How Emojis Are Reshaping Cybercrime Tactics: A Deep Dive [2025]
Introduction
In the digital arms race between cybersecurity experts and cybercriminals, innovation knows no bounds. The latest twist? Emojis. While these colorful symbols have been a staple of digital communication for years, their role in cybercrime is a growing concern. Cybercriminals are now using emojis to obfuscate communication, evade detection, and orchestrate illicit activities. But what does this mean for the future of cybersecurity?
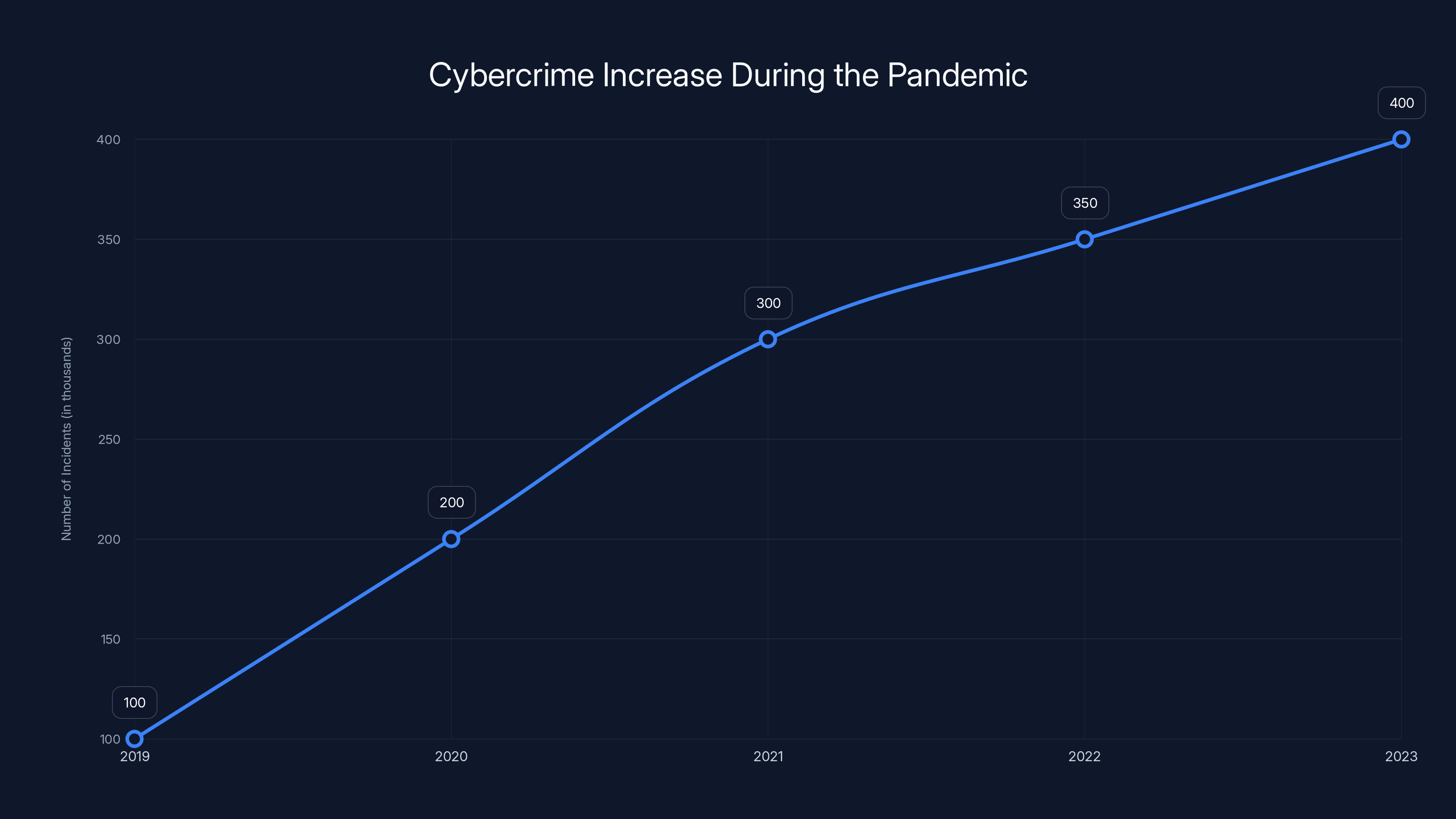
Cybercrime incidents have surged by an estimated 300% since the onset of the pandemic, highlighting the increased vulnerabilities due to remote work. (Estimated data)
TL; DR
- Emojis as Tools: Cybercriminals use emojis to obscure keywords and evade detection.
