Understanding and Mitigating DDoS Attacks: Lessons from the Recent Ubuntu Outage [2025]
When Ubuntu's public-facing infrastructure faced a significant outage due to a Distributed Denial of Service (DDoS) attack, the tech community was reminded of the vulnerabilities even the most robust systems can exhibit. This article dives deep into what happened, why it matters, and how organizations can protect themselves from similar threats in the future.
TL; DR
- DDoS Attack on Ubuntu: Recent attack overwhelmed Ubuntu's infrastructure, affecting critical services.
- Impact on Users: Disrupted access to essential tools and services relied upon by millions.
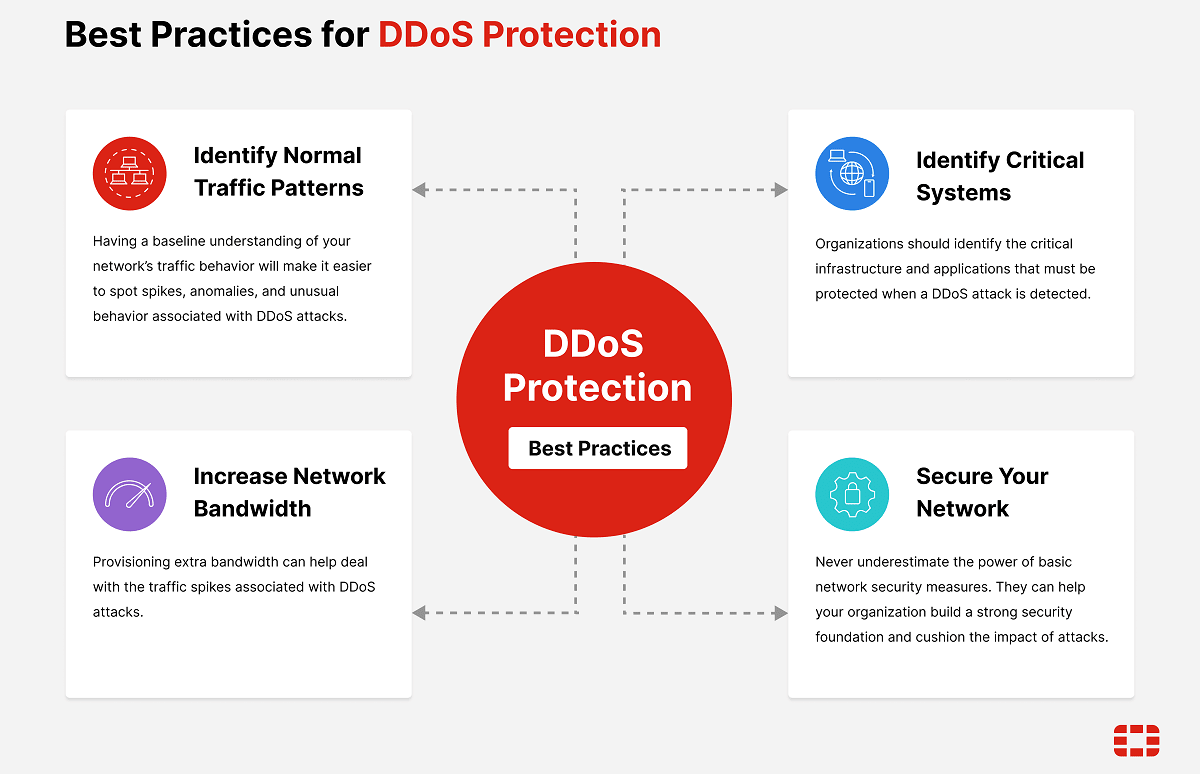
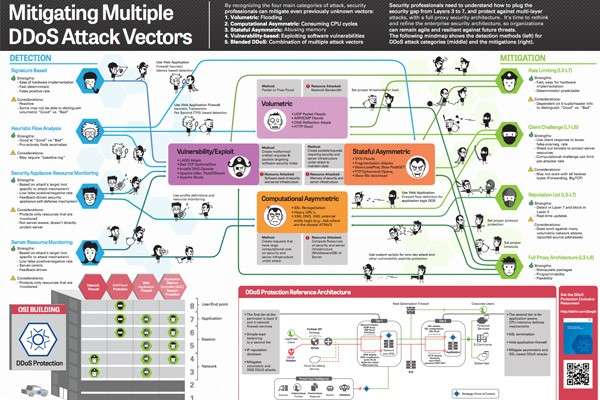
- Mitigation Strategies: Importance of multi-layered defenses and real-time monitoring.
