Understanding and Mitigating New Rowhammer Attacks on Nvidia GPUs [2025]
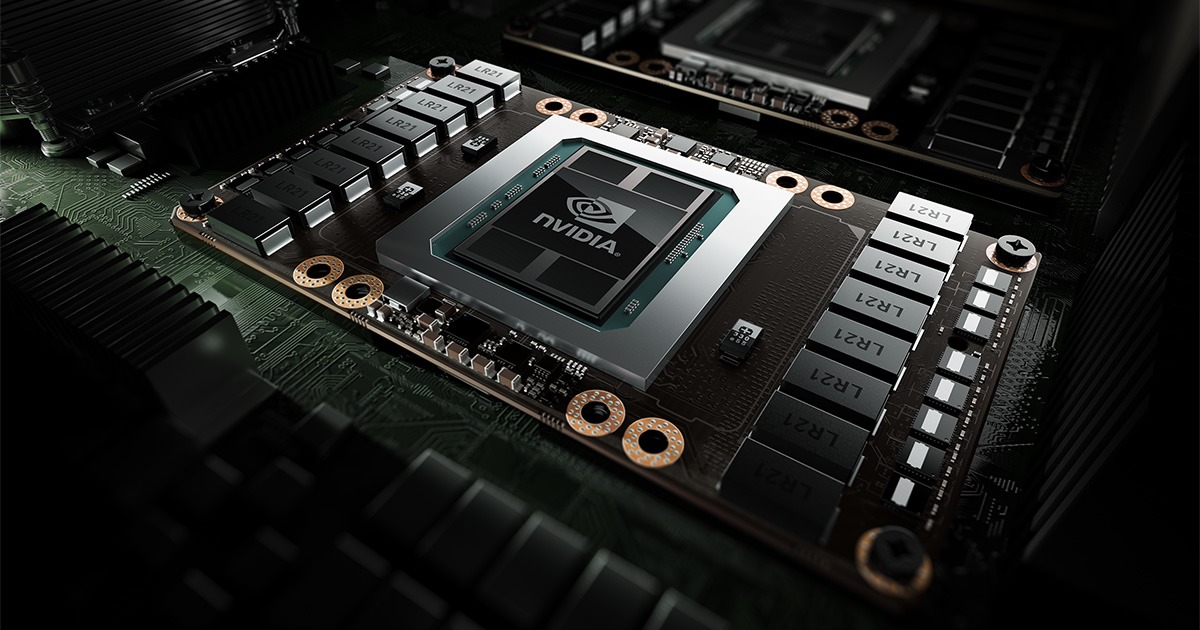
Last month, a researcher uncovered new vulnerabilities in Nvidia GPUs that could potentially give attackers complete control over machines. This isn't just a theoretical risk—it's a tangible threat, especially in high-performance computing environments where GPUs are shared among multiple users.
TL; DR
- New Rowhammer attacks: Target Nvidia GPUs, exploiting memory vulnerabilities.
- GDDRHammer and Ge Forge: Two attack vectors identified.
- Cloud environments at risk: Shared GPU use increases vulnerability.
- Mitigation strategies: Involves hardware updates and software patches.
- Future trends: Emphasis on developing more resilient hardware.
