Why Default BitLocker Settings Aren’t Enough: Fortifying Against Physical Threats [2025]
Walk into any café or airport lounge, and you’ll see it—a sea of laptops, tablets, and smartphones busily helping professionals work outside the confines of traditional offices. This modern workplace is convenient, but it also introduces new security challenges, particularly when it comes to protecting sensitive data from physical threats.
TL; DR
- Default BitLocker settings offer basic encryption but lack advanced protections against physical tampering.
- Customizing BitLocker settings can enhance security by implementing pre-boot authentication and managing recovery keys.
- Physical threats like device theft and cold boot attacks require proactive countermeasures.
- Embrace a layered security approach combining BitLocker with other tools and practices.
- Future trends point towards integrating AI for predictive threat analysis and stronger endpoint defenses.
Understanding Physical Threats to Endpoints
The Reality of Physical Attacks
Physical attacks on endpoints are no longer just an edge-case scenario. With valuable data stored on portable devices, the risk of theft or unauthorized access is significant. Whether it's a lost laptop or a stolen USB drive, once a malicious actor has physical access, the stakes are high.
Types of Physical Attacks:
- Device Theft: Stolen devices provide direct access to data.
- Cold Boot Attacks: Exploits that retrieve encryption keys from RAM.
- Evil Maid Attacks: Involve tampering with a device left unattended to install malicious software.

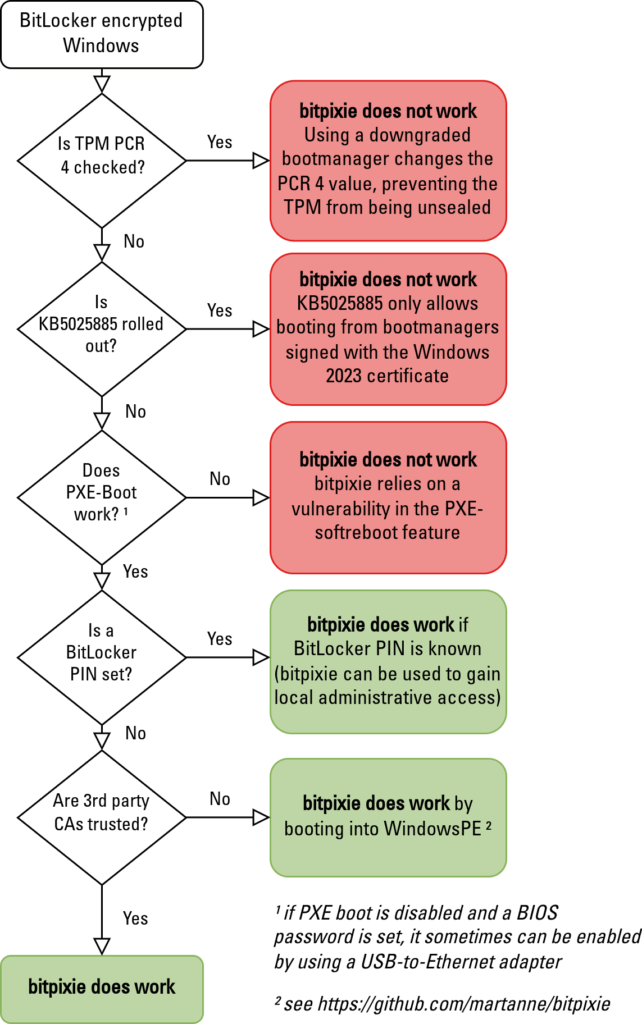
Why Default BitLocker Isn’t Enough
The Limitations of Default Configurations
BitLocker, Microsoft's disk encryption program, comes pre-installed on many Windows devices. While it offers a layer of protection, its default settings aren't sufficient to guard against sophisticated physical attacks. According to a PCWorld report, recent updates have highlighted vulnerabilities in default configurations.
Default BitLocker Features:
- Disk Encryption: Protects data at rest.
- TPM Integration: Uses the Trusted Platform Module for key management.
However, without additional configurations, BitLocker may not prevent unauthorized access if a device is physically compromised.