- Future Trends: Growing sophistication in attack methods demands advanced security measures.
- Actionable Takeaway: Proactive measures and robust incident response plans are crucial.

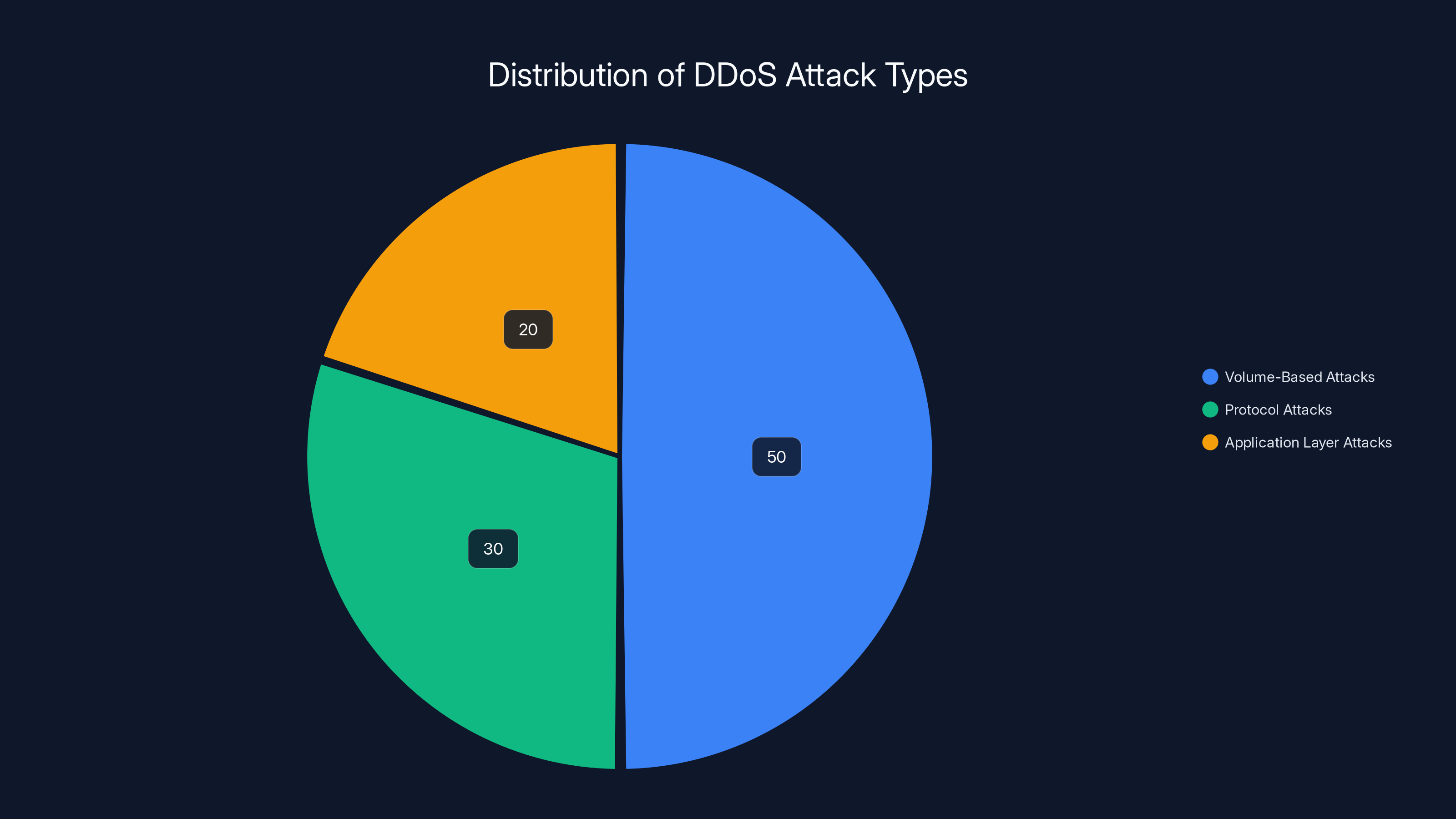
Volume-based attacks constitute the majority of DDoS attacks, followed by protocol and application layer attacks. (Estimated data)
The Anatomy of a DDoS Attack
What is a DDoS Attack?
