Understanding the FBI's Takedown of Pro-Iranian Hacking Group Websites [2025]
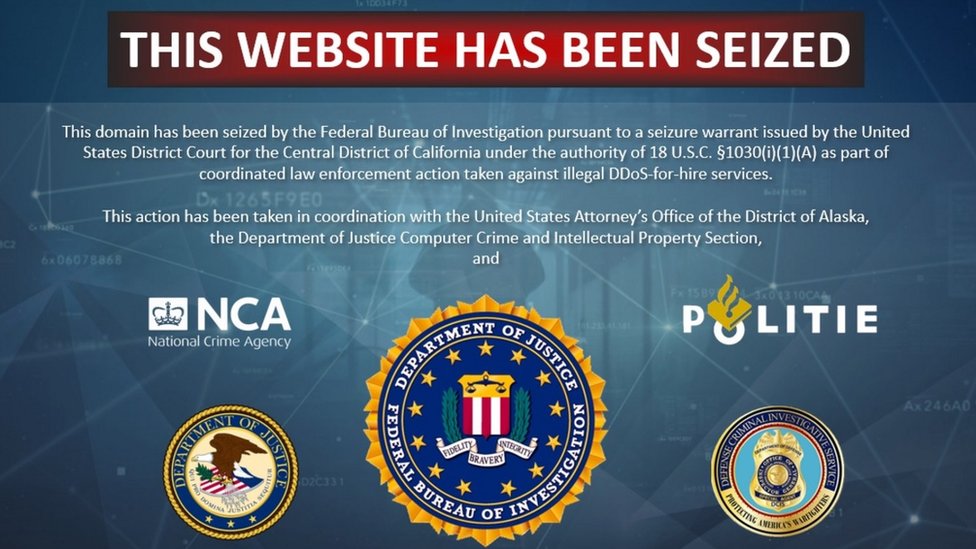
Last week, the FBI seized two websites operated by the pro-Iranian hacking group known as Handala. This move came shortly after the group claimed responsibility for a destructive cyberattack on the U.S. medical technology giant, Stryker. The websites, which had been used to publicize Handala's hacks and to dox individuals linked to the Israeli military and defense contractors, were replaced with a banner announcing the law enforcement action. According to The Times of Israel, this attack highlighted the vulnerabilities in critical sectors.
The seizure announcement suggested that U.S. authorities believed these sites were being used to conduct or support malicious cyber activities on behalf of a foreign state actor. But what does this mean for cybersecurity at large, and how can organizations protect themselves against similar threats? The Center for Strategic and International Studies discusses how cyber warfare could shape conflicts involving the U.S. and Israel against Iran.
TL; DR
- FBI Seizure: The FBI took down websites linked to pro-Iranian hackers after a cyberattack on Stryker.
- Cyber Threats: These sites were used for malicious cyber activities, possibly linked to a foreign state.
- Mitigation Strategies: Organizations must enhance cybersecurity measures to prevent such attacks.
- Future Trends: Cybersecurity will increasingly focus on state-sponsored threats.
- Bottom Line: Robust cybersecurity practices are crucial to defend against sophisticated cyber threats.
