The Curious Case of the Trump Phone: Unraveling the Mystique [2025]
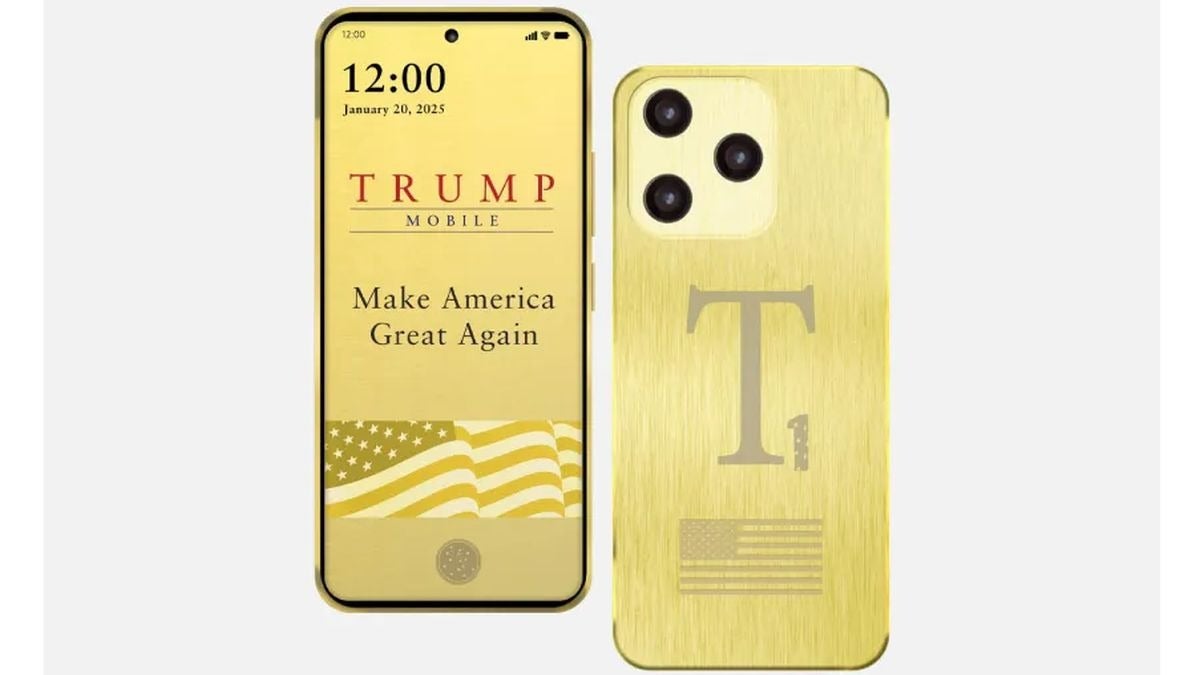
In recent years, the tech world has been abuzz with rumors and speculations about a device colloquially termed the "Trump Phone." This elusive gadget, shrouded in mystery and intrigue, has sparked debates across tech forums and political arenas alike. But what exactly is the Trump Phone, and why does it captivate our imagination? Let's delve into the heart of this technological enigma, exploring its origins, implications, and what it might mean for the future of communication technology.
TL; DR
- The Trump Phone is a rumored device linked to former President Trump, sparking privacy and security debates.
- Its existence highlights the growing intersection of politics and technology.
- Potential features could redefine secure communications.
- Challenges include encryption, data privacy, and ethical implications.
- Future tech trends may see a rise in personalized secure communication devices.

