Understanding Cybersecurity Threats: Lessons from Sri Lanka's Recent Financial Breaches [2025]
Cybersecurity incidents have been grabbing headlines worldwide, and the recent breaches in Sri Lanka's finance ministry serve as a stark reminder of the vulnerabilities that exist even within governmental institutions. The theft of $2.5 million followed by a missing payment to the U.S. Postal Service highlights the need for robust cybersecurity measures. In this article, we'll delve into the technical aspects of these breaches, explore best practices, and provide a comprehensive guide to safeguarding against similar threats.
TL; DR
- Sri Lanka experienced a $2.5 million financial breach linked to business email compromise, as reported by TechCrunch.
- A subsequent $625,000 payment to the U.S. Postal Service went missing, raising concerns about broader vulnerabilities, according to OCCRP.
- Business email compromise (BEC) attacks are rising, targeting government and private sectors, as highlighted by the FBI Internet Crime Complaint Report 2025.
- Robust cybersecurity measures and employee training are crucial to prevent such incidents, as emphasized in a recent analysis.
- Future trends in cybersecurity involve AI-driven threat detection and blockchain for transaction security, as discussed in the Trends Research report.

![Distribution of Financial Breach Impacts in Sri Lanka [2025]](https://c3wkfomnkm9nz5lc.public.blob.vercel-storage.com/charts/chart-1777469606943-i01r0cjnx2p.png)
The chart illustrates the estimated distribution of impacts from recent financial breaches in Sri Lanka, with theft of funds being the most significant at 40%. Estimated data.
The Anatomy of the Breach
The breaches in Sri Lanka's finance ministry are indicative of a larger trend in cybercrime. Business Email Compromise (BEC) attacks have become increasingly common, largely due to their high success rate and the significant financial gains they offer to cybercriminals. These attacks typically involve the impersonation of a legitimate business entity to trick victims into transferring funds or revealing sensitive information, as detailed in a Talos Intelligence report.
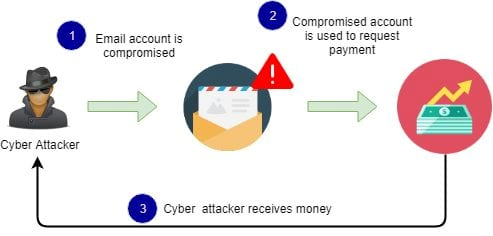
How BEC Attacks Work
- Reconnaissance: Attackers gather information about the target organization, often through social engineering or exploiting publicly available data.
- Phishing: They send emails that appear to be from trusted sources within the organization, instructing employees to transfer funds or share sensitive information.
- Execution: Once the victim is convinced, they unknowingly transfer funds to the attackers' account.
- Cover-up: The attackers may delete traces of their presence or use sophisticated methods to mask their activities.
Key Vulnerabilities Exploited
In the case of Sri Lanka, the breaches highlighted several vulnerabilities:
- Lack of Multi-Factor Authentication (MFA): Many organizations still rely solely on passwords, which can be easily compromised, as noted in the New York Times.
- Insufficient Employee Training: Employees are often the weakest link in cybersecurity, and without proper training, they can easily fall prey to phishing schemes, as discussed in a Help Net Security report.
- Inadequate Monitoring: Real-time monitoring of financial transactions could have detected anomalies sooner, according to CXO Digital Pulse.
