The Myth of the Trump Phone: Unraveling the Truth Behind the Rumor [2025]
Every few years, whispers of a so-called "Trump Phone" surface, captivating tech enthusiasts and political analysts alike. This mythical device, rumored to be a high-security phone endorsed or designed by former President Donald Trump, has never materialized. Yet, the speculation persists, fueled by a mix of political intrigue, technological advancements, and privacy concerns.
TL; DR
- No tangible Trump Phone exists: Despite rumors, there is no evidence of a Trump-branded phone being developed or released, as confirmed by a CNET report.
- Political branding impacts tech rumors: High-profile figures often influence tech narratives, leading to persistent myths.
- Privacy and security concerns: These drive the demand for devices perceived as 'secure,' contributing to the Trump Phone myth.
- Market trends and consumer behavior: Analysis shows no significant shift towards a niche market for politically branded devices.
- Future of secure communications: Advances in encryption and privacy tech may fulfill desires that drive such rumors.

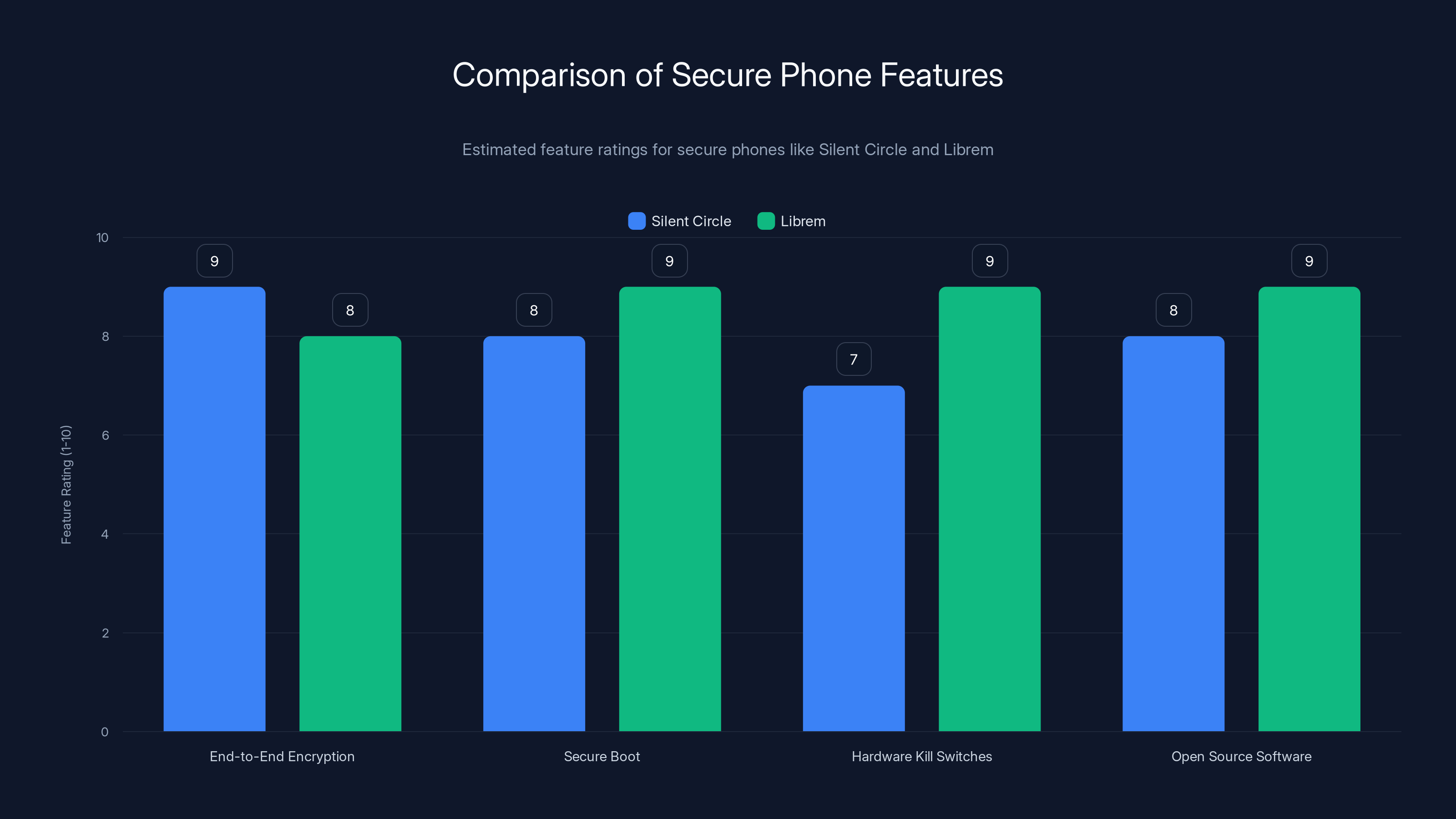
Estimated feature ratings show that both Silent Circle and Librem offer robust security features, with Librem slightly ahead in hardware kill switches and open source software. Estimated data.