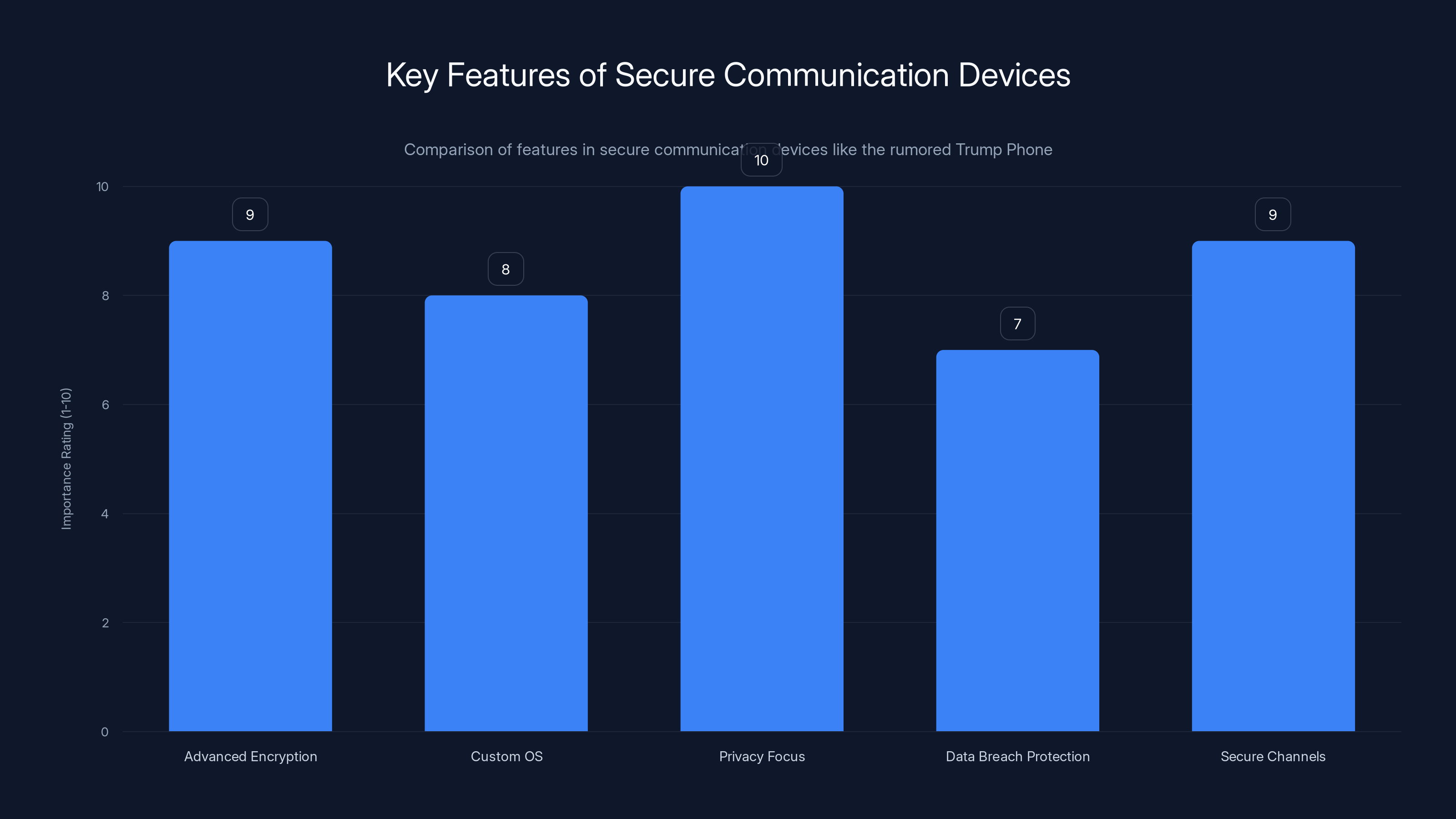
The chart highlights the estimated importance of various features in secure communication devices, emphasizing privacy and encryption. Estimated data.
The Origin Story: Fact or Fiction?
The story of the Trump Phone begins with whispers in the corridors of power and speculation from tech insiders. It is rumored that this device was developed to provide secure communication for high-profile individuals, particularly during the Trump administration. While the existence of such a phone has never been officially confirmed, its legend persists, fueled by occasional leaks and anecdotal accounts.
What Makes the Trump Phone Unique?
The allure of the Trump Phone lies in its purported features, which focus heavily on security and privacy. In an era where data breaches and surveillance are rampant, a device promising unbreakable encryption and anonymous communication is tantalizing.
- End-to-End Encryption: Unlike standard smartphones, the Trump Phone allegedly employs advanced encryption to secure messages and calls, making interception nearly impossible. This aligns with the growing demand for enhanced phone security.
- Customized Operating System: The device is rumored to run on a proprietary OS, built from the ground up to resist hacking attempts and prevent unauthorized data access.
- Signal Jamming Capabilities: Some reports suggest it can disable nearby recording devices, further enhancing privacy.
The Technological Backbone
At the core of any secure device is its technology stack. While specifics about the Trump Phone remain speculative, we can infer potential technologies it might employ based on current security trends.
- Quantum Cryptography: Leveraging quantum mechanics to develop cryptographic keys that are theoretically unhackable, as demonstrated in recent quantum breakthroughs.