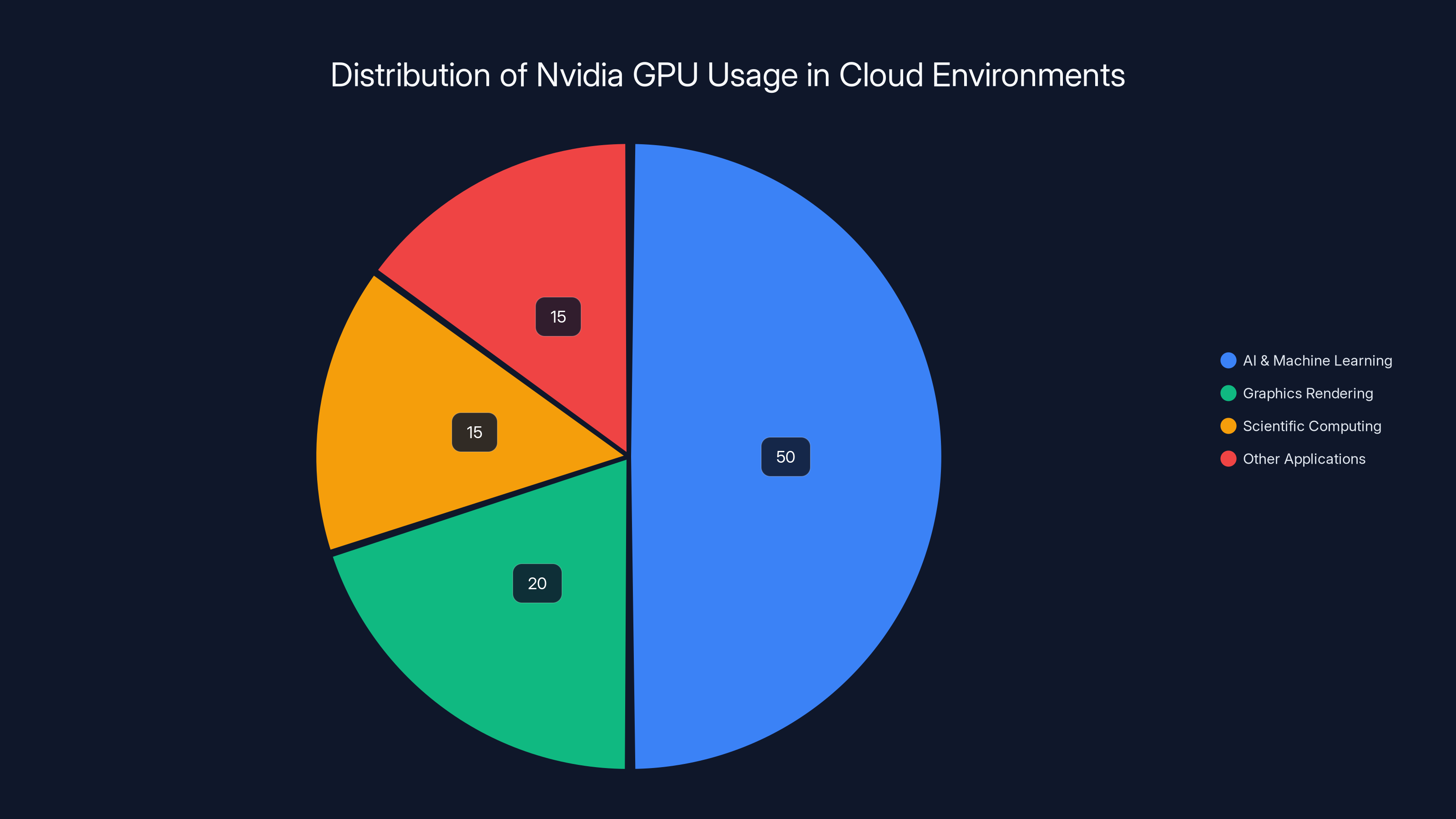
Estimated data shows that AI & Machine Learning dominate Nvidia GPU usage in cloud environments, accounting for about 50% of the total usage.
