Spotting the Spyware: How Modern Spies Are Weaponizing Phishing [2025]
The email you trust could already be compromised. In today's digital world, phishing has become a significant threat, with cybercriminals utilizing advanced tactics to infiltrate personal and corporate systems. While phishing isn't new, its evolution has made it a powerful tool for modern spies.
TL; DR
- Phishing attacks have evolved with AI and deep fakes, making them harder to detect. According to a recent study, AI-driven phishing attacks are becoming increasingly sophisticated.
- Common tactics include spear phishing and whale phishing, targeting individuals based on their business roles. Microsoft's investigation into recent attacks highlights the targeted nature of these phishing attempts.
- Protective measures include multi-factor authentication and employee training. Bolster AI's new solution emphasizes the importance of these measures in combating AI-driven fraud.
- AI in cybersecurity offers both advantages and challenges. The dual nature of AI in cybersecurity is evident as it can be used to both enhance security and facilitate cyberattacks.
- Future trends suggest a rise in AI-driven phishing and biometric security. As noted in the Hacker News report, the integration of AI in phishing is expected to increase.
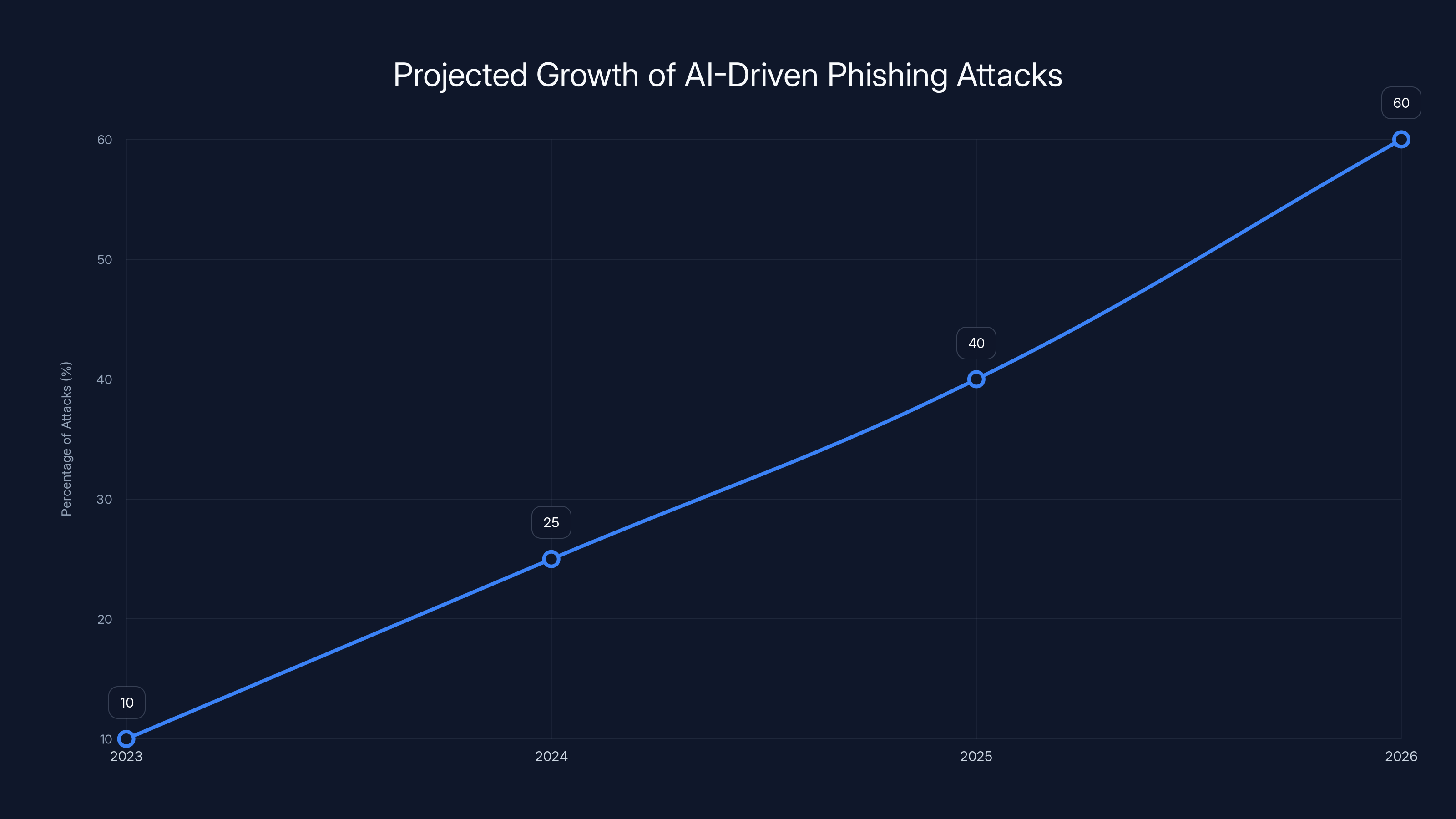
The percentage of phishing attacks using AI is projected to grow significantly, reaching 60% by 2026. (Estimated data)
Understanding Phishing
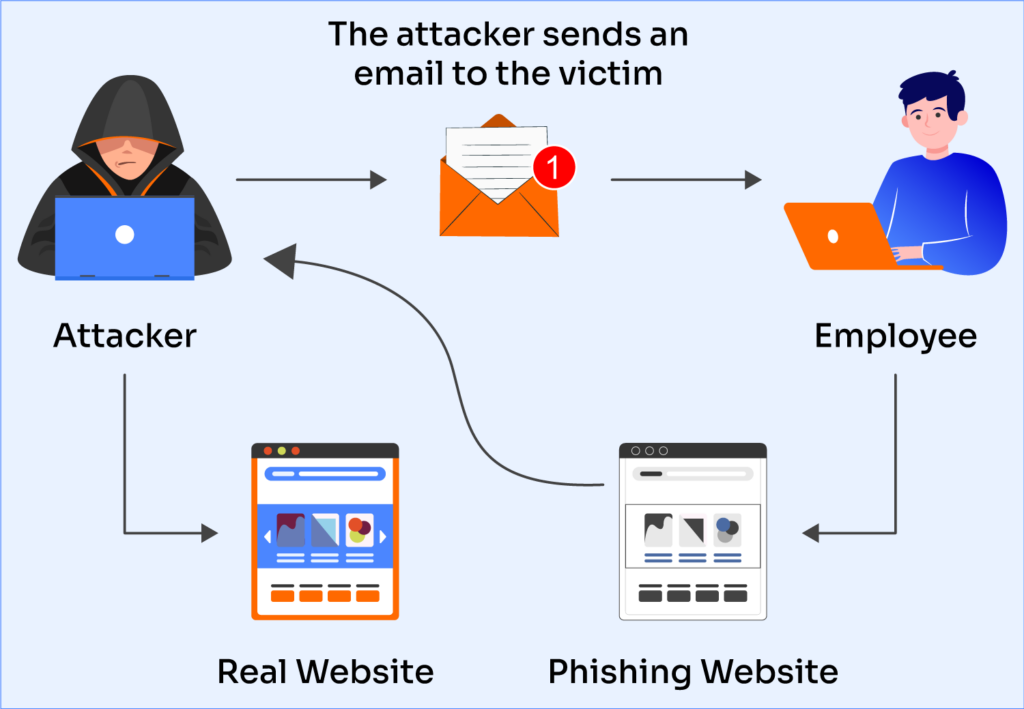
Phishing is a cybercrime where attackers impersonate legitimate organizations via email, text message, or other online communication to steal sensitive information. This often includes usernames, passwords, and financial details.
Types of Phishing Attacks
- Email Phishing: The most common form, where attackers send out mass emails pretending to be from reputable sources.
- Spear Phishing: Targeted attacks aimed at specific individuals or organizations. These are highly personalized and difficult to detect.
- Whale Phishing: Targets high-profile individuals such as CEOs or executives. The stakes are higher, and the tactics are more sophisticated.