The Genesis of a Rumor
The idea of a "Trump Phone" likely originated from a blend of political branding and the public's fascination with secure communication devices. In an era where privacy breaches are common, the allure of a phone promising heightened security is understandable. However, the reality is that no such device has been officially announced or developed under Trump's name.
Political Branding in Technology
Politicians have long influenced public perception, and technology is no exception. The notion of a Trump-branded phone taps into the broader trend of political figures associating themselves with products to bolster their brand. This strategy is not new; consider how various public figures have lent their names to everything from clothing lines to diet supplements.
Why the Rumor Persists
- Privacy Concerns: In an age of rampant data collection and surveillance, the idea of a phone with superior privacy features is appealing. It's a narrative that resonates with those wary of tech giants and government oversight, as discussed in StateScoop's analysis of privacy legislation.
- Political Polarization: The Trump brand remains polarizing, and anything associated with it tends to attract attention, whether positive or negative.
- Technological Feasibility: With advancements in encryption and secure communication, the idea seems plausible, even if unfounded.
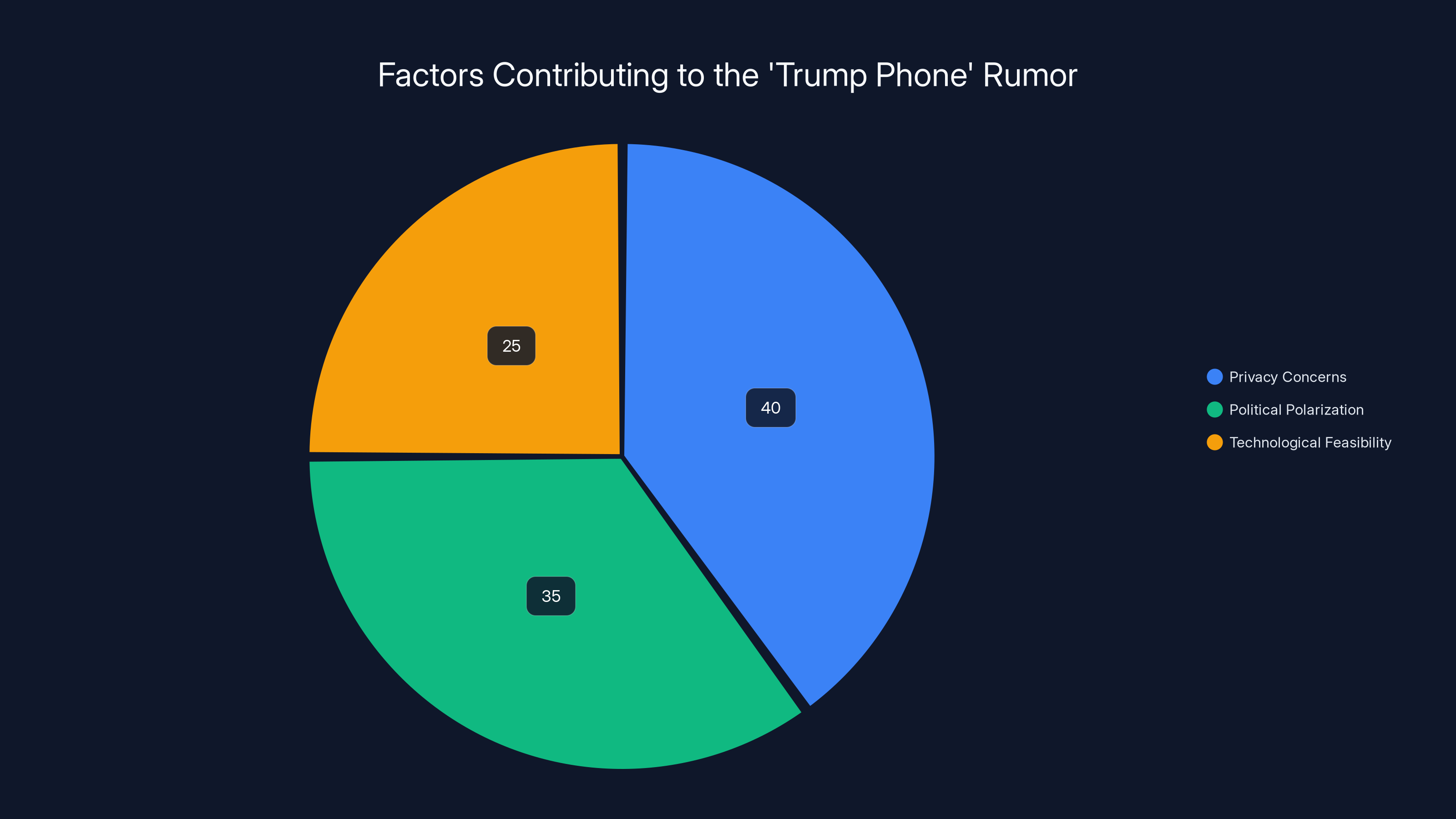
Privacy concerns are the leading factor contributing to the persistence of the 'Trump Phone' rumor, followed by political polarization and technological feasibility. (Estimated data)
The Anatomy of a Secure Phone
While the Trump Phone remains a myth, real-world examples of secure phones offer insight into what such a device might entail. Companies like Silent Circle and Librem have developed smartphones with enhanced security features, catering to users prioritizing privacy.
Features of a Secure Phone
- End-to-End Encryption: Protects communications from interception.
- Secure Boot: Verifies the integrity of the operating system upon startup, as highlighted in ZDNet's report on Secure Boot.
- Hardware Kill Switches: Allow users to disable microphones and cameras.
- Open Source Software: Provides transparency and allows for independent security audits.
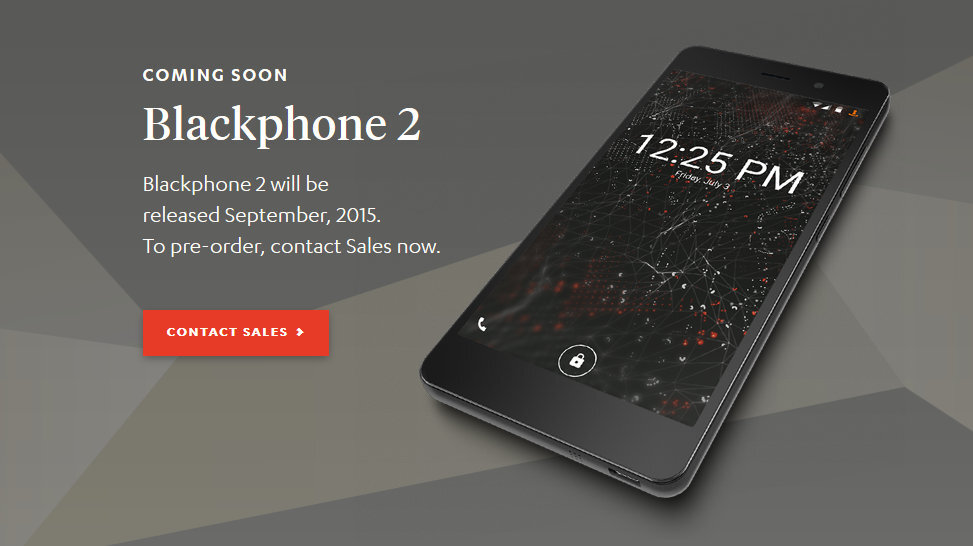
Case Study: Silent Circle's Blackphone
Silent Circle's Blackphone is a prime example of a secure smartphone. It uses an Android-based OS, Silent OS, which focuses on privacy. The device includes features like encrypted calls and messages, and it's marketed to those needing secure communications.
