Understanding and Mitigating Microsoft Teams Helpdesk Impersonation Attacks [2025]
Last month, a startling revelation shook the tech community: cybercriminals have been exploiting Microsoft Teams to impersonate IT helpdesk personnel. This sneaky tactic has allowed attackers to blend seamlessly into routine IT support activities, leaving organizations vulnerable to data breaches and unauthorized access. But here's the kicker—it’s not just about Teams. This trend highlights a broader challenge in cybersecurity: the exploitation of trust in digital communication platforms.
TL; DR
- New Threat: Cybercriminals are impersonating IT helpdesk via Microsoft Teams to gain unauthorized access.
- Trust Exploitation: These attacks take advantage of the trust users place in IT support personnel.
- Mitigation Strategies: Implementing multi-factor authentication (MFA) and user training are key defense mechanisms.
- Remote Assistance Risks: Abusing remote assistance features is a common method for attackers to gain control.
- Future Trends: Expect more sophisticated social engineering attacks targeting internal communication tools.

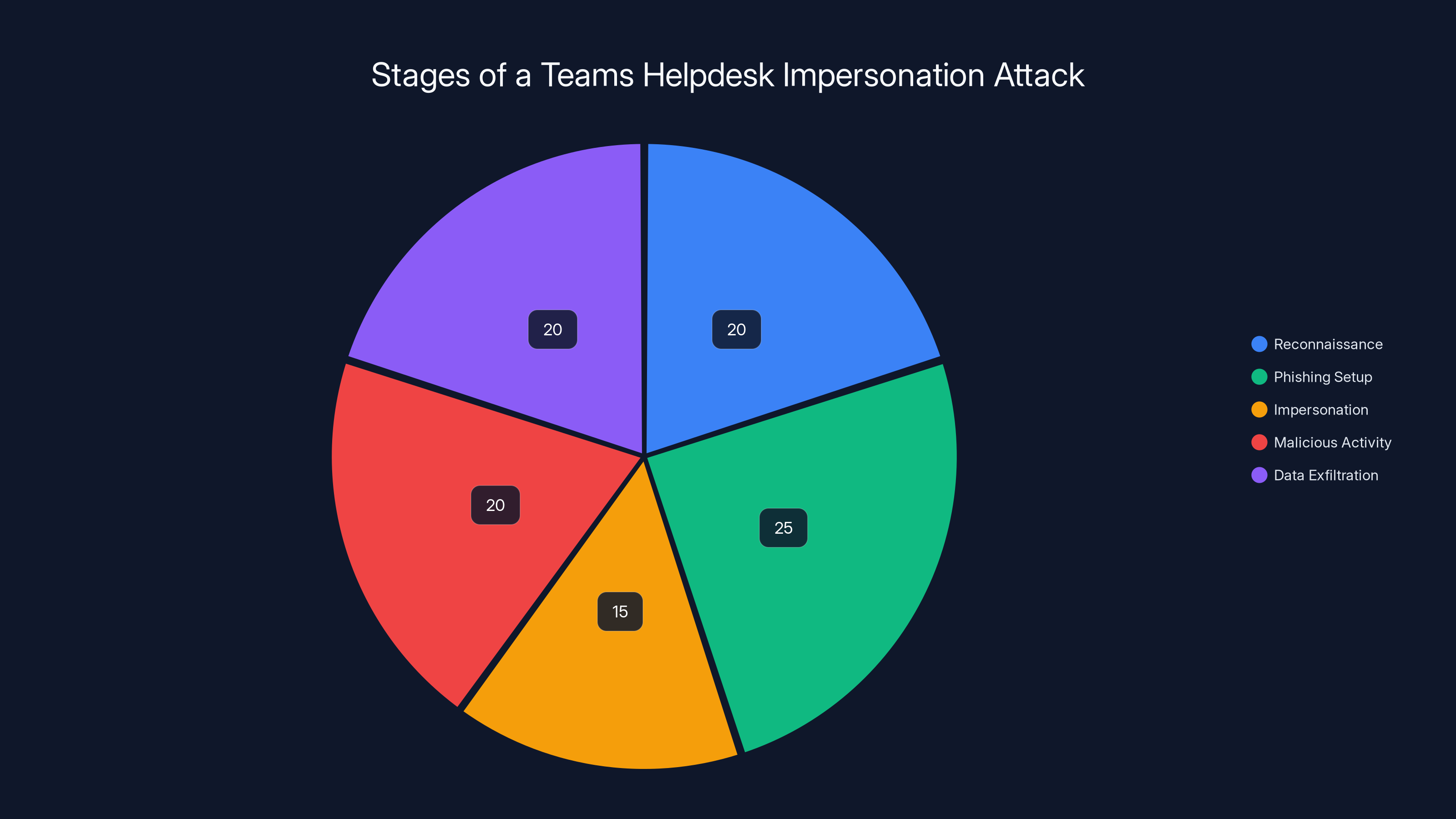
Estimated data shows that phishing setup and reconnaissance are the most effort-intensive stages in a Teams helpdesk impersonation attack.