A Distributed Denial of Service (DDoS) attack involves overwhelming a target's network or server with a flood of internet traffic. The goal is to render the service inoperable by exceeding its capacity to handle requests. This can be achieved through various methods, such as exploiting vulnerabilities or simply bombarding the target with excessive fake traffic.
Types of DDoS Attacks:
- Volume-Based Attacks: Flood the bandwidth of the target network.
- Protocol Attacks: Consume actual server resources or intermediate communication equipment.
- Application Layer Attacks: Target specific applications to exhaust resources.
How DDoS Attacks are Executed
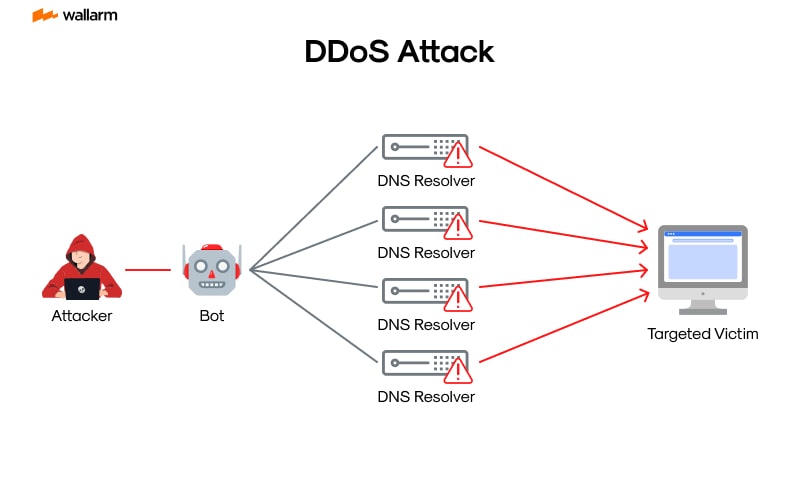
DDoS attacks are typically executed using a network of compromised devices known as a botnet. These devices, often infected without the owner's knowledge, can be remotely controlled by hackers to launch an attack at a specific target. According to BitSight's analysis, botnets like Rondodox are increasingly used for such purposes.