- Layered Obfuscation: This technique adds a layer of complexity, making it harder for traditional filters to flag suspicious activity.
- Evolution of Tactics: The trend reflects a broader shift towards more sophisticated evasion techniques.
- Challenges for Security: New methodologies are required to detect and decode these tactics effectively.
- Future Implications: As technology evolves, so too will the methods criminals use to exploit it.
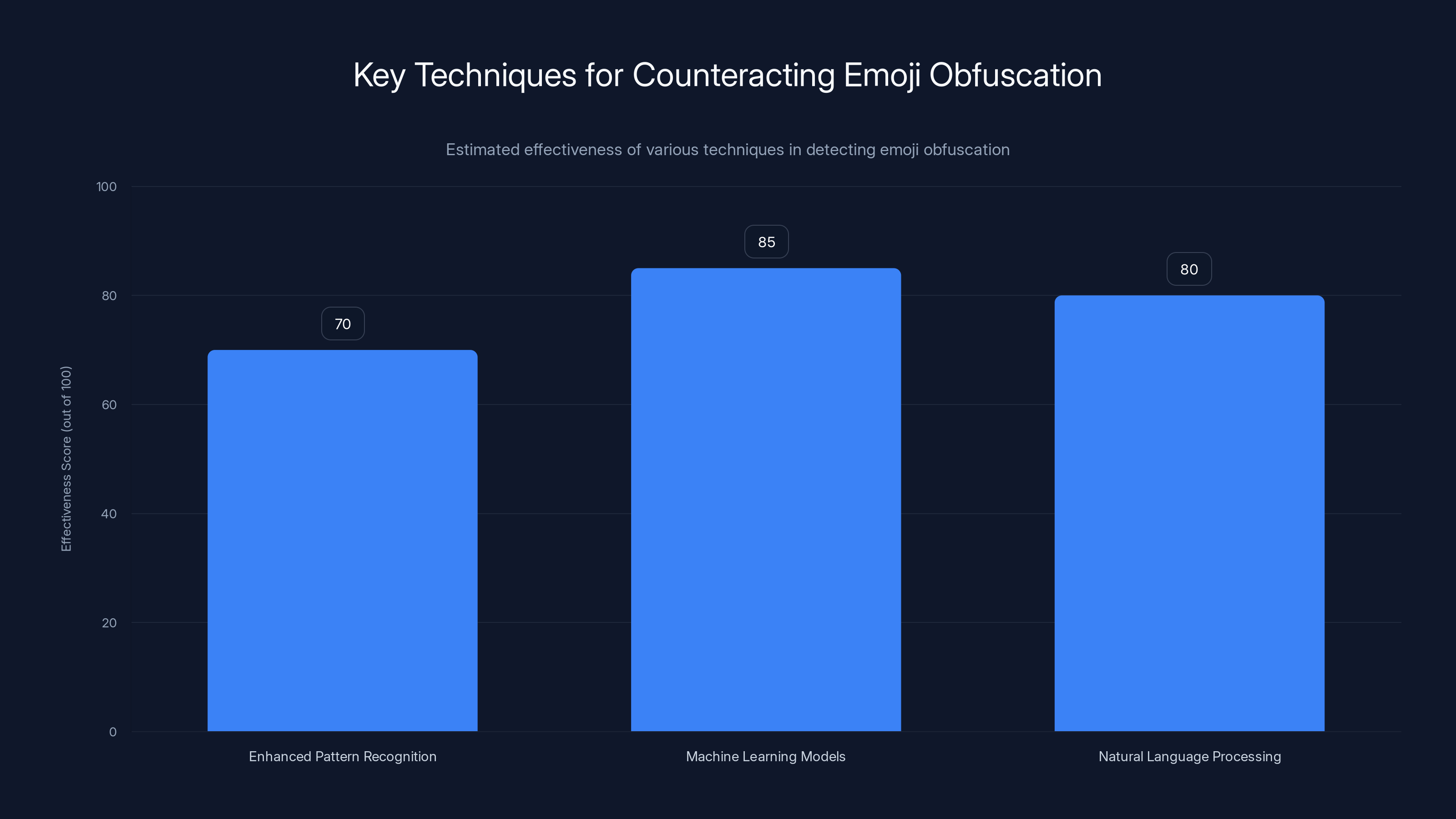
Machine learning models are estimated to be the most effective in detecting emoji obfuscation, followed closely by NLP techniques. Estimated data.
The Rise of Emoji-Based Obfuscation
What’s Happening?
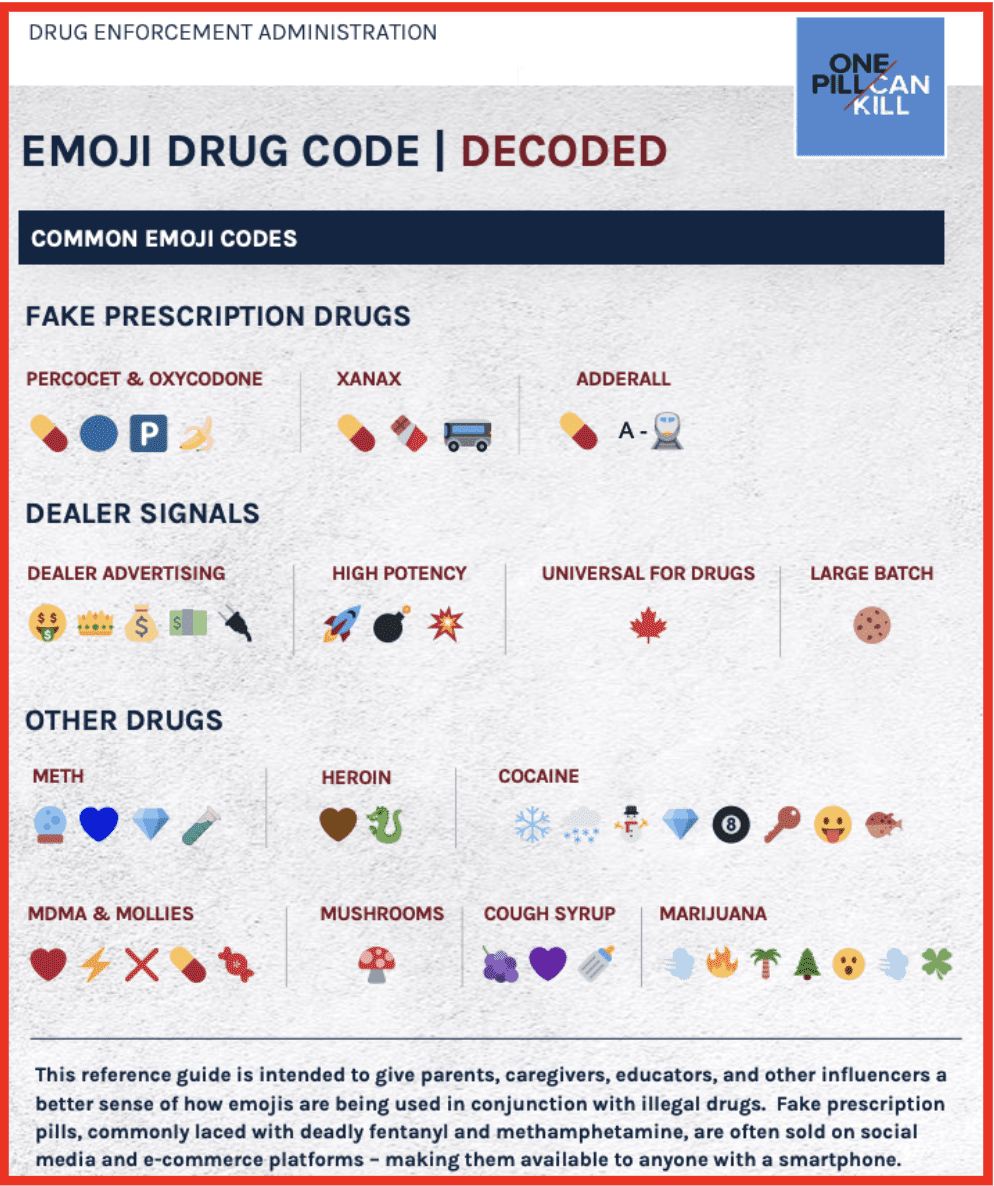
