The FBI's Remote Router Resets: What It Means for Your Network [2025]
Last week, the FBI made headlines by remotely resetting thousands of routers across the United States. This unprecedented action was part of an effort to neutralize a growing cybersecurity threat posed by compromised devices—specifically targeting routers manufactured by companies like TP-Link. But what does this mean for you and your network? How can you ensure your devices remain secure amidst such interventions? Let's dive deep into the implications and explore best practices for safeguarding your network.
TL; DR
- FBI's Action: The FBI remotely reset thousands of routers to combat a Russian GRU cyber threat.
- Affected Devices: Primarily older, end-of-life routers from manufacturers like TP-Link.
- Security Implications: Highlights vulnerabilities in outdated devices and the need for regular updates.
- Preventive Measures: Importance of firmware updates, strong passwords, and network segmentation.
- Future Trends: Expect increased government intervention in cybersecurity and the rise of AI-driven security solutions.

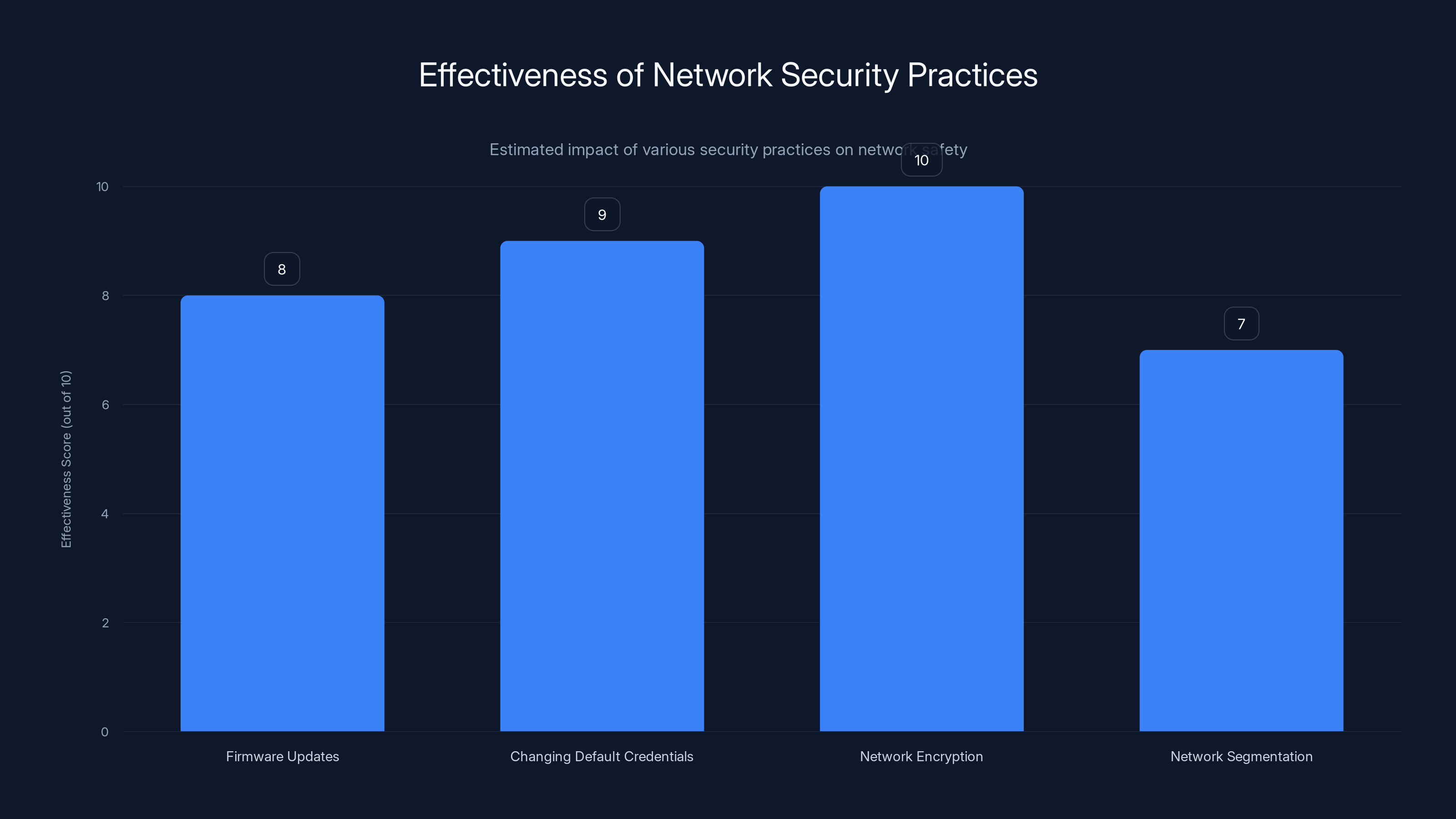
Changing default credentials and enabling network encryption are among the most effective practices for securing a network. Estimated data.