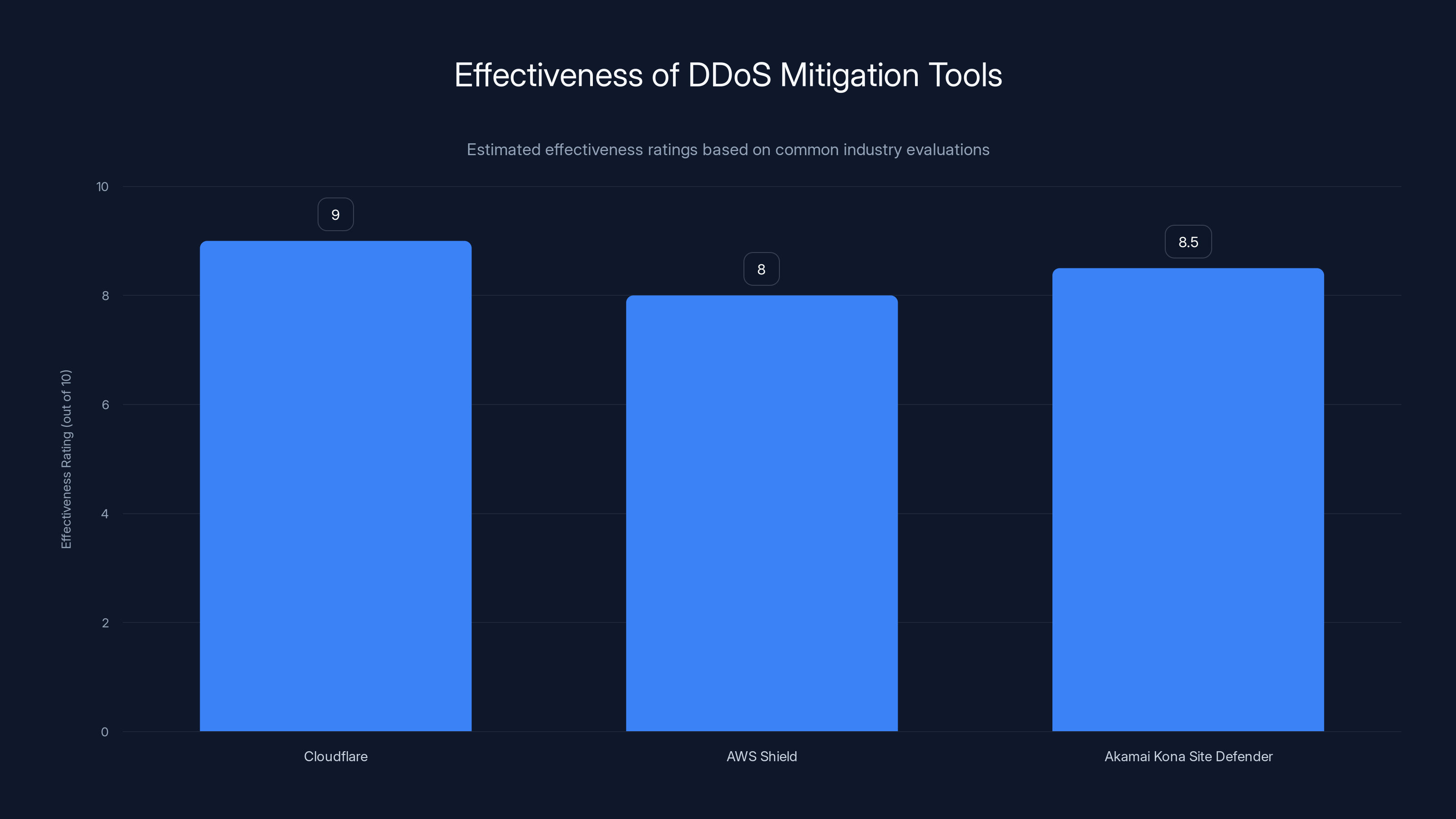
Cloudflare is estimated to have the highest effectiveness in DDoS mitigation, followed closely by Akamai Kona Site Defender and AWS Shield. Estimated data based on typical industry evaluations.
The Recent Attack on Ubuntu: A Case Study
Overview of the Incident
In a recent incident, Ubuntu, developed by Canonical, faced a sustained DDoS attack affecting its public services. This attack highlighted the vulnerabilities even major platforms can face and underscored the importance of preparedness.
Impacted Services:
- Ubuntu's security API
- Several official websites
Response and Mitigation Efforts
Canonical responded promptly, deploying mitigation techniques to counteract the attack. These included traffic filtering, rate limiting, and engaging with DDoS protection services to manage the influx of malicious traffic. As noted by Cybersecurity Insiders, effective response strategies are critical to minimizing financial losses during such attacks.

Practical Implementation to Defend Against DDoS
Building a Resilient Network Architecture
- Redundant Systems: Implement redundant systems to ensure service continuity.
- Load Balancing: Distribute traffic across multiple servers to prevent overloading.
- Rate Limiting: Control the rate of incoming requests to manage traffic spikes.
- Traffic Analysis: Use real-time analytics to identify and mitigate attacks early.