In recent years, cybercriminals have increasingly turned to emojis as a means of communication. The colorful icons, typically associated with lighthearted exchanges, are now being co-opted to replace critical keywords—like "credit card" or "password"—in discussions on illicit forums.
Imagine a conversation where the 💳 emoji replaces the term "credit card." In such scenarios, automated monitoring systems, which rely on keyword detection, may overlook these discussions entirely.
How Does It Work?
The mechanics are surprisingly simple yet effective. Cybercriminals use emojis to replace sensitive words, sidestepping keyword-based filters. This layered form of obfuscation complicates the task of identifying malicious conversations.
Consider this example:
- Traditional Message: “Selling credit card info, contact for details.”
- Obfuscated Message: “Selling 💳 info, contact for details.”
The emoji serves as a substitute, effectively bypassing keyword detection and allowing illicit communications to proceed undetected.
Technical Details: Why Emojis Work
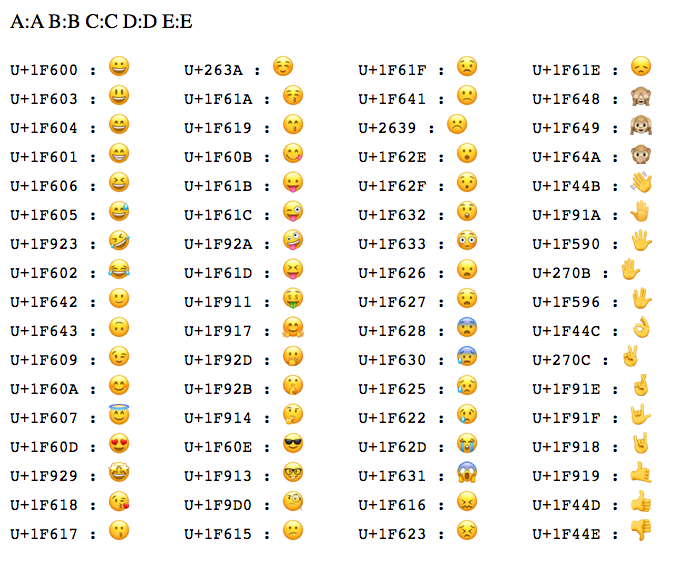
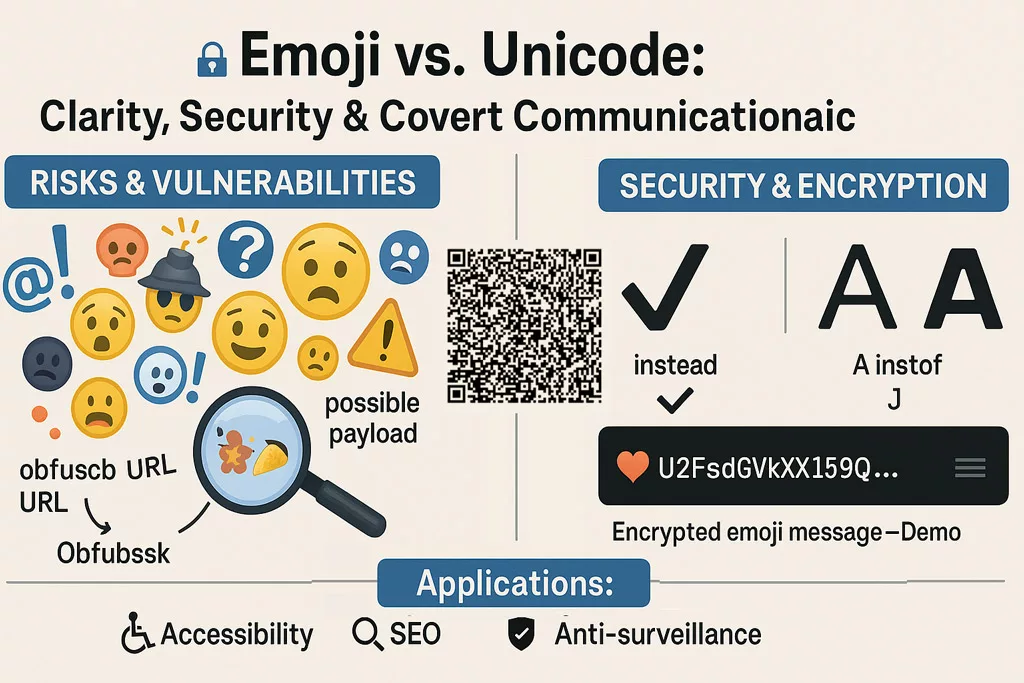
Unicode and Encoding
Emojis work as a tool for obfuscation largely due to Unicode encoding. Each emoji is represented by a unique Unicode sequence, allowing it to function as a stand-in for words or phrases. This encoding is consistent across platforms, ensuring that the message is perceived the same way by all parties involved.
Evasion of Traditional Filters
Most conventional detection systems rely heavily on keyword matching to flag suspicious content. Emojis circumvent this by being non-textual in nature. While a word like "card" might trigger an alert, the use of 💳 will not, as it does not match any traditional keyword.