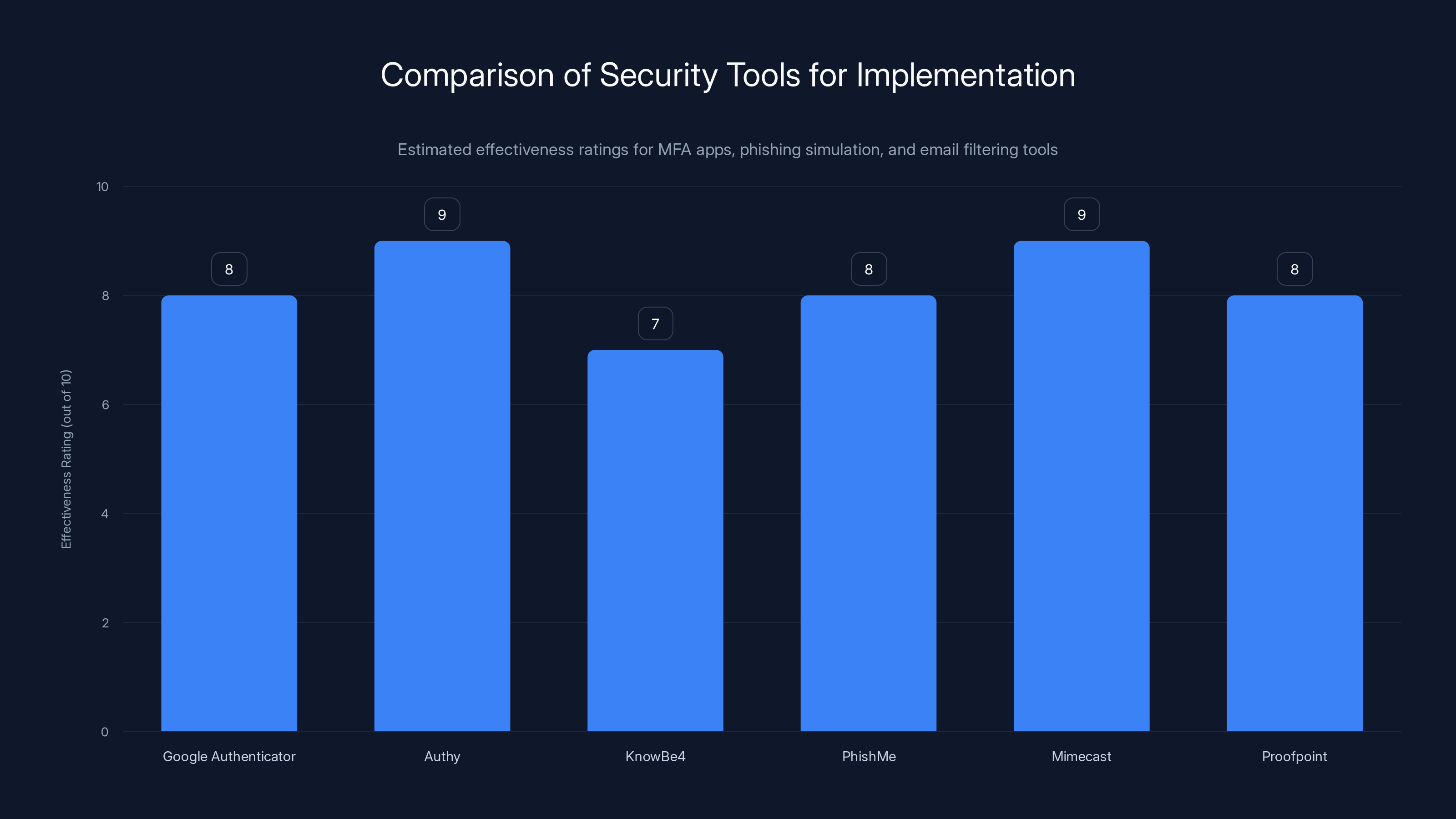
Estimated effectiveness ratings show Authy and Mimecast as leading tools in their categories for security implementation. Estimated data.
How Phishing Has Evolved
Phishing techniques have evolved significantly, leveraging advancements in technology to create more convincing attacks.