Effective DDoS Mitigation Tools
- Cloudflare: Offers comprehensive DDoS protection services, including real-time traffic analysis and mitigation.
- AWS Shield: Provides automatic DDoS protection for AWS-hosted applications.
- Akamai Kona Site Defender: Delivers cloud-based web application firewall and DDoS protection.
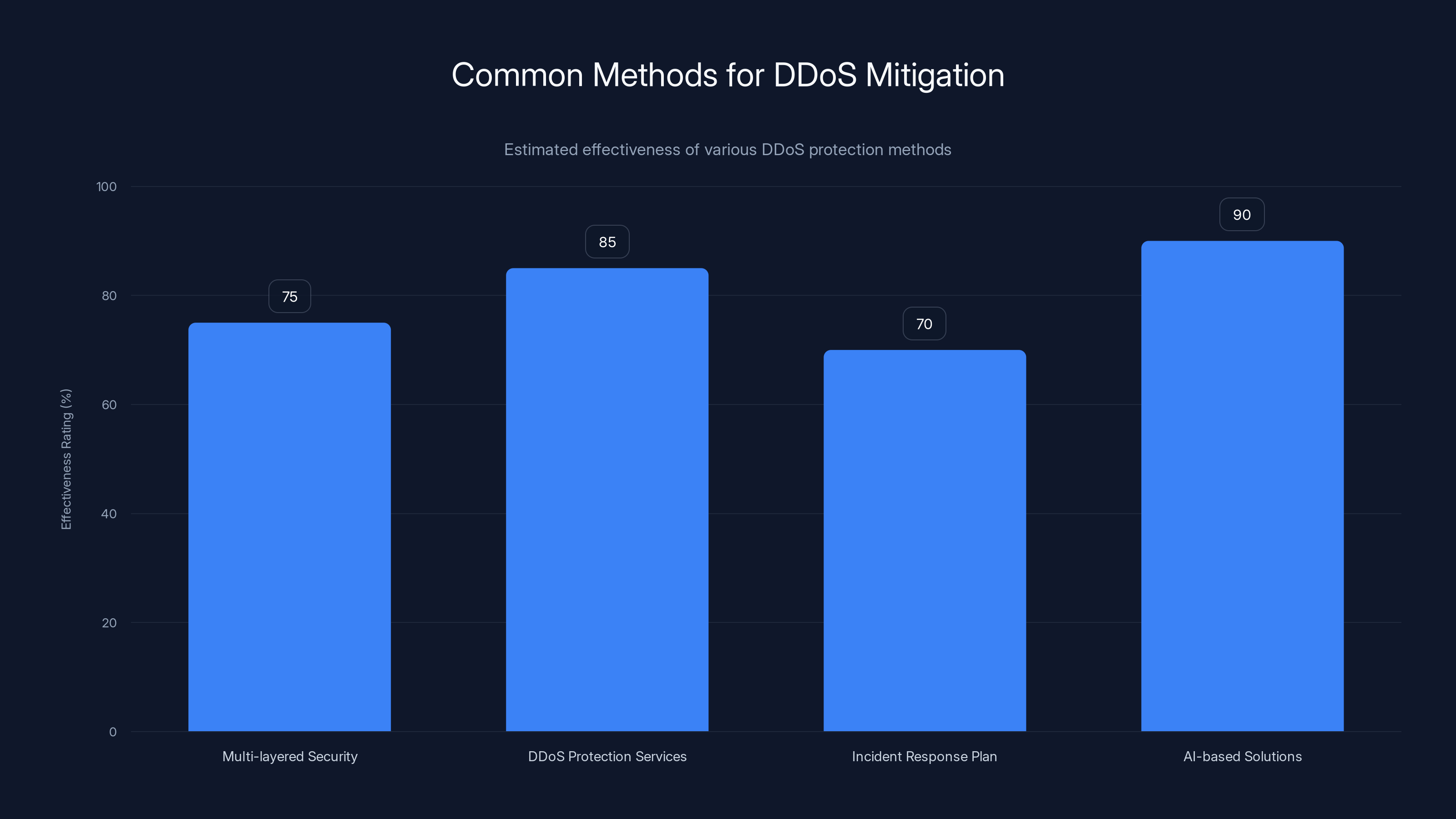
AI-based solutions are estimated to be the most effective in mitigating DDoS attacks, with a rating of 90%. Estimated data.