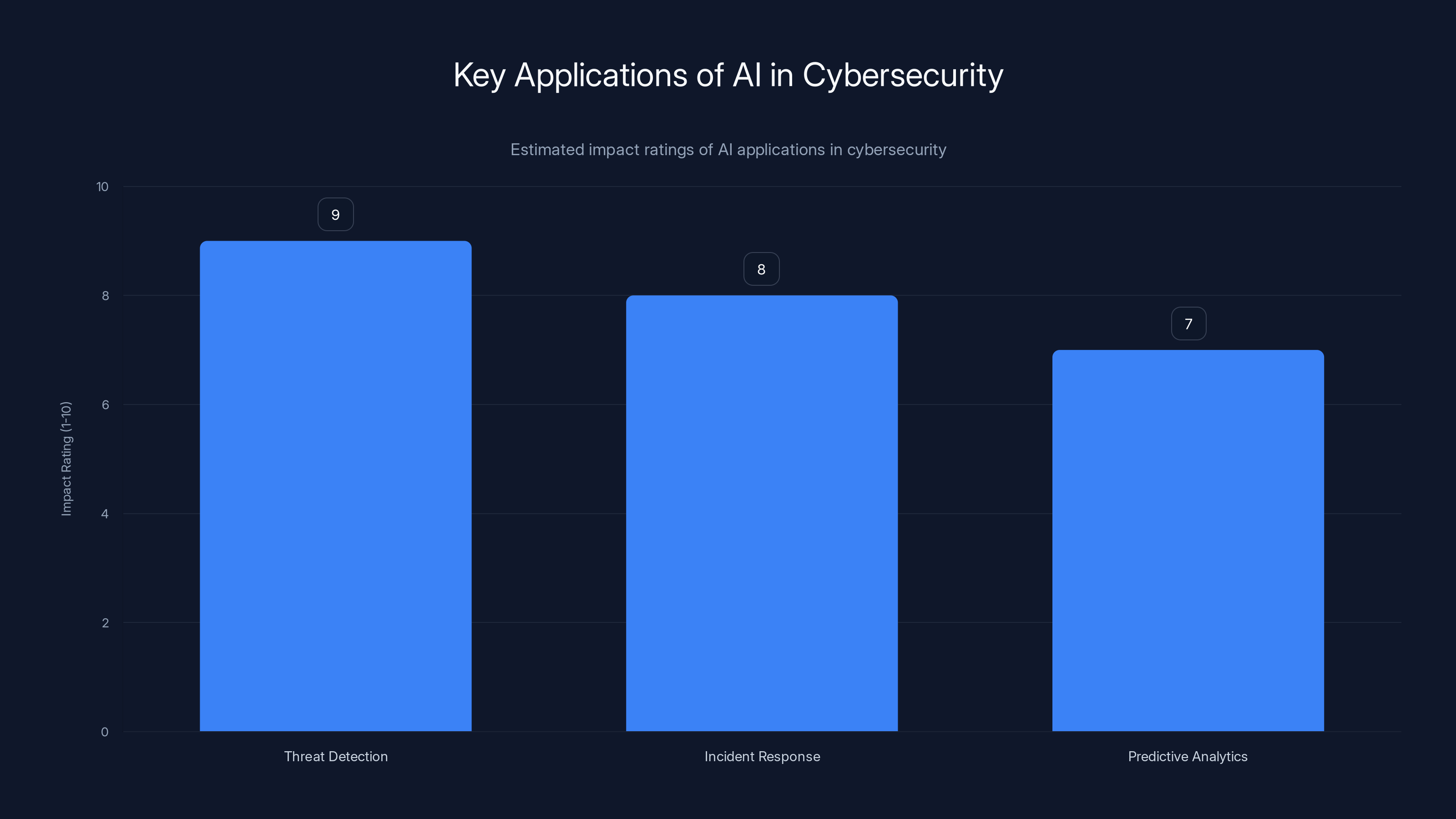
AI applications in cybersecurity show high impact, with threat detection rated highest at 9. Estimated data.