Understanding the FBI's Router Reset Operation
In a move that surprised many, the FBI took the bold step of remotely resetting routers identified as compromised by foreign cyber actors. The operation was a countermeasure against Russian GRU hacking attempts that targeted vulnerable home and small office routers. This section will break down why the FBI intervened and what it means for device owners.
The Cyber Threat Landscape
Cybersecurity threats have been escalating, with state-sponsored attacks becoming more sophisticated. The GRU, Russia's military intelligence agency, has been implicated in numerous cyber espionage and sabotage operations. Their tactics often involve exploiting vulnerabilities in widely-used hardware to gain access to sensitive networks.
Why Routers Are a Target
Routers are attractive targets for hackers because they serve as gateways to home and business networks. Compromising a router can give attackers unfettered access to all the devices connected to it, enabling data theft, network snooping, and more.
Key Vulnerabilities:
- Outdated Firmware: Many users neglect firmware updates, leaving routers exposed.
- Default Credentials: Routers shipped with default passwords are easy prey for attackers.
- Lack of Monitoring: Unlike computers, routers often lack active security monitoring.
The FBI's Role and Response
The FBI utilized a legal mechanism to perform remote resets on compromised routers. This action was designed to disrupt the malware and restore the devices to a safer state. However, it also raises questions about privacy and the extent of government intervention in cybersecurity.

Regular updates and strong passwords are crucial for network security. Estimated data based on common security advice.
How to Secure Your Network: Best Practices
Given the vulnerabilities exposed by this incident, it’s crucial to adopt robust security practices for your network. Here’s how you can protect your devices and data.
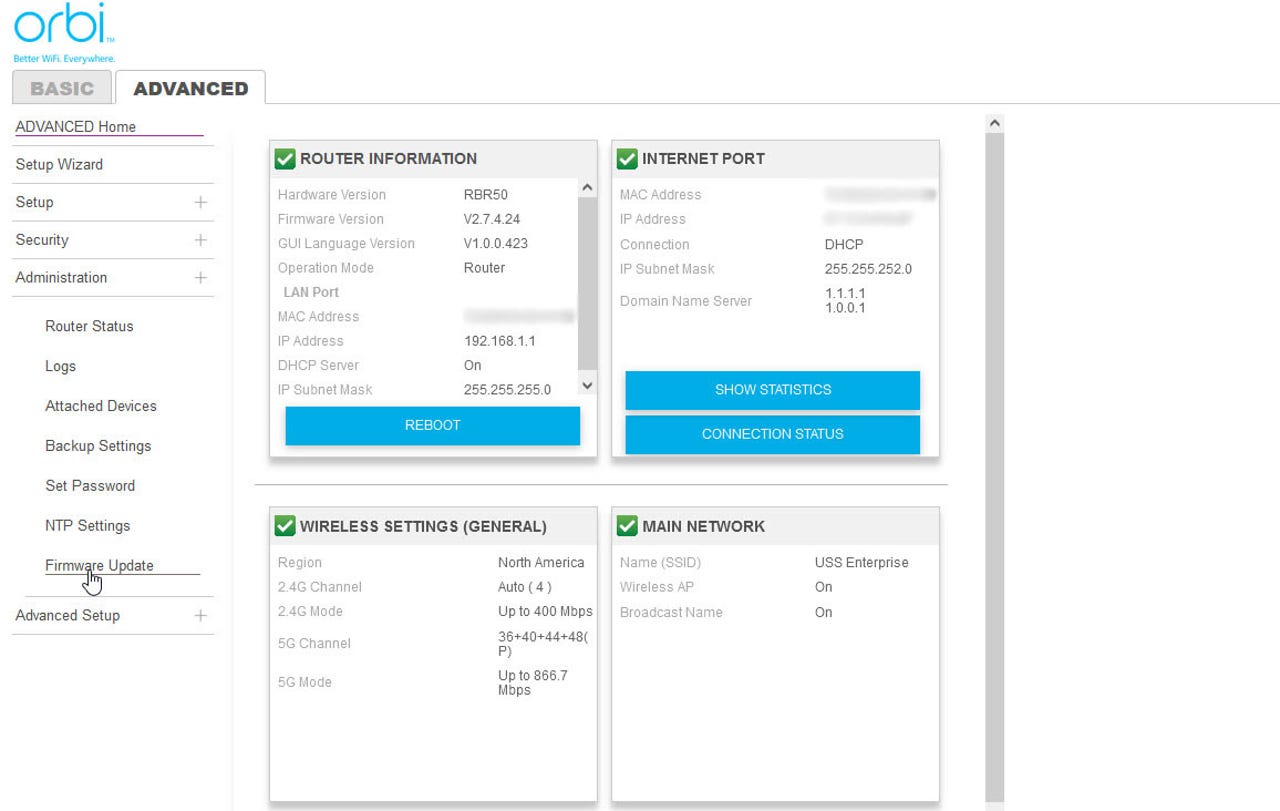
Update Your Router's Firmware Regularly
