The Massive Banks of Malware: Visualizing the Data Giants [2025]
In the realm of cybersecurity, malware is a formidable adversary. But have you ever wondered just how vast the digital landscape of malware really is? Imagine stacks of hard drives towering higher than the Eiffel Tower, each filled with malicious code. This isn't just a flight of fancy—it's the reality for some of the world's largest malware repositories, as detailed by TechCrunch.
TL; DR
- Vast Malware Repositories: Repositories like vx-underground and Virus Total hold up to 31 petabytes of malware data.
- Physical Visualization: A petabyte of data translates to thousands of hard drives; stacked, they could rival iconic structures.
- Role in Cybersecurity: These repositories are crucial for training AI models and enhancing threat intelligence.
- Practical Application: Understanding malware data helps improve detection systems and response strategies.
- Future Trends: Expect growth in data size and sophistication, emphasizing the need for advanced AI tools.
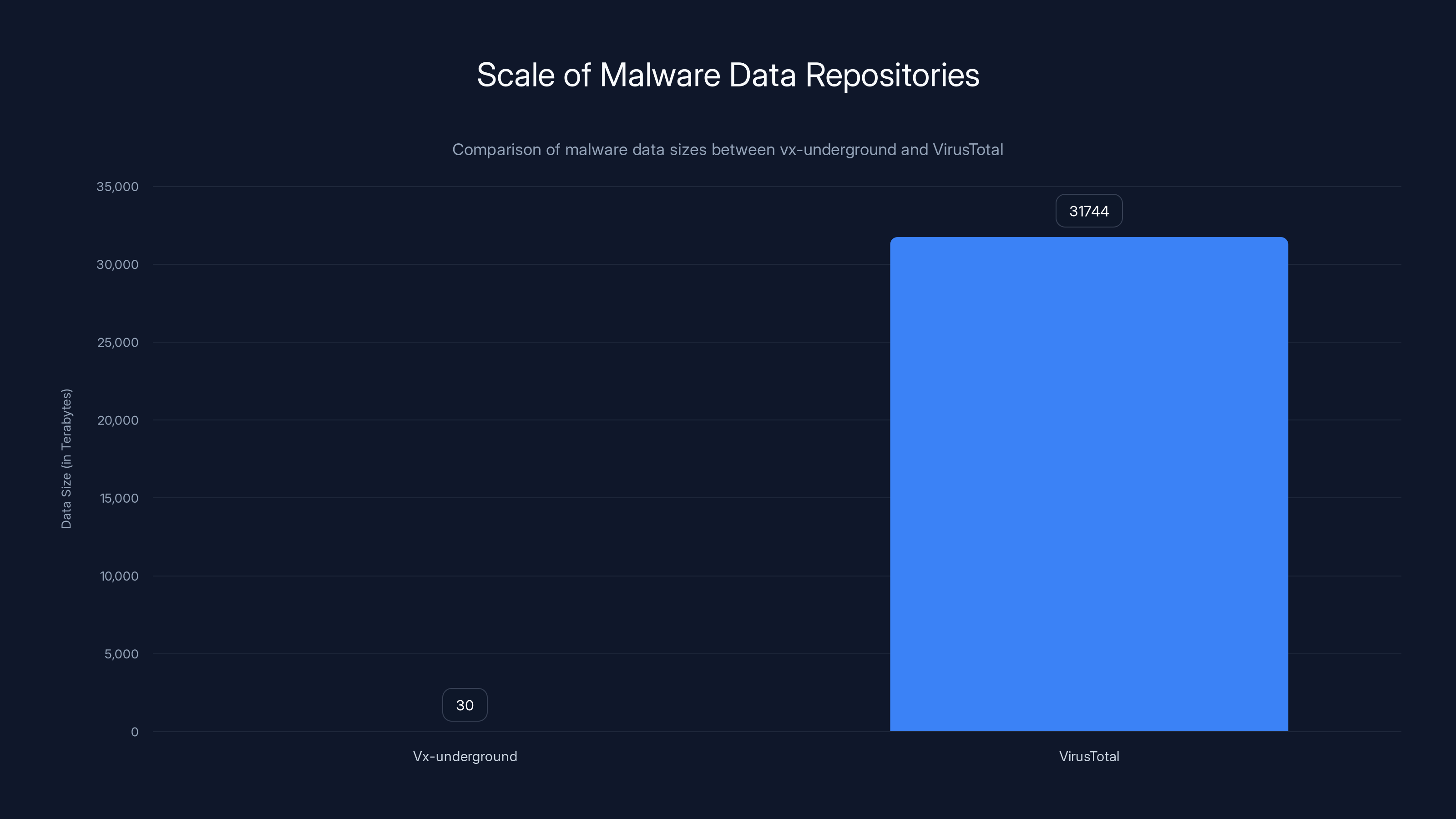
VirusTotal's malware data repository is significantly larger, holding over 31,000 terabytes compared to vx-underground's 30 terabytes.