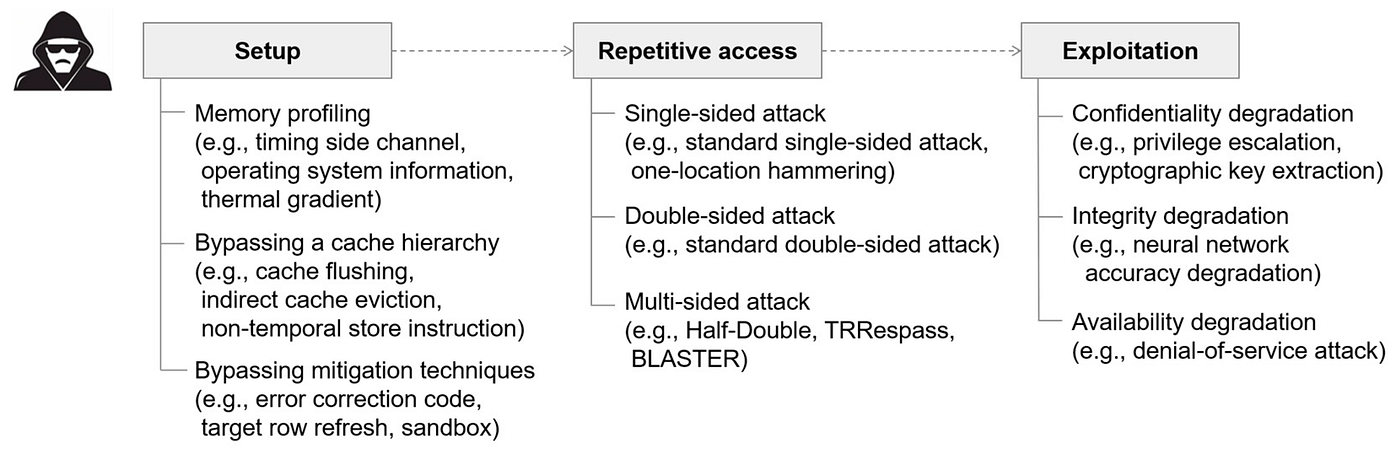
The Rise of Rowhammer Attacks
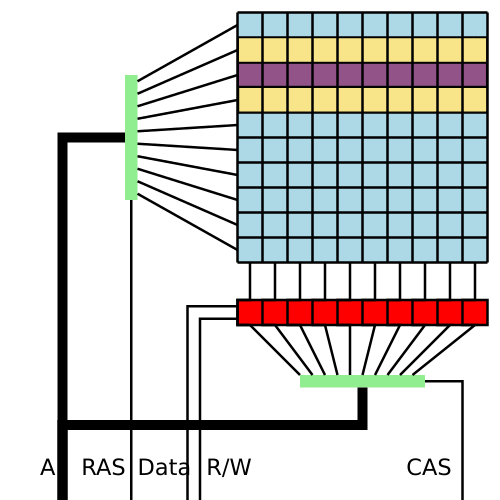
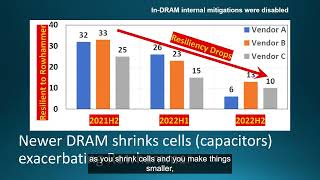
Rowhammer attacks have been around for nearly a decade, but their evolution continues to pose serious threats to modern computing systems. Initially discovered in DRAM chips, Rowhammer exploits the physical properties of memory chips to induce bit flips—where a '0' changes to a '1' or vice versa—by rapidly accessing memory rows.
How Rowhammer Works
The basic premise of a Rowhammer attack is to cause electrical disturbances in DRAM cells by repeatedly accessing—or "hammering"—adjacent rows. This rapid succession causes voltage fluctuations that can inadvertently flip bits in nearby rows.
Example: Imagine a library where pulling books from one shelf causes books on the neighboring shelf to fall out of place. Similarly, hammering one row in memory can cause adjacent rows to lose data integrity.