The Anatomy of a Teams Helpdesk Impersonation Attack
How It Works
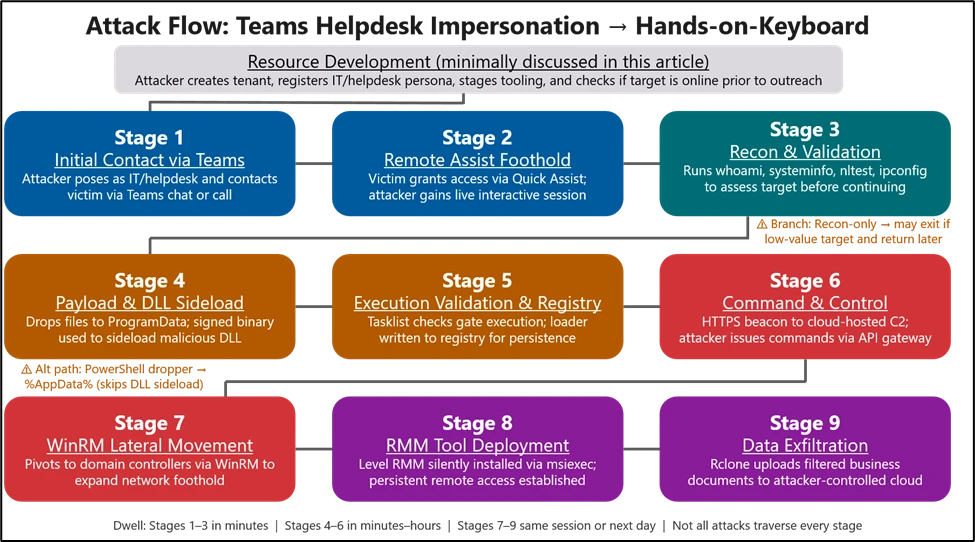
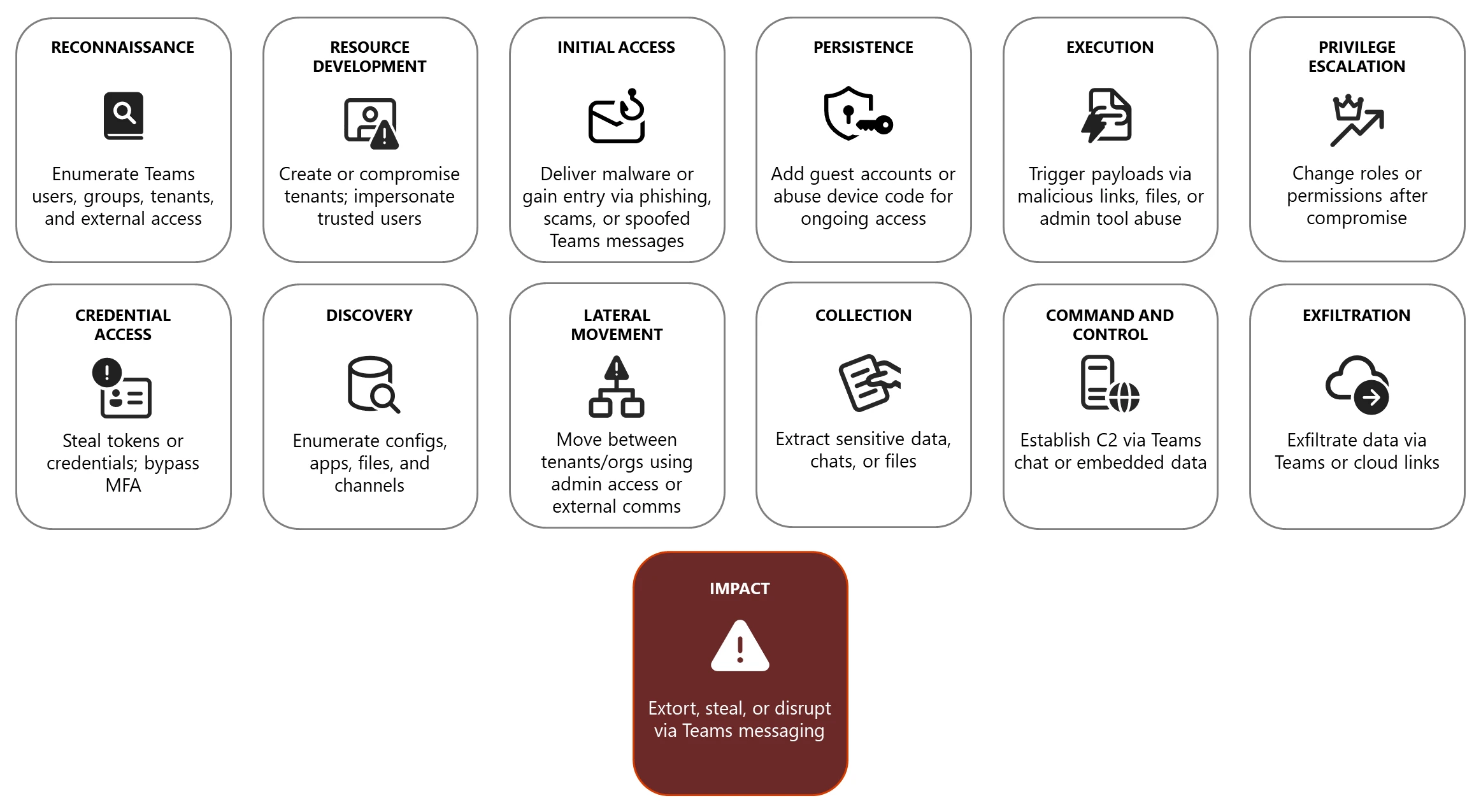
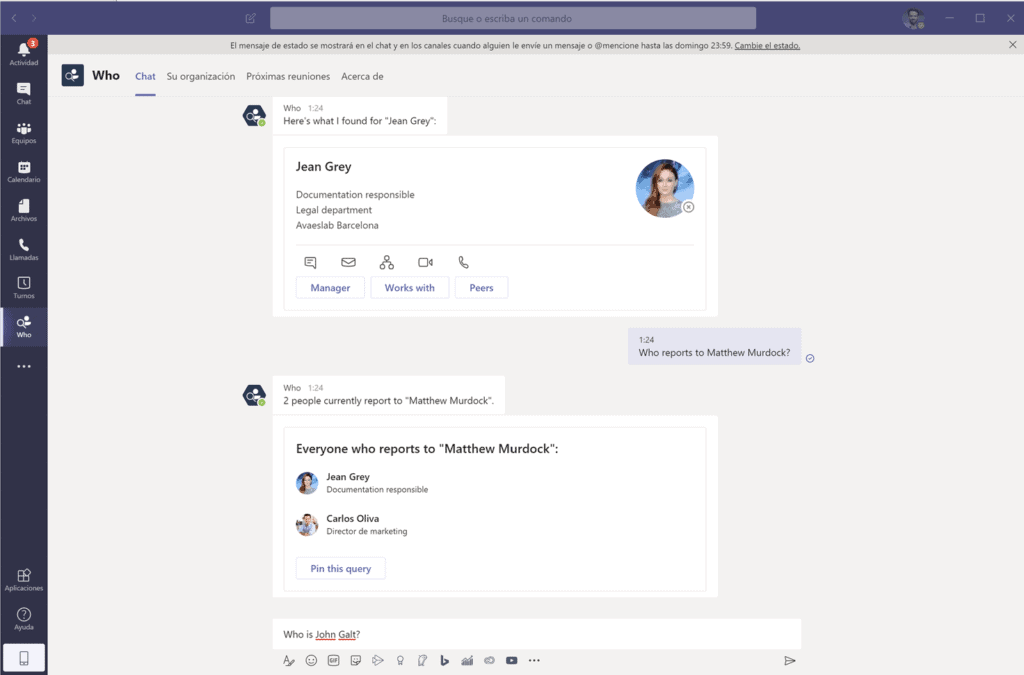
At the core, these attacks involve malicious actors posing as legitimate IT support staff within Microsoft Teams. By leveraging the cross-tenant chat feature, attackers can initiate conversations with employees under the guise of providing assistance. This approach is particularly effective because it capitalizes on the inherent trust employees have in their IT teams.
Key Steps in the Attack:
- Reconnaissance: Attackers gather information about the organization’s IT team and employees.
- Phishing Setup: Using spoofed emails or social engineering, attackers gain access to Teams.
