Introduction: The Marquis Ransomware Attack
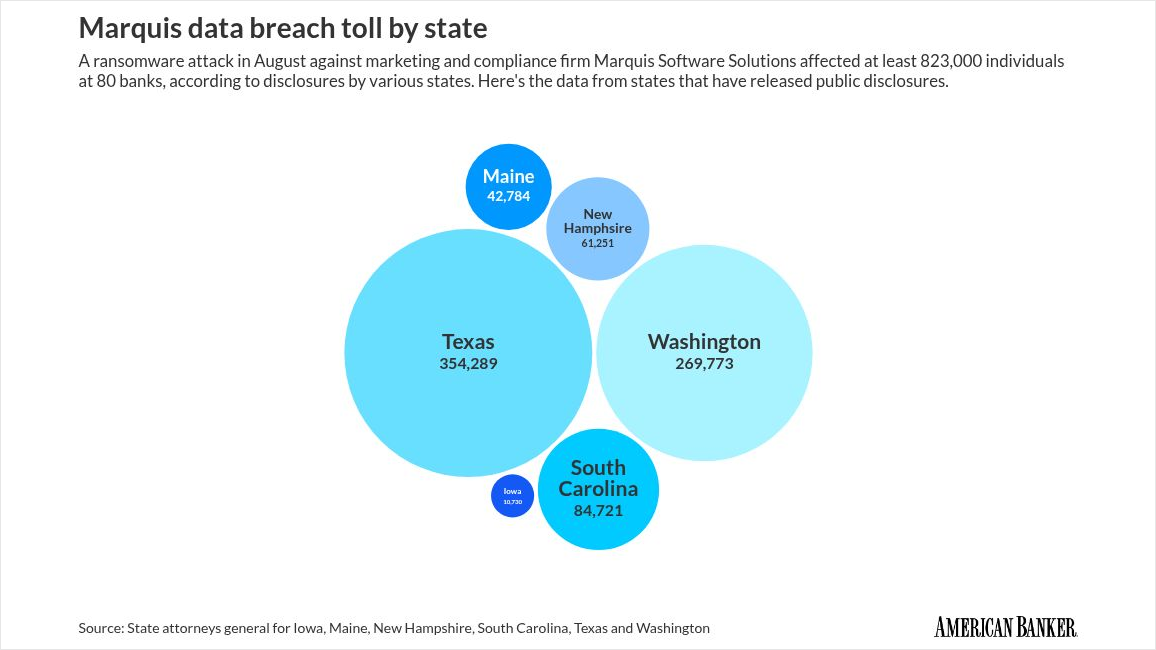
In August 2025, Marquis, a fintech company based in Plano, Texas, experienced a significant ransomware attack. The breach affected over 672,000 individuals, exposing their personal and financial data. This incident underscores the growing threat of ransomware and highlights the critical need for robust cybersecurity measures.
TL; DR
- Massive Data Breach: Over 672,000 individuals' data stolen in the Marquis ransomware attack.
- Sensitive Information Exposed: Names, dates of birth, and postal addresses compromised.
- Prevention Strategies: Implement multi-layered security and regular employee training.
- Immediate Response: Incident response plans are crucial for minimizing damage.
- Future Trends: Increased focus on AI-driven security solutions.