Firmware updates are essential for maintaining router security. They patch known vulnerabilities and improve device performance. Most manufacturers release updates periodically, which can be installed via the router's web interface.
Steps to Update Firmware:
- Log into your router's admin panel using its IP address.
- Navigate to the firmware update section.
- Download the latest firmware from the manufacturer's website.
- Follow the on-screen instructions to complete the update.
Change Default Credentials
Default usernames and passwords are a major security risk. Always change these credentials to something unique and complex as soon as you set up your router.
Password Tips:
- Use a mix of uppercase, lowercase, numbers, and special characters.
- Avoid using easily guessed information like birthdays or common words.
- Consider a passphrase for added security.
Enable Network Encryption
Ensure your network is encrypted using WPA3, the latest standard in wireless security. This makes it significantly harder for unauthorized users to access your network.
Encryption Setup:
- Access your router's settings through the admin panel.
- Select 'Wireless Security' or 'Wi-Fi Settings'.
- Choose WPA3 from the dropdown menu and save the changes.
Implement Network Segmentation
Network segmentation involves dividing your network into separate segments to enhance security. This limits the potential damage if one segment is compromised.
How to Segment Your Network:
- Use VLANs (Virtual Local Area Networks) to create separate networks for different device types (e.g., IoT devices, computers, guests).
- Configure firewall rules to control traffic between segments.
Monitor Network Traffic
Use network monitoring tools to keep an eye on traffic and detect any unusual activity. This can help you identify potential threats early.
Recommended Tools:
- Wireshark: A powerful network protocol analyzer.
- Nagios: A monitoring system that provides alerts for unusual activity.

Common Pitfalls and How to Avoid Them
While implementing security measures, users often make mistakes that can leave their networks vulnerable. Here are some common pitfalls and solutions.