The Anatomy of a Cyberattack
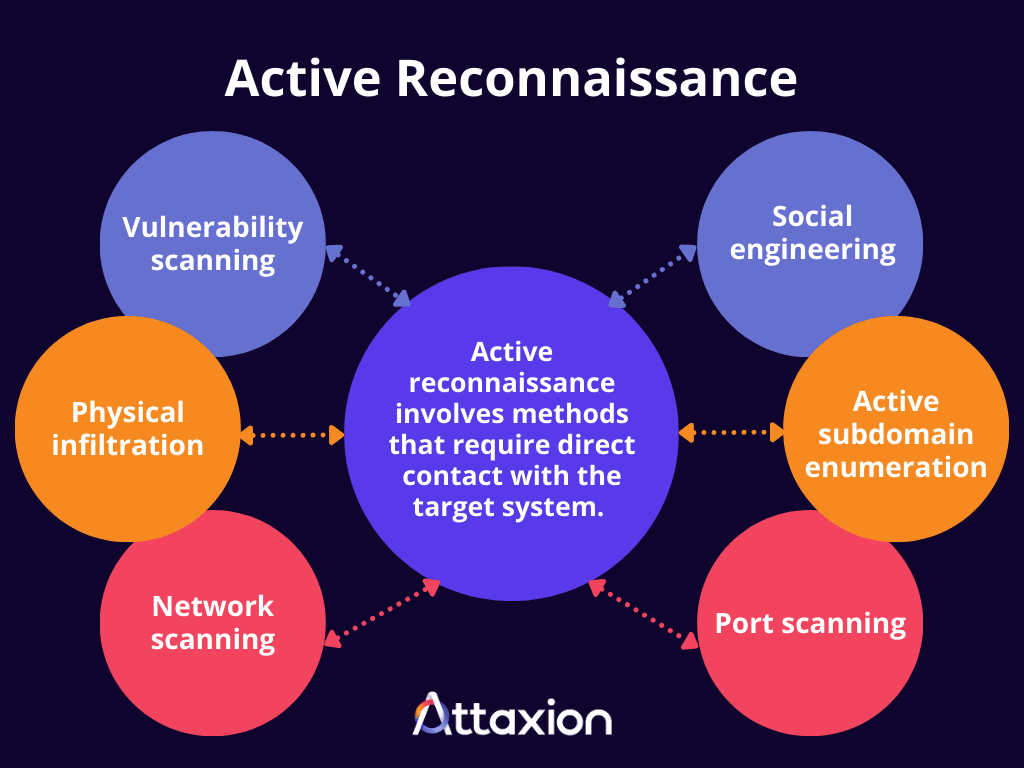
When discussing cyberattacks like the one on Stryker, it's essential to understand the typical anatomy of such an event. Cyberattacks generally follow a structured process, which includes reconnaissance, intrusion, exploitation, and exfiltration. Each stage is critical to the attack's success and requires specific countermeasures.
Reconnaissance
In this initial phase, attackers gather as much information as possible about the target. This could involve scanning for vulnerabilities, gathering data from public sources, or even social engineering tactics to gain insider information.
Best Practices:
- Regularly update and patch systems to close known vulnerabilities.
- Conduct regular security audits and penetration testing.
- Educate employees about phishing and social engineering tactics.
Intrusion
Once enough information is gathered, attackers attempt to penetrate the target's defenses. This could involve exploiting software vulnerabilities or using stolen credentials. The Microsoft February 2026 Patch Tuesday addressed numerous vulnerabilities, highlighting the importance of timely updates.
Best Practices:
- Implement multi-factor authentication (MFA) to secure access.
- Use intrusion detection systems (IDS) to monitor for suspicious activities.
- Restrict access based on the principle of least privilege.
Exploitation
After gaining access, attackers exploit this to gain control over systems or data. This step often involves deploying malware or ransomware to lock down critical systems. Research by Halcyon shows how ransomware like Crytox can evade endpoint security.
Best Practices:
- Employ endpoint protection solutions to detect and block malware.
- Regularly back up data and ensure backups are immutable.
- Monitor network traffic for unusual patterns.
Exfiltration
In the final stage, attackers extract valuable information from the target's systems. This could include intellectual property, customer data, or other sensitive information.
Best Practices:
- Encrypt sensitive data at rest and in transit.
- Monitor data flows and set up alerts for large or unexpected data transfers.
- Implement data loss prevention (DLP) solutions.

