The Hidden Risks of Meta's Retreat from End-to-End Encryption on Instagram DMs
In the ever-evolving landscape of digital communication, privacy concerns have taken center stage. The decision by Meta to limit the deployment of end-to-end encryption (E2EE) on Instagram Direct Messages (DMs) has sparked widespread debate. This article delves into the implications of this decision, exploring the technical, legal, and ethical dimensions at play.
TL; DR
- Meta's decision: Limiting E2EE on Instagram DMs poses significant privacy risks, as reported by One World News.
- User privacy impact: Without E2EE, user data is vulnerable to unauthorized access, as highlighted by Fortune.
- Legal pressures: Government surveillance demands challenge tech companies' privacy commitments, according to the Electronic Frontier Foundation.
- Technical hurdles: Implementing E2EE involves complex technical challenges.
- Future trends: The debate over E2EE will shape the future of digital privacy.
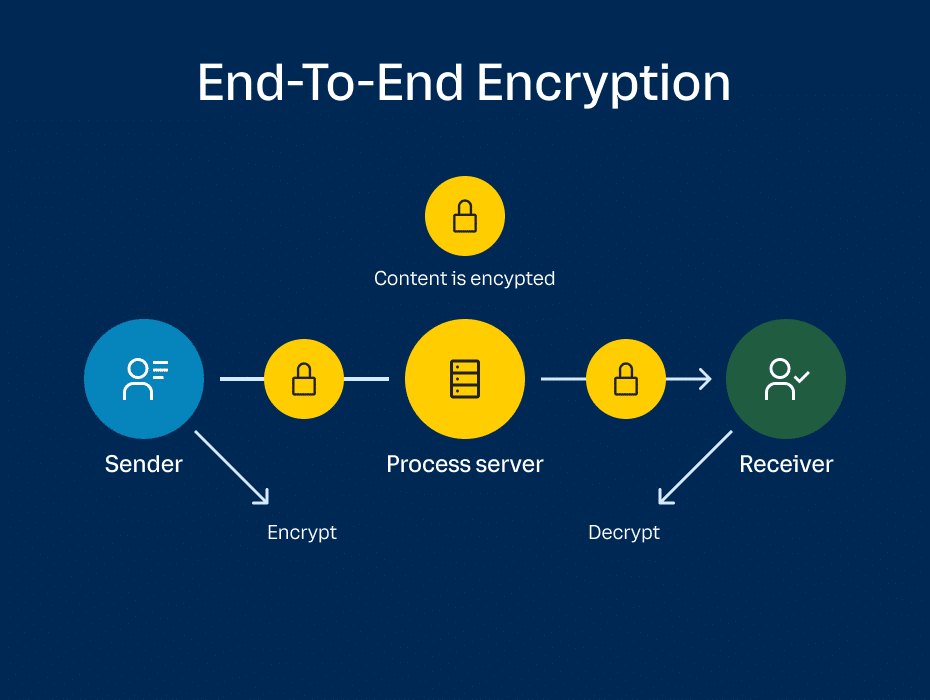
Understanding End-to-End Encryption
What is End-to-End Encryption?
End-to-end encryption is a method of securing communication where only the communicating users can read the messages. In E2EE, the message is encrypted on the sender’s device and only decrypted on the recipient’s device. This ensures that intermediaries, including service providers, cannot access the contents of the messages.
How Does E2EE Work?
E2EE relies on cryptographic keys, which are unique to each user. When a message is sent, it is encrypted using the recipient's public key and can only be decrypted by the recipient's private key.
- Public Key: Used to encrypt messages, widely shared.
- Private Key: Used to decrypt messages, kept secret.
This encryption method ensures that even if a message is intercepted, it cannot be read without the private key.

Meta's Decision: A Step Backward?
The Announcement
In December 2023, Meta announced that while its Messenger app would have E2EE by default, Instagram DMs would only support E2EE as an opt-in feature. This decision raised eyebrows given the heightened focus on user privacy and security, as noted by MSN.
The Implications
The absence of default E2EE on Instagram DMs means that conversations are susceptible to unauthorized access by hackers, third parties, or even Meta itself. This vulnerability is particularly concerning in a time when data breaches and digital surveillance are rampant, as highlighted by The Hacker News.