Introduction
Malware—it's the digital thorn in our side, continuously evolving and adapting to outsmart even the most robust defenses. As cybersecurity warriors, researchers, and tech enthusiasts, understanding the scale of malware data can provide insights into the battle we're facing. Let's dive into the colossal world of malware databases and explore their implications for cybersecurity.
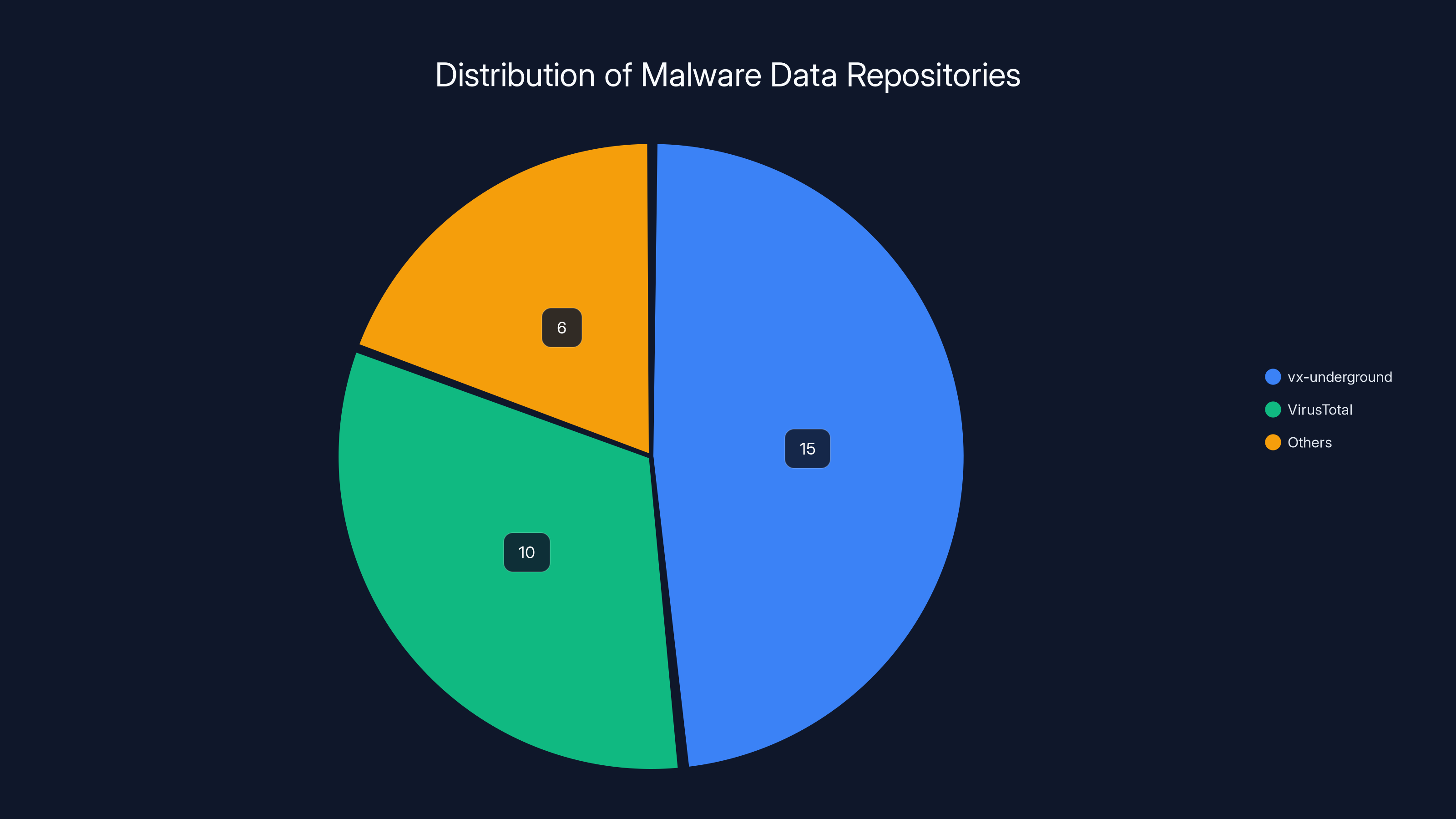
Estimated data shows vx-underground and VirusTotal holding the majority of malware data, crucial for AI model training and threat intelligence.