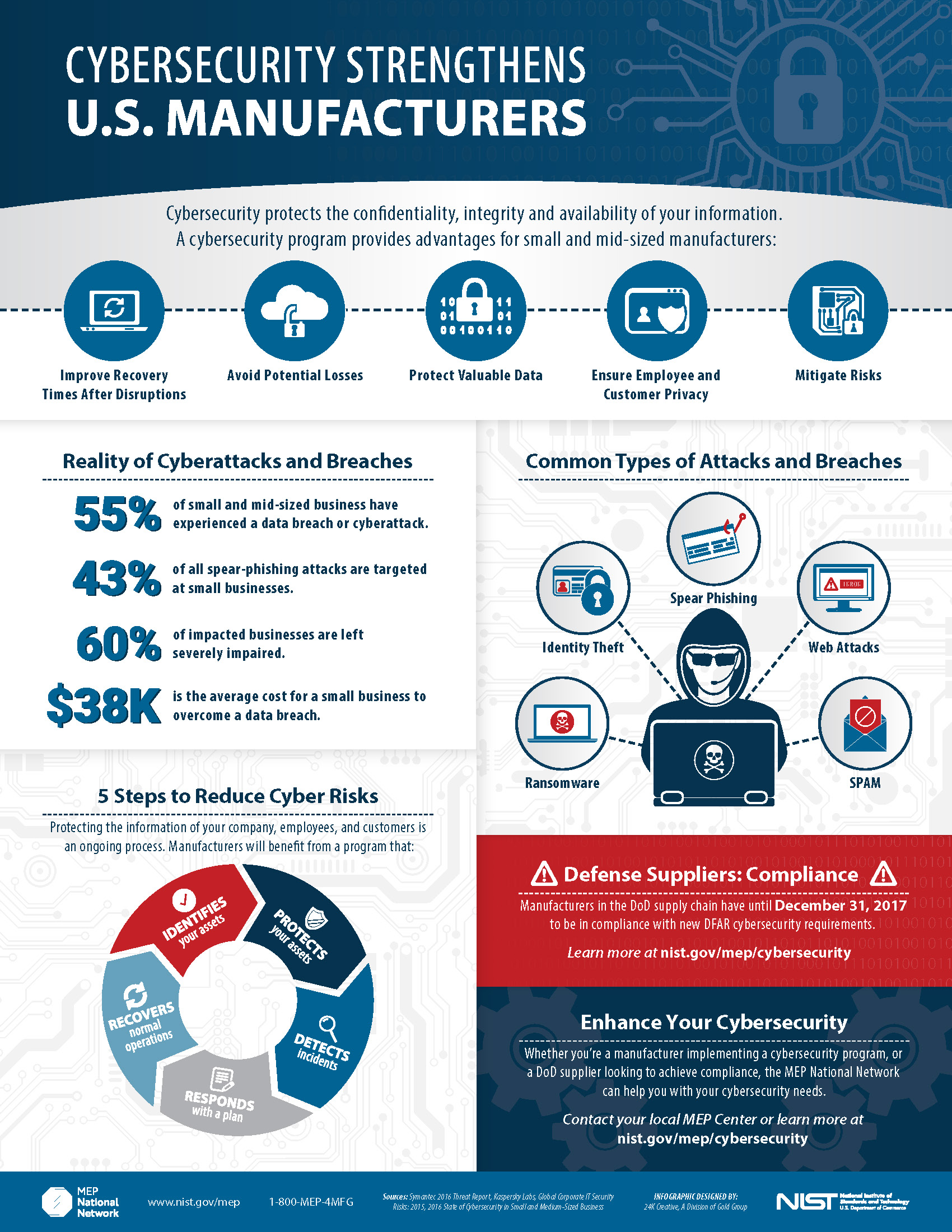
The pie chart illustrates the distribution of financial losses from recent cybersecurity breaches, highlighting the significant impact of business email compromise. Estimated data.
Best Practices for Cybersecurity
To prevent such incidents, organizations need to adopt a multi-faceted approach:
-
Implement Multi-Factor Authentication (MFA): Adding an extra layer of security can prevent unauthorized access even if passwords are compromised, as recommended by HIPAA Journal.
plaintextExample: Use a combination of passwords and a one-time code sent to a mobile device. -
Conduct Regular Employee Training: Employees should be regularly trained to recognize phishing attempts and understand the importance of cybersecurity.
-
Establish Robust Monitoring Systems: Implement systems that can monitor and flag suspicious activity in real-time, as suggested by Industrial Cyber.
-
Regular Audits and Updates: Conduct regular security audits and ensure that all software is up to date to protect against known vulnerabilities, as advised by ERP Today.
Common Pitfalls and Solutions
Pitfall: Over-Reliance on Technology
While technology is a crucial component of cybersecurity, over-reliance on software solutions can lead to complacency.
Solution: Balance technological solutions with human oversight. Regularly update policies and conduct manual checks where necessary.
Pitfall: Inadequate Incident Response Plan
Many organizations lack a clear plan for responding to cybersecurity incidents, leading to delayed and ineffective responses.
Solution: Develop a comprehensive incident response plan that includes roles, responsibilities, and a communication strategy.