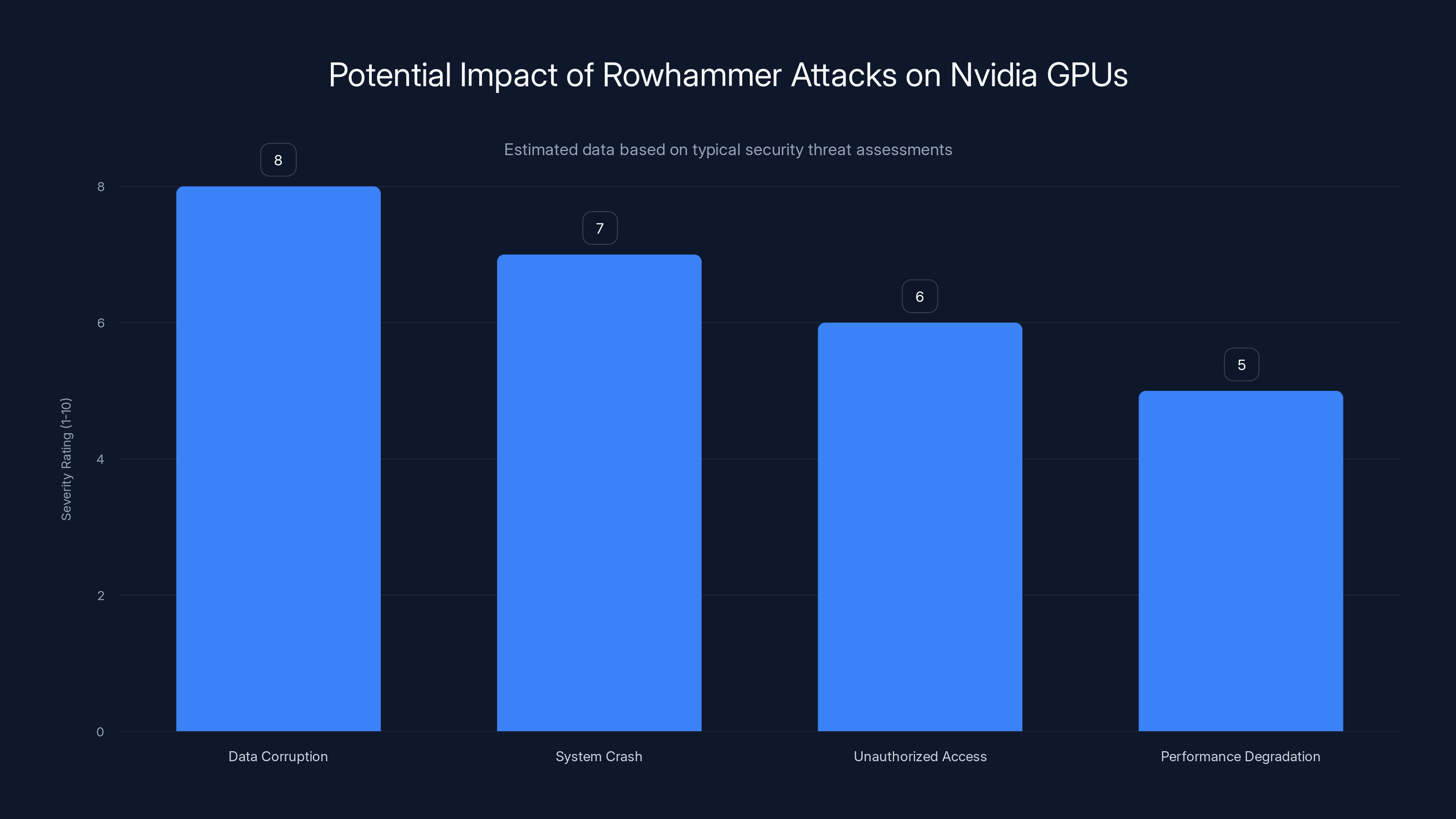
Rowhammer attacks on Nvidia GPUs can lead to severe data corruption and system crashes, with an estimated severity rating of 8 and 7 respectively. Estimated data.
New Threat Vectors: GDDRHammer and Ge Forge
The latest research highlights two new Rowhammer attack vectors targeting Nvidia GPUs: GDDRHammer and Ge Forge.