The Sheer Scale of Malware Data
How Big is Big?
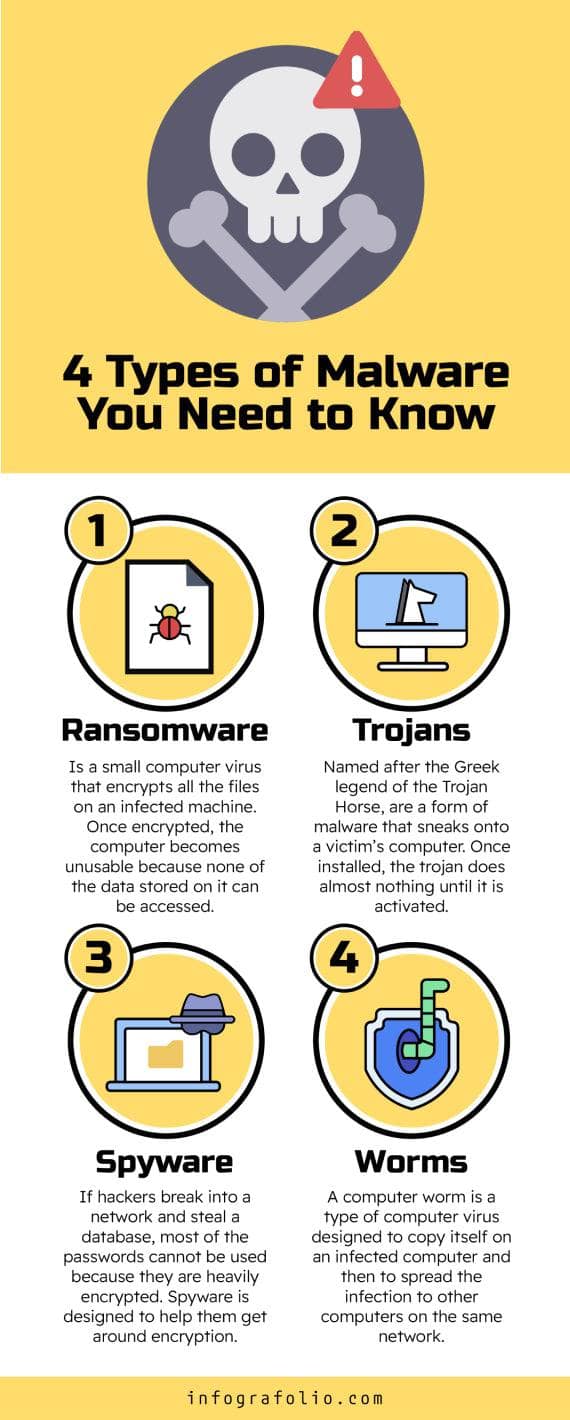
When we talk about malware data, we're referring to vast collections of files that contain malicious code. These can include everything from simple scripts to complex, multi-layered attacks. Organizations like vx-underground and Virus Total manage some of the largest repositories of such data.