Pros:
- Strong privacy controls
- Regular security updates
- User control over app permissions
Cons:
- Limited app ecosystem
- Higher cost compared to mainstream devices
Technical Challenges and Best Practices
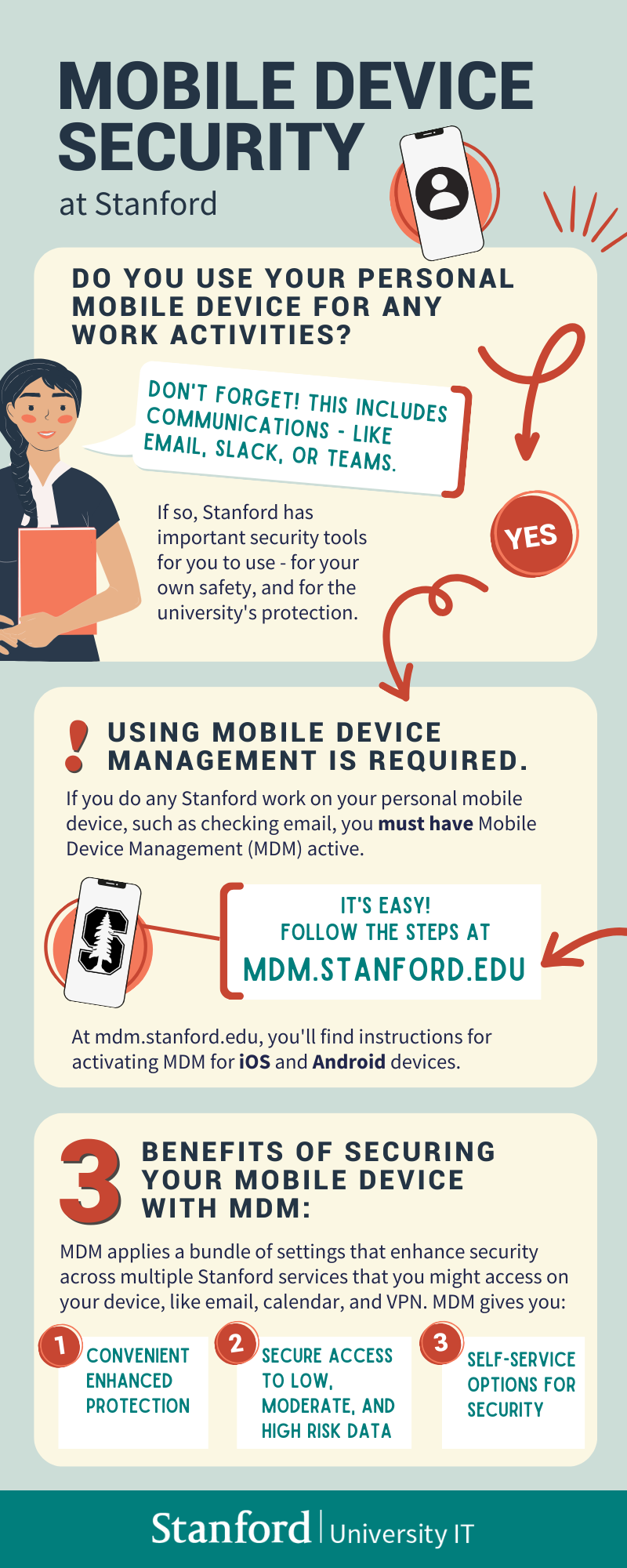
Creating a truly secure phone involves overcoming significant technical hurdles. Here are some best practices for enhancing smartphone security:
- Regular Software Updates: Ensure devices receive timely updates to patch vulnerabilities.
- User Education: Educate users on security practices, such as recognizing phishing attempts.
- Decentralized Data Storage: Minimize risk by storing sensitive data locally rather than on cloud servers.
- Robust Encryption Protocols: Utilize advanced encryption standards to safeguard data.