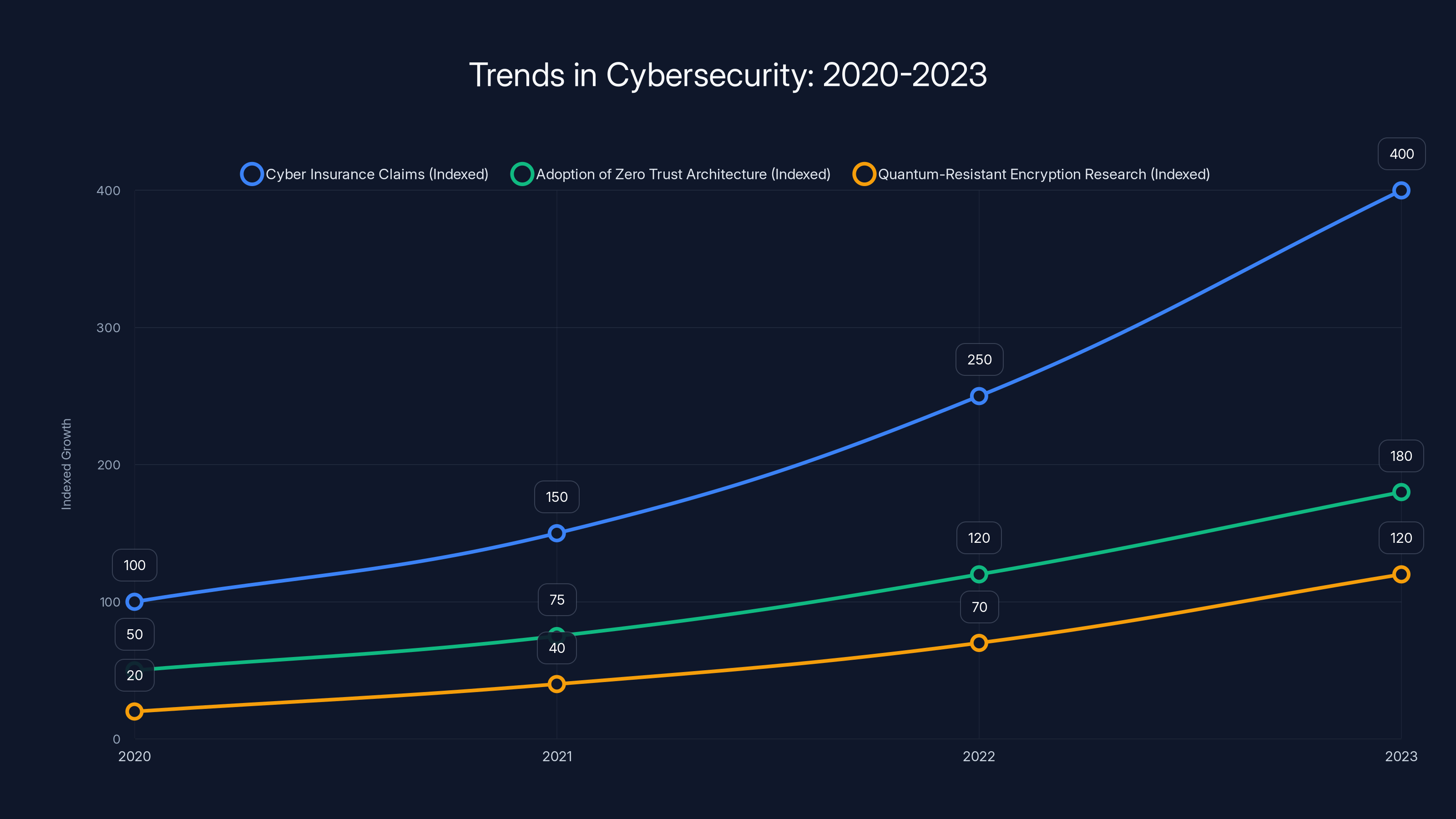
Cyber insurance claims surged by over 300% from 2020 to 2023, highlighting the increased impact of cybercrime. Zero Trust Architecture and quantum-resistant encryption research are also on the rise. (Estimated data)
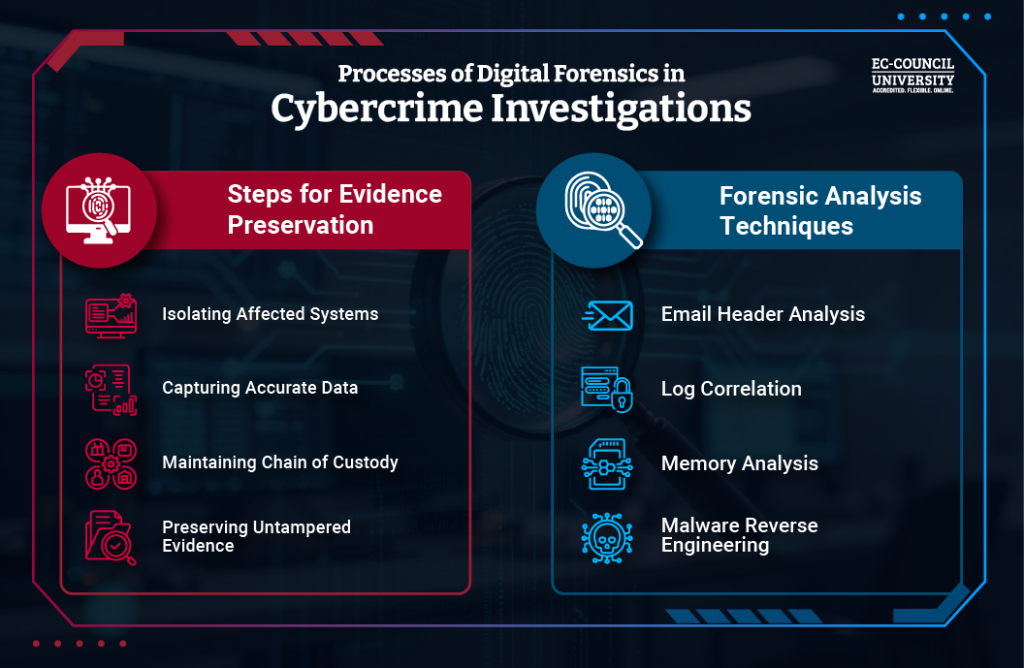
The Role of Law Enforcement in Cybersecurity
The FBI's takedown of Handala's websites underscores the critical role that law enforcement agencies play in cybersecurity. By disrupting the infrastructure used by hackers, these agencies can significantly hinder their operations. However, the collaboration between businesses and law enforcement is paramount to effectively combat cybercrime. Yahoo News provides further insights into the FBI's actions against these cyber threats.
How Law Enforcement Works with Businesses
- Information Sharing: Law enforcement agencies often share intelligence about emerging threats, helping businesses prepare for potential attacks.
- Incident Response: In the event of a cyberattack, law enforcement can assist with the investigation, helping to identify perpetrators and mitigate damage.
- Legal Action: Agencies can take legal action against cybercriminals, such as seizing assets or launching prosecutions.
Quick Tip: Establish a point of contact with local law enforcement and participate in information-sharing initiatives like the Cyber Information Sharing and Collaboration Program (CISCP).
Emerging Threats and Trends
As cybersecurity threats evolve, so too must the strategies used to combat them. The increasing prevalence of state-sponsored attacks, like those allegedly linked to Handala, underscores the need for robust defenses. The National Defense Magazine discusses how AI is enabling new cyber risks.
State-Sponsored Attacks
State-sponsored cyberattacks are typically more sophisticated and better-resourced than those conducted by independent hackers. These attacks often have political or economic motives and can target critical infrastructure, government entities, or large corporations. Arctic Wolf reported on the disruption caused by the Handala group's attack on Stryker's systems.
Case Study: In 2023, a state-sponsored group targeted a major U.S. energy provider, disrupting operations and causing millions in damages. The attack highlighted vulnerabilities in industrial control systems (ICS) and prompted a renewed focus on securing critical infrastructure. The NVIDIA blog explores the role of AI in securing these systems.
The Rise of AI in Cybersecurity
Artificial intelligence (AI) is playing an increasingly important role in cybersecurity. AI can help identify and respond to threats faster than human analysts, making it a valuable tool in the fight against cybercrime.
Key Applications:
- Threat Detection: AI algorithms can analyze vast amounts of data to identify potential threats in real time.
- Incident Response: AI can automate response actions, reducing the time it takes to contain attacks.
- Predictive Analytics: AI can predict future threats based on historical data, allowing organizations to proactively defend against them.
Quick Tip: Consider integrating AI-powered solutions like Runable into your cybersecurity strategy to enhance threat detection and response capabilities.