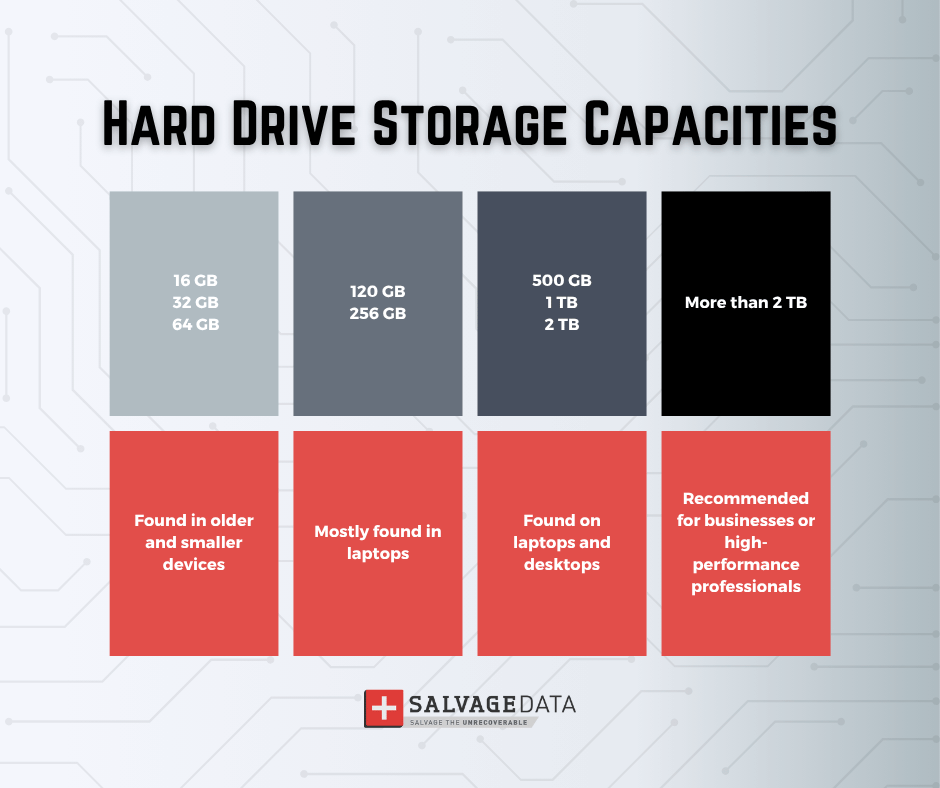
Vx-underground boasts a collection of approximately 30 terabytes of malware source code. In contrast, Virus Total's archive dwarfs this, holding about 31 petabytes of malware samples. To put it in perspective, a petabyte is equivalent to 1,024 terabytes.
Visualizing the Data as Hard Drives
Consider this: a single terabyte hard drive is about the size of a paperback book. Now, imagine stacking these books until they reach the height of the Eiffel Tower. For vx-underground's 30 terabytes, that's like stacking 30 of these paperbacks. But for Virus Total's 31 petabytes, you'd need over 31,000 such stacks. It's a staggering thought, as highlighted by PCWorld.