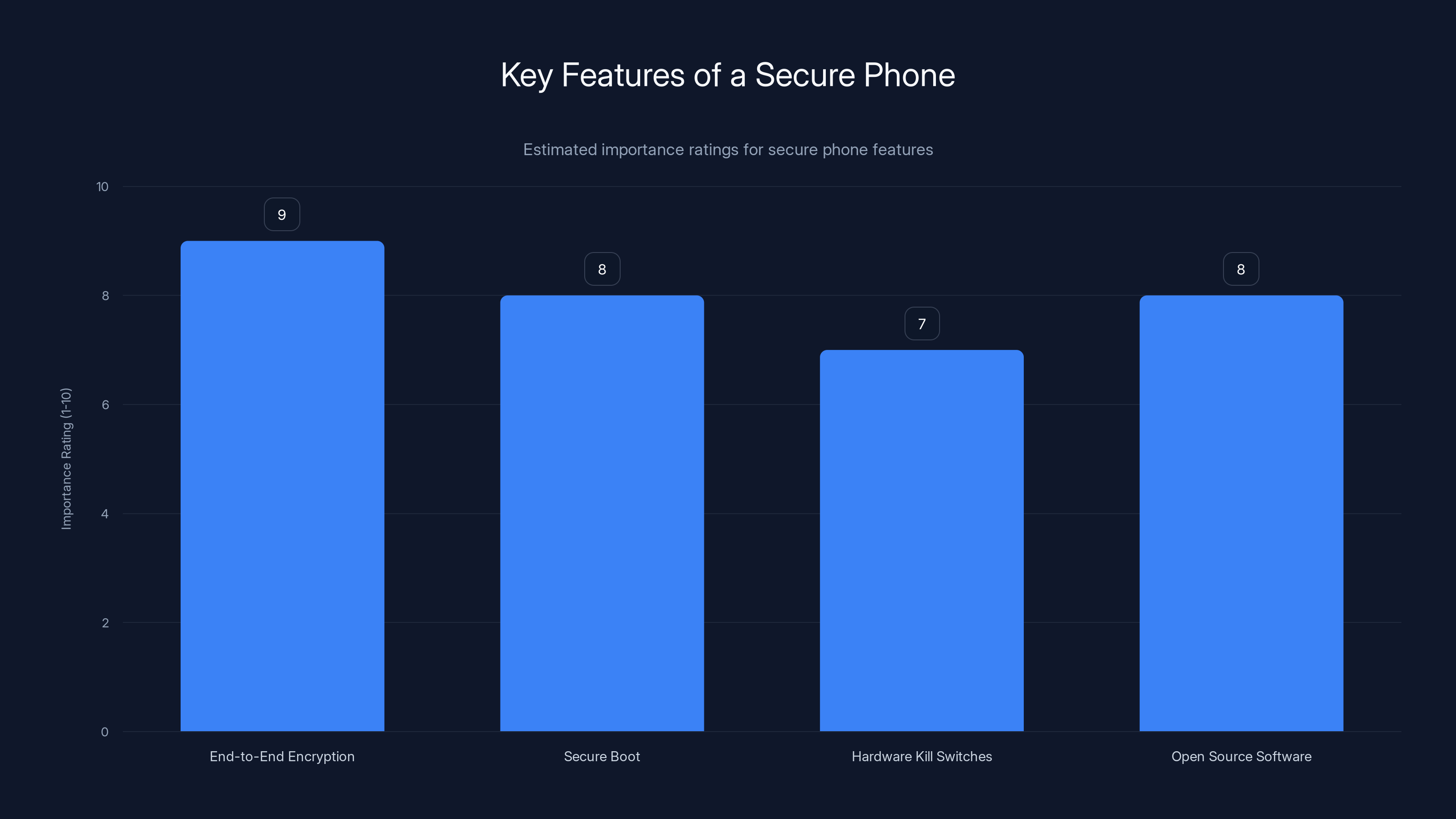
End-to-end encryption is rated as the most important feature for a secure phone, followed closely by secure boot and open source software. (Estimated data)
Implementation Guide: Building a Secure Communication App
For developers, creating an app that offers secure communication can be a viable alternative to a secure phone. Here's a step-by-step guide:
- Define the Scope: Determine the level of security needed and the target audience.