GDDRHammer
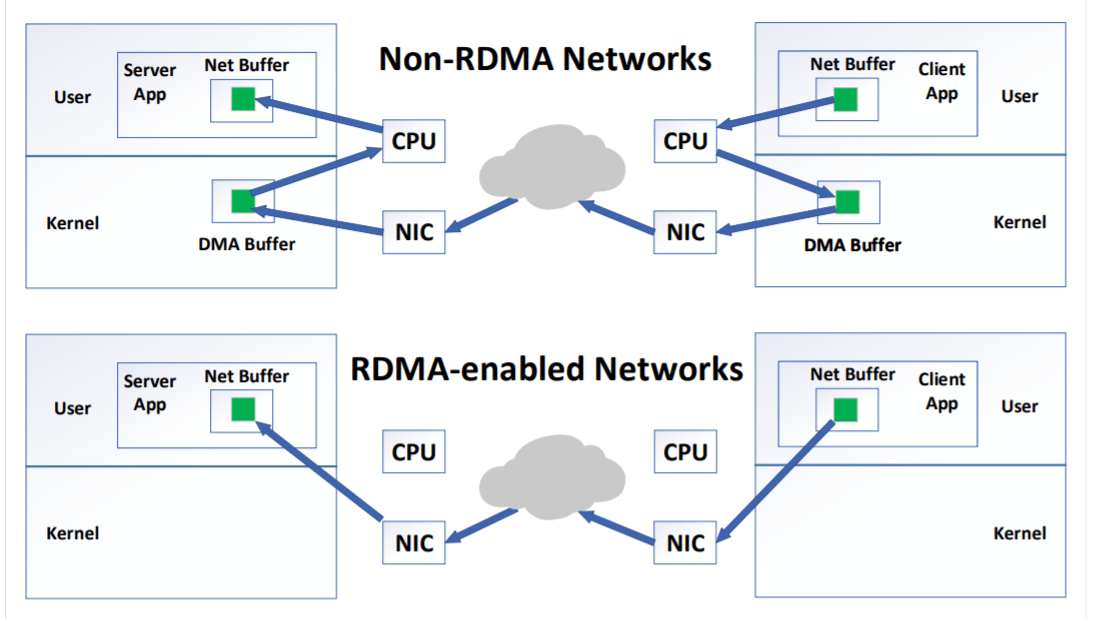
GDDRHammer specifically targets GDDR memory used in Nvidia GPUs. By exploiting the high-density memory configuration, attackers can induce bit flips that compromise the integrity of the data processed by the GPU.
Ge Forge
Ge Forge, on the other hand, targets the CPU by leveraging vulnerabilities in the GPU's memory management. This method allows attackers to execute privileged commands, effectively taking over the host machine.
Why Nvidia GPUs?
Nvidia GPUs are the backbone of many AI and machine learning applications due to their superior processing power. However, their widespread use in cloud environments makes them particularly susceptible to these attacks.
The Cloud Conundrum
In cloud settings, high-performance GPUs are often shared among multiple users to maximize resource utilization. This shared environment creates an ideal scenario for attackers to exploit Rowhammer vulnerabilities, as they can access the same physical hardware simultaneously with other users.
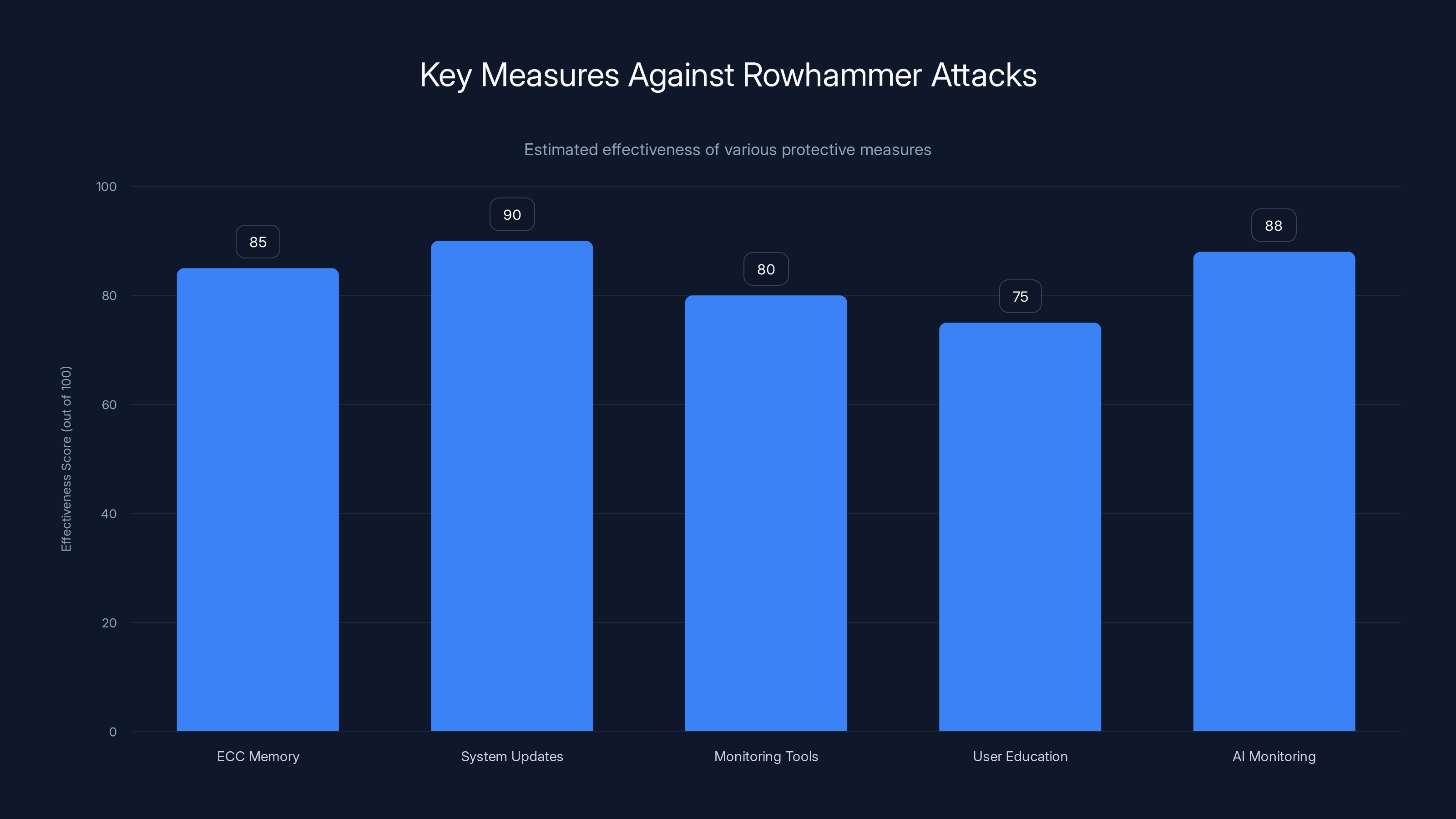
Estimated data shows that system updates and AI monitoring are among the most effective measures against Rowhammer attacks, highlighting the importance of proactive security strategies.
Real-World Implications
The potential impact of these attacks is significant. By taking control of a machine, an attacker can:
- Access sensitive data: Retrieve user data stored on the machine.
- Disrupt operations: Cause system crashes or degrade performance.
- Spread malware: Use the compromised machine to propagate malicious software.

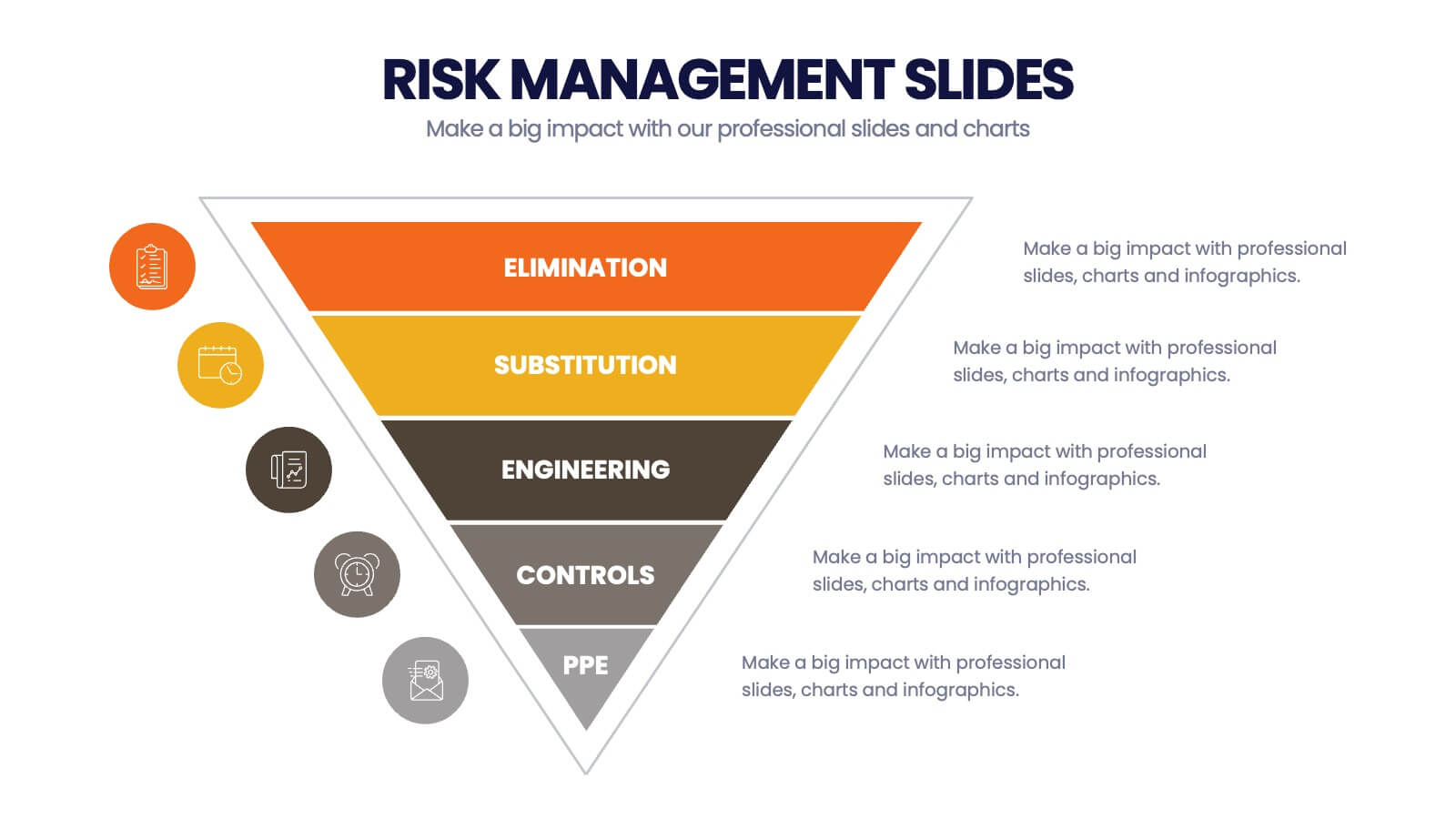
Mitigation and Defense Strategies
Hardware-Based Solutions
One of the primary defenses against Rowhammer attacks is to improve the physical design of memory chips. This includes implementing error-correcting code (ECC) memory that can detect and correct single-bit errors.
Software Patches and Updates
Software updates are crucial in defending against these vulnerabilities. Nvidia and other manufacturers regularly release patches to address known security issues. Keeping systems updated is a fundamental step in security hygiene.
Monitoring and Detection Tools
Deploying monitoring tools that can detect unusual memory access patterns is another effective strategy. These tools can flag potential Rowhammer attacks in real-time, allowing for immediate response.
Practical Implementation Guide
Step-by-Step Protection
- Upgrade Hardware: If possible, use ECC memory to mitigate bit flip errors.
- Regular Updates: Ensure all systems are running the latest firmware and driver updates.
- Install Monitoring Tools: Use software that detects abnormal memory access patterns.
- User Education: Train users on recognizing phishing attempts and other social engineering tactics.
- Access Controls: Limit user permissions to reduce the impact of potential attacks.
Common Pitfalls
Ignoring Updates
One of the biggest mistakes companies make is failing to regularly update their systems. This can leave known vulnerabilities unpatched, making systems easy targets.
Overlooking User Education
Even the most secure systems can be compromised through human error. Educating users about security best practices is critical.
Future Trends
As memory technology continues to evolve, so too will the methods used by attackers. The focus will likely shift towards developing more resilient hardware capable of withstanding such attacks.
Recommendations for the Future
- Invest in Research: Support initiatives focused on developing Rowhammer-resistant memory.
- Collaborate with Industry: Work with other companies to share information about vulnerabilities and mitigation strategies.
- Adopt AI Solutions: Utilize AI-driven monitoring solutions to detect anomalies faster.
Conclusion
Rowhammer attacks on Nvidia GPUs represent a significant threat to modern computing environments. By understanding these vulnerabilities and implementing comprehensive mitigation strategies, organizations can protect their systems from potential exploitation.