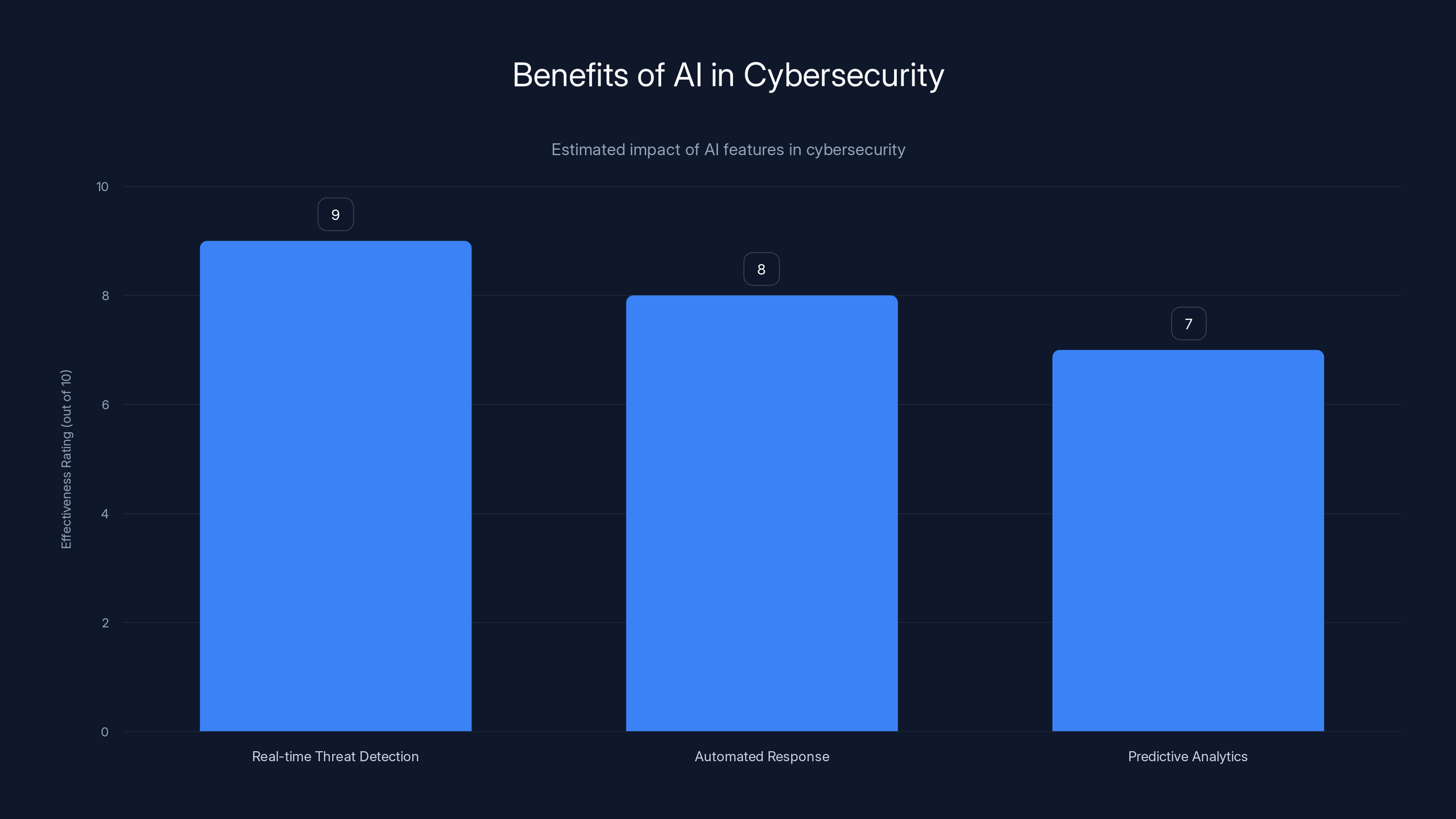
AI features like real-time threat detection, automated response, and predictive analytics significantly enhance cybersecurity, with effectiveness ratings of 9, 8, and 7 respectively. Estimated data.
