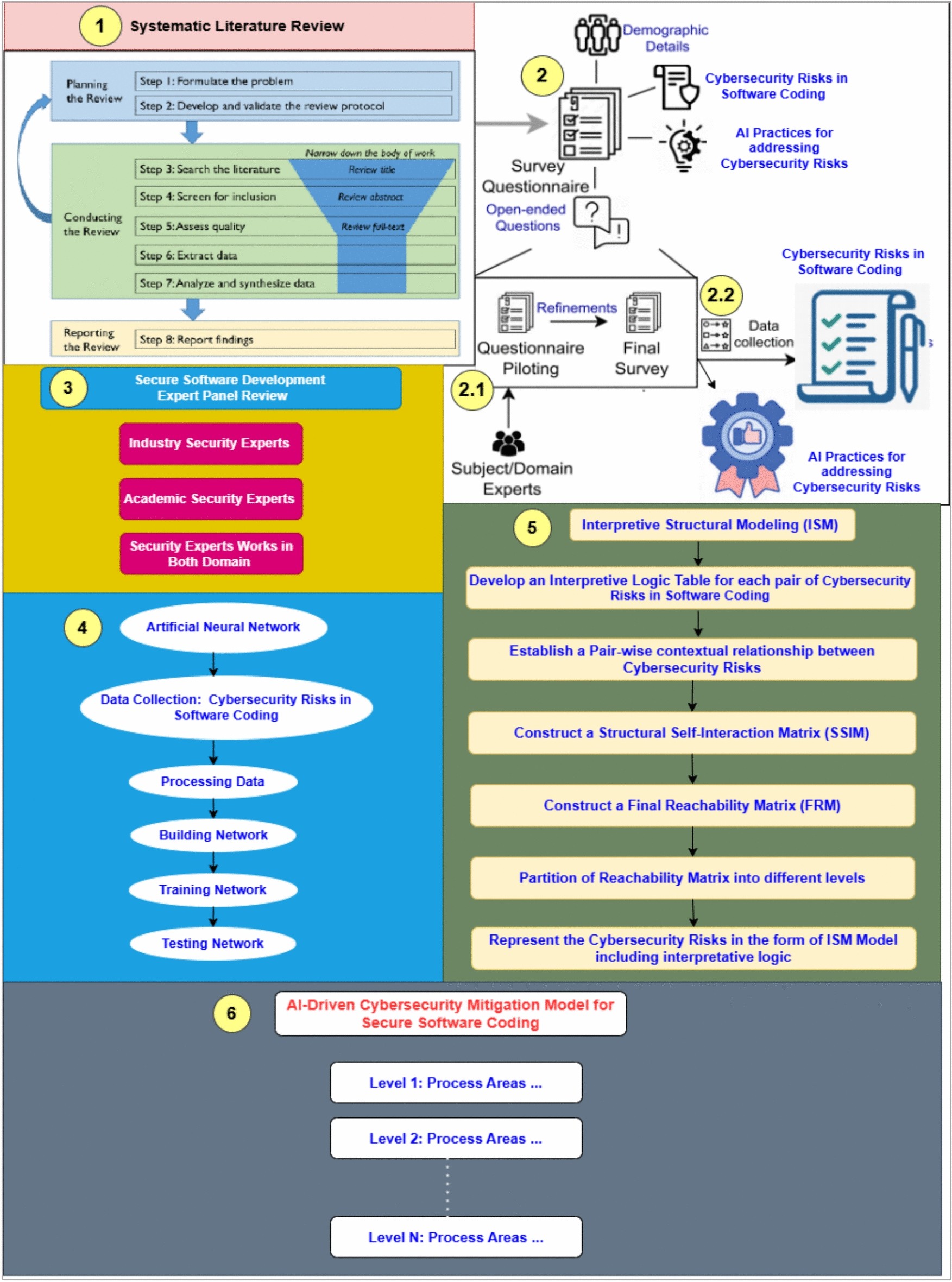
The Role of AI in Cybersecurity
Artificial intelligence is revolutionizing cybersecurity by enabling faster detection of threats and automating responses. AI can analyze patterns and detect anomalies that might indicate a breach.
AI-Powered Security Systems
- Threat Detection: AI systems can quickly identify and mitigate threats in real-time.
- Automated Response: AI can automate responses to common threats, reducing the time to neutralize them.
- Predictive Analysis: By analyzing data patterns, AI can predict potential threats before they occur.
Common Pitfalls in Data Security
While implementing security measures is crucial, it's equally important to avoid common pitfalls that can undermine these efforts.
Pitfall 1: Over-reliance on Technology
Technology is a powerful tool, but over-reliance without human oversight can lead to complacency. Regular human review and intervention are necessary.
Pitfall 2: Neglecting Employee Training
Employing the best technology is futile if employees are not trained to recognize and respond to security threats. Regular training sessions should be mandatory.
Pitfall 3: Ignoring Small Threats
Small vulnerabilities can lead to major breaches. Organizations must address all potential threats, no matter how insignificant they seem.
Future Trends in Cybersecurity
The landscape of cybersecurity is continuously evolving, and staying ahead of trends is crucial for staying secure.
Increased Use of AI and Machine Learning
AI and machine learning will continue to play a critical role in enhancing cybersecurity measures, making threat detection faster and more accurate.
Greater Emphasis on Data Privacy
With increasing regulatory requirements, organizations will need to prioritize data privacy and ensure compliance to avoid hefty penalties.
Rise of Zero Trust Architecture
Zero Trust is a security framework that requires all users, whether inside or outside the organization, to be authenticated and authorized before accessing data.