Potential Vulnerabilities:
- No Pre-Boot Authentication: Without this, an attacker can boot the device using external tools.
- Recovery Key Mismanagement: Default setups might leave recovery keys exposed.
Enhancing BitLocker Security
Implementing Pre-Boot Authentication
Pre-boot authentication requires users to provide a PIN or password before the operating system loads. This step ensures that only authorized users can access the encrypted data. As noted in Federal News Network, this is a critical layer of security.
How to Enable Pre-Boot Authentication:
- Open the BitLocker Management Console.
- Select the drive to configure.
- Choose “Require additional authentication at startup.”
- Set up a PIN or password.
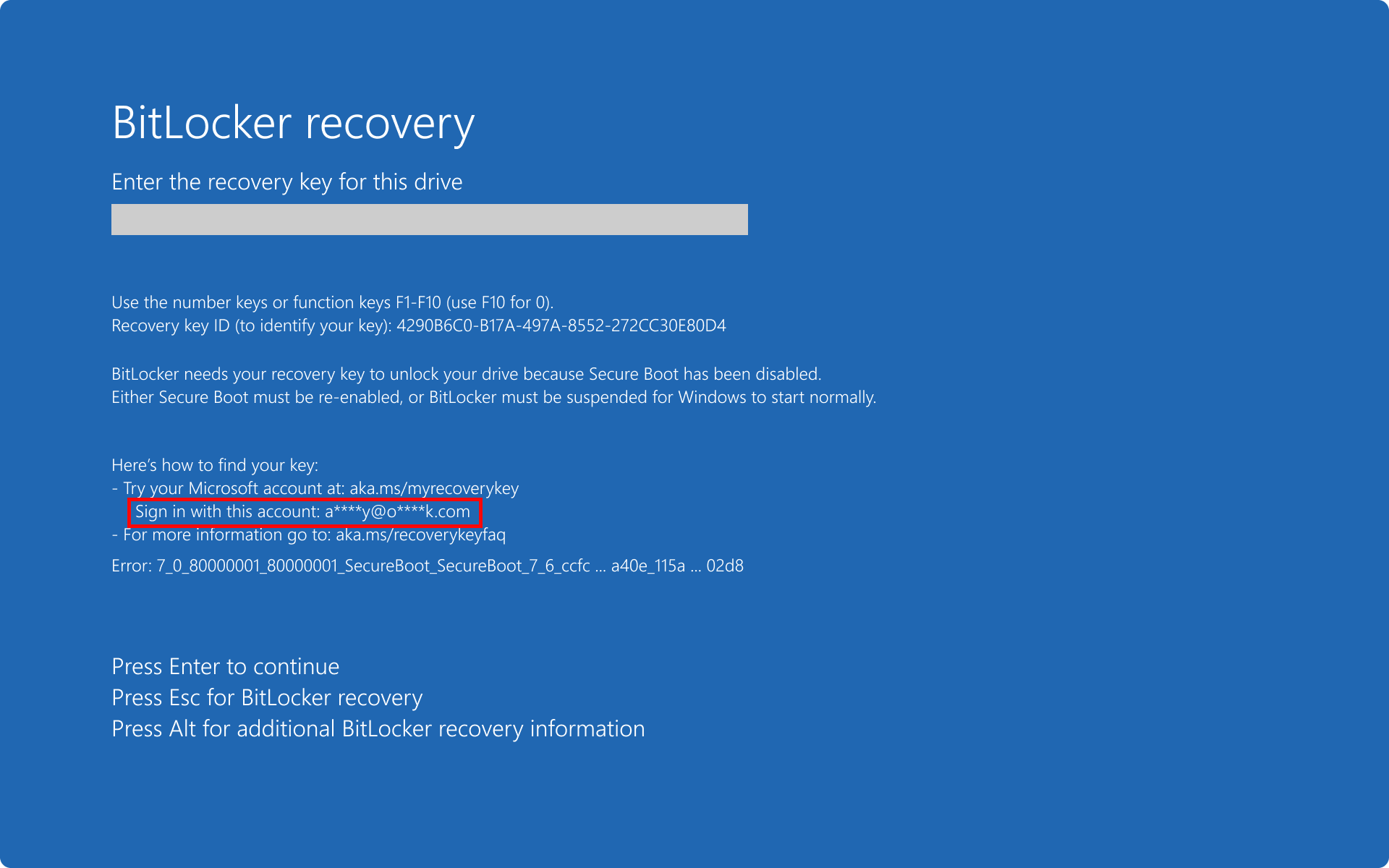
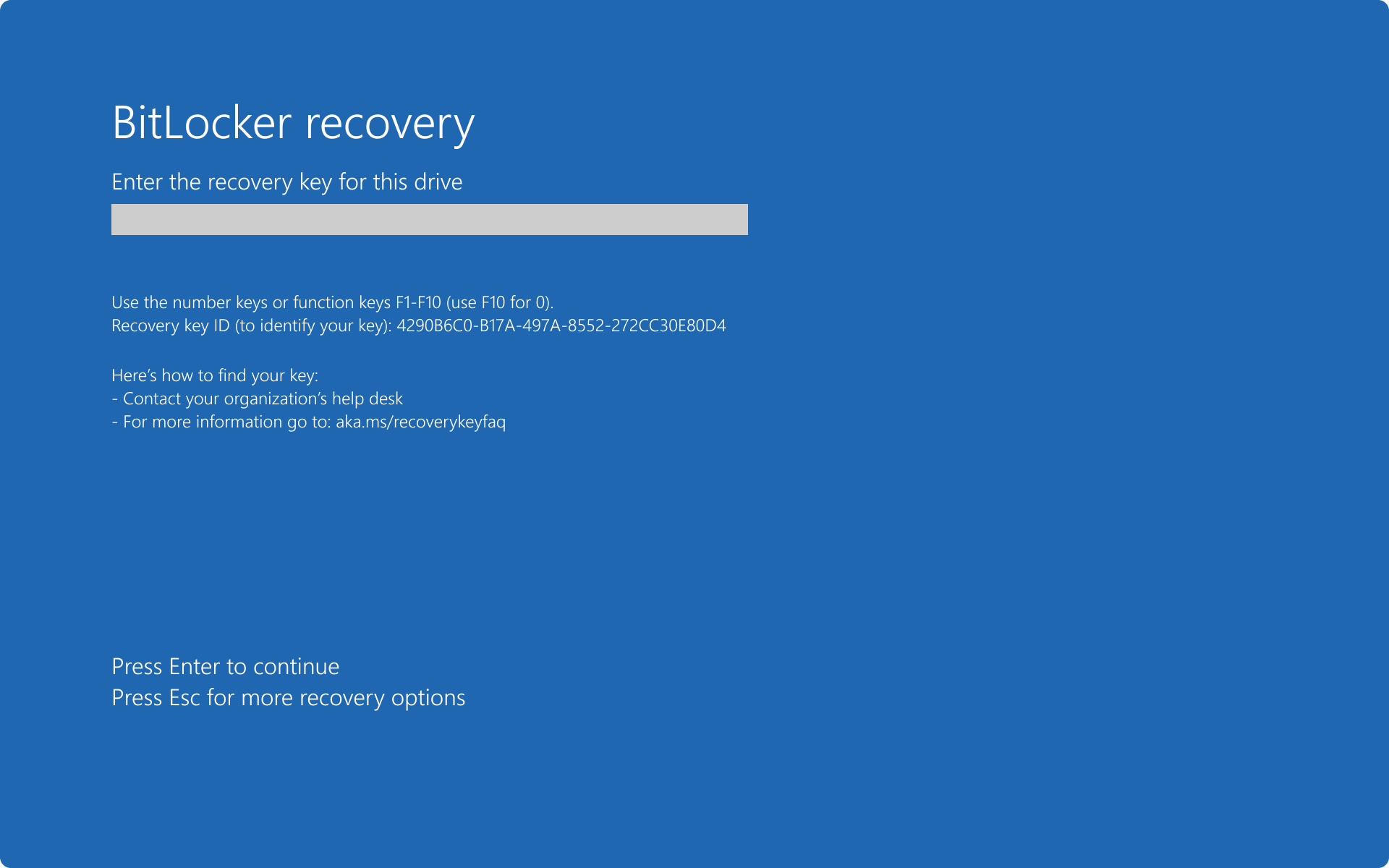
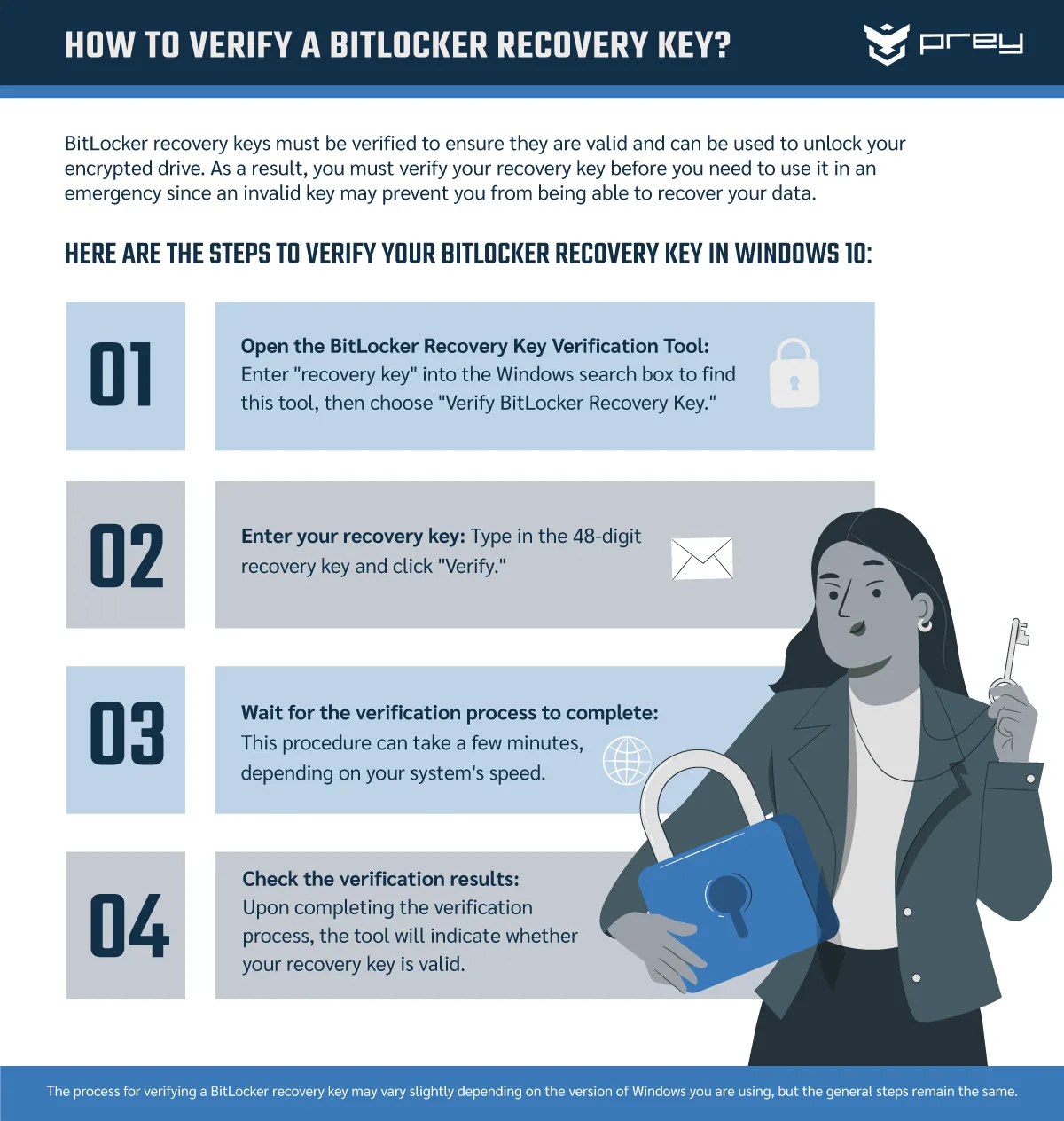
Managing Recovery Keys Securely
Recovery keys are crucial for data access if users forget their passwords, but they can also be a security risk if not managed properly.