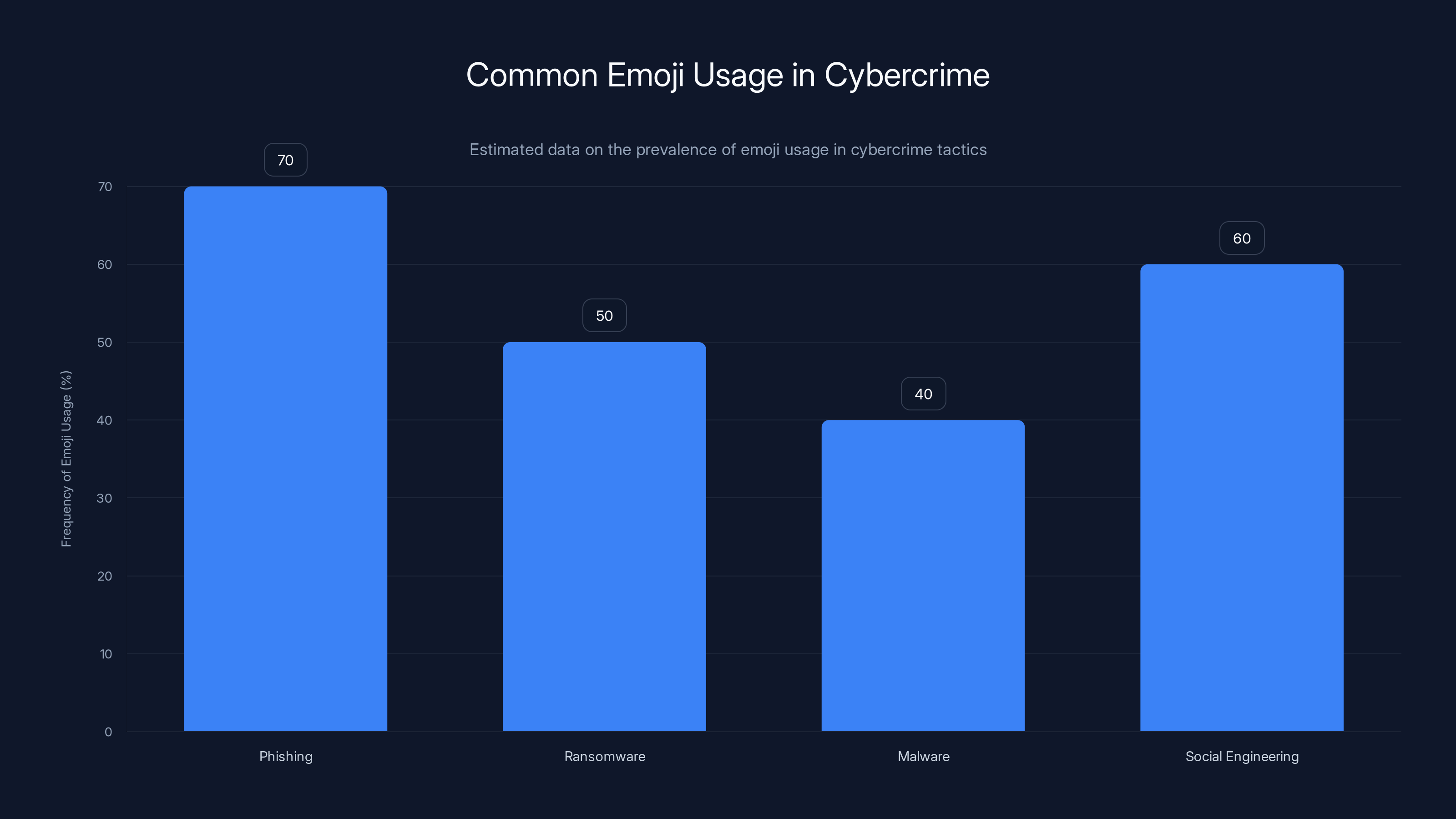
Estimated data shows that emojis are most frequently used in phishing and social engineering tactics, highlighting their role in obfuscation.
Practical Implementation Guides
Counteracting Emoji Obfuscation
For security professionals, the challenge is adapting systems to detect and respond to this new threat vector. Here are some steps that can be taken:
- Enhanced Pattern Recognition: Systems should be updated to recognize patterns involving emojis, especially when they appear in contexts that suggest substitution.
- Machine Learning Models: Implement machine learning algorithms capable of detecting unusual patterns in communication, considering the use of emojis as potential anomalies.
- Natural Language Processing (NLP): Leverage NLP to understand the context of conversations, identifying when emojis replace conventional keywords.
Example Code for Emoji Detection
Here's a simple Python script using regular expressions to identify messages containing emojis typically used for obfuscation:
pythonimport re
def detect_emoji_use(message):
# Emoji pattern commonly used in obfuscation
emoji_pattern = re.compile("[💳🔑💵]")
if emoji_pattern.search(message):
return "Potential obfuscation detected."
return "No suspicious activity."
message = "Selling 💳 info, contact for details."
print(detect_emoji_use(message))
Common Pitfalls and Solutions
- Over-reliance on Keyword Detection: Traditional systems may miss subtleties introduced by emojis. Solution: Integrate pattern recognition and context analysis.
- Ignoring Context: Emojis in isolation aren't inherently suspicious. Solution: Analyze surrounding text to ascertain intent.