Use Case: Automate your security monitoring with AI to detect potential Rowhammer attacks in real-time.
Try Runable For Free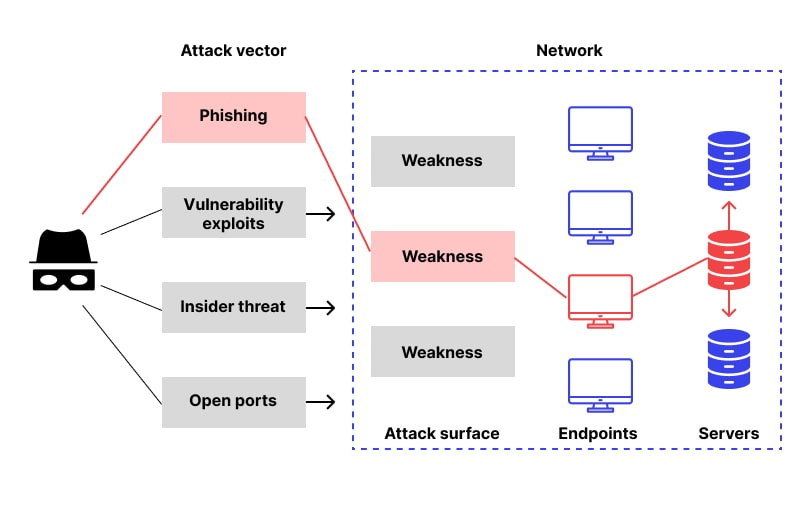
FAQ
What is a Rowhammer attack?
A Rowhammer attack is a type of cyberattack that exploits the physical properties of memory chips to induce bit flips, potentially compromising system integrity.
How do Rowhammer attacks target Nvidia GPUs?
These attacks exploit vulnerabilities in the GPU's memory to gain control over the host machine, often targeting shared cloud environments where GPUs are used by multiple users.
What are the implications of these attacks?
Successful attacks can lead to unauthorized access to sensitive data, system disruptions, and the spread of malware.
How can organizations protect against Rowhammer attacks?
Organizations can mitigate risks by using ECC memory, keeping systems updated, deploying monitoring tools, and educating users on security best practices.
What are the future trends in combating Rowhammer attacks?
Future trends include developing more resilient hardware, collaborating with industry peers, and adopting AI-driven monitoring solutions.
Why are shared cloud environments particularly vulnerable?
The shared nature of cloud environments means multiple users can access the same physical hardware, increasing the risk of exploitation.
How important are software updates in preventing these attacks?
Software updates are crucial as they address known vulnerabilities, making it harder for attackers to exploit systems.
Can AI help in detecting Rowhammer attacks?
Yes, AI can be used to monitor and detect unusual patterns in memory access that may indicate a Rowhammer attack, allowing for quicker response times.
Key Takeaways
- New Rowhammer attacks target Nvidia GPUs exploiting memory vulnerabilities.
- GDDRHammer and GeForge are key attack vectors compromising cloud environments.
- Mitigation involves hardware updates, software patches, and user education.
- Future trends focus on resilient hardware and AI-driven monitoring solutions.
- Regular system updates and ECC memory are critical in defending against these threats.
- Shared cloud environments are particularly vulnerable to Rowhammer attacks.
- AI can enhance detection of Rowhammer attacks through real-time monitoring.
Related Articles
- Introducing Proton Meet: A New Era of Secure Video Conferencing [2025]
- Microsoft's Bold Move: Three New Foundational AI Models [2025]
- Google Announces Gemma 4 AI Models with Apache 2.0 License [2025]
- PS5 Pro's Next-Gen PSSR Tech Transforms Assassin’s Creed Shadows [2025]
- Apple's Focused Innovation: What Tim Cook's Approach Means for the Future [2025]
- Unlocking the Best VPN Deals of 2025: Expert Guide to Maximizing Savings
![Understanding and Mitigating New Rowhammer Attacks on Nvidia GPUs [2025]](https://tryrunable.com/blog/understanding-and-mitigating-new-rowhammer-attacks-on-nvidia/image-1-1775151302040.jpg)