- Blockchain Integration: Utilizing blockchain technology to decentralize and secure data, preventing unauthorized tampering, which is becoming increasingly relevant in healthcare and other sectors.
- Biometric Authentication: Advanced biometric systems for user identification, such as facial recognition and fingerprint scanning, are crucial in modern secure devices.
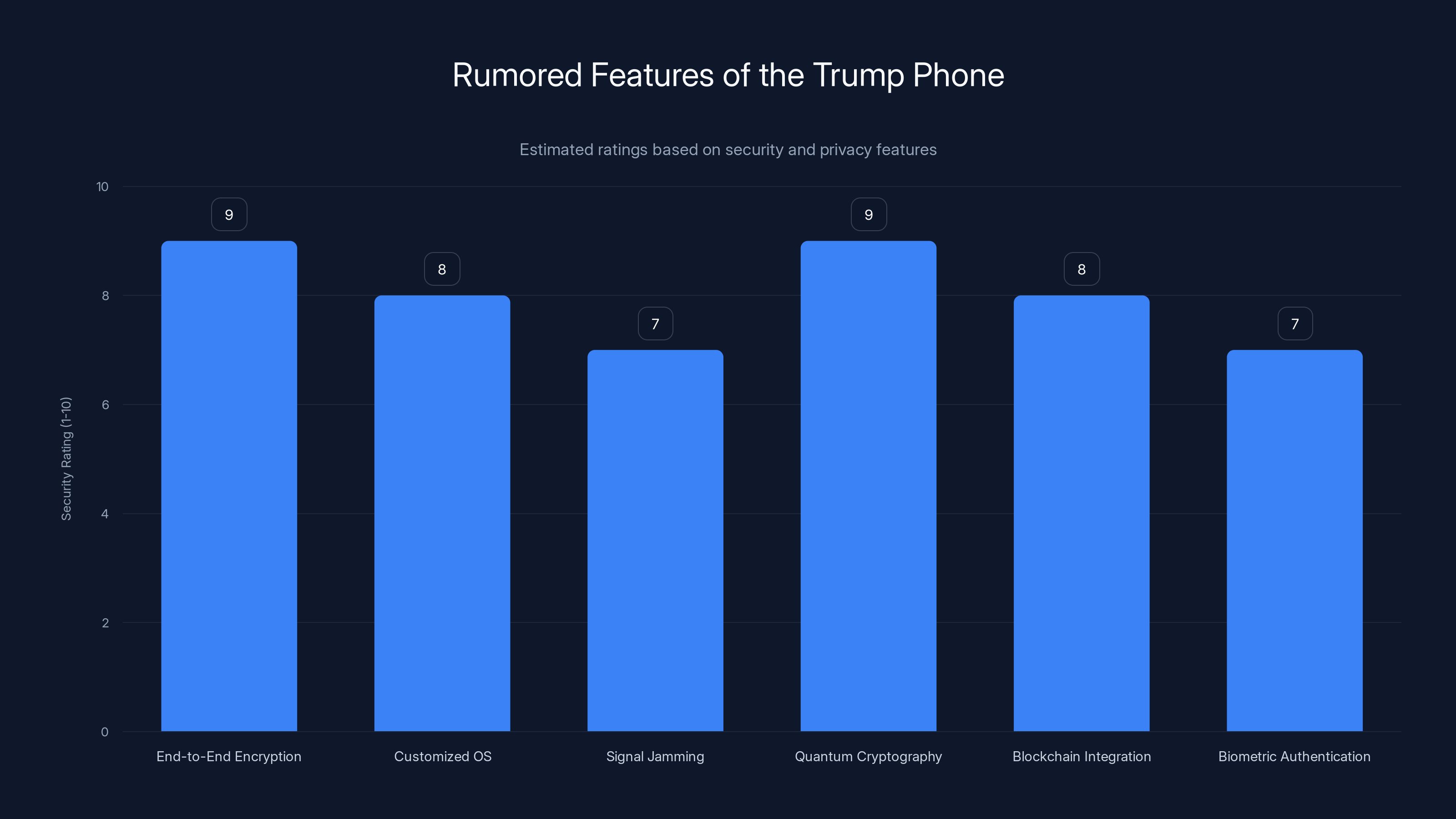
The Trump Phone is speculated to have high security ratings across various features, with end-to-end encryption and quantum cryptography leading the pack. (Estimated data)
Privacy vs. Convenience: A Delicate Balance
The Trump Phone raises important questions about the balance between privacy and convenience. In a world where smartphones are an integral part of daily life, adding layers of security often comes at the cost of user experience.