Ignoring Firmware Updates
Many users underestimate the importance of firmware updates, leaving their routers exposed to known vulnerabilities. Set reminders to check for updates monthly.
Using Weak Passwords
Weak passwords are easy targets for attackers. Use password managers to generate and store strong, unique passwords for all your devices.
Leaving Remote Management Enabled
Remote management features can be exploited by attackers to gain access to your router. Disable this feature unless absolutely necessary.

Encryption and firmware updates are crucial for router security, with AI monitoring also playing a significant role. (Estimated data)
Future Trends in Router Security
As cyber threats evolve, so do security solutions. The future of router security will likely involve more sophisticated technologies and practices.
AI-Driven Security Solutions
Artificial Intelligence (AI) and Machine Learning (ML) are set to revolutionize network security. These technologies can analyze network traffic patterns in real-time, identifying and neutralizing threats before they cause damage.
Benefits of AI and ML in Security:
- Proactive Threat Detection: AI can identify anomalies and potential threats faster than traditional methods.
- Automated Responses: Quick mitigation of threats without human intervention.
Increased Government Involvement
Expect more government intervention in cybersecurity as threats grow in complexity and scale. This could include more frequent remote interventions and stricter regulations on network security standards.
The Rise of Quantum Encryption
Quantum encryption, leveraging the principles of quantum mechanics, promises unbreakable security. As quantum computing advances, quantum encryption may become standard in protecting sensitive communications.
Conclusion: Stay Vigilant and Proactive
The FBI's remote router reset operation serves as a stark reminder of the vulnerabilities inherent in our digital infrastructure. As technology advances, so too do the methods employed by cybercriminals. By staying informed and proactive about network security, you can protect your devices and data from becoming victims of the next cyber attack.
Remember:
- Regularly update your devices.
- Use strong, unique passwords.
- Enable the latest security protocols.
- Monitor your network for unusual activity.
Use Case: Automate your network security checks with AI-powered tools to ensure constant vigilance against cyber threats.
Try Runable For Free
FAQ
What is a router reset?
A router reset involves rebooting the device to clear any temporary configurations or issues. It can be done manually or remotely by authorized entities like the FBI in this case.
Why did the FBI reset routers?
The FBI reset routers to mitigate a cybersecurity threat associated with compromised devices, particularly targeting older models vulnerable to hacking.
How can I secure my router?
Secure your router by updating its firmware, using strong passwords, enabling encryption, and disabling unnecessary features like remote management.
What is WPA3 encryption?
WPA3 is the latest security protocol for Wi-Fi networks, offering stronger encryption and protection against brute-force attacks compared to its predecessors.
How does AI help in network security?
AI helps by analyzing network traffic in real-time, identifying potential threats quickly, and automating responses to neutralize attacks.
What future trends should I expect in router security?
Expect advancements in AI-driven security solutions, increased government involvement, and the adoption of quantum encryption technologies.

Key Takeaways
- FBI intervened to reset compromised routers, highlighting vulnerabilities in outdated devices.
- Regular firmware updates and strong passwords are crucial for router security.
- AI-driven security solutions offer proactive threat detection and response.
- Government involvement in cybersecurity is likely to increase.
- Quantum encryption promises unbreakable security for future communications.
Related Articles
- Understanding Data Security in the Age of AI: Lessons from a US Bank Security Lapse [2025]
- Understanding the Security Implications of Running Claude Code in Chrome [2025]
- Why Intelligence and Investigative Capability are Essential to Enterprise Security [2025]
- Google's Landmark Discovery: AI-Generated Zero-Day Exploit [2025]
- WhatsApp Users Can Soon Have Private Conversations With Meta AI [2025]
- Hosting Mini Data Centers at Home: The Future of AI Compute [2025]
![The FBI's Remote Router Resets: What It Means for Your Network [2025]](https://tryrunable.com/blog/the-fbi-s-remote-router-resets-what-it-means-for-your-networ/image-1-1778686624962.jpg)