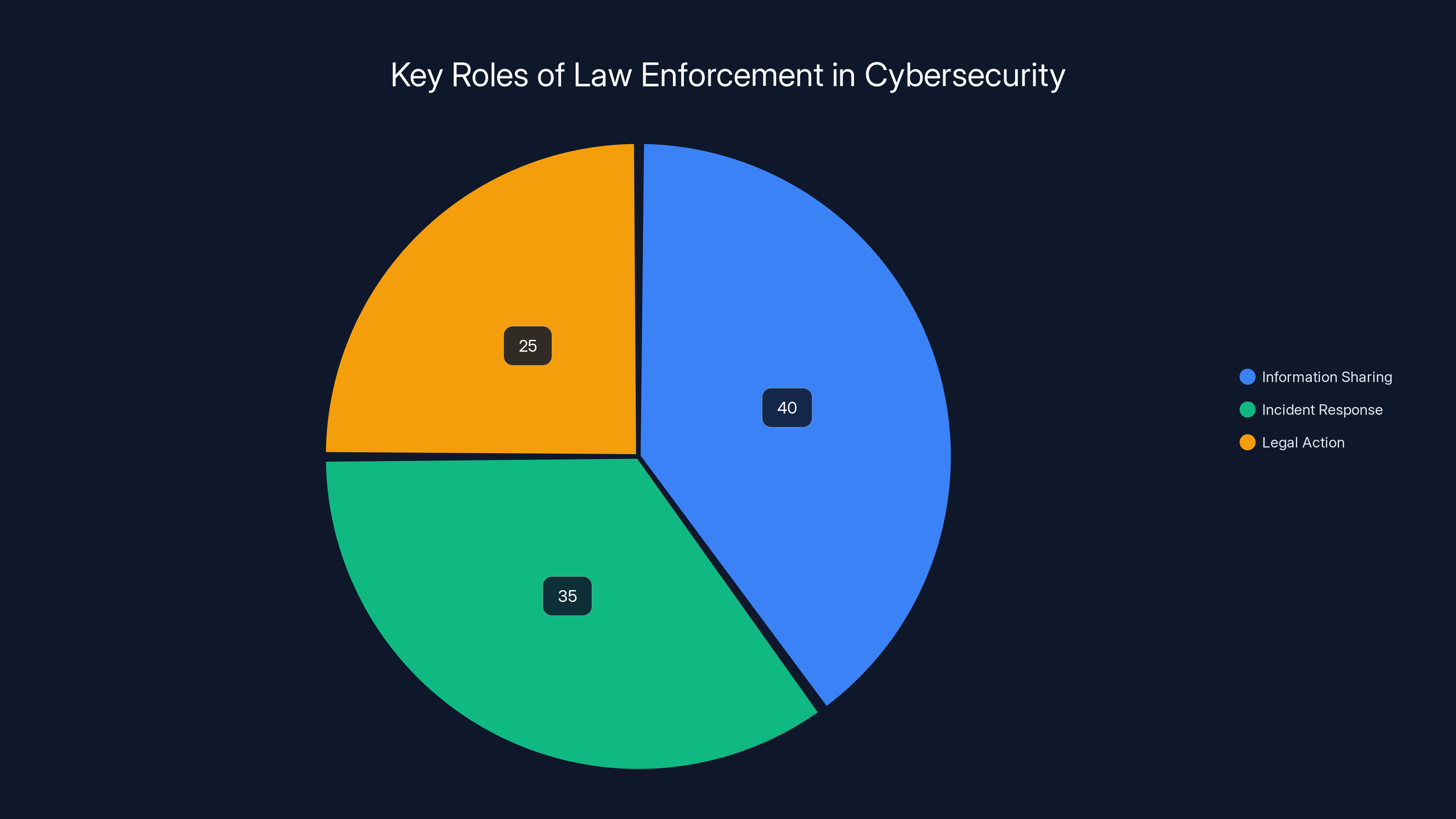
Law enforcement's role in cybersecurity is distributed across information sharing (40%), incident response (35%), and legal action (25%). Estimated data.
Best Practices for Cybersecurity
In light of growing cyber threats, organizations must adopt comprehensive cybersecurity strategies. Here are some best practices to help safeguard against attacks:
- Regularly Update Software: Keep all systems and applications up to date to protect against known vulnerabilities.
- Conduct Employee Training: Educate employees about cybersecurity risks and train them to recognize phishing attempts.
- Implement Network Segmentation: Isolate critical systems from the rest of the network to limit the spread of malware.