AI and Deep Fakes
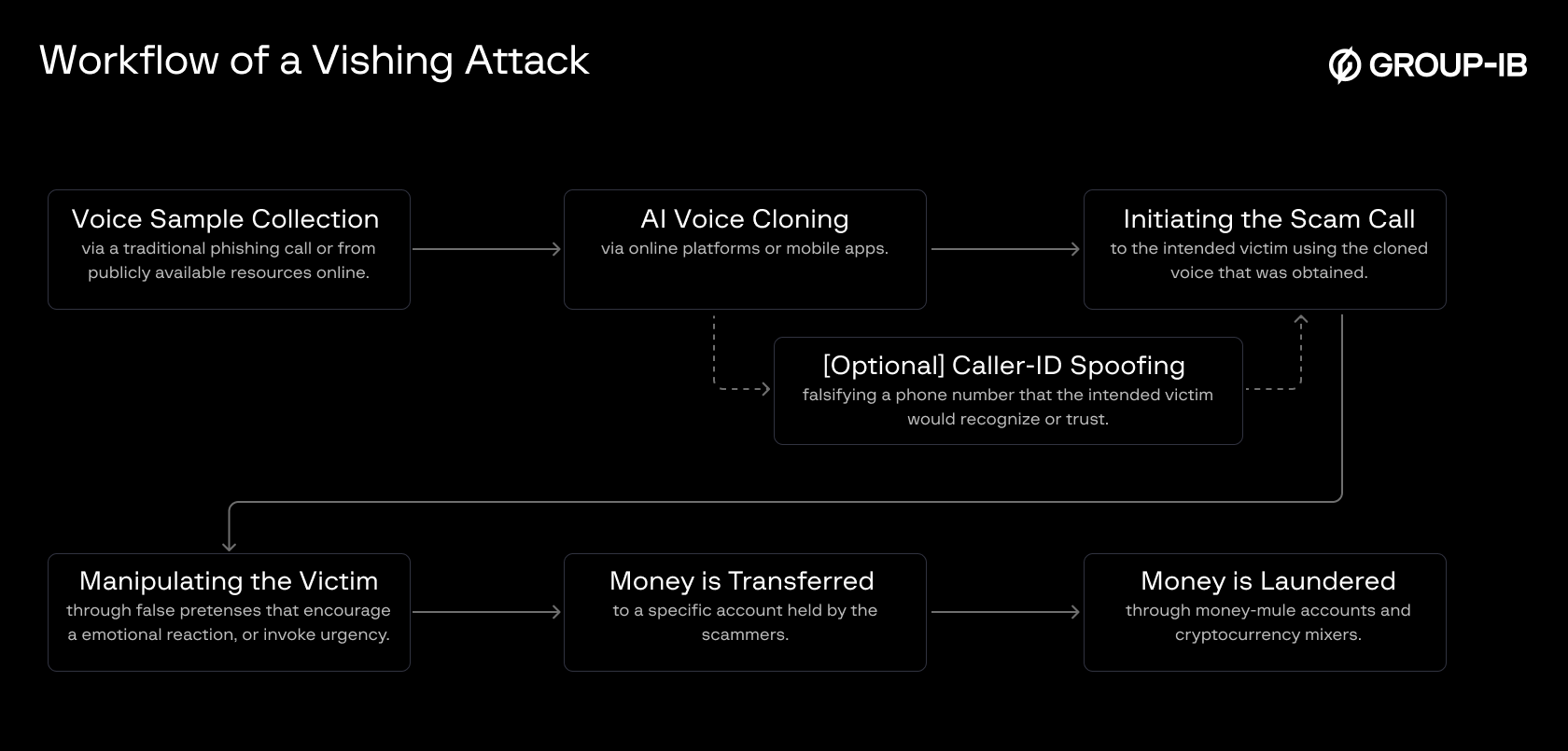
Modern phishing attacks often use AI to enhance their effectiveness. AI can analyze vast amounts of data to personalize phishing emails, making them more believable. AI voice cloning is one such technology being exploited in phishing schemes.
Deep fakes, or synthetic media where a person in an existing image or video is replaced with someone else's likeness, are also being used in phishing campaigns to create convincing fake videos or voice messages.
Example: An executive receives a video message from what appears to be their CEO, instructing them to transfer funds to a new account.
Common Phishing Tactics
Phishers employ a range of tactics to deceive their targets. Here are some of the most common:
- Spoofed Emails: Emails that appear to come from legitimate sources.
- Malicious Links: URLs that lead to fake websites designed to steal login credentials.
- Attachment Malware: Files attached to emails that install malware when opened.
- Urgency and Fear: Messages that create a sense of urgency or fear to prompt immediate action.
Real-World Use Case
A recent attack involved a fake email from a well-known bank, urging recipients to update their security information to prevent account suspension. The email contained a link to a phishing site that mimicked the bank's login page.


Spoofed emails are the most common phishing tactic, estimated to account for 40% of attacks. Estimated data.
Best Practices for Phishing Prevention
Multi-Factor Authentication (MFA)
Enabling MFA adds an extra layer of security by requiring a second form of identification, such as a text message code or fingerprint scan, in addition to a password.