Why These Repositories Matter
Training AI Models
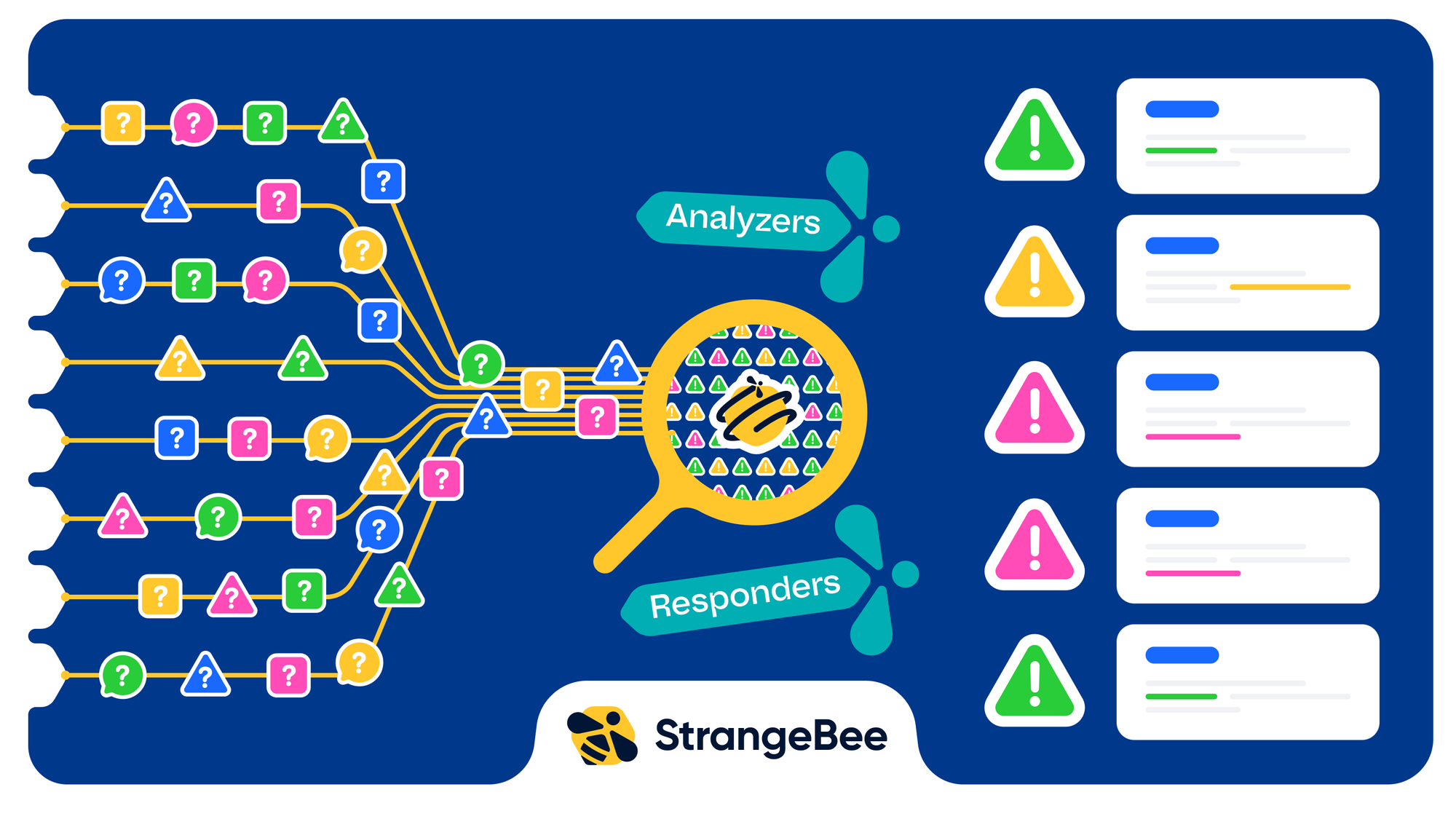
These vast collections of malware data are not just for archival purposes. They're essential for training AI models that detect and predict new malware variants. AI needs vast amounts of data to learn, and these repositories provide the necessary fuel.
Example: A cybersecurity firm uses these data sets to train a machine learning model. The model learns to identify patterns and anomalies that signify malware, improving its detection rate over time.
Enhancing Threat Intelligence
Threat intelligence relies on understanding the landscape of malware. By analyzing these repositories, researchers can identify trends and predict future threats. This intelligence is crucial for developing pre-emptive measures, as noted by Europol.
Example: A threat intelligence team analyzes Virus Total's data to discover a new malware strain targeting financial institutions. They issue an alert, allowing banks to bolster their defenses.