Future Trends in Cybersecurity
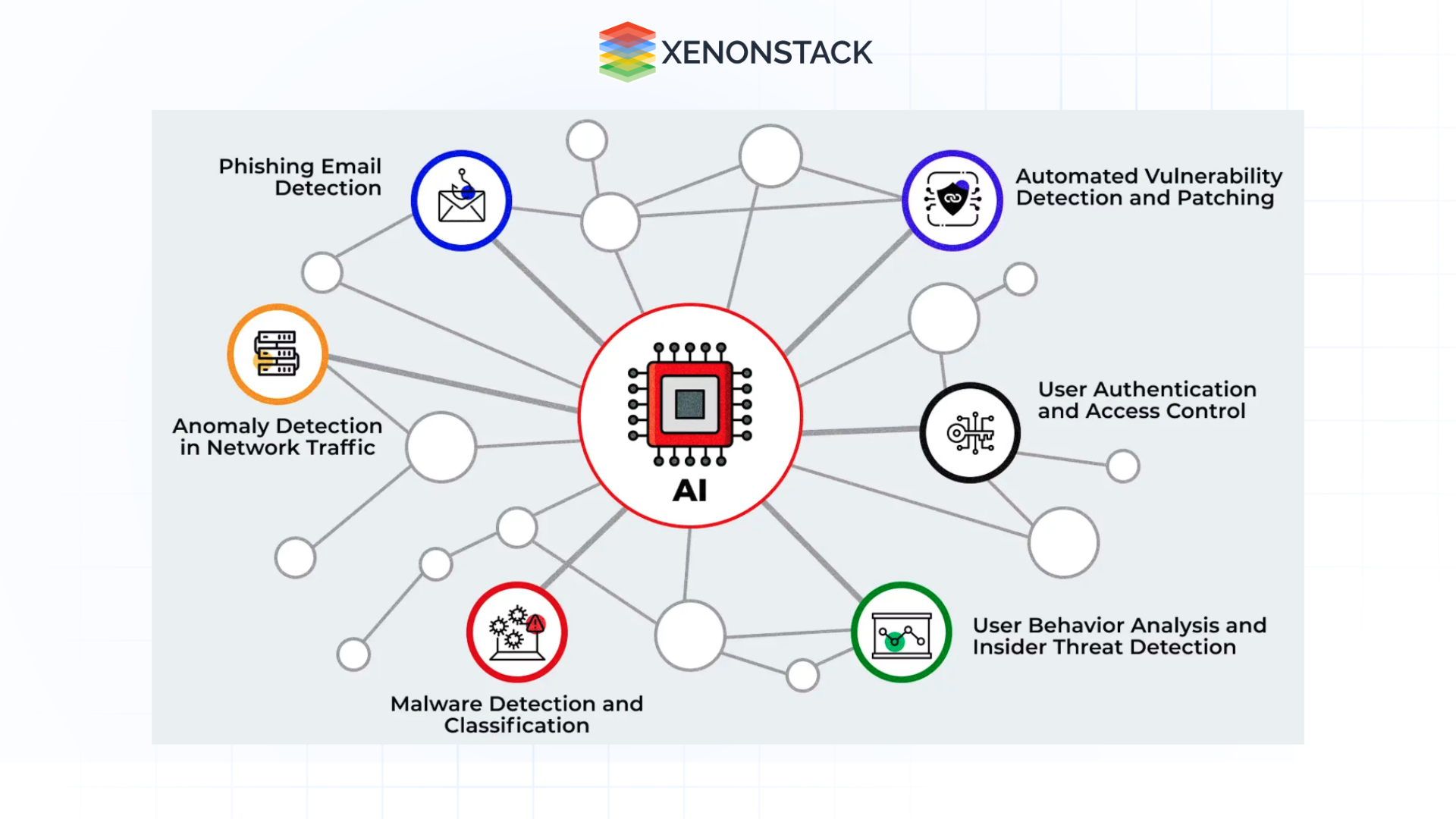
Looking ahead, several trends are poised to shape the cybersecurity landscape:
- AI-Driven Threat Detection: Artificial Intelligence can analyze vast amounts of data to detect threats in real-time. This technology is becoming increasingly accessible and effective, as noted in the Trends Research report.
-
Blockchain for Secure Transactions: Blockchain technology offers a decentralized and tamper-proof way to conduct transactions, reducing the risk of fraud, as discussed by CXO Digital Pulse.
-
Zero Trust Architecture: This approach assumes that threats can come from within or outside the network. It requires strict identity verification for every person and device attempting to access resources, as highlighted by New York Times.