- User Interface Challenges: Secure devices can suffer from clunky interfaces that prioritize security over ease of use.
- App Compatibility: Custom operating systems may not support popular apps, limiting functionality.
Implementation Guide: Building a Secure Communication Device
Creating a device like the Trump Phone involves addressing several technical and ethical challenges. Here's a step-by-step guide for developers and tech innovators:
- Define Security Protocols: Outline the encryption standards and privacy measures needed.
- Select Hardware Components: Choose components that support advanced security features, such as secure processing units.
- Develop a Custom OS: Build an operating system focused on security, with regular updates to patch vulnerabilities.
- Test for Vulnerabilities: Conduct extensive penetration testing to identify and fix potential security loopholes.
- Ensure Compliance: Adhere to international data protection laws and industry standards, as highlighted in recent healthcare industry discussions.

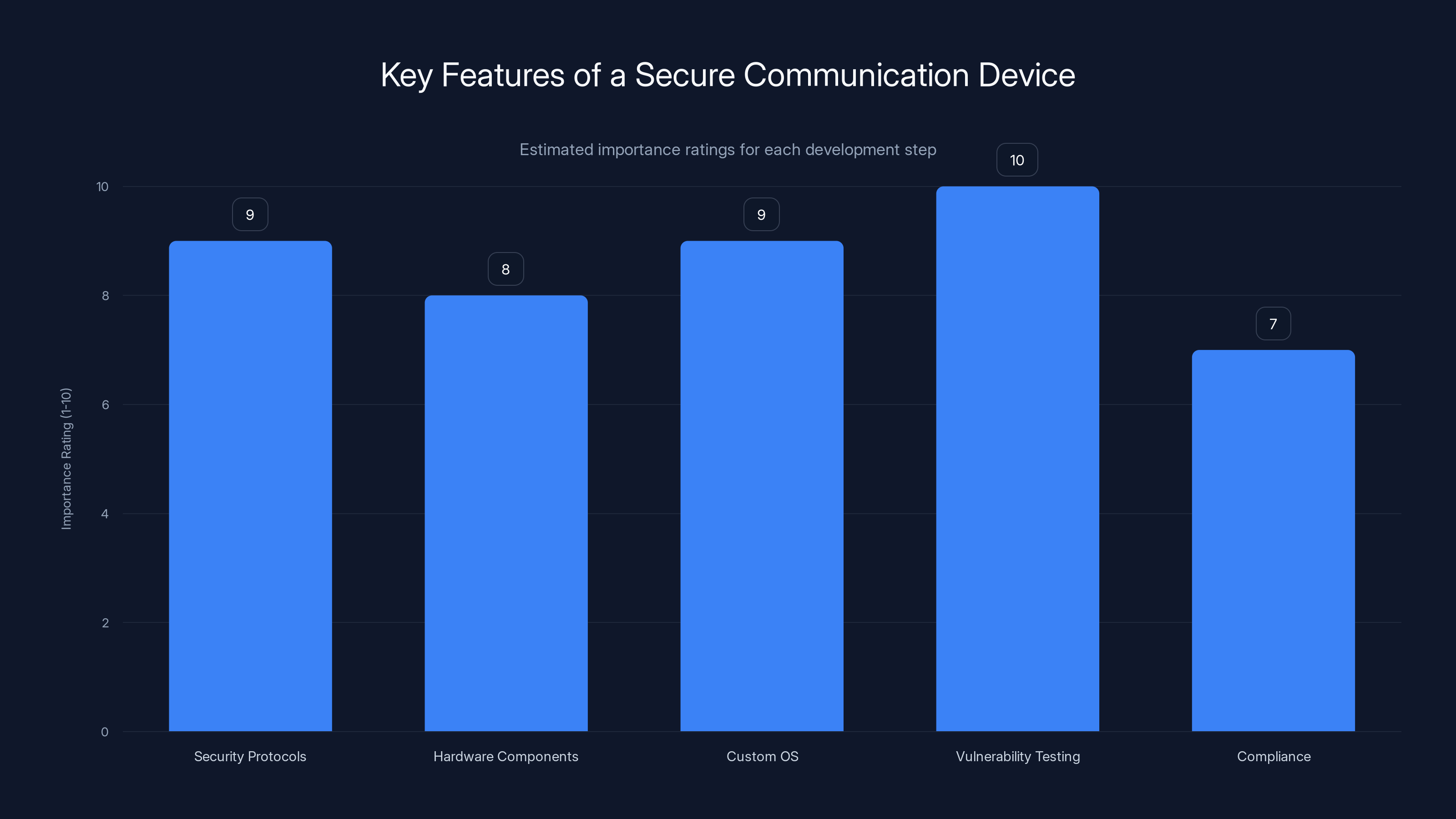
Vulnerability testing is crucial, rated highest in importance for building a secure communication device. Estimated data.