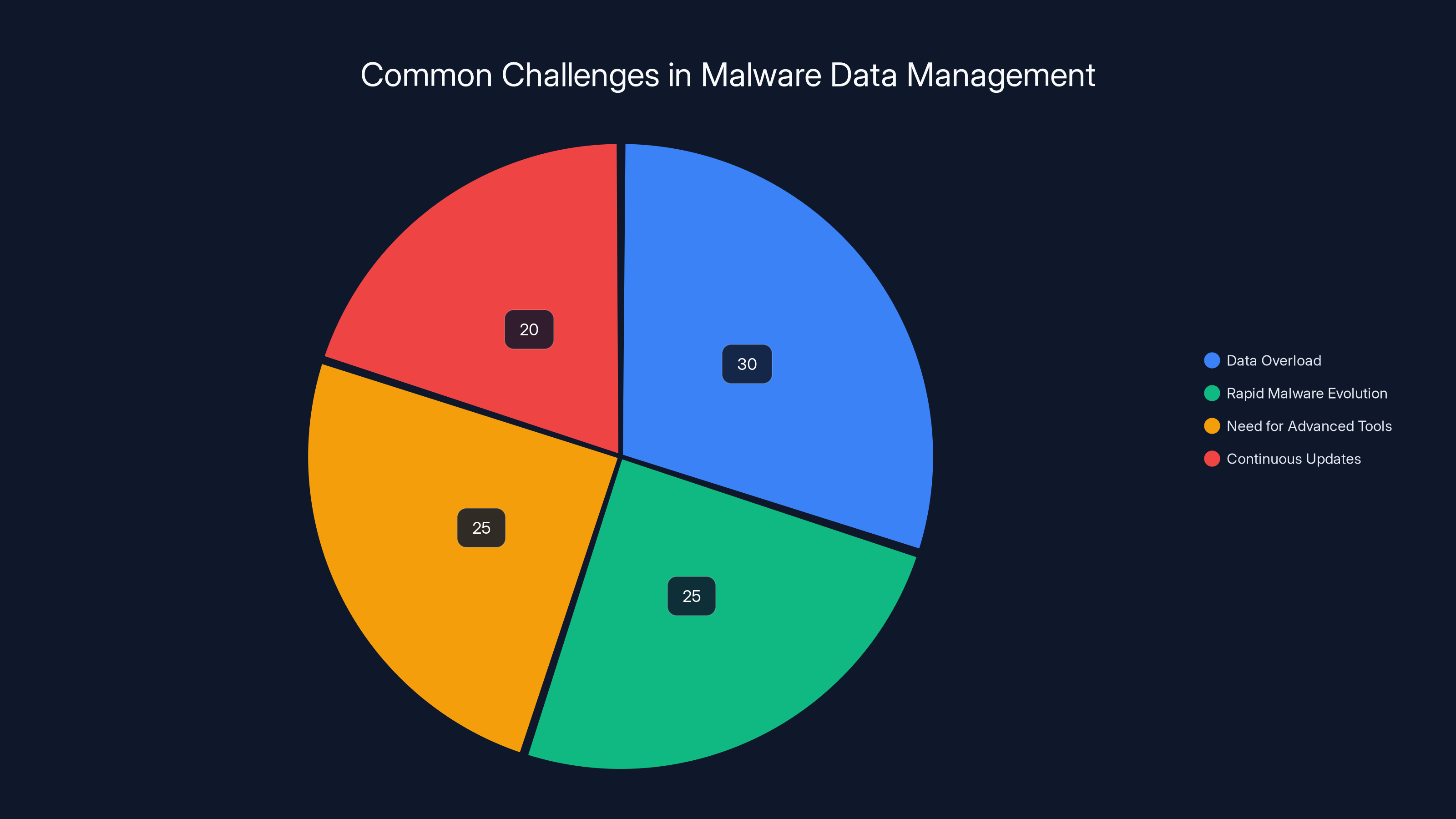
Data overload and rapid malware evolution are the most significant challenges, each accounting for over 25% of the issues faced by organizations. (Estimated data)
Practical Implementation: Leveraging Malware Data
Building Better Detection Systems
One of the primary uses of malware data is building more effective detection systems. By understanding how malware operates, developers can design systems that recognize and neutralize threats more efficiently.
Steps to Building an Effective Detection System:
- Data Collection: Gather extensive malware samples.
- Feature Extraction: Identify key characteristics of malware.