- Impersonation: Attackers create fake IT profiles to interact with employees.
- Malicious Activity: Under the pretext of troubleshooting, attackers request remote access.
- Data Exfiltration: Once access is granted, attackers can install malware or extract sensitive data.
Why Teams?
Microsoft Teams is a popular choice for businesses worldwide due to its integration with the Microsoft 365 suite and its robust communication features. However, its widespread adoption also makes it an attractive target for cybercriminals looking to exploit its trust-based environment.
Example Scenario
Imagine this: You're working late, and an IT support message pops up on Teams. The 'technician' claims there's a critical issue affecting your account and requests immediate action. Trusting the familiar Teams interface, you comply, unknowingly granting access to a hacker. This scenario is all too common and underscores the need for vigilance.
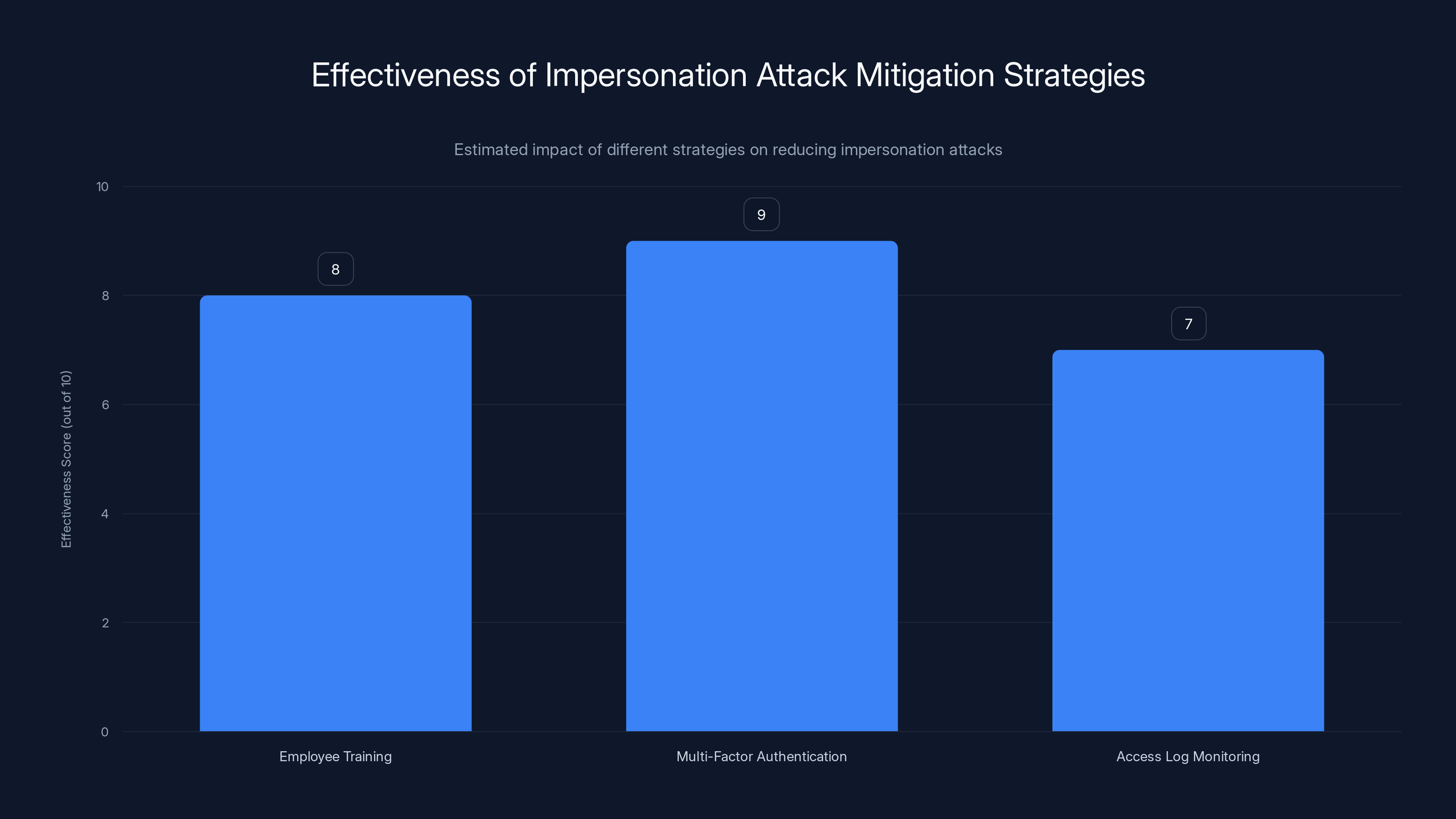
Multi-Factor Authentication (MFA) is estimated to be the most effective strategy for mitigating impersonation attacks, with a score of 9 out of 10. Employee training and access log monitoring also play crucial roles, scoring 8 and 7 respectively. Estimated data.
Best Practices for Mitigating Impersonation Attacks
1. Educate and Train Employees
Real talk: Your best defense is a well-informed team. Employees should be trained to recognize phishing attempts and verify the identities of IT personnel. Regular cybersecurity awareness training can significantly reduce the risk of successful attacks.
Training Tips:
- Conduct simulated phishing exercises.
- Provide clear guidelines for verifying IT requests.
- Encourage a culture of skepticism—if something feels off, it probably is.
2. Implement Multi-Factor Authentication (MFA)
MFA is a must-have in today’s threat landscape. By requiring multiple forms of verification, MFA adds a crucial layer of security that can thwart unauthorized access even if credentials are compromised.
MFA Setup:
- Use app-based authenticators for additional security.
- Encourage users to report any suspicious MFA requests.
3. Monitor and Audit Access Logs
Keeping an eye on access logs can help identify unusual activity early. Look for signs of unauthorized access or unusual login patterns, such as logins from unknown locations.
Tools for Monitoring:
- Utilize Microsoft’s built-in security tools for log analysis.
- Set up alerts for suspicious activity.