Best Practices for Recovery Key Management:
- Secure Storage: Store keys in a secure location separate from the device.
- Key Rotation: Change recovery keys regularly.
- Audit Access: Keep logs of who has access to recovery keys.
Countermeasures Against Physical Threats
Preparing for Cold Boot Attacks
Cold boot attacks exploit the fact that RAM data persists for a short period after a device is powered off. Attackers can freeze RAM chips to slow the decay of data, making it possible to extract encryption keys. According to Hackaday, enabling full disk encryption is a key defense.
Defenses Against Cold Boot Attacks:
- Enable Full Disk Encryption: Ensures all data, including swap files and hibernation files, is encrypted.
- Disable Sleep Mode: Require complete shutdowns to clear RAM.
Mitigating Evil Maid Attacks
Evil maid attacks involve physical tampering with unattended devices to install malware or backdoors.
Preventive Measures:
- Physical Security: Use cable locks or secure storage when devices are unattended.
- BIOS Passwords: Set BIOS passwords to prevent unauthorized boot order changes.
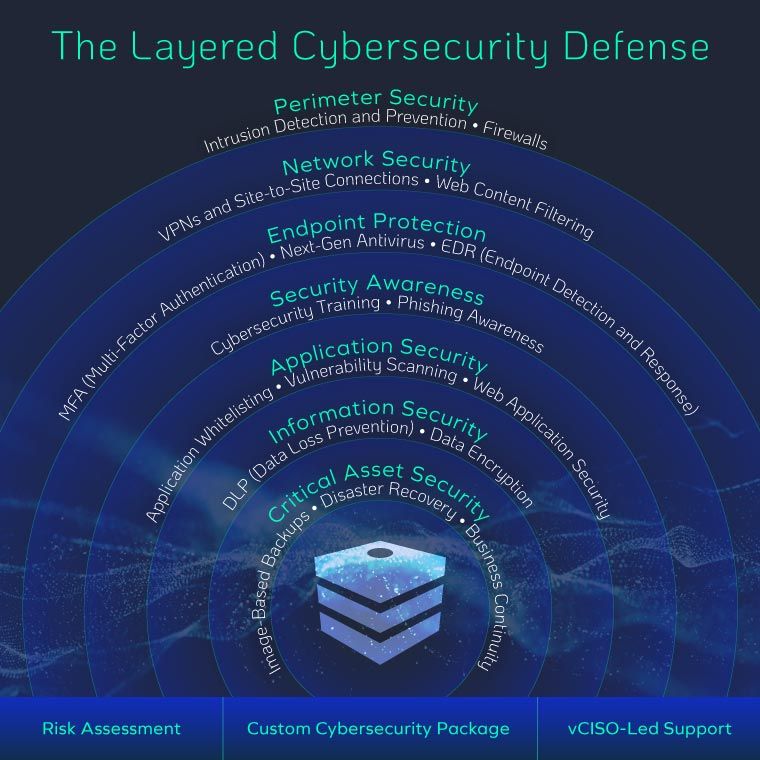
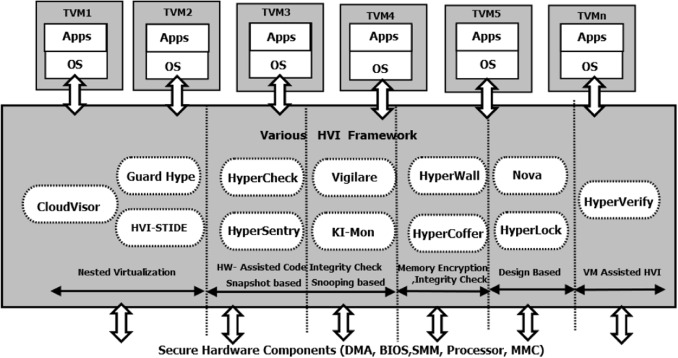
Integrating BitLocker with Other Security Measures
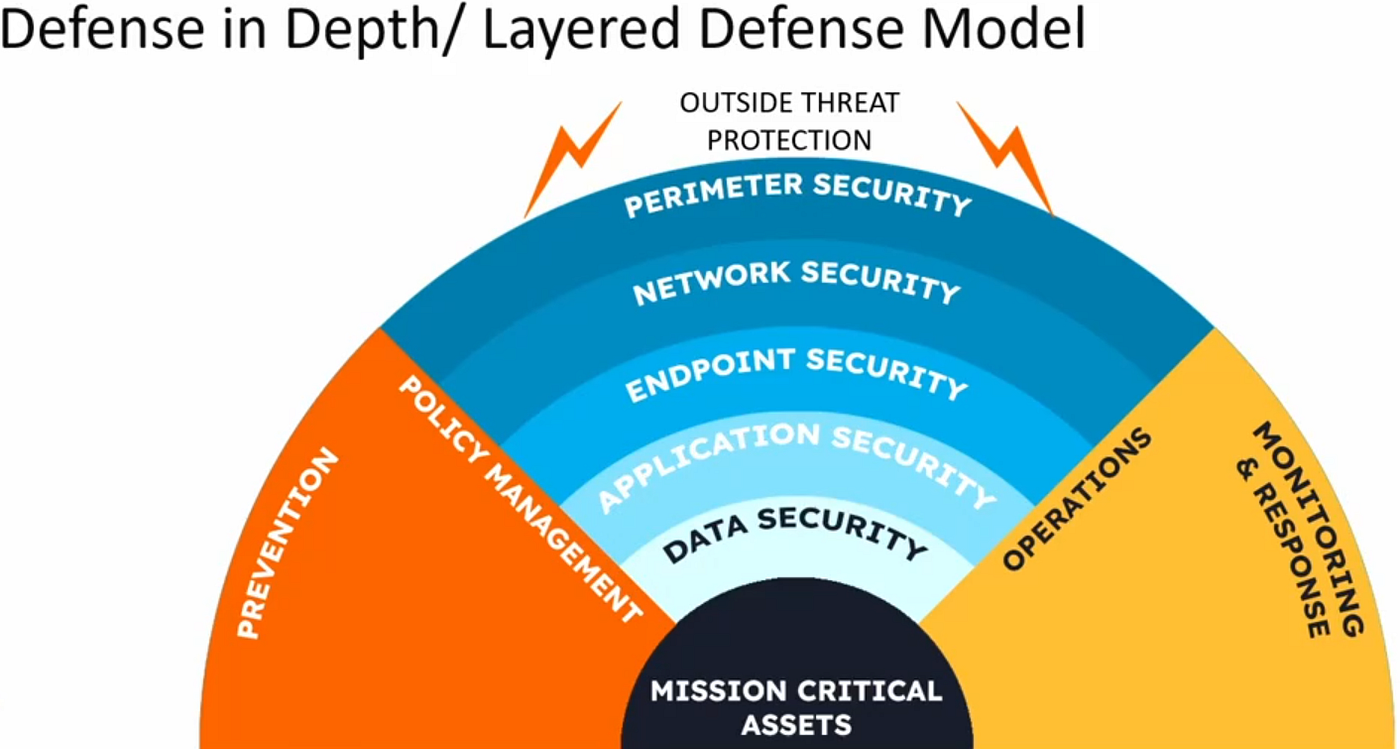
Layered Security Approach
Relying solely on BitLocker is not advisable. A comprehensive security strategy involves multiple layers of defense. The eSecurity Planet highlights the importance of integrating AI for enhanced security.
Additional Security Tools:
- Endpoint Detection and Response (EDR): Detects threats at the endpoint level.
- Zero Trust Architecture: Assumes no implicit trust, verifying each request as though it originates from an open network.