- Resource Allocation: Monitoring emoji use requires additional resources. Solution: Prioritize high-risk channels for monitoring.
Future Trends and Recommendations
The Evolving Landscape
As cybercriminals refine their tactics, the security landscape must evolve. Expect the use of emojis for obfuscation to expand, potentially incorporating AI-generated images and videos.
Recommendations for Security Teams
- Stay Informed: Continuously update your knowledge of emerging tactics and tools.
- Invest in Training: Equip your team with skills in AI and NLP to better combat evolving threats.
- Collaborate with Peers: Share insights and strategies with other professionals to stay ahead of cybercriminals.
The Role of AI and Machine Learning
AI and machine learning are pivotal in detecting patterns that elude traditional methods. By analyzing vast amounts of data, these technologies can identify anomalies and predict potential threats before they materialize.
Case Study: Successful Detection
A financial institution recently thwarted a significant data breach using an AI-enhanced system that flagged emojis in transaction records. The system identified unusual patterns, prompting further investigation, which revealed a coordinated attempt to siphon funds using obfuscated communications.
Conclusion
The use of emojis in cybercrime is a testament to the ingenuity of cybercriminals and the ongoing cat-and-mouse game with security professionals. As these tactics evolve, so too must our strategies. By embracing new technologies and methodologies, the cybersecurity community can stay one step ahead, ensuring that digital spaces remain safe and secure.
Use Case: Automate your weekly security audits with AI to detect new obfuscation techniques.
Try Runable For FreeFAQ
What is emoji obfuscation?
Emoji obfuscation refers to the use of emojis to replace or mask keywords in digital communications to evade detection by security systems.
How does emoji obfuscation impact cybersecurity?
By using emojis, cybercriminals can bypass keyword-based detection systems, making it harder for security professionals to identify malicious communications.
What are the benefits of using emojis in cybercrime?
Emojis provide a unique method for obfuscating intent, allowing criminals to communicate covertly without triggering traditional security alerts.
How can organizations counteract emoji-based threats?
Organizations can counteract these threats by enhancing their detection systems with pattern recognition, machine learning, and natural language processing.
Why are emojis effective in evading detection?
Emojis are effective because they are non-textual symbols that can replace key phrases, bypassing keyword-based detection systems.
What future trends might we see in cybercrime?
Future trends may include the integration of AI-generated content for more sophisticated obfuscation and the use of multimedia elements to disguise intent.
How important is AI in combating emoji-based cybercrime?
AI is crucial as it enables the analysis of large data sets to detect patterns and anomalies that traditional methods might miss.
What role does machine learning play in cybersecurity?
Machine learning helps in identifying new patterns of cybercrime by analyzing data trends and predicting potential threats.
Key Takeaways
- Emojis are being used by cybercriminals to evade detection systems.
- This trend represents a shift towards more sophisticated cybercrime tactics.
- New detection methodologies are needed to counteract emoji obfuscation.
- AI and machine learning are critical in identifying and mitigating these threats.
- Continuous adaptation and knowledge sharing are essential for staying ahead in cybersecurity.
Related Articles
- Stolen Session Cookies: The Hidden Threat to Account Security [2025]
- Understanding Anthropic's Mythos AI Model: A New Era in Cybersecurity [2025]
- Hackers Exploiting WhatsApp and Cloud Tools for Silent Computer Takeovers [2025]
- Understanding the LAPD Data Breach: Lessons in Cybersecurity [2025]
- US Agencies Alert: Iranian Hackers Targeting American Critical Infrastructure [2025]
- Investing in AI Startups: Why the 'AI Shift' Makes 2025 a Prime Time for New Ventures
![How Emojis Are Reshaping Cybercrime Tactics: A Deep Dive [2025]](https://tryrunable.com/blog/how-emojis-are-reshaping-cybercrime-tactics-a-deep-dive-2025/image-1-1775669783100.jpg)