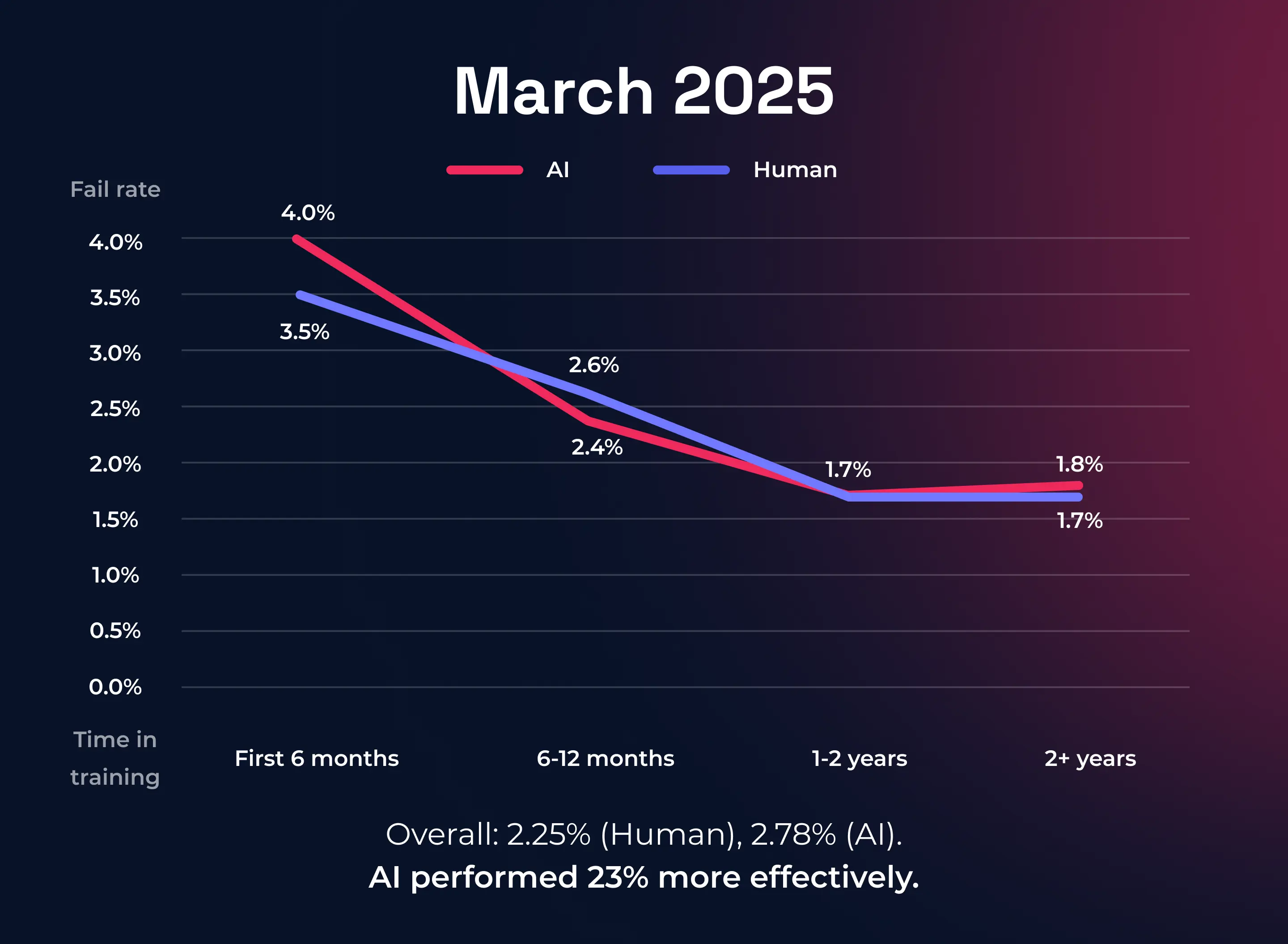
Employee Training and Awareness
Regular training sessions can help employees recognize phishing attempts and understand the importance of cybersecurity.
Email Filtering Software
Advanced email filters can help identify and block phishing emails. These tools analyze emails for suspicious content and block them before they reach the inbox.
Regular Security Audits
Conducting regular security audits can help identify vulnerabilities in your system and ensure that protective measures are up-to-date.
The Role of AI in Cybersecurity
AI is a double-edged sword in cybersecurity. While it can be used to enhance security measures, it can also be exploited by cybercriminals.
AI for Defense
AI can automate threat detection, analyze patterns in cyberattacks, and predict future threats. Machine learning algorithms can learn from past incidents, improving over time.