Potential Pitfalls and Solutions
Security-focused devices face unique challenges, and the Trump Phone is no exception. Here are some common pitfalls and how to address them:
- Over-Promising Security: Avoid making claims that can't be backed by technology. Transparency is key.
- Regular Updates: Security is not static; frequent updates are necessary to combat new threats.
- User Education: Educate users on best practices for maintaining device security to minimize human error, as over 90% of breaches are due to human error.
The Political Intersection
The Trump Phone is more than just a technological curiosity; it's a symbol of the increasing overlap between politics and technology. As high-profile individuals become more reliant on digital communication, the demand for secure, tamper-proof devices will only grow.
Implications for National Security
Devices like the Trump Phone could play a crucial role in national security, providing secure lines of communication that are immune to foreign interception. This is particularly relevant given the ongoing surveillance debates.
- Secure Diplomatic Communication: Ensuring that sensitive conversations remain confidential.
- Preventing Data Leaks: Protecting national secrets from adversaries.

Future Trends: What Lies Ahead?
The concept of a secure, personalized communication device is likely to gain traction. Here are some trends we might see in the coming years:
- Increased Demand for Privacy: As awareness of digital privacy grows, so will the demand for secure devices.
- Advancements in AI: AI could play a significant role in enhancing device security, from anomaly detection to adaptive encryption.
- Integration with Io T: Secure devices could extend their protection to connected Io T devices, creating a secure ecosystem, as noted in recent developments in post-quantum security.
Conclusion: A Real or Imagined Innovation?
While the Trump Phone remains a topic of speculation, its underlying concepts highlight significant advancements in secure communication technology. Whether real or imagined, it prompts us to consider the future of privacy and security in our increasingly connected world.
FAQ
What is the Trump Phone?
The Trump Phone is a rumored secure communication device linked to former President Trump, known for its focus on privacy and security.
How does the Trump Phone work?
The device reportedly uses advanced encryption, a custom operating system, and other security features to safeguard communications.
What are the benefits of the Trump Phone?
Benefits include enhanced privacy, protection against data breaches, and secure communication channels.
Is the Trump Phone real?
While there is no official confirmation, the concept highlights important trends in secure communication technology.
What are the challenges of creating secure phones?
Challenges include balancing security with usability, ensuring app compatibility, and maintaining regular security updates.
What future trends can we expect for secure devices?
Expect increased demand for privacy, AI integration, and broader Io T security measures.
How does politics influence tech innovation?
Political needs often drive tech advancements, especially in areas like national security and privacy.
Can secure devices prevent all data breaches?
While they enhance security, no device can guarantee complete protection against all threats.

Key Takeaways
- The Trump Phone highlights the intersection of politics and technology.
- Advanced encryption and custom OS are key features of secure devices.
- Balancing privacy with usability is a major challenge in device design.
- Future trends include AI integration and increased privacy demands.
- Secure communication devices could play a significant role in national security.
Related Articles
- The Journey Back to Smartphones: A New Chapter for AR Veterans [2025]
- Tim Cook's Warning: Rising Memory Costs and Potential Mac Price Hikes [2025]
- The Unprecedented Growth of AWS and the Future of AI in Cloud Computing [2025]
- Top Tech of the Month: The Best New Gadgets We've Tested for May 2026
- Why Encryption Breaking is 20x Cheaper and What CEOs Need to Do [2025]
- Apple's Record Sales Amidst Leadership Change and Looming Chip Shortage [2025]
![The Curious Case of the Trump Phone: Unraveling the Mystique [2025]](https://tryrunable.com/blog/the-curious-case-of-the-trump-phone-unraveling-the-mystique-/image-1-1777653257433.jpg)