Case Study: Implementing a Zero Trust Model
A leading tech company recently adopted a Zero Trust model to enhance its security posture. This involved re-architecting their networks to ensure that no resource was inherently trusted.
Steps Taken
- Network Segmentation: Divided the network into smaller, isolated segments to limit access.
- Continuous Monitoring: Implemented systems to monitor all network traffic and user activities continuously.
- Strict Access Controls: Enforced strict access controls and regularly updated them based on user roles and activities.
The result was a significant reduction in potential attack vectors and improved detection and response times.
Conclusion: Preparing for the Future
The Rockstar Games breach serves as a stark reminder of the importance of robust security measures. While no system is completely immune, implementing best practices and staying informed of trends can significantly mitigate risks.
Use Case: Automate security logs review and anomaly detection with AI to enhance your cybersecurity posture.
Try Runable For Free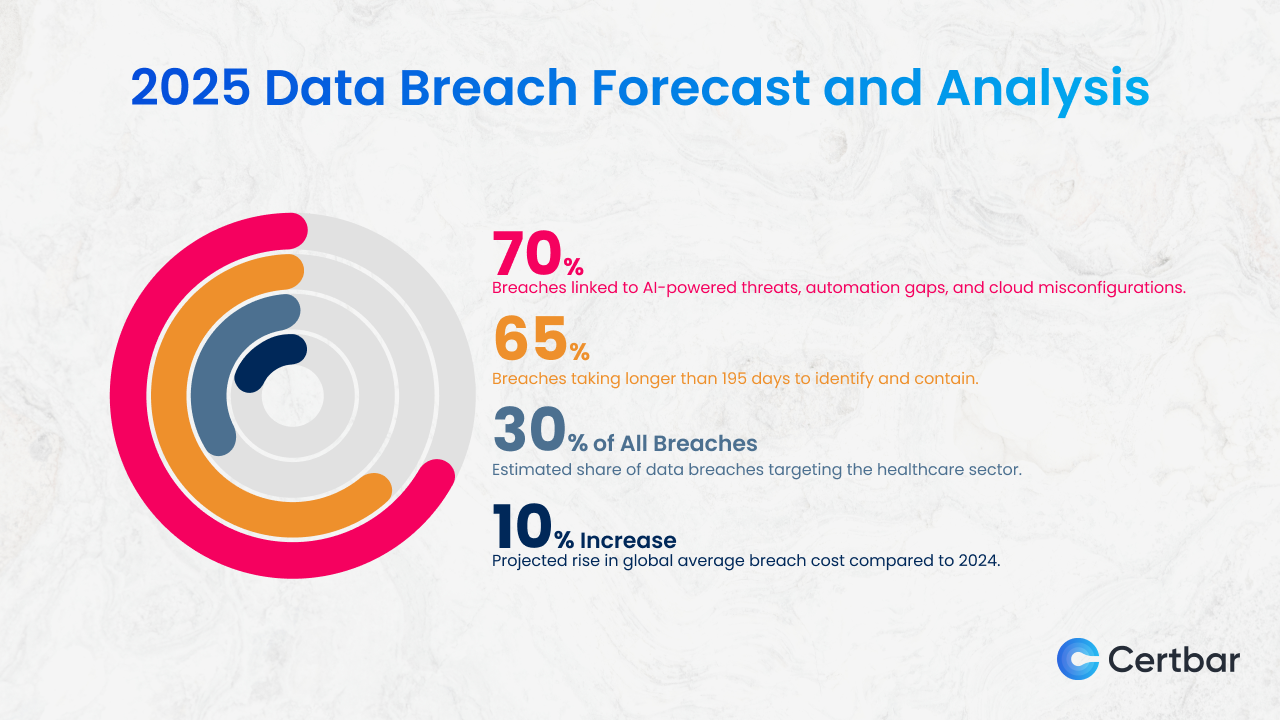
FAQ
What is a data breach?
A data breach occurs when unauthorized individuals access private data, potentially leading to financial losses and reputational damage.
How does AI help in cybersecurity?
AI enhances cybersecurity by enabling faster threat detection, automating responses, and predicting potential threats through data analysis.
What are the benefits of Zero Trust architecture?
Zero Trust architecture increases security by ensuring that all users are authenticated and authorized before accessing data, reducing potential attack vectors.
How can companies prevent data breaches?
Companies can prevent data breaches by implementing strong access controls, conducting regular security audits, and providing ongoing employee training.
What are the future trends in cybersecurity?
Future trends include increased use of AI, greater emphasis on data privacy, and the rise of Zero Trust architecture to enhance security measures.
Key Takeaways
- Data breaches expose vulnerabilities in security systems, as seen with Rockstar Games.
- Business data leaks can lead to financial and reputational damage.
- Implementing strong access controls and regular audits is crucial for data security.
- AI-driven security systems are becoming essential for threat detection and response.
- Future trends include AI in cybersecurity, Zero Trust architecture, and increased data privacy focus.
Related Articles
- Tech Support Scams and How to Combat Them [2025]
- The Future of Leadership: Mark Zuckerberg's AI Clone and Its Implications [2025]
- Five Signs Data Drift is Undermining Your Security Models [2025]
- Governing Generative AI Risks in the Enterprise [2025]
- The Claude Code Plugin: Unveiling Data Collection in Non-Vercel Projects [2025]
- Understanding the NZXT Flex PC Settlement and Its Implications [2025]
![The Complex World of Data Breaches: Lessons from the Rockstar Games Leak [2025]](https://tryrunable.com/blog/the-complex-world-of-data-breaches-lessons-from-the-rockstar/image-1-1776162839232.jpg)