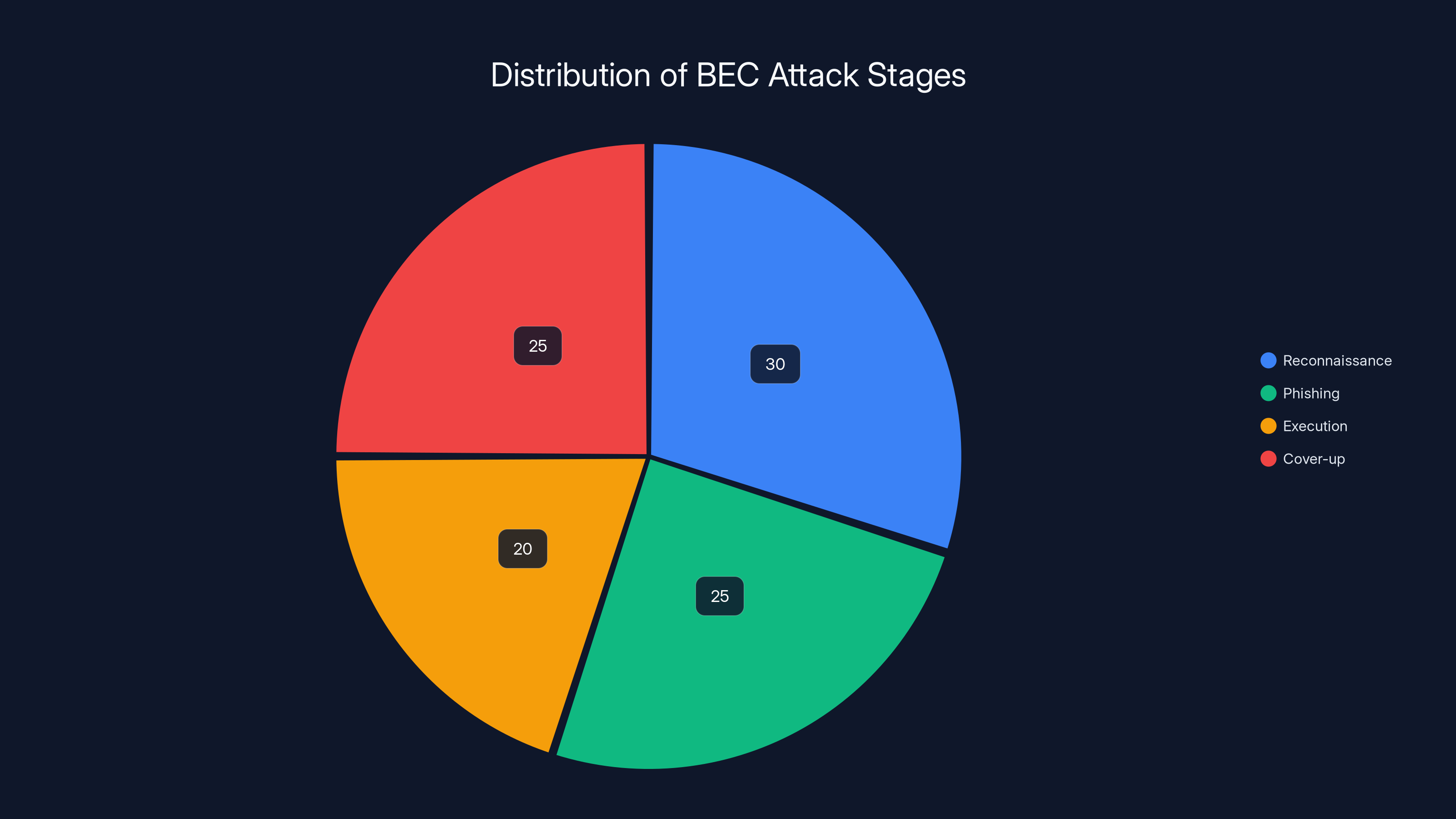
Estimated data shows that reconnaissance and cover-up stages take up the largest portions of time in a BEC attack, highlighting the importance of preparation and concealment.
Practical Implementation Guide
Step 1: Conduct a Risk Assessment
Identify and prioritize assets, vulnerabilities, and potential impacts. This assessment will guide the allocation of resources towards the most critical areas, as advised by Industrial Cyber.