Common Pitfalls and Solutions
Pitfall: Underestimating Threats
Organizations often underestimate the potential impact of DDoS attacks until they experience one. This complacency can lead to inadequate preparation. A recent study highlights the emerging cyber threats targeting infrastructure, emphasizing the need for vigilance.
Solution: Regular threat assessments and stress testing of systems to ensure readiness for potential attacks.
Pitfall: Inadequate Incident Response Plans
Without a clear incident response plan, organizations may struggle to react swiftly to DDoS attacks, prolonging downtime and increasing losses.
Solution: Develop and regularly update a comprehensive incident response plan that includes specific DDoS scenarios.
Future Trends in DDoS Attacks
Increasing Sophistication
As technology evolves, so do the methods employed by attackers. We can expect more sophisticated DDoS attacks that leverage AI and machine learning to become harder to detect and mitigate. According to SecurityWeek, AI-driven attacks are on the rise, although their sophistication remains low for now.
Emerging Threats:
- IoT Botnets: Exploiting the growing number of connected devices.
- AI-Driven Attacks: Using machine learning to adapt attack strategies in real-time.
Recommendations for Future-Proofing
- Invest in AI-Driven Security Solutions: Implement AI systems capable of learning and adapting to new threats.
- Enhance Collaboration: Foster collaboration between industry players to share threat intelligence and best practices.
- Promote User Awareness: Educate users and employees about security best practices to reduce the risk of device compromise.
Conclusion
The recent DDoS attack on Ubuntu serves as a stark reminder of the ever-present threat posed by cyber-attacks. By understanding these threats and implementing robust security measures, organizations can better protect themselves and ensure service continuity.
Use Case: Automate your incident response with AI-driven workflows to detect and mitigate threats faster.
Try Runable For Free
FAQ
What is a DDoS attack?
A DDoS attack is a cyber-attack where multiple systems overwhelm a target's bandwidth or resources, making it inaccessible.
How can companies protect against DDoS attacks?
Companies can protect themselves by implementing multi-layered security measures, using DDoS protection services, and having a robust incident response plan.
Why are DDoS attacks common?
DDoS attacks are common because they are relatively easy to execute and can cause significant disruption with minimal effort.
What are the signs of a DDoS attack?
Signs include unusually slow network performance, unavailability of a particular website, and a sudden increase in traffic.
How does a botnet work?
A botnet is a network of compromised devices controlled by attackers to perform various malicious tasks, including DDoS attacks.
Can AI help in DDoS mitigation?
Yes, AI can help by analyzing traffic patterns in real-time to identify and mitigate threats more quickly than traditional methods.
Key Takeaways
- Understanding DDoS attacks is crucial for robust cybersecurity.
- Recent Ubuntu outage highlights vulnerabilities in public infrastructure.
- Implementing multi-layered defenses can mitigate DDoS impacts.
- Future attacks may leverage AI, increasing attack sophistication.
- Organizations must develop and regularly update incident response plans.
Related Articles
- OpenAI's New Cyber Tool: Access Restrictions and Industry Implications [2025]
- Understanding Cybersecurity Threats: Lessons from Sri Lanka's Recent Financial Breaches [2025]
- Exploring TikTok's Campus Hub: Revolutionizing College Connectivity [2025]
- Essential Guide to Dental Practice Software Security: Safeguarding Patient Data [2025]
- Understanding Polymarket's Long Shot Bets: Insights and Implications [2025]
- Unraveling the Best VPN Deal of 2026: Why CyberGhost at $1.75/Month is a Game Changer
![Understanding and Mitigating DDoS Attacks: Lessons from the Recent Ubuntu Outage [2025]](https://tryrunable.com/blog/understanding-and-mitigating-ddos-attacks-lessons-from-the-r/image-1-1777649769863.png)