- Model Training: Use machine learning to train detection algorithms.
- Testing and Validation: Continuously test the system against new malware samples.
- Deployment: Implement the system in real-world environments.
Improving Response Strategies
Beyond detection, these data sets help in crafting robust response strategies. Knowing the common traits of malware allows organizations to respond swiftly and effectively.
Example: A company uses insights from malware data to develop a response playbook, ensuring rapid action when a breach occurs.
Common Pitfalls and Solutions
Data Overload
With the sheer volume of data, organizations can face challenges in processing and analyzing it effectively. This is where AI tools come into play, automating much of the workload.
Solution: Implement AI-driven analytics platforms that can handle large-scale data processing autonomously, as suggested by Fortune.
Keeping Up with Evolution
Malware evolves rapidly, often outpacing traditional defense mechanisms. Staying ahead requires constant updates and adaptations to detection systems.
Solution: Regularly update AI models with the latest data and trends from malware repositories.
Future Trends in Malware Data Management
The Rise of AI and Automation
As malware becomes more sophisticated, so too must our defenses. AI and automation are set to play even larger roles in the future, with systems becoming increasingly autonomous in threat detection and response.
Expanding Data Repositories
The volume of malware data is only going to increase. This growth necessitates more advanced data management solutions capable of handling petabyte-scale operations, as discussed in Fortune Business Insights.
Recommendations for Cybersecurity Professionals
- Invest in AI Tools: Leverage AI for both detection and response to stay ahead of new threats.
- Continuous Learning: Stay updated with the latest trends in malware evolution and defense strategies.
- Collaboration is Key: Work with other organizations to share insights and data, enhancing overall security.
Conclusion
The world of malware is vast and ever-expanding. By understanding and leveraging the immense banks of malware data, cybersecurity professionals can better protect against the evolving threat landscape. As data repositories grow, so too must our strategies and tools, ensuring we remain one step ahead in the digital arms race.
FAQ
What is a malware repository?
A malware repository is a large collection of malware samples and source code used for research and training purposes.
How do AI models use malware data?
AI models use malware data to learn patterns and anomalies, improving their ability to detect and predict new malware threats.
Why is it important to visualize malware data?
Visualizing malware data helps in understanding the scale and impact of malware, making it easier to communicate the importance of cybersecurity measures.
What challenges do organizations face with large-scale malware data?
Organizations often struggle with data overload and the rapid evolution of malware, requiring advanced AI tools and continuous updates.
How can cybersecurity professionals benefit from malware repositories?
Professionals can use these repositories to train AI models, enhance threat intelligence, and improve detection and response strategies.
What are the future trends in malware data management?
Expect increased reliance on AI and automation, along with the growth of data repositories and improved data management solutions.
How can organizations stay ahead of evolving malware threats?
Invest in AI tools, stay informed about the latest trends, and collaborate with other organizations to share insights and data.
What is the role of threat intelligence in cybersecurity?
Threat intelligence involves analyzing data to identify trends and predict threats, allowing organizations to develop pre-emptive cybersecurity measures.
Key Takeaways
- Vast malware repositories are crucial for AI training and threat intelligence.
- Understanding data scale helps visualize the impact of cybersecurity threats.
- AI-driven analytics are essential for managing large-scale malware data.
- Continuous updates and AI integration are vital for effective malware defense.
- Future cybersecurity will increasingly rely on AI and expanding data repositories.
Related Articles
- How AutoScientist is Revolutionizing AI Model Training [2025]
- How Alexa is Transforming the Amazon Shopping Experience [2025]
- Exploring Unitree's $650,000 Transformable Mecha: The Future of Robotics [2025]
- Understanding Meta's AI Account Policy on Threads [2025]
- Mind Robotics: Revolutionizing Industrial Automation with $400M Boost [2025]
- The FBI's Remote Router Resets: What It Means for Your Network [2025]
![The Massive Banks of Malware: Visualizing the Data Giants [2025]](https://tryrunable.com/blog/the-massive-banks-of-malware-visualizing-the-data-giants-202/image-1-1778697270514.jpg)