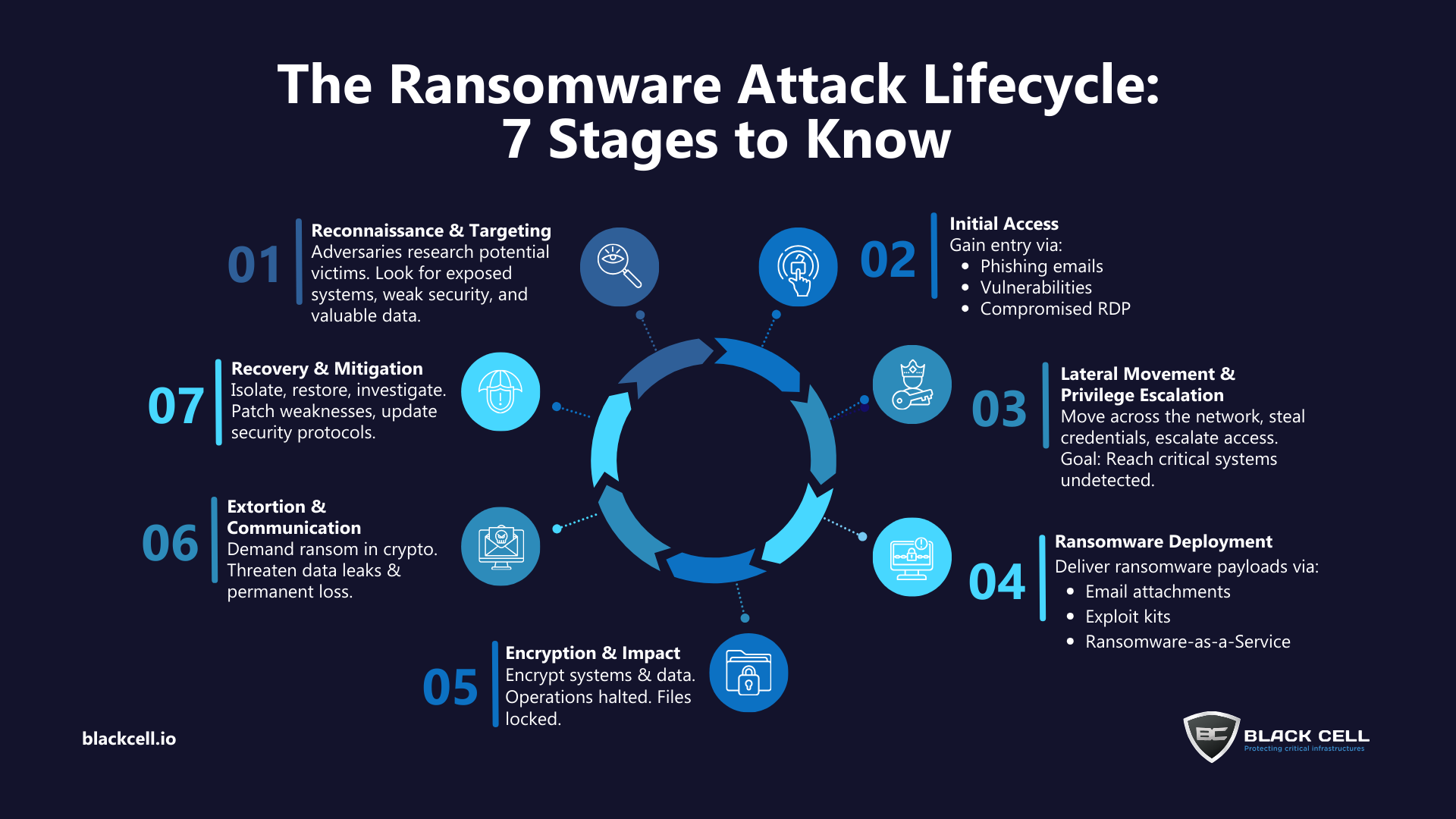
The Anatomy of a Ransomware Attack
Ransomware attacks are a form of malware that encrypts a victim's files. The attacker then demands a ransom to restore access. Typically, these attacks exploit vulnerabilities in software or human behavior, such as phishing emails.
How Ransomware Works
- Infection: Malware infiltrates the network through phishing, downloaded files, or software vulnerabilities.
- Encryption: Files are encrypted, rendering them inaccessible.
- Ransom Demand: Victims receive a message demanding payment for the decryption key.
- Impact: Operations are disrupted, leading to potential financial and reputational damage.