- Choose the Right Encryption: Implement end-to-end encryption using protocols like Signal Protocol.
- Focus on Usability: Ensure the app is user-friendly to encourage adoption.
- Conduct Security Audits: Regularly audit the app for vulnerabilities and update it accordingly.
Code Example: Implementing End-to-End Encryption
javascriptconst crypto = require('crypto');
function encrypt(text, secret) {
const iv = crypto.randomBytes(16);
const cipher = crypto.createCipheriv('aes-256-cbc', Buffer.from(secret), iv);
let encrypted = cipher.update(text);
encrypted = Buffer.concat([encrypted, cipher.final()]);
return iv.toString('hex') + ':' + encrypted.toString('hex');
}

Common Pitfalls and Solutions
- Overlooking User Experience: Security often comes at the cost of usability. Balance both to ensure adoption.
- Assuming Security is Absolute: No system is entirely secure. Always be vigilant and proactive in addressing vulnerabilities.
- Neglecting Compliance: Ensure your solutions comply with data protection regulations like GDPR or CCPA.
Future Trends in Secure Communications
As technology evolves, so do the methods for securing communication. Here are some trends to watch:
- Quantum Encryption: Promises unbreakable encryption by harnessing the principles of quantum mechanics.
- Decentralized Networks: Use blockchain to create secure, distributed communication networks.
- AI-Powered Threat Detection: Leverage AI to identify and mitigate security threats in real-time.
Recommendations for Consumers and Developers
For consumers, prioritize devices and apps that are transparent about their security features. Look for those that offer regular updates and have a track record of addressing vulnerabilities.
For developers, focus on building solutions that not only emphasize security but also consider usability. Engage users with clear instructions and support to foster trust and adoption.
Conclusion: The Reality of the Trump Phone
The Trump Phone may remain a myth, but the demand for secure communication devices is very real. In a world increasingly concerned about privacy, both consumers and developers play crucial roles in shaping the future of secure communications. By focusing on transparency, regular updates, and user education, we can meet the growing demand for privacy without needing a mythical device to lead the charge.
FAQ
What is the Trump Phone?
The Trump Phone is a rumored secure smartphone supposedly endorsed by Donald Trump. However, there is no evidence such a device exists, as noted in MSN's coverage.
Why do rumors about the Trump Phone persist?
Rumors persist due to a combination of privacy concerns, political branding, and technological advancements that make the concept seem plausible.
What features would a secure phone have?
A secure phone would likely include end-to-end encryption, secure boot, hardware kill switches, and open source software for transparency.
How can developers build secure communication apps?
Developers should focus on implementing end-to-end encryption, ensuring usability, conducting regular security audits, and complying with data protection regulations.
What are the future trends in secure communications?
Future trends include quantum encryption, decentralized networks, and AI-powered threat detection.
How can consumers ensure their devices are secure?
Consumers should choose devices and apps that are transparent about their security practices, offer regular updates, and have a reliable track record.

Key Takeaways
- The Trump Phone is a persistent rumor with no evidence of existence.
- Political branding influences technology narratives and consumer perceptions.
- Secure phones prioritize features like encryption and hardware kill switches.
- Developers should focus on usability alongside security in app development.
- Future trends in secure communications include quantum encryption and AI.
Related Articles
- Microsoft 365 Copilot: Navigating Data Processing Compliance [2025]
- OpenAI's Privacy Filter: Revolutionizing On-Device Data Sanitization [2025]
- Anthropic's Mythos Rollout and Its Cybersecurity Implications [2025]
- Why Default BitLocker Settings Aren’t Enough: Fortifying Against Physical Threats [2025]
- OpenAI’s Next-Gen Image Generator: Web-Enhanced Creativity [2025]
- Framework Unveils the Laptop 13 Pro with Intel's Panther Lake Chips [2025]
![The Myth of the Trump Phone: Unraveling the Truth Behind the Rumor [2025]](https://tryrunable.com/blog/the-myth-of-the-trump-phone-unraveling-the-truth-behind-the-/image-1-1777039470256.jpg)