AI for Offense
Conversely, cybercriminals use AI to automate attacks, making them more efficient and harder to detect. AI can create more personalized phishing emails and craft more convincing deep fakes.

Future Trends in Phishing
Rise of AI-Driven Phishing
As AI technology advances, we can expect more sophisticated phishing attacks that are harder to detect and prevent.
Increased Use of Biometric Security
Biometric security measures, such as facial recognition and fingerprint scanning, are becoming more prevalent. These can offer a higher level of security against phishing attacks.
Enhanced Threat Intelligence
Organizations are increasingly using threat intelligence platforms to share information about phishing attacks and collaborate on defense strategies.
Practical Implementation Guide
Setting Up Multi-Factor Authentication
- Choose an Authenticator App: Google Authenticator, Authy, etc.
- Enable MFA on Accounts: Access your account settings and activate MFA.
- Secure Backup Codes: Store backup codes in a secure location.
Conducting Phishing Simulations
- Select a Simulation Tool: Use platforms like Know Be 4 or Phish Me.
- Design Realistic Scenarios: Create phishing emails similar to those your organization might face.
- Analyze Results: Evaluate the effectiveness and areas for improvement.
Implementing Email Filtering
- Choose a Filtering Solution: Consider options like Mimecast or Proofpoint.
- Set Filtering Rules: Define what constitutes suspicious content.
- Monitor and Adjust: Regularly review filtering effectiveness and make necessary adjustments.
Common Pitfalls and Solutions
Overconfidence in Technology
Relying solely on technology without proper employee training can leave gaps in your security strategy. Ensure that all employees are aware of phishing threats and know how to respond.
Ignoring Smaller Phishing Attempts
Organizations often focus on large-scale attacks, ignoring smaller phishing attempts. Even minor breaches can lead to significant damage if not addressed promptly.
Failure to Update Security Measures
Cybersecurity is a dynamic field. Regularly update your security measures to keep up with the latest threats.
Conclusion
Phishing remains a formidable threat in the digital age, evolving with advancements in AI and technology. By understanding modern phishing tactics and implementing robust security measures, individuals and organizations can significantly reduce their risk of falling victim to these attacks.
Stay informed, stay vigilant, and be prepared to adapt to the ever-changing landscape of cybersecurity.
Use Case: Automate your cybersecurity training with Runable's AI-powered solutions.
Try Runable For Free
Key Takeaways
- Phishing tactics are evolving with AI and deep fakes.
- Multi-factor authentication enhances security.
- Employee awareness is crucial for phishing prevention.
- AI-driven phishing attacks are on the rise.
- Biometric security offers a higher level of protection.
- Regular security audits help identify vulnerabilities.
Related Articles
- When Robots Run: The Future of Racing and Robotics [2025]
- Solving Rare Earth Processing Bottlenecks: DARPA’s Smash Program and the Future of U.S. Independence [2025]
- Johny Srouji's Ascension: Leading Apple's Hardware Revolution [2025]
- AI's Fascination with Stonehenge: Unraveling the Myths and Realities [2025]
- Understanding the Vercel Hack: Lessons and Best Practices [2025]
- Maximizing Email Marketing ROI: Strategies and Insights [2025]
FAQ
What is Spotting the Spyware: How Modern Spies Are Weaponizing Phishing [2025]?
The email you trust could already be compromised
What does tl; dr mean?
In today's digital world, phishing has become a significant threat, with cybercriminals utilizing advanced tactics to infiltrate personal and corporate systems
Why is Spotting the Spyware: How Modern Spies Are Weaponizing Phishing [2025] important in 2025?
While phishing isn't new, its evolution has made it a powerful tool for modern spies
How can I get started with Spotting the Spyware: How Modern Spies Are Weaponizing Phishing [2025]?
- Phishing attacks have evolved with AI and deep fakes, making them harder to detect
What are the key benefits of Spotting the Spyware: How Modern Spies Are Weaponizing Phishing [2025]?
- Common tactics include spear phishing and whale phishing, targeting individuals based on their business roles
What challenges should I expect?
- Protective measures include multi-factor authentication and employee training
![Spotting the Spyware: How Modern Spies Are Weaponizing Phishing [2025]](https://tryrunable.com/blog/spotting-the-spyware-how-modern-spies-are-weaponizing-phishi/image-1-1776765878272.jpg)