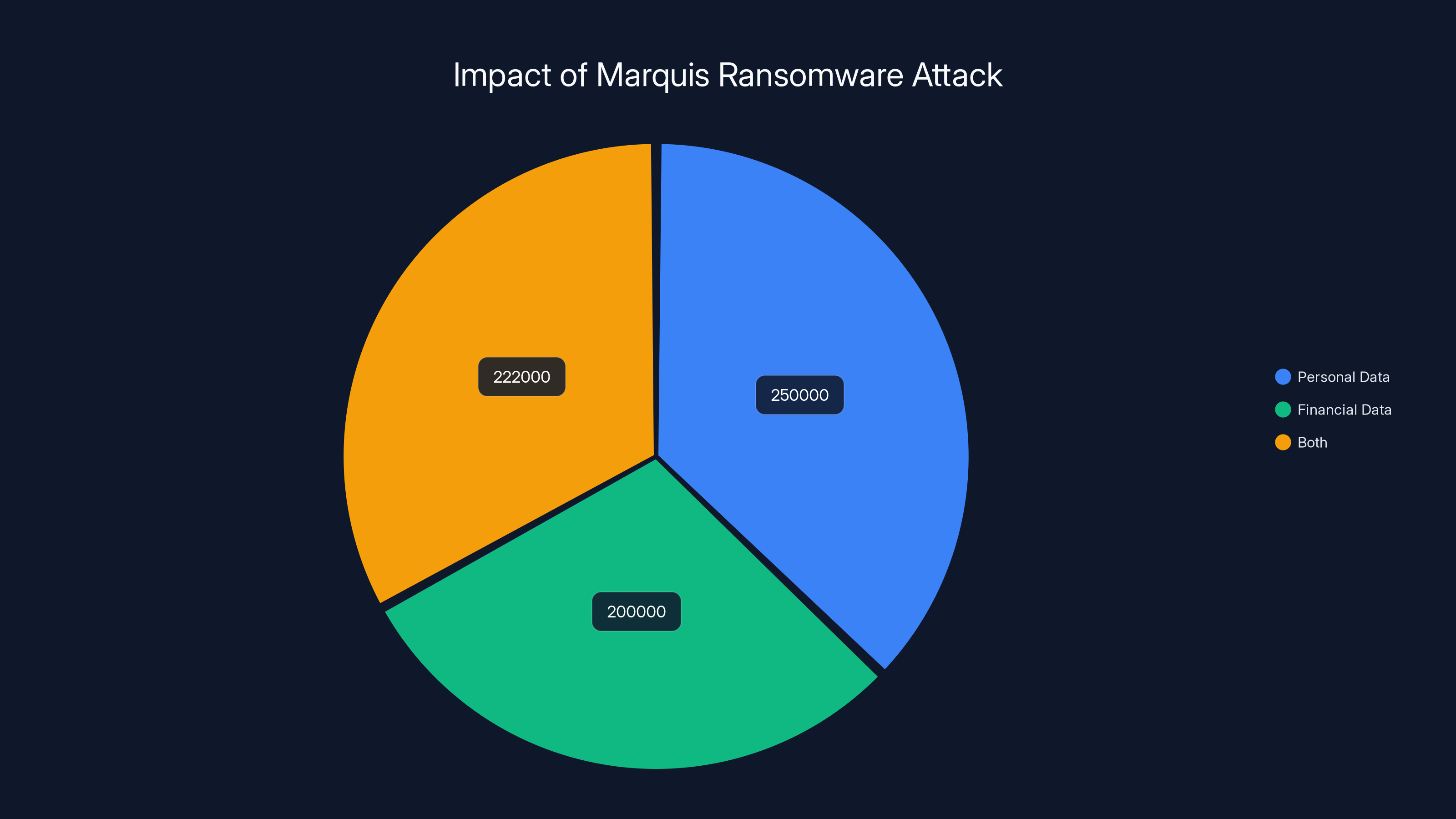
The ransomware attack on Marquis affected over 672,000 individuals, with a significant portion having both personal and financial data exposed. Estimated data.
Case Study: Marquis Ransomware Attack
In the case of Marquis, the attack led to the exposure of sensitive data from over 672,000 individuals. The attack was facilitated through vulnerabilities in the company's systems, allowing hackers to access and encrypt data.
Impact of the Attack
- Data Breach: Personal information, including names, birth dates, and addresses, was stolen.
- Reputational Damage: Trust in Marquis and associated banks was severely impacted.
- Financial Losses: The cost of response and potential ransoms demanded by attackers.
Lessons Learned from Marquis
- Regular Security Audits: Identifying vulnerabilities before attackers do is critical.
- Employee Training: Educating staff about phishing and social engineering can prevent breaches.
- Data Encryption: Encrypting sensitive data at rest and in transit can mitigate damage.
Preventing Ransomware Attacks
Preventing ransomware attacks requires a multi-faceted approach that includes both technical and behavioral strategies.
Technical Measures
- Endpoint Protection: Use advanced antivirus and anti-malware tools.
- Network Segmentation: Isolate critical systems to prevent lateral movement of malware.
- Regular Updates: Patch systems and software to fix vulnerabilities.
Behavioral Measures
- Security Training: Regularly train employees on cybersecurity best practices.
- Phishing Simulations: Conduct tests to improve employees' ability to detect phishing attempts.