The Technical Challenges of Implementing E2EE
Complexity in Development
Implementing E2EE is not a straightforward task. It involves substantial technical challenges, including:
- Key Management: Securely generating, distributing, and storing cryptographic keys is complex, as discussed by Security Brief.
- Device Synchronization: Ensuring that encrypted messages are accessible across multiple devices adds complexity.
- Performance Overheads: E2EE can introduce latency and increase resource consumption.
Maintaining User Experience
Balancing security with user experience is critical. Users expect seamless communication without noticeable delays or increased complexity.
Legal and Ethical Considerations
Government Surveillance
Governments worldwide have been increasing pressure on tech companies to provide access to encrypted communications. This pressure often stems from national security concerns, such as combating terrorism or child exploitation, as reported by Reuters.
Ethical Dilemmas
Tech companies face ethical dilemmas when balancing user privacy with compliance with legal requests. The decision to limit E2EE could set a precedent, potentially weakening privacy standards across the industry.

Common Pitfalls and Solutions
Pitfalls in Implementing E2EE
- Inadequate Key Management: Poorly managed keys can lead to security breaches, as noted by CPO Magazine.
- User Misunderstanding: Users may not understand the importance of E2EE or how to enable it.
Solutions
- User Education: Educate users on the benefits and usage of E2EE.
- Robust Key Management: Implement strong key management practices to safeguard encryption keys.

The Future of Digital Privacy
Trends in Encryption
As digital communication continues to evolve, so too will the technologies that protect it. Future trends may include:
- Post-Quantum Cryptography: Developing encryption methods resistant to quantum computing threats.
- Zero-Knowledge Proofs: Ensuring privacy without sacrificing usability or performance.
The Role of Policy and Regulation
Policy and regulation will play a crucial role in shaping the future of digital privacy. Tech companies, policymakers, and privacy advocates must collaborate to establish standards that protect user privacy while accommodating legal requirements.

Recommendations for Users
How to Protect Your Privacy
- Enable E2EE: Opt-in for E2EE on platforms that offer it.
- Use Secure Messaging Apps: Prefer apps with a strong commitment to privacy and security, such as X-Chat.
- Stay Informed: Keep up with privacy developments and adjust your digital habits accordingly.
For Developers and Organizations
- Prioritize Security: Invest in secure development practices and regular audits.
- Advocate for Privacy: Support policies and initiatives that prioritize user privacy.

Conclusion
Meta's decision to limit E2EE on Instagram DMs highlights the ongoing tension between user privacy and security needs. As the digital landscape continues to evolve, it is crucial for both individuals and organizations to prioritize security and privacy. By understanding the technical challenges, legal pressures, and ethical considerations, we can better navigate this complex terrain and work towards a more secure digital future.

Key Takeaways
- Meta's decision to limit E2EE on Instagram DMs poses significant privacy risks.
- Without E2EE, user data is vulnerable to unauthorized access.
- Government surveillance demands challenge tech companies' privacy commitments.
- Implementing E2EE involves complex technical challenges.
- The debate over E2EE will shape the future of digital privacy.
- Users should enable E2EE and use secure messaging apps.
- Developers and organizations should prioritize security and advocate for privacy.
Related Articles
- NymVPN Turns One: Celebrating a Year of Growth and Future Innovations [2025]
- The Future of VPNs: ExpressVPN's Potential Shadowsocks Integration [2025]
- Russia's Intensified Crackdown on VPNs: Navigating Internet Restrictions in 2025
- Tech Giants Unveiled: NVIDIA’s $1T Vision, Meta’s Strategic Layoffs, and Adobe’s Leadership Shift [2025]
- Meta's AI Content Moderation Shift [2025]
- Meta Revives Horizon Worlds VR: A Strategic Pivot [2025]
FAQ
What is The Hidden Risks of Meta's Retreat from End-to-End Encryption on Instagram DMs [2025]?
In the ever-evolving landscape of digital communication, privacy concerns have taken center stage
What does tl; dr mean?
The decision by Meta to limit the deployment of end-to-end encryption (E2EE) on Instagram Direct Messages (DMs) has sparked widespread debate
Why is The Hidden Risks of Meta's Retreat from End-to-End Encryption on Instagram DMs [2025] important in 2025?
This article delves into the implications of this decision, exploring the technical, legal, and ethical dimensions at play
How can I get started with The Hidden Risks of Meta's Retreat from End-to-End Encryption on Instagram DMs [2025]?
- Meta's decision: Limiting E2EE on Instagram DMs poses significant privacy risks
What are the key benefits of The Hidden Risks of Meta's Retreat from End-to-End Encryption on Instagram DMs [2025]?
- User privacy impact: Without E2EE, user data is vulnerable to unauthorized access
What challenges should I expect?
- Legal pressures: Government surveillance demands challenge tech companies' privacy commitments
![The Hidden Risks of Meta's Retreat from End-to-End Encryption on Instagram DMs [2025]](https://tryrunable.com/blog/the-hidden-risks-of-meta-s-retreat-from-end-to-end-encryptio/image-1-1774002890906.jpg)