Case Study: Implementing a Multi-Layered Defense
A mid-sized tech firm faced repeated attempts at physical intrusion during international business trips. By enhancing their BitLocker setup and employing additional security tools, they significantly reduced unauthorized access incidents.
Steps Taken:
- Enabled pre-boot authentication on all company laptops.
- Implemented a company-wide policy for securing recovery keys.
- Integrated EDR solutions to monitor and respond to unusual activities.
Common Pitfalls and Solutions
Mismanagement of Recovery Keys
Issue: Recovery keys stored insecurely pose a risk of unauthorized access.
Solution: Implement strict key management policies and educate employees on secure storage practices.
Overreliance on Default Settings
Issue: Default BitLocker settings may not cover all potential attack vectors.
Solution: Regularly review and update encryption policies to address emerging threats.
Future Trends in Endpoint Security
AI and Machine Learning in Security
Artificial Intelligence (AI) is set to revolutionize endpoint security by predicting threats before they occur. According to Microsoft's security blog, AI is crucial for predictive threat analysis.
Potential Developments:
- Predictive Analytics: Using AI to identify patterns that suggest potential security breaches.
- Automated Threat Detection: Leveraging machine learning to autonomously detect and neutralize threats.
The Rise of Quantum Computing
Quantum computing poses a potential threat to current encryption standards, including those used by BitLocker.
Preparing for Quantum Threats:
- Quantum-Ready Cryptography: Transitioning to encryption methods that are resistant to quantum decryption methods.
Conclusion: Strengthening Endpoint Security
The modern workplace demands robust security measures to protect against a variety of threats, including physical attacks. While BitLocker provides a solid foundation, its default settings are not enough. By implementing advanced configurations and integrating with other security solutions, organizations can better defend their endpoints against physical and digital threats.
FAQ
What is BitLocker?
BitLocker is a disk encryption program included with Windows operating systems, designed to protect data by providing encryption for entire volumes.
How does BitLocker protect against physical attacks?
BitLocker encrypts data at rest, making it difficult for unauthorized users to access the contents of a device's storage if they gain physical access to it.
What are the benefits of pre-boot authentication?
Pre-boot authentication adds an extra security layer, requiring a PIN or password before the operating system loads, thus preventing unauthorized access.
How can I manage BitLocker recovery keys securely?
Store recovery keys in a secure location, separate from the device, and implement policies for regular key rotation and access auditing.
What is an evil maid attack?
An evil maid attack involves tampering with a device left unattended in order to install malware or backdoors, often requiring physical access.
Why should I disable sleep mode on my devices?
Disabling sleep mode ensures that RAM contents are cleared, protecting against cold boot attacks which exploit residual data in RAM.
What role does AI play in endpoint security?
AI enhances endpoint security by enabling predictive threat analysis and automated detection of anomalies, improving response times to potential threats.
How will quantum computing affect encryption?
Quantum computing could break current encryption algorithms, necessitating the development and adoption of quantum-resistant cryptographic methods.
Key Takeaways
- Default BitLocker settings are insufficient against physical attacks.
- Pre-boot authentication enhances endpoint security.
- Proper management of recovery keys is critical to prevent unauthorized access.
- A multi-layered security approach is necessary for comprehensive protection.
- AI and quantum computing will shape the future of endpoint security.
Related Articles
- Understanding Cybersecurity Breaches: Lessons from the Seiko USA Incident [2025]
- Mastodon Faces Major DDoS Attack: Understanding, Mitigation, and Future Preparedness [2025]
- France's Move to Linux: A Bold Shift from Windows 11 and What It Means for Microsoft's Future [2025]
- Cyber Warfare: Preparing Your Enterprise for the Digital Frontlines [2025]
- How Mozilla Leveraged AI to Fix Bugs in Firefox [2025]
- Microsoft Restructures Game Pass: Removing Call of Duty, New Pricing Explained [2025]
![Why Default BitLocker Settings Aren’t Enough: Fortifying Against Physical Threats [2025]](https://tryrunable.com/blog/why-default-bitlocker-settings-aren-t-enough-fortifying-agai/image-1-1776848682375.jpg)