Estimated data shows that the 'Impact' phase takes the longest, consuming 40% of the total attack duration, highlighting the significant disruption caused by ransomware.
Implementing a Cybersecurity Framework
A structured cybersecurity framework can help organizations prepare for and respond to ransomware attacks.
Key Components of a Cybersecurity Framework
- Risk Assessment: Identify and prioritize potential threats.
- Incident Response Plan: Outline procedures for detecting, responding to, and recovering from attacks.
- Continuous Monitoring: Use AI and machine learning to detect anomalies in real time.
The Role of AI in Cybersecurity
Artificial Intelligence (AI) is increasingly being leveraged to enhance cybersecurity measures. AI can quickly analyze vast amounts of data, identifying threats and vulnerabilities faster than human analysts.
Benefits of AI in Cybersecurity
- Real-time Threat Detection: AI systems can identify unusual patterns and potential threats as they occur.
- Automated Response: AI can automate initial responses to mitigate damage before human intervention.
- Predictive Analytics: AI can predict future threats based on historical data, enabling proactive defense strategies.
Common Pitfalls in Cybersecurity
Despite best efforts, many organizations still fall victim to ransomware due to common pitfalls.
Pitfall #1: Lack of Preparedness
Organizations often underestimate the threat of ransomware, leading to inadequate preparation.
Pitfall #2: Insufficient Training
Without ongoing training, employees may fall prey to phishing attacks, a primary vector for ransomware.

Future Trends in Ransomware Defense
As ransomware attacks evolve, so too must the strategies to combat them.
Trend #1: Increased Use of AI
AI will continue to play a significant role in identifying and mitigating threats.
Trend #2: Regulatory Changes
Governments are likely to introduce stricter regulations regarding data protection and breach notifications.
Trend #3: Collaboration Across Sectors
Public and private sector collaboration will be crucial in developing effective defenses against ransomware.
Conclusion: Building Resilience Against Ransomware
The Marquis ransomware attack serves as a stark reminder of the vulnerabilities that exist in today's digital landscape. By implementing robust cybersecurity measures and fostering a culture of security awareness, organizations can build resilience against such threats.
Bottom Line: Preparing for ransomware attacks requires a proactive approach, integrating technology, training, and strategic planning to safeguard sensitive data and maintain trust.
FAQ
What is ransomware?
Ransomware is a type of malware that encrypts a victim's data, demanding a ransom for the decryption key.
How can organizations prevent ransomware attacks?
Implementing strong security measures, regular employee training, and maintaining up-to-date software can significantly reduce the risk of ransomware attacks.
What should be included in an incident response plan?
An effective incident response plan should include steps for detection, containment, eradication, recovery, and communication.
How does AI help in cybersecurity?
AI enhances cybersecurity by providing real-time threat detection, automated responses, and predictive analytics to anticipate future threats.
What role does employee training play in cybersecurity?
Regular training helps employees recognize and respond appropriately to phishing attempts and other social engineering attacks.
What are the future trends in ransomware defense?
Future trends include increased use of AI, stricter regulatory requirements, and greater collaboration between the public and private sectors.
References
- National Institute of Standards and Technology (NIST) Cybersecurity Framework
- Cybersecurity and Infrastructure Security Agency (CISA) Ransomware Guide
- Federal Bureau of Investigation (FBI) Cyber Crime Resources
Key Takeaways
- Over 672,000 individuals affected in Marquis ransomware attack.
- Critical to implement multi-layered security measures.
- AI plays a significant role in real-time threat detection.
- Employee training is crucial for phishing prevention.
- Future trends point to increased AI use and stricter regulations.
Related Articles
- Apple’s New Era of Background Security Updates: An In-Depth Look [2025]
- The Ultimate Guide to Dark Web Monitoring Services [2025]
- Proof Over Promises: A New Doctrine for Cybersecurity [2025]
- Hundreds of Millions of iPhones Can Be Hacked With a New Tool Found in the Wild | WIRED
- Optimizing Mobile Device Management: Security Meets Efficiency [2025]
- Alibaba's OpenClaw App: Navigating China's AI Craze Amid Cybersecurity Concerns [2025]
![Understanding Ransomware Attacks: Lessons from the Marquis Data Theft Incident [2025]](https://tryrunable.com/blog/understanding-ransomware-attacks-lessons-from-the-marquis-da/image-1-1773846438860.jpg)