Common Pitfalls and How to Avoid Them
Over-Reliance on Technology
Technology is a powerful tool, but it’s not infallible. Relying solely on technological solutions without considering the human element can leave gaps in your security posture.
Solution: Balance technology with ongoing employee training and awareness.
Ignoring Red Flags
In many cases, attacks succeed because users ignore warning signs. Whether it’s a strange email address or an unusual request, these red flags should not be dismissed.
Solution: Foster a culture of reporting and verify all unusual requests, even from trusted sources.

Over-reliance on technology and ignoring red flags are common pitfalls, occurring in 70% and 60% of cases respectively. Estimated data based on typical security challenges.
Future Trends in Cybersecurity
As digital communication tools like Microsoft Teams become more integral to business operations, expect cyberattacks to become more sophisticated. AI-driven social engineering tactics and deepfake technology are likely to play a larger role in impersonation attacks.
Preparing for the Future
- Invest in AI-driven security tools: These can help detect and mitigate threats in real-time.
- Stay informed: Keep up with the latest cybersecurity trends and threat intelligence.
- Regularly update security protocols: Adapt to new threats as they emerge.

Conclusion: Taking Action
Here’s the bottom line: The threat of impersonation attacks on platforms like Microsoft Teams is real and growing. By implementing robust security measures, educating employees, and staying vigilant, organizations can protect themselves from these sophisticated attacks.
Remember, cybersecurity is not just the responsibility of IT—it's a team effort. Stay proactive, stay informed, and stay secure.
Use Case: Automate security protocol updates and employee training notifications with Runable to enhance your organizational security posture.
Try Runable For FreeFAQ
What are helpdesk impersonation attacks?
Helpdesk impersonation attacks involve cybercriminals posing as IT support to gain unauthorized access to systems.
How do attackers impersonate IT support on Microsoft Teams?
Attackers use the cross-tenant chat feature to pose as legitimate IT personnel, exploiting trust to request access.
What are the warning signs of an impersonation attack?
Unusual requests for information, unexpected remote access requests, and emails from unfamiliar addresses are key indicators.
How can organizations protect themselves from these attacks?
Implementing MFA, educating employees, and monitoring access logs are effective strategies to mitigate these attacks.
What role does employee training play in preventing cyber attacks?
Training helps employees recognize and respond appropriately to phishing attempts, significantly reducing the risk of successful attacks.
Why is MFA important in cybersecurity?
MFA adds an additional layer of security, making it more difficult for attackers to gain access even if passwords are compromised.
How can AI help in cybersecurity?
AI can analyze vast amounts of data to identify patterns and detect anomalies, improving threat detection and response times.
What future trends should organizations be aware of in cybersecurity?
As technology evolves, expect more sophisticated attacks utilizing AI-driven social engineering and deepfake technology.
Key Takeaways
- Cybercriminals are exploiting Microsoft Teams to impersonate IT support.
- Trust in digital communication platforms is being leveraged by attackers.
- Multi-factor authentication is critical for preventing unauthorized access.
- Employee training is essential for recognizing and preventing phishing attacks.
- Future attacks may utilize AI-driven social engineering tactics.
Related Articles
- Spotting the Spyware: How Modern Spies Are Weaponizing Phishing [2025]
- Troubleshooting Microsoft Teams Startup Issues: Causes, Solutions, and Future Trends [2025]
- They Built a Legendary Privacy Tool. Now They’re Sworn Enemies | WIRED
- Software 3.0: Coding Accelerated, But Delivery Still Lags [2025]
- When Robots Run: The Future of Racing and Robotics [2025]
- Quantum Computing Revolutionizes Genome Analysis: Faster DNA Insights [2025]
![Understanding and Mitigating Microsoft Teams Helpdesk Impersonation Attacks [2025]](https://tryrunable.com/blog/understanding-and-mitigating-microsoft-teams-helpdesk-impers/image-1-1776769444082.jpg)