Step 2: Develop a Security Policy
Create a comprehensive security policy that outlines procedures and responsibilities. Ensure it is regularly updated to reflect new threats and technologies, as recommended by ERP Today.
Step 3: Implement Security Controls
- Access Controls: Restrict access to sensitive information based on roles and responsibilities.
- Encryption: Use encryption to protect data both at rest and in transit, as advised by CXO Digital Pulse.
Step 4: Monitor and Test
Regularly monitor systems for signs of breaches and conduct penetration testing to identify weaknesses before attackers do, as suggested by HIPAA Journal.

Case Study: Successful Mitigation of a BEC Attack
In a recent case, a mid-sized company successfully thwarted a BEC attack through proactive measures:
- Early Detection: The company's security systems flagged an unusual email requesting a large transfer of funds, as reported by Talos Intelligence.
- Verification Protocols: Employees were trained to verify such requests via phone calls to known contacts.
- Quick Response: The incident response team acted swiftly, preventing any financial loss.

Recommendations for Organizations
-
Invest in Cyber Insurance: This can help mitigate financial losses in the event of a successful attack, as suggested by Help Net Security.
-
Foster a Security-First Culture: Encourage employees to prioritize security in their daily activities and provide incentives for reporting potential threats, as emphasized by Omnilert.
Conclusion
The cyber incidents faced by Sri Lanka's finance ministry are a wake-up call for organizations worldwide. By understanding the tactics used by attackers and implementing robust security measures, organizations can protect themselves from similar threats. As technology evolves, so too must our approaches to cybersecurity—continuously adapting to stay one step ahead of cybercriminals.
FAQ
What is a Business Email Compromise (BEC) attack?
A BEC attack is a form of cybercrime where attackers use email to trick victims into transferring funds or revealing sensitive information, as explained by Talos Intelligence.
How can organizations prevent BEC attacks?
Organizations can prevent BEC attacks by implementing multi-factor authentication, conducting regular employee training, and establishing robust monitoring systems, as recommended by HIPAA Journal.
What role does AI play in cybersecurity?
AI enhances cybersecurity by analyzing large datasets to detect and respond to threats in real-time, improving the speed and accuracy of threat detection, as noted in the Trends Research report.
Why is employee training important in cybersecurity?
Employees are often targeted in cyberattacks. Training helps them recognize phishing attempts and understand the importance of following security protocols, as discussed by Omnilert.
How does blockchain technology enhance security?
Blockchain provides a decentralized and secure way to conduct transactions, reducing the risk of fraud and ensuring data integrity, as explained by CXO Digital Pulse.
What should an incident response plan include?
An incident response plan should include roles, responsibilities, and communication strategies to ensure a quick and effective response to cybersecurity incidents, as advised by ERP Today.
Key Takeaways
- Sri Lanka's finance ministry breach highlights the rise of BEC attacks and the need for robust cybersecurity measures, as reported by TechCrunch.
- Multi-factor authentication and employee training are critical defenses against cyber threats, as emphasized by HIPAA Journal.
- AI and blockchain technologies offer promising advancements in enhancing security and preventing fraud, as discussed in the Trends Research report.
- A comprehensive incident response plan is essential for minimizing damage from cyberattacks, as advised by ERP Today.
- Fostering a security-first culture within organizations can significantly reduce the risk of cyber incidents, as emphasized by Omnilert.
The Path Forward
As cyber threats continue to evolve, organizations must remain vigilant and proactive in their cybersecurity efforts. By leveraging emerging technologies, fostering a culture of security, and maintaining robust defenses, they can protect themselves against the ever-present threat of cybercrime.
Related Articles
- Why Default BitLocker Settings Aren’t Enough: Fortifying Against Physical Threats [2025]
- Why Tokyo is the Most Important Tech Destination of 2026 [2025]
- Indefinite Pausing of Windows Updates: A Deep Dive [2025]
- Understanding Insider Trading in Prediction Markets: The Case of Polymarket and Beyond [2025]
- The Myth of the Trump Phone: Unraveling the Truth Behind the Rumor [2025]
- Australia Joins Global Efforts with Claude Mythos to Tackle Cybersecurity Challenges [2025]
![Understanding Cybersecurity Threats: Lessons from Sri Lanka's Recent Financial Breaches [2025]](https://tryrunable.com/blog/understanding-cybersecurity-threats-lessons-from-sri-lanka-s/image-1-1777469704722.jpg)