- Monitor and Audit: Continuously monitor network traffic and conduct regular security audits to identify potential weaknesses.
The Future of Cybersecurity
Looking ahead, the cybersecurity landscape will continue to change as new technologies emerge and threat actors adapt. Here are some trends to watch:
Zero Trust Architecture
The Zero Trust model assumes that threats could exist both inside and outside the network, requiring verification for every request. This approach minimizes the risk of lateral movement and data breaches.
Quantum Computing
Quantum computing has the potential to break traditional encryption methods, posing a significant threat to data security. Organizations must stay ahead by exploring quantum-resistant encryption techniques.
Cyber Insurance
As cyberattacks become more common, more businesses are turning to cyber insurance to mitigate financial losses. Understanding policy coverage and exclusions is crucial for effective risk management. San Diego Business Journal discusses how family offices can mitigate risks using cybersecurity and AI.
Did You Know: Cyber insurance claims increased by over 300% between 2020 and 2023, reflecting the growing impact of cybercrime on businesses.
Conclusion
The FBI's takedown of pro-Iranian hacking group websites serves as a stark reminder of the persistent cyber threats facing organizations today. By understanding the anatomy of cyberattacks and implementing robust cybersecurity measures, businesses can better protect themselves against these evolving threats. As the landscape continues to change, staying informed and proactive is key to maintaining a strong security posture.
FAQ
What is a cyberattack?
A cyberattack is any attempt to gain unauthorized access to a computer system, network, or data with the intent to cause harm or disruption.
How does the FBI combat cybercrime?
The FBI works with local law enforcement, private sector partners, and international agencies to investigate cybercrimes, disrupt criminal networks, and prosecute offenders.
What are state-sponsored cyberattacks?
State-sponsored cyberattacks are executed by government-affiliated groups, often targeting critical infrastructure or sensitive information for political or economic gain.
How can businesses protect themselves from cyberattacks?
Businesses can protect themselves by implementing strong cybersecurity practices, such as regular software updates, employee training, and network segmentation.
What role does AI play in cybersecurity?
AI enhances cybersecurity by improving threat detection, automating incident response, and providing predictive analytics to anticipate future threats.
What is Zero Trust architecture?
Zero Trust is a security model that requires verification for every request, assuming potential threats exist both inside and outside the network.
Why is cyber insurance important?
Cyber insurance helps businesses recover financially from cyber incidents by covering costs associated with data breaches, business interruption, and legal liabilities.
How can organizations stay ahead of evolving cyber threats?
Organizations can stay ahead by continuously updating their cybersecurity strategies, investing in new technologies, and participating in information-sharing initiatives.
Key Takeaways
- FBI's proactive measures against cyber threats highlight the importance of law enforcement in cybersecurity.
- State-sponsored cyberattacks pose a significant risk to critical infrastructure and require robust defenses.
- AI is becoming a crucial tool in enhancing threat detection and incident response capabilities.
- Zero Trust architecture minimizes the risk of breaches by verifying every network request.
- Quantum computing could challenge current encryption methods, necessitating the exploration of quantum-resistant techniques.
- Cyber insurance is increasingly important for managing the financial impact of cyber incidents.
- Continuous education and training are vital for employees to recognize and respond to cyber threats.
- Collaborative efforts between businesses and law enforcement are essential for combating cybercrime effectively.
Related Articles
- Google's Strategic Alliance Against Global Scams: A Deep Dive [2025]
- Understanding Ransomware Attacks: Lessons from the Marquis Data Theft Incident [2025]
- Hundreds of Millions of iPhones Can Be Hacked With a New Tool Found in the Wild | WIRED
- Apple’s New Era of Background Security Updates: An In-Depth Look [2025]
- Google's $32B Wiz Acquisition: Strategic Insights and Future Implications [2025]
- The Future of Internet Law: Exploring the Implications of Proposed Legislative Changes [2025]
![Understanding the FBI's Takedown of Pro-Iranian Hacking Group Websites [2025]](https://tryrunable.com/blog/understanding-the-fbi-s-takedown-of-pro-iranian-hacking-grou/image-1-1773934489399.png)



